sm4内核源码注释
内核版本:4.19.90
源码路径 crypto/sm4_generic.c
// SPDX-License-Identifier: GPL-2.0
/*
* SM4 Cipher Algorithm.
*
* Copyright (C) 2018 ARM Limited or its affiliates.
* All rights reserved.
*/
#include <crypto/sm4.h>
#include <linux/module.h>
#include <linux/init.h>
#include <linux/types.h>
#include <linux/errno.h>
#include <linux/crypto.h>
#include <asm/byteorder.h>
#include <asm/unaligned.h>
//4个32比特位的常量,用于辅助生成轮密钥
static const u32 fk[4] = {
0xa3b1bac6, 0x56aa3350, 0x677d9197, 0xb27022dc
};
//轮函数中的非线性变换(查表)将32比特的输入转化为对应的32比特的输出
static const u8 sbox[256] = {
0xd6, 0x90, 0xe9, 0xfe, 0xcc, 0xe1, 0x3d, 0xb7,
0x16, 0xb6, 0x14, 0xc2, 0x28, 0xfb, 0x2c, 0x05,
0x2b, 0x67, 0x9a, 0x76, 0x2a, 0xbe, 0x04, 0xc3,
0xaa, 0x44, 0x13, 0x26, 0x49, 0x86, 0x06, 0x99,
0x9c, 0x42, 0x50, 0xf4, 0x91, 0xef, 0x98, 0x7a,
0x33, 0x54, 0x0b, 0x43, 0xed, 0xcf, 0xac, 0x62,
0xe4, 0xb3, 0x1c, 0xa9, 0xc9, 0x08, 0xe8, 0x95,
0x80, 0xdf, 0x94, 0xfa, 0x75, 0x8f, 0x3f, 0xa6,
0x47, 0x07, 0xa7, 0xfc, 0xf3, 0x73, 0x17, 0xba,
0x83, 0x59, 0x3c, 0x19, 0xe6, 0x85, 0x4f, 0xa8,
0x68, 0x6b, 0x81, 0xb2, 0x71, 0x64, 0xda, 0x8b,
0xf8, 0xeb, 0x0f, 0x4b, 0x70, 0x56, 0x9d, 0x35,
0x1e, 0x24, 0x0e, 0x5e, 0x63, 0x58, 0xd1, 0xa2,
0x25, 0x22, 0x7c, 0x3b, 0x01, 0x21, 0x78, 0x87,
0xd4, 0x00, 0x46, 0x57, 0x9f, 0xd3, 0x27, 0x52,
0x4c, 0x36, 0x02, 0xe7, 0xa0, 0xc4, 0xc8, 0x9e,
0xea, 0xbf, 0x8a, 0xd2, 0x40, 0xc7, 0x38, 0xb5,
0xa3, 0xf7, 0xf2, 0xce, 0xf9, 0x61, 0x15, 0xa1,
0xe0, 0xae, 0x5d, 0xa4, 0x9b, 0x34, 0x1a, 0x55,
0xad, 0x93, 0x32, 0x30, 0xf5, 0x8c, 0xb1, 0xe3,
0x1d, 0xf6, 0xe2, 0x2e, 0x82, 0x66, 0xca, 0x60,
0xc0, 0x29, 0x23, 0xab, 0x0d, 0x53, 0x4e, 0x6f,
0xd5, 0xdb, 0x37, 0x45, 0xde, 0xfd, 0x8e, 0x2f,
0x03, 0xff, 0x6a, 0x72, 0x6d, 0x6c, 0x5b, 0x51,
0x8d, 0x1b, 0xaf, 0x92, 0xbb, 0xdd, 0xbc, 0x7f,
0x11, 0xd9, 0x5c, 0x41, 0x1f, 0x10, 0x5a, 0xd8,
0x0a, 0xc1, 0x31, 0x88, 0xa5, 0xcd, 0x7b, 0xbd,
0x2d, 0x74, 0xd0, 0x12, 0xb8, 0xe5, 0xb4, 0xb0,
0x89, 0x69, 0x97, 0x4a, 0x0c, 0x96, 0x77, 0x7e,
0x65, 0xb9, 0xf1, 0x09, 0xc5, 0x6e, 0xc6, 0x84,
0x18, 0xf0, 0x7d, 0xec, 0x3a, 0xdc, 0x4d, 0x20,
0x79, 0xee, 0x5f, 0x3e, 0xd7, 0xcb, 0x39, 0x48
};
//按照一定规则生成的常量,用于辅助生成32个长度为32比特位的轮密钥
static const u32 ck[] = {
0x00070e15, 0x1c232a31, 0x383f464d, 0x545b6269,
0x70777e85, 0x8c939aa1, 0xa8afb6bd, 0xc4cbd2d9,
0xe0e7eef5, 0xfc030a11, 0x181f262d, 0x343b4249,
0x50575e65, 0x6c737a81, 0x888f969d, 0xa4abb2b9,
0xc0c7ced5, 0xdce3eaf1, 0xf8ff060d, 0x141b2229,
0x30373e45, 0x4c535a61, 0x686f767d, 0x848b9299,
0xa0a7aeb5, 0xbcc3cad1, 0xd8dfe6ed, 0xf4fb0209,
0x10171e25, 0x2c333a41, 0x484f565d, 0x646b7279
};
//轮函数中的非线性变换,也就是查表。对32比特的输入,分为4个8比特的单位进行查表。
static u32 sm4_t_non_lin_sub(u32 x)
{
int i;
u8 *b = (u8 *)&x;
for (i = 0; i < 4; ++i)
b[i] = sbox[b[i]];
return x;
}
//密钥扩展中的非线性变换L’,用于得到轮密钥
// L'(B) = B ^ B<<<13 ^ B<<<23
static u32 sm4_key_lin_sub(u32 x)
{
return x ^ rol32(x, 13) ^ rol32(x, 23);
}
//轮函数中的线性变换L,输入为查表后的结果,用于得到本轮的最终输出
//L(B)= B ^ B<<<2 ^ B<<<10 ^ B <<<18 ^ B<<<24
static u32 sm4_enc_lin_sub(u32 x)
{
return x ^ rol32(x, 2) ^ rol32(x, 10) ^ rol32(x, 18) ^ rol32(x, 24);
}
//密钥扩展算法,先进行查表,然后作L‘变换
static u32 sm4_key_sub(u32 x)
{
return sm4_key_lin_sub(sm4_t_non_lin_sub(x));
}
//轮函数运算,先进行查表,然后作L变换
static u32 sm4_enc_sub(u32 x)
{
return sm4_enc_lin_sub(sm4_t_non_lin_sub(x));
}
//一轮轮变换的具体过程, x[1] ^ x[2] ^ x[3] ^ rk先做非线性变换(查表),再做一次L变换,最后与X[0]做一次^运算
//返回值为32比特长度的X[4], X[1] X[2] X[3] X[4]作为下一轮轮变换的输入
static u32 sm4_round(const u32 *x, const u32 rk)
{
return x[0] ^ sm4_enc_sub(x[1] ^ x[2] ^ x[3] ^ rk);
}
/**
* crypto_sm4_expand_key - Expands the SM4 key as described in GB/T 32907-2016
* @ctx: The location where the computed key will be stored.
* @in_key: The supplied key.
* @key_len: The length of the supplied key.
*
* Returns 0 on success. The function fails only if an invalid key size (or
* pointer) is supplied.
*/
//扩展加密密钥:输入为128比特的密钥,对密钥进行扩展得到32个长度为32比特的轮密钥
int crypto_sm4_expand_key(struct crypto_sm4_ctx *ctx, const u8 *in_key,
unsigned int key_len)
{
u32 rk[4], t;
const u32 *key = (u32 *)in_key;
int i;
//#define SM4_KEY_SIZE 16
//密钥长度为128比特,也就是16个字节
if (key_len != SM4_KEY_SIZE)
return -EINVAL;
//根据初始加密密钥(key[0] key[1] key[2] key[3]) 以及fk[0] fk[1] fk[2] fk[3] 生成K0,K1,K2,K3
//K0=key[0] ^ fk[0]
for (i = 0; i < 4; ++i)
rk[i] = get_unaligned_be32(&key[i]) ^ fk[i];
//生成轮密钥,轮密钥保存在ctx->rkey_enc[32]数组中
//rki=K(i+4)=Ki ^ T'(K(i+1) ^ K(i+2) ^ K(i+3) ^ CKi)
for (i = 0; i < 32; ++i) {
t = rk[0] ^ sm4_key_sub(rk[1] ^ rk[2] ^ rk[3] ^ ck[i]);
ctx->rkey_enc[i] = t;//存储加密轮密钥
//进行下一轮轮密钥生成迭代
rk[0] = rk[1];
rk[1] = rk[2];
rk[2] = rk[3];
rk[3] = t;
}
//解密轮密钥与加密轮密钥顺序相反
for (i = 0; i < 32; ++i)
ctx->rkey_dec[i] = ctx->rkey_enc[31 - i];
return 0;
}
EXPORT_SYMBOL_GPL(crypto_sm4_expand_key);
/**
* crypto_sm4_set_key - Set the AES key.
* @tfm: The %crypto_tfm that is used in the context.
* @in_key: The input key.
* @key_len: The size of the key.
*
* Returns 0 on success, on failure the %CRYPTO_TFM_RES_BAD_KEY_LEN flag in tfm
* is set. The function uses crypto_sm4_expand_key() to expand the key.
* &crypto_sm4_ctx _must_ be the private data embedded in @tfm which is
* retrieved with crypto_tfm_ctx().
*/
int crypto_sm4_set_key(struct crypto_tfm *tfm, const u8 *in_key,
unsigned int key_len)
{
struct crypto_sm4_ctx *ctx = crypto_tfm_ctx(tfm);
u32 *flags = &tfm->crt_flags;
int ret;
ret = crypto_sm4_expand_key(ctx, in_key, key_len);
if (!ret)
return 0;
*flags |= CRYPTO_TFM_RES_BAD_KEY_LEN;
return -EINVAL;
}
EXPORT_SYMBOL_GPL(crypto_sm4_set_key);
//加密的具体过程
//输入rk为
static void sm4_do_crypt(const u32 *rk, u32 *out, const u32 *in)
{
u32 x[4], i, t;
//得到原始的明文数据,共128比特位,4个u32类型的变量
for (i = 0; i < 4; ++i)
x[i] = get_unaligned_be32(&in[i]);
//对每个明文块(128比特的数据) 完成32轮迭代
for (i = 0; i < 32; ++i) {
//sm4_round完成每一轮迭代的具体过程,
//rk[i]为轮密钥,x为当前迭代轮的128比特的输入,t为当前轮的输出,t作为下一轮迭代输入X4(最后32比特值)
t = sm4_round(x, rk[i]);
//完成一轮迭代后,重新更新输入,作为下一轮的输入
x[0] = x[1];
x[1] = x[2];
x[2] = x[3];
x[3] = t;
}
//第32轮迭代的结果,反序输出作为最终的加密输出
for (i = 0; i < 4; ++i)
put_unaligned_be32(x[3 - i], &out[i]);
}
/* encrypt a block of text */
//完成一个分组数据的加密工作,分组大小:128比特
void crypto_sm4_encrypt(struct crypto_tfm *tfm, u8 *out, const u8 *in)
{
const struct crypto_sm4_ctx *ctx = crypto_tfm_ctx(tfm);
//ctx->rkey_enc为轮密钥数组
//out期望为128比特的加密输出结果
//in期望为128比特的明文消息
sm4_do_crypt(ctx->rkey_enc, (u32 *)out, (u32 *)in);
}
EXPORT_SYMBOL_GPL(crypto_sm4_encrypt);
/* decrypt a block of text */
//完成一个分组数据的解密工作,分组大小:128比特
void crypto_sm4_decrypt(struct crypto_tfm *tfm, u8 *out, const u8 *in)
{
const struct crypto_sm4_ctx *ctx = crypto_tfm_ctx(tfm);
//解密与加密流程相同,唯一的区别是两者的轮密钥互逆。加密[i]=解密[32-i]
sm4_do_crypt(ctx->rkey_dec, (u32 *)out, (u32 *)in);
}
EXPORT_SYMBOL_GPL(crypto_sm4_decrypt);
static struct crypto_alg sm4_alg = {
.cra_name = "sm4",
.cra_driver_name = "sm4-generic",
.cra_priority = 100,
.cra_flags = CRYPTO_ALG_TYPE_CIPHER,
.cra_blocksize = SM4_BLOCK_SIZE,//块大小16字节,即128比特
.cra_ctxsize = sizeof(struct crypto_sm4_ctx),
.cra_module = THIS_MODULE,
.cra_u = {
.cipher = {
.cia_min_keysize = SM4_KEY_SIZE,//密钥长度为16字节,即128比特
.cia_max_keysize = SM4_KEY_SIZE,//密钥长度为16字节,即128比特
.cia_setkey = crypto_sm4_set_key,//设置加密密钥,密钥长度128比特
.cia_encrypt = crypto_sm4_encrypt,//对一个数据块(128比特)进行加密
.cia_decrypt = crypto_sm4_decrypt//对一个数据块(128比特)进行解密
}
}
};
static int __init sm4_init(void)
{
return crypto_register_alg(&sm4_alg);
}
static void __exit sm4_fini(void)
{
crypto_unregister_alg(&sm4_alg);
}
module_init(sm4_init);
module_exit(sm4_fini);
MODULE_DESCRIPTION("SM4 Cipher Algorithm");
MODULE_LICENSE("GPL v2");
MODULE_ALIAS_CRYPTO("sm4");
MODULE_ALIAS_CRYPTO("sm4-generic");
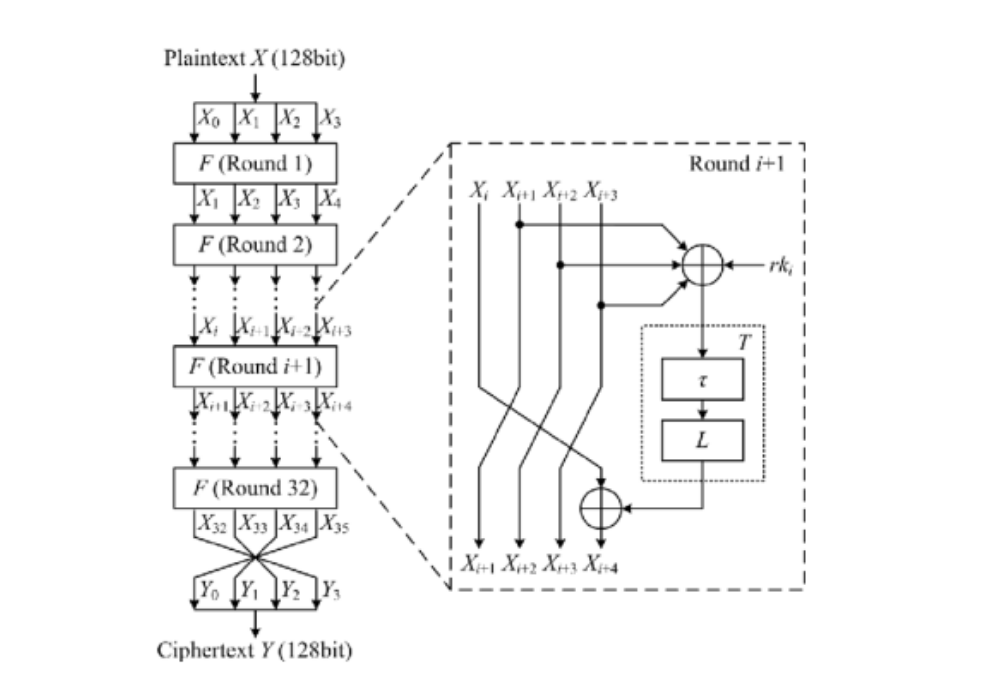
附1:sm4整体加密流程图 ref: https://blog.csdn.net/zhangpeterx/article/details/83654504
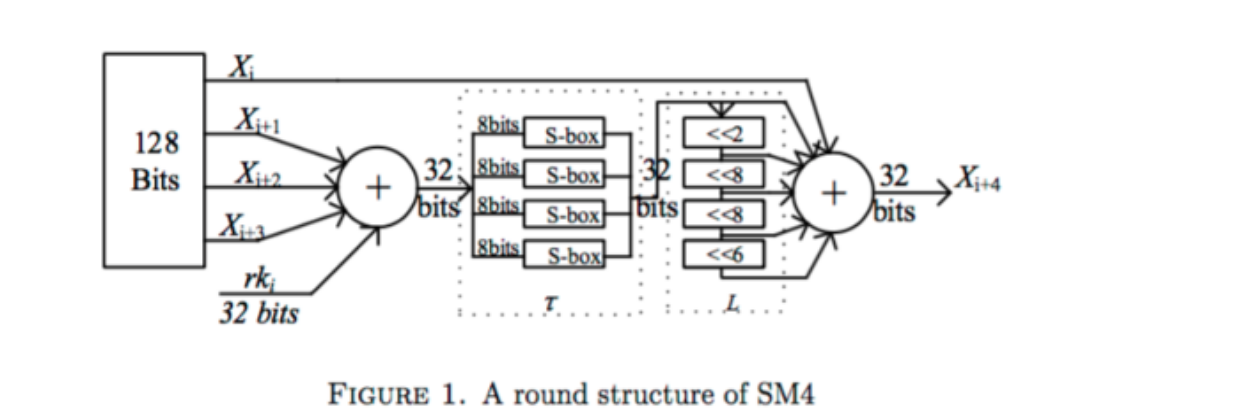
附2:sm4轮函数示意图 ref: https://blog.csdn.net/zhangpeterx/article/details/83654504



 浙公网安备 33010602011771号
浙公网安备 33010602011771号