西湖论剑 2023
西湖论剑 2023
搞了一天出了俩逆向,还有一个没交上…
1. Dual personality
类似天堂之门,
将cs段寄存器设为0x33,切换到64位模式;设为0x23,切换回32位模式。
32位、64位模式切换。有反调试,静态分析即可。
import struct target = bytes.fromhex('AA4F0FE2E44199542C2B847EBC8F8B78D373885EAE47857031B309CE13F50DCA') key0 = [4, 0x77, 0x82, 0x4a] key1 = [0xc, 0x22, 0x38, 0x0E] key2 = (0x5df966ae - 0x21524111) & 0xffffffff flag = [target[_] ^ key0[_ % 4] for _ in range(32)] for i in range(4): v, = struct.unpack('<Q', bytes(flag[i * 8: (i + 1) * 8])) nv = (v >> key1[i]) | (v << (64 - key1[i])) & 0xffffffffffffffff vv = struct.pack('<Q', nv) for j in range(8): flag[i * 8 + j] = vv[j] for i in range(8): v, = struct.unpack('<L', bytes(flag[i * 4: (i + 1) * 4])) nv = (v - key2) & 0xffffffff key2 ^= v vv = struct.pack('<L', nv) for j in range(4): flag[i * 4 + j] = vv[j] print(''.join(chr(c) for c in flag))
2. Easy VT
总结一句话,逆向出 flag 很简单,但是在比赛已经结束的情况下,让我去测试这个 flag 是正确的,可以说是难死我了。
根据上述参考材料,关键在于这里。
int sub_401C90() { int len; // [esp+4h] [ebp-Ch] int cmd; // [esp+8h] [ebp-8h] cmd = vmread_from(0x4402); // vmexit 事件,指令 len = vmread_from(0x440C); // 指令长度 FREG__ = vmread_from(0x6820); ESP__ = vmread_from(0x681C); dword_4040C0 = vmread_from(0x681E); switch ( cmd ) { case 10: sub_401180(); break; case 18: // vmcall sub_401250(); break; case 19: sub_4012B0(); // vm_clear break; case 20: // launch sub_401450(); break; case 21: // vm_ptrld sub_4017B0(); break; case 22: // vm_ptrst set_real_value(); break; case 23: // vmread sub_401970(); break; case 24: // vmresume tea(); break; case 25: // wmwrite 指令 sub_401A90(); break; case 26: // vmx_off 指令 final_check(); break; case 27: // vmx_on 指令 sub_401610(); break; case 28: sub_4011D0(); break; default: break; } vmwrite_to(0x681E, len + dword_4040C0); vmwrite_to(0x681C, ESP__); return vmwrite_to(0x6820, FREG__); }
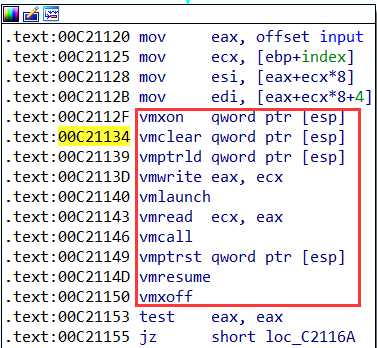
根据下图中指令的顺序,可以得出正确的分支执行顺序
发现是 rc4(标准) + tea(变种),中间还有v0 和 v1的来回交换。脚本如下
import ctypes from Crypto.Cipher import ARC4 import struct flag = [0x94, 0x39, 0x07, 0x5C, 0xB3, 0x5C, 0x80, 0x0D, 0x86, 0xA5, 0xDD, 0x87, 0x8E, 0xFB, 0x17, 0x03, 0x29, 0xEF, 0x20, 0x65, 0xAF, 0x87, 0x49, 0x5A, 0xA4, 0xC2, 0x2D, 0xEB, 0x0E, 0x47, 0xCF, 0x38] tea_key = [0x00102030, 0x40506070, 0x8090A0B0, 0xC0D0E0F0] key3 = tea_key[1] key2 = tea_key[3] key1 = tea_key[2] key0 = tea_key[0] def tea_dec(v0, v1): value_0 = ctypes.c_uint32(v0) value_1 = ctypes.c_uint32(v1) delta = ctypes.c_uint32(0xC95D6ABF) sum_ = ctypes.c_uint32(0x20000000 - delta.value * 32) for i in range(32): sum_.value += delta.value value_1.value -= (key0 + (value_0.value >> 5)) ^ (sum_.value + value_0.value) ^ (key1 + 16 * value_0.value) value_0.value += (key2 + (value_1.value >> 5)) ^ (sum_.value + value_1.value) ^ (key3 + 16 * value_1.value) return value_0.value, value_1.value def rc4_dec(v): rc4_key = b'04e52c7e31022b0b' rc4 = ARC4.new(rc4_key) return rc4.decrypt(v) for i in range(4): v0, v1 = struct.unpack('<LL', bytes(flag[i * 8: (i + 1) * 8])) nv0, nv1 = tea_dec(v0, v1) v = struct.pack('<LL', nv1, nv0) nv0, nv1 = struct.unpack('<LL', rc4_dec(v)) v = struct.pack('<LL', nv1, nv0) for j in range(8): flag[i * 8 + j] = v[j] print(''.join(chr(i) for i in flag))
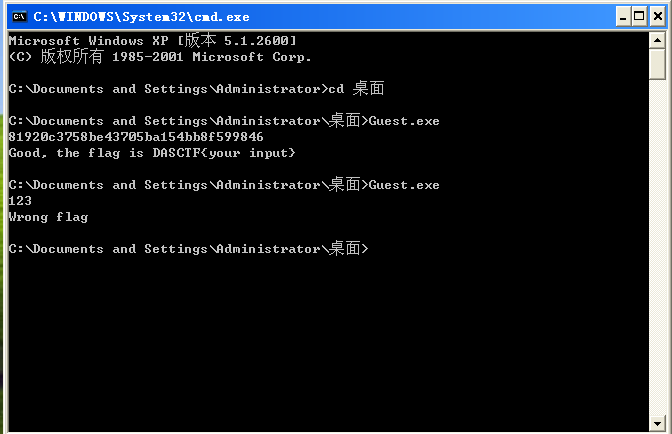
关键:咋跑起来?
win11 、 win7 驱动后跑不起来,应该是签名的问题反正死活折腾不上去。最后无奈装了 xp,安装了一系列的 dll,补齐环境之后,发现驱动是跑起来了, Guest.exe 又不兼容了,我 ******。但是还好,我写个兼容的就是了
#include <stdio.h> int main() { char buff[100]; gets(buff); int EAX; for (int i = 0;; ++i) { if (i >= 4) { printf("Good, the flag is DASCTF{your input}\n"); return 0; } __asm__ __volatile__("mov eax, %1;" "mov ecx, %2;" "mov esi, [eax+ecx*8];" "mov edi, [eax+ecx*8+4];" "vmxon qword ptr [esp];" "vmclear qword ptr [esp];" "vmptrld qword ptr [esp];" "vmwrite eax, ecx;" "vmlaunch;" "vmread ecx, eax;" "vmcall;" "vmptrst qword ptr [esp];" "vmresume;" "vmxoff;" "mov %0, eax":"=r"(EAX):"r"(&buff), "r"(i)); if (!EAX) break; } printf("Wrong flag\n"); return 0; }
最后,经过一天的折腾终于….
3. Berkeley
bpf 逆向,参考 bpf,ebpf一些原理以及逆向基于libbpf-bootstrap编写的bpf文件
状态不太好,先是忽略了 BitVec 是有符号数,然后是迟迟没有想到去爆破。
cipher = [0xf3, 0x27, 0x47, 0x1b, 0x8f, 0x09, 0xfb, 0x17, 0x70, 0x48, 0xb0, 0x53, 0x32, 0xdb, 0xc0, 0xb8, 0x63, 0x2d, 0x40, 0x4b, 0xf5, 0x16, 0xf0, 0x35, 0xe7, 0xdf, 0xea, 0xa2, 0x9c, 0x41, 0xb3, 0x25, 0xd7, 0x0c, 0x33, 0x9c, 0x7b, 0x5a, 0xcd, 0x13, 0xbb, 0xee, 0x3e, 0x0e, 0xf2, 0xcf, 0x35, 0xda, 0xaf, 0xa2, 0x66, 0x7d, 0x38, 0x37, 0x67, 0x1e, 0x1f, 0x6b, 0x7b, 0x30, 0x0b, 0x7a, 0x02, 0xa9, 0xc8, 0x61, 0x27, 0x41, 0xdb, 0x01, 0x22, 0x31, 0x6f, 0xb6, 0xd4, 0x1b, 0x04, 0xd3, 0x94, 0xb8, 0x46, 0xc7, 0x24, 0xcf, 0xbd, 0xaf, 0x0b, 0xdc, 0x2e, 0xbb, 0xb2, 0x71, 0xf4, 0x99, 0x57, 0x36, 0xd1, 0x95, 0x52, 0x92, 0xba, 0x6d, 0xf3, 0x30, 0x50, 0x59, 0x9b, 0xea, 0x2f, 0x83, 0xdc, 0xf0, 0xde, 0x57, 0xa1, 0xac, 0xd2, 0x51, 0xa2, 0x1d, 0x59, 0xa8, 0x00, 0xb6, 0xe2, 0x65, 0x41, 0x0c, 0x4f, 0xeb, 0xf0, 0x2e, 0x58, 0x2a, 0x1f, 0xf4, 0x95, 0x72, 0x88, 0x7c, 0xa9, 0x0e, 0xcb, 0x3c, 0x42, 0xb9, 0xf3, 0x49, 0x9b, 0x52, 0x98, 0x12, 0xa3, 0x17, 0x51, 0xc0, 0x59, 0x40, 0x0a, 0xbc, 0xe8, 0x4c, 0x04, 0xfb, 0x13, 0x0a, 0x17, 0x3f, 0xe6, 0x36, 0x97, 0xdf, 0xb3, 0xe2, 0x42, 0x7f, 0xf8, 0xcc, 0x0e, 0xd1, 0x77, 0xc4, 0xa8, 0x46, 0x48, 0xe3, 0xf1, 0x0a, 0xef, 0x94, 0x56, 0x54, 0x5b, 0xca, 0xbd, 0xdd, 0x7f, 0x56, 0x47, 0xc2, 0x99, 0xfa, 0x89, 0xcc, 0xe1, 0xb9, 0x3a, 0x78, 0xe2, 0x37, 0x58, 0x01, 0x1b, 0xc3, 0x4b, 0xe6, 0x8c, 0xf3, 0xe5, 0xb6, 0x71, 0x9e, 0x63, 0xaf, 0x11, 0xce, 0x87, 0xf6, 0x6e, 0xde, 0xc8, 0xb1, 0xd0, 0x7a, 0x15, 0x6c, 0x10, 0x08, 0x99, 0x7b, 0x22, 0x55, 0x10, 0x7a, 0x82, 0x73, 0xfc, 0x62, 0xcb, 0x34, 0xa7, 0xb7, 0x62, 0xfa, 0x6b, 0x9f] key = [0xc1, 0xd1, 0x02, 0x61, 0xd6, 0xf7, 0x13, 0xa2, 0x9b, 0x20, 0xd0, 0x4a, 0x8f, 0x7f, 0xee, 0xb9, 0x00, 0x63, 0x34, 0xb0, 0x33, 0xb7, 0x8a, 0x8b, 0x94, 0x60, 0x2e, 0x8e, 0x21, 0xff, 0x90, 0x82, 0xd5, 0x87, 0x96, 0x78, 0x22, 0xb6, 0x48, 0x6c, 0x45, 0xc7, 0x5a, 0x16, 0x80, 0xfd, 0xe4, 0x8c, 0xbf, 0x01, 0x1f, 0x4b, 0x79, 0x24, 0xa0, 0xb4, 0x23, 0x4d, 0x3b, 0xc5, 0x5d, 0x6f, 0x0d, 0xc9, 0xd4, 0xca, 0x55, 0xe0, 0x39, 0xad, 0x2b, 0xcd, 0x2c, 0xec, 0xc2, 0x6b, 0x30, 0xe6, 0x0c, 0xa8, 0x9a, 0x2f, 0xf6, 0xe8, 0xbb, 0x32, 0x57, 0xfb, 0x0b, 0x9d, 0xf2, 0x3f, 0xb5, 0xf9, 0x59, 0xe5, 0x10, 0xcf, 0x51, 0x41, 0xe9, 0x50, 0xdf, 0x26, 0x74, 0x58, 0xcb, 0x64, 0x54, 0x73, 0xab, 0xf4, 0xb2, 0x9f, 0x18, 0xf8, 0x4e, 0xfe, 0x08, 0x1d, 0x4f, 0x49, 0xd3, 0xac, 0x38, 0x12, 0x77, 0x11, 0x69, 0x07, 0x1c, 0x99, 0xb3, 0xe7, 0x3d, 0x05, 0xd8, 0xfc, 0x70, 0x46, 0x93, 0x09, 0x65, 0x89, 0xb1, 0xc6, 0x52, 0xfa, 0xd2, 0x0e, 0xa9, 0x17, 0xe3, 0x91, 0xa1, 0x68, 0x5b, 0x2a, 0xf0, 0xc3, 0x42, 0xcc, 0x29, 0xde, 0xdc, 0x85, 0x98, 0x31, 0x5c, 0xbc, 0x2d, 0xef, 0x5e, 0x7e, 0xaf, 0x67, 0x62, 0xa7, 0x56, 0x88, 0xa4, 0x43, 0x40, 0xe1, 0x37, 0x9e, 0x36, 0x76, 0x71, 0x84, 0xbd, 0x06, 0x8d, 0x47, 0x7d, 0x53, 0xd7, 0xc8, 0xce, 0x15, 0x92, 0x95, 0x4c, 0x28, 0x6d, 0x75, 0xeb, 0x7c, 0xf3, 0xbe, 0xaa, 0xb8, 0xed, 0x03, 0x3c, 0x27, 0x3e, 0x19, 0xdd, 0xa6, 0x66, 0x25, 0x1e, 0xc4, 0x6e, 0xc0, 0xe2, 0xdb, 0x3a, 0xd9, 0x81, 0xa5, 0x1b, 0xf5, 0x04, 0xae, 0xba, 0xea, 0x97, 0x83, 0x35, 0x44, 0xa3, 0x7a, 0x1a, 0xf1, 0x86, 0xda, 0x7b, 0x14, 0x72, 0x9c, 0x6a, 0x0f, 0x5f, 0x0a] cst32 = [0x80, 0x40, 0x20, 0x10, 0x08, 0x04, 0x02, 0x01] for i in range(256): cipher[i] = key.index(cipher[i]) ^ key[i] print(cipher) import z3 for i in range(32): c = z3.BitVec(f'x{i}', 8) s = z3.Solver() s.add(c & 0x80 == 0) # 万恶之源 s.add(c < 128) 不可以, 要用 s.add(c > 0),因为 BitVec 是有符号数 for j in range(8): s.add((~((cst32[j] + c) ^ c)) & 0xff == key.index(cipher[i * 8 + j])) if s.check() == z3.sat: print(chr(s.model()[c].as_long()), end='')
补充一些关于 bpf 逆向分析的细节
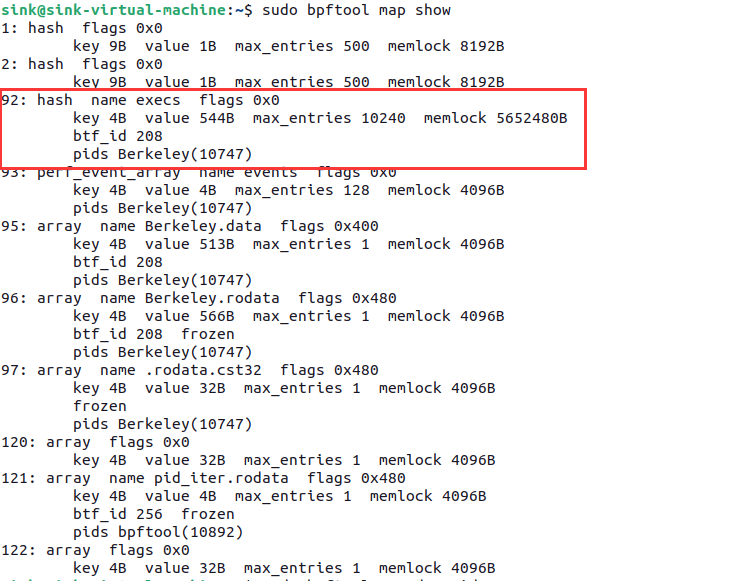
暂时没发现咋调试 bpf,但是可以通过 bpftool 查看执行后的某些值的变化,比如下面的这些
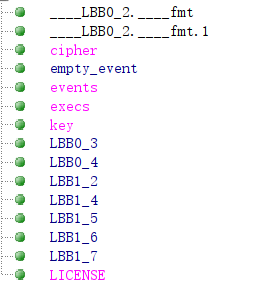
举个在解决这个题中非常有用的例子 execs ,
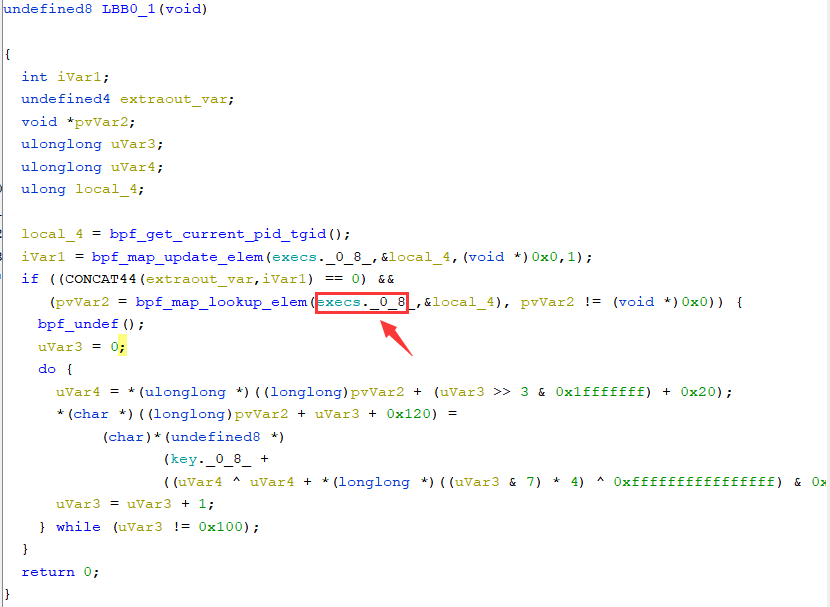
我们可以通过在 check_flag 函数下断点的方式来获取到在执行完 LBB0_1 之后的输出的值,即代码中偏移为 0x120 的部分,
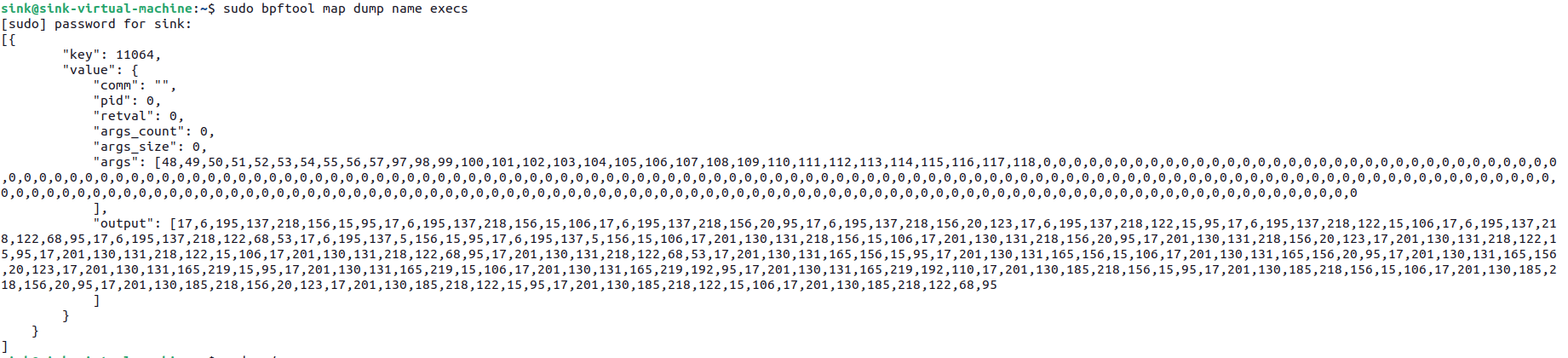
通过这种方法,可以输入 0-9a-f,建立输入和输出的映射关系,使用下面的脚本解决
# from idaapi import * # # # buf = get_bytes(0x30060, 8472) # f = open(r'D:\dump.bin', 'wb') # f.write(buf) # f.close() import string cipher = [0xf3, 0x27, 0x47, 0x1b, 0x8f, 0x09, 0xfb, 0x17, 0x70, 0x48, 0xb0, 0x53, 0x32, 0xdb, 0xc0, 0xb8, 0x63, 0x2d, 0x40, 0x4b, 0xf5, 0x16, 0xf0, 0x35, 0xe7, 0xdf, 0xea, 0xa2, 0x9c, 0x41, 0xb3, 0x25, 0xd7, 0x0c, 0x33, 0x9c, 0x7b, 0x5a, 0xcd, 0x13, 0xbb, 0xee, 0x3e, 0x0e, 0xf2, 0xcf, 0x35, 0xda, 0xaf, 0xa2, 0x66, 0x7d, 0x38, 0x37, 0x67, 0x1e, 0x1f, 0x6b, 0x7b, 0x30, 0x0b, 0x7a, 0x02, 0xa9, 0xc8, 0x61, 0x27, 0x41, 0xdb, 0x01, 0x22, 0x31, 0x6f, 0xb6, 0xd4, 0x1b, 0x04, 0xd3, 0x94, 0xb8, 0x46, 0xc7, 0x24, 0xcf, 0xbd, 0xaf, 0x0b, 0xdc, 0x2e, 0xbb, 0xb2, 0x71, 0xf4, 0x99, 0x57, 0x36, 0xd1, 0x95, 0x52, 0x92, 0xba, 0x6d, 0xf3, 0x30, 0x50, 0x59, 0x9b, 0xea, 0x2f, 0x83, 0xdc, 0xf0, 0xde, 0x57, 0xa1, 0xac, 0xd2, 0x51, 0xa2, 0x1d, 0x59, 0xa8, 0x00, 0xb6, 0xe2, 0x65, 0x41, 0x0c, 0x4f, 0xeb, 0xf0, 0x2e, 0x58, 0x2a, 0x1f, 0xf4, 0x95, 0x72, 0x88, 0x7c, 0xa9, 0x0e, 0xcb, 0x3c, 0x42, 0xb9, 0xf3, 0x49, 0x9b, 0x52, 0x98, 0x12, 0xa3, 0x17, 0x51, 0xc0, 0x59, 0x40, 0x0a, 0xbc, 0xe8, 0x4c, 0x04, 0xfb, 0x13, 0x0a, 0x17, 0x3f, 0xe6, 0x36, 0x97, 0xdf, 0xb3, 0xe2, 0x42, 0x7f, 0xf8, 0xcc, 0x0e, 0xd1, 0x77, 0xc4, 0xa8, 0x46, 0x48, 0xe3, 0xf1, 0x0a, 0xef, 0x94, 0x56, 0x54, 0x5b, 0xca, 0xbd, 0xdd, 0x7f, 0x56, 0x47, 0xc2, 0x99, 0xfa, 0x89, 0xcc, 0xe1, 0xb9, 0x3a, 0x78, 0xe2, 0x37, 0x58, 0x01, 0x1b, 0xc3, 0x4b, 0xe6, 0x8c, 0xf3, 0xe5, 0xb6, 0x71, 0x9e, 0x63, 0xaf, 0x11, 0xce, 0x87, 0xf6, 0x6e, 0xde, 0xc8, 0xb1, 0xd0, 0x7a, 0x15, 0x6c, 0x10, 0x08, 0x99, 0x7b, 0x22, 0x55, 0x10, 0x7a, 0x82, 0x73, 0xfc, 0x62, 0xcb, 0x34, 0xa7, 0xb7, 0x62, 0xfa, 0x6b, 0x9f] key = [0xc1, 0xd1, 0x02, 0x61, 0xd6, 0xf7, 0x13, 0xa2, 0x9b, 0x20, 0xd0, 0x4a, 0x8f, 0x7f, 0xee, 0xb9, 0x00, 0x63, 0x34, 0xb0, 0x33, 0xb7, 0x8a, 0x8b, 0x94, 0x60, 0x2e, 0x8e, 0x21, 0xff, 0x90, 0x82, 0xd5, 0x87, 0x96, 0x78, 0x22, 0xb6, 0x48, 0x6c, 0x45, 0xc7, 0x5a, 0x16, 0x80, 0xfd, 0xe4, 0x8c, 0xbf, 0x01, 0x1f, 0x4b, 0x79, 0x24, 0xa0, 0xb4, 0x23, 0x4d, 0x3b, 0xc5, 0x5d, 0x6f, 0x0d, 0xc9, 0xd4, 0xca, 0x55, 0xe0, 0x39, 0xad, 0x2b, 0xcd, 0x2c, 0xec, 0xc2, 0x6b, 0x30, 0xe6, 0x0c, 0xa8, 0x9a, 0x2f, 0xf6, 0xe8, 0xbb, 0x32, 0x57, 0xfb, 0x0b, 0x9d, 0xf2, 0x3f, 0xb5, 0xf9, 0x59, 0xe5, 0x10, 0xcf, 0x51, 0x41, 0xe9, 0x50, 0xdf, 0x26, 0x74, 0x58, 0xcb, 0x64, 0x54, 0x73, 0xab, 0xf4, 0xb2, 0x9f, 0x18, 0xf8, 0x4e, 0xfe, 0x08, 0x1d, 0x4f, 0x49, 0xd3, 0xac, 0x38, 0x12, 0x77, 0x11, 0x69, 0x07, 0x1c, 0x99, 0xb3, 0xe7, 0x3d, 0x05, 0xd8, 0xfc, 0x70, 0x46, 0x93, 0x09, 0x65, 0x89, 0xb1, 0xc6, 0x52, 0xfa, 0xd2, 0x0e, 0xa9, 0x17, 0xe3, 0x91, 0xa1, 0x68, 0x5b, 0x2a, 0xf0, 0xc3, 0x42, 0xcc, 0x29, 0xde, 0xdc, 0x85, 0x98, 0x31, 0x5c, 0xbc, 0x2d, 0xef, 0x5e, 0x7e, 0xaf, 0x67, 0x62, 0xa7, 0x56, 0x88, 0xa4, 0x43, 0x40, 0xe1, 0x37, 0x9e, 0x36, 0x76, 0x71, 0x84, 0xbd, 0x06, 0x8d, 0x47, 0x7d, 0x53, 0xd7, 0xc8, 0xce, 0x15, 0x92, 0x95, 0x4c, 0x28, 0x6d, 0x75, 0xeb, 0x7c, 0xf3, 0xbe, 0xaa, 0xb8, 0xed, 0x03, 0x3c, 0x27, 0x3e, 0x19, 0xdd, 0xa6, 0x66, 0x25, 0x1e, 0xc4, 0x6e, 0xc0, 0xe2, 0xdb, 0x3a, 0xd9, 0x81, 0xa5, 0x1b, 0xf5, 0x04, 0xae, 0xba, 0xea, 0x97, 0x83, 0x35, 0x44, 0xa3, 0x7a, 0x1a, 0xf1, 0x86, 0xda, 0x7b, 0x14, 0x72, 0x9c, 0x6a, 0x0f, 0x5f, 0x0a] map = [17, 6, 195, 137, 218, 156, 15, 95, 17, 6, 195, 137, 218, 156, 15, 106, 17, 6, 195, 137, 218, 156, 20, 95, 17, 6, 195, 137, 218, 156, 20, 123, 17, 6, 195, 137, 218, 122, 15, 95, 17, 6, 195, 137, 218, 122, 15, 106, 17, 6, 195, 137, 218, 122, 68, 95, 17, 6, 195, 137, 218, 122, 68, 53, 17, 6, 195, 137, 5, 156, 15, 95, 17, 6, 195, 137, 5, 156, 15, 106, 17, 201, 130, 131, 218, 156, 15, 106, 17, 201, 130, 131, 218, 156, 20, 95, 17, 201, 130, 131, 218, 156, 20, 123, 17, 201, 130, 131, 218, 122, 15, 95, 17, 201, 130, 131, 218, 122, 15, 106, 17, 201, 130, 131, 218, 122, 68, 95, 17, 201, 130, 131, 218, 122, 68, 53, 17, 201, 130, 131, 165, 156, 15, 95, 17, 201, 130, 131, 165, 156, 15, 106, 17, 201, 130, 131, 165, 156, 20, 95, 17, 201, 130, 131, 165, 156, 20, 123, 17, 201, 130, 131, 165, 219, 15, 95, 17, 201, 130, 131, 165, 219, 15, 106, 17, 201, 130, 131, 165, 219, 192, 95, 17, 201, 130, 131, 165, 219, 192, 110, 17, 201, 130, 185, 218, 156, 15, 95, 17, 201, 130, 185, 218, 156, 15, 106, 17, 201, 130, 185, 218, 156, 20, 95, 17, 201, 130, 185, 218, 156, 20, 123, 17, 201, 130, 185, 218, 122, 15, 95, 17, 201, 130, 185, 218, 122, 15, 106, 17, 201, 130, 185, 218, 122, 68, 95] for i in range(256): cipher[i] = key.index(cipher[i]) ^ key[i] for i in range(32): v = cipher[i * 8: (i + 1) * 8] for j in range(32): if v == map[j * 8: (j + 1) * 8]: print(string.printable[j], end='')




