TOTP动态令牌
一、TOTP原理
转载:
动态令牌离线生成机制探究(2FA & TOTP)_摸鱼Script的博客-CSDN博客 著作权归作者所有,转载请注明出处。
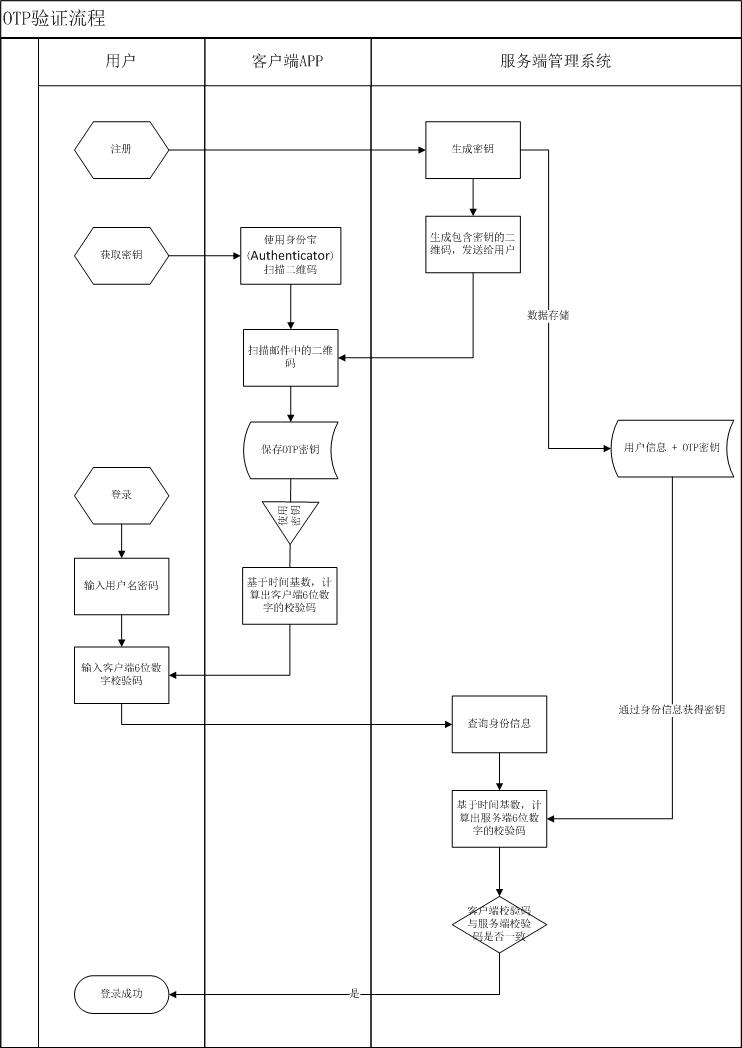
图解TOTP:
代码实现如下:代码来源Github
地址:https://github.com/Netthaw/TOTP-MCU 著作权归作者所有,转载请注明出处。
1 #include "totp/totp.h" 2 #include "totp/sha1.h" 3 #include <stdio.h> 4 #include <string.h> 5 #include "base32.h" 6 #include "hardware/datetime.h" 7 8 uint8_t* _hmacKey; 9 uint32_t _timeStep; 10 11 // Init the library with the private key, its length and the timeStep duration 12 void TOTP(uint8_t* hmacKey, uint32_t timeStep) 13 { 14 _hmacKey = hmacKey;//这个指针要指向一个不会释放的变量,否则数据每次都会丢失 15 _timeStep = timeStep; 16 } 17 // Generate a code, using the timestamp provided//使用提供的时间戳生成代码 18 uint32_t getCodeFromTimestamp(void) 19 { 20 long nowTime = strTounixtime(getNowDateTime()); //获取当前时间戳 21 uint32_t steps = nowTime / _timeStep;//时间戳/时间间隔 22 return getCodeFromSteps(steps);//传入时间戳生成的步数,处理后返回最终6位验证码 23 } 24 25 // Generate a code, using the number of steps provided//使用提供的步骤数生成代码 26 uint32_t getCodeFromSteps(uint32_t steps) { 27 // STEP 0, map the number of steps in a 8-bytes array (counter value) 28 uint8_t _byteArray[8]; 29 30 _byteArray[0] = 0x00; 31 _byteArray[1] = 0x00; 32 _byteArray[2] = 0x00; 33 _byteArray[3] = 0x00; 34 _byteArray[4] = (uint8_t)((steps >> 24) & 0xFF); 35 _byteArray[5] = (uint8_t)((steps >> 16) & 0xFF); 36 _byteArray[6] = (uint8_t)((steps >> 8) & 0XFF); 37 _byteArray[7] = (uint8_t)((steps & 0XFF)); 38 39 // STEP 1, get the HMAC-SHA1 hash from counter and key 40 initHmac(_hmacKey, strlen(_hmacKey)); 41 writeArray(_byteArray, 8); 42 uint8_t* _hash = resultHmac(); 43 44 // STEP 2, apply dynamic truncation to obtain a 4-bytes string 45 uint32_t _truncatedHash = 0; 46 uint8_t _offset = _hash[20 - 1] & 0xF; 47 uint8_t j; 48 for (j = 0; j < 4; ++j) { 49 _truncatedHash <<= 8; 50 _truncatedHash |= _hash[_offset + j]; 51 } 52 53 // STEP 3, compute the OTP value 54 _truncatedHash &= 0x7FFFFFFF; //Disabled 55 _truncatedHash %= 1000000; 56 return _truncatedHash; 57 } 58 59 void totpInit(void) 60 { 61 static char hmacKey[] = "CERBERUS1"; 62 TOTP(hmacKey,60); 63 // Secret key, Key length, Timestep (7200s - 2hours) 64 }
#ifndef TOTP_H #define TOTP_H #include <stdint.h> uint32_t getCodeFromTimestamp(void); uint32_t getCodeFromSteps(uint32_t steps); void totpInit(void); #endif
#include <stdio.h> #include <string.h> #include "totp/sha1.h" #define SHA1_K0 0x5a827999 #define SHA1_K20 0x6ed9eba1 #define SHA1_K40 0x8f1bbcdc #define SHA1_K60 0xca62c1d6 union _buffer { uint8_t b[BLOCK_LENGTH]; uint32_t w[BLOCK_LENGTH/4]; } buffer; union _state { uint8_t b[HASH_LENGTH]; uint32_t w[HASH_LENGTH/4]; } state; uint8_t bufferOffset; uint32_t byteCount; unsigned char keyBuffer[BLOCK_LENGTH]; unsigned char innerHash[HASH_LENGTH]; uint8_t sha1InitState[] = { 0x01,0x23,0x45,0x67, // H0 0x89,0xab,0xcd,0xef, // H1 0xfe,0xdc,0xba,0x98, // H2 0x76,0x54,0x32,0x10, // H3 0xf0,0xe1,0xd2,0xc3 // H4 }; void init(void) { memcpy(state.b,sha1InitState,HASH_LENGTH); byteCount = 0; bufferOffset = 0; } uint32_t rol32(uint32_t number, uint8_t bits) { return ((number << bits) | (uint32_t)(number >> (32-bits))); } void hashBlock() { uint8_t i; uint32_t a,b,c,d,e,t; a=state.w[0]; b=state.w[1]; c=state.w[2]; d=state.w[3]; e=state.w[4]; for (i=0; i<80; i++) { if (i>=16) { t = buffer.w[(i+13)&15] ^ buffer.w[(i+8)&15] ^ buffer.w[(i+2)&15] ^ buffer.w[i&15]; buffer.w[i&15] = rol32(t,1); } if (i<20) { t = (d ^ (b & (c ^ d))) + SHA1_K0; } else if (i<40) { t = (b ^ c ^ d) + SHA1_K20; } else if (i<60) { t = ((b & c) | (d & (b | c))) + SHA1_K40; } else { t = (b ^ c ^ d) + SHA1_K60; } t+=rol32(a,5) + e + buffer.w[i&15]; e=d; d=c; c=rol32(b,30); b=a; a=t; } state.w[0] += a; state.w[1] += b; state.w[2] += c; state.w[3] += d; state.w[4] += e; } void addUncounted(uint8_t data) { buffer.b[bufferOffset ^ 3] = data; bufferOffset++; if (bufferOffset == BLOCK_LENGTH) { hashBlock(); bufferOffset = 0; } } static void write(uint8_t data) { ++byteCount; addUncounted(data); return; } void writeArray(uint8_t *buffer, uint8_t size){ while (size--) { write(*buffer++); } } void pad() { // Implement SHA-1 padding (fips180-2 �˜5.1.1) // Pad with 0x80 followed by 0x00 until the end of the block addUncounted(0x80); while (bufferOffset != 56) addUncounted(0x00); // Append length in the last 8 bytes addUncounted(0); // We're only using 32 bit lengths addUncounted(0); // But SHA-1 supports 64 bit lengths addUncounted(0); // So zero pad the top bits addUncounted(byteCount >> 29); // Shifting to multiply by 8 addUncounted(byteCount >> 21); // as SHA-1 supports bitstreams as well as addUncounted(byteCount >> 13); // byte. addUncounted(byteCount >> 5); addUncounted(byteCount << 3); } uint8_t* result(void) { // Pad to complete the last block pad(); // Swap byte order back uint8_t i; for (i=0; i<5; i++) { uint32_t a,b; a=state.w[i]; b=a<<24; b|=(a<<8) & 0x00ff0000; b|=(a>>8) & 0x0000ff00; b|=a>>24; state.w[i]=b; } // Return pointer to hash (20 characters) return state.b; } #define HMAC_IPAD 0x36 #define HMAC_OPAD 0x5c void initHmac(const uint8_t* key, uint8_t keyLength) { uint8_t i; memset(keyBuffer,0,BLOCK_LENGTH); if (keyLength > BLOCK_LENGTH) { // Hash long keys init(); for (;keyLength--;) write(*key++); memcpy(keyBuffer,result(),HASH_LENGTH); } else { // Block length keys are used as is memcpy(keyBuffer,key,keyLength); } // Start inner hash init(); for (i=0; i<BLOCK_LENGTH; i++) { write(keyBuffer[i] ^ HMAC_IPAD); } } uint8_t* resultHmac(void) { uint8_t i; // Complete inner hash memcpy(innerHash,result(),HASH_LENGTH); // Calculate outer hash init(); for (i=0; i<BLOCK_LENGTH; i++) write(keyBuffer[i] ^ HMAC_OPAD); for (i=0; i<HASH_LENGTH; i++) write(innerHash[i]); return result(); }
#ifndef SHA1_H #define SHA1_H #include <stdint.h> #define HASH_LENGTH 20 #define BLOCK_LENGTH 64 void initHmac(const uint8_t* secret, uint8_t secretLength); uint8_t* resultHmac(void); void writeArray(uint8_t *buffer, uint8_t size); #endif
#include "totp.h" void main void { totpInit(); while(1) { uint32_t newCode = getCodeFromTimestamp();//4~6位数据 printf("222******************************newCode:%d\n",newCode); } }
TOTP动态令牌一般是设备端和服务端步骤保持一致。所以如果要想获取相同的验证码,必须保证传入哈希算法的共享密钥相同,如果有加解密,加解密方式需保持一致。时间戳同步。
博客园文件里有一个服务端代码生成的TOTP可执行文件可以验证上述代码,可以下载到电脑本地执行,该代码的密钥和上面是一致的,时间获取的是本地电脑的时间。






【推荐】国内首个AI IDE,深度理解中文开发场景,立即下载体验Trae
【推荐】编程新体验,更懂你的AI,立即体验豆包MarsCode编程助手
【推荐】抖音旗下AI助手豆包,你的智能百科全书,全免费不限次数
【推荐】轻量又高性能的 SSH 工具 IShell:AI 加持,快人一步
· 阿里最新开源QwQ-32B,效果媲美deepseek-r1满血版,部署成本又又又降低了!
· 开源Multi-agent AI智能体框架aevatar.ai,欢迎大家贡献代码
· Manus重磅发布:全球首款通用AI代理技术深度解析与实战指南
· 被坑几百块钱后,我竟然真的恢复了删除的微信聊天记录!
· AI技术革命,工作效率10个最佳AI工具