NetworkPolicy Ingress及Egress简介及案例
一、NetworkPolicy简介
官方介绍:https://kubernetes.io/zh/docs/concepts/services-networking/network-policies/
基于NetworkPolicy在三层(网络层)或四层(传输层)控制拒绝或允许请求流量。
- 允许或拒绝特定的pod请求目的namespace中的目的pod的所有或指定端口。
- 允许或拒绝特定的namespace请求目的namespace中的所有或特定的pod所有或指定端口。
- 允许或拒绝特定的源IP范围或IP地址请求目的pod的所有或特定端口。
二、NetworkPolicy环境准备
2.1、环境条件
环境:
- 1.kubernetes 1.24.x, calico网络组件, 2个node节点或以上。
- 2.两个namespace, linux和python, 分别代表不同项目的Pod。
- 3.每个namespace 运行多个pod, 且pod可以运行在不同的node主机。
- 4.测试环境为每个namespace分别运行一个nginx和一个tomcat pod, 用于测试不同主机的Pod运行在同一个ns的场景、 以及跨ns的访问通信及访问限制。
创建namespace:
- # kubectl create ns linux
- # kubectl create ns python
- # kubectl label ns linux nsname=linux
- # kubectl label ns python nsname=python
2.2、部署测试web服务
1.linux ns部署nginx和tomcat, 并让nginx可以将来自于/app的请求转发至当前namespace的tomcat pod。
2.python ns部署nginx和tomcat, 并让nginx可以将来自于/app的请求转发至当前namespace的tomcat pod。
3.测试运行在linux ns的nginx能否将请求转发至运行在python ns的tomcat:
4.测试容器(创建多个pod用于后期从不同的节点进行测试):
- #创建测试Pod,用于测试访问目的nginx、 tomcat等业务pod:
- ~# kubectl run net-test-centos-pod1 --image=centos:7.9.2009 sleep 10000000 -n linux
- ~# kubectl run net-test-centos-pod1 --image=centos:7.9.2009 sleep 10000000 -n python
- ~# kubectl run centos-net-test1 --image=centos:7.9.2009 sleep 360000 #测试容器
[root@easzlab-deploy ~]# kubectl create ns linux namespace/linux created [root@easzlab-deploy ~]# kubectl create ns python namespace/python created [root@easzlab-deploy ~]# kubectl label ns linux nsname=linux namespace/linux labeled [root@easzlab-deploy ~]# kubectl label ns python nsname=python namespace/python labeled [root@easzlab-deploy ~]# kubectl run net-test-centos-pod1 --image=centos:7.9.2009 sleep 10000000 -n linux pod/net-test-centos-pod1 created [root@easzlab-deploy ~]# kubectl run net-test-centos-pod1 --image=centos:7.9.2009 sleep 10000000 -n python pod/net-test-centos-pod1 created [root@easzlab-deploy ~]# kubectl run centos-net-test1 --image=centos:7.9.2009 sleep 360000 pod/centos-net-test1 created [root@easzlab-deploy ~]# kubectl get pod -n linux -owide NAME READY STATUS RESTARTS AGE IP NODE NOMINATED NODE READINESS GATES net-test-centos-pod1 1/1 Running 0 80s 10.200.40.226 172.16.88.160 <none> <none> [root@easzlab-deploy ~]# kubectl get pod -n python -owide NAME READY STATUS RESTARTS AGE IP NODE NOMINATED NODE READINESS GATES net-test-centos-pod1 1/1 Running 0 77s 10.200.40.227 172.16.88.160 <none> <none> [root@easzlab-deploy ~]# [root@easzlab-deploy python-ns2]# kubectl get pod -owide NAME READY STATUS RESTARTS AGE IP NODE NOMINATED NODE READINESS GATES centos-net-test1 1/1 Running 0 3m58s 10.200.233.75 172.16.88.161 <none> <none> [root@easzlab-deploy python-ns2]#
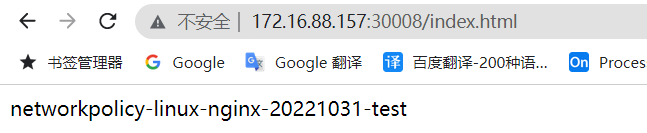
在linux-ns1下准备服务部署文件
[root@easzlab-deploy linux-ns1]# cat nginx.yaml kind: Deployment #apiVersion: extensions/v1beta1 apiVersion: apps/v1 metadata: labels: app: linux-nginx-deployment-label name: linux-nginx-deployment namespace: linux spec: replicas: 1 selector: matchLabels: app: linux-nginx-selector template: metadata: labels: app: linux-nginx-selector spec: containers: - name: linux-nginx-container image: nginx:1.20.2-alpine #command: ["/apps/tomcat/bin/run_tomcat.sh"] #imagePullPolicy: IfNotPresent imagePullPolicy: Always ports: - containerPort: 80 protocol: TCP name: http - containerPort: 443 protocol: TCP name: https env: - name: "password" value: "123456" - name: "age" value: "18" # resources: # limits: # cpu: 2 # memory: 2Gi # requests: # cpu: 500m # memory: 1Gi --- kind: Service apiVersion: v1 metadata: labels: app: linux-nginx-service-label name: linux-nginx-service namespace: linux spec: type: NodePort ports: - name: http port: 80 protocol: TCP targetPort: 80 nodePort: 30008 - name: https port: 443 protocol: TCP targetPort: 443 nodePort: 30443 selector: app: linux-nginx-selector [root@easzlab-deploy linux-ns1]# [root@easzlab-deploy linux-ns1]# cat tomcat.yaml kind: Deployment #apiVersion: extensions/v1beta1 apiVersion: apps/v1 metadata: labels: app: linux-tomcat-app1-deployment-label name: linux-tomcat-app1-deployment namespace: linux spec: replicas: 1 selector: matchLabels: app: linux-tomcat-app1-selector template: metadata: labels: app: linux-tomcat-app1-selector spec: containers: - name: linux-tomcat-app1-container image: tomcat:7.0.109-jdk8-openjdk #command: ["/apps/tomcat/bin/run_tomcat.sh"] #imagePullPolicy: IfNotPresent imagePullPolicy: Always ports: - containerPort: 8080 protocol: TCP name: http env: - name: "password" value: "123456" - name: "age" value: "18" # resources: # limits: # cpu: 2 # memory: 2Gi # requests: # cpu: 500m # memory: 1Gi --- kind: Service apiVersion: v1 metadata: labels: app: linux-tomcat-app1-service-label name: linux-tomcat-app1-service namespace: linux spec: type: NodePort ports: - name: http port: 80 protocol: TCP targetPort: 8080 nodePort: 30006 selector: app: linux-tomcat-app1-selector [root@easzlab-deploy linux-ns1]# [root@easzlab-deploy linux-ns1]# kubectl apply -f nginx.yaml deployment.apps/linux-nginx-deployment created service/linux-nginx-service created [root@easzlab-deploy linux-ns1]# [root@easzlab-deploy linux-ns1]# kubectl apply -f tomcat.yaml deployment.apps/linux-tomcat-app1-deployment created service/linux-tomcat-app1-service created [root@easzlab-deploy linux-ns1]# [root@easzlab-deploy linux-ns1]# kubectl get pod -n linux -owide NAME READY STATUS RESTARTS AGE IP NODE NOMINATED NODE READINESS GATES linux-nginx-deployment-864bcf5f4c-vnssz 1/1 Running 0 2m27s 10.200.40.228 172.16.88.160 <none> <none> linux-tomcat-app1-deployment-78c6ff7749-l6sf2 1/1 Running 0 2m21s 10.200.40.229 172.16.88.160 <none> <none> net-test-centos-pod1 1/1 Running 0 3h10m 10.200.40.226 172.16.88.160 <none> <none> [root@easzlab-deploy linux-ns1]# [root@easzlab-deploy linux-ns1]# kubectl get svc -n linux NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE linux-nginx-service NodePort 10.100.89.84 <none> 80:30008/TCP,443:30443/TCP 2m51s linux-tomcat-app1-service NodePort 10.100.238.159 <none> 80:30006/TCP 2m44s [root@easzlab-deploy linux-ns1]#
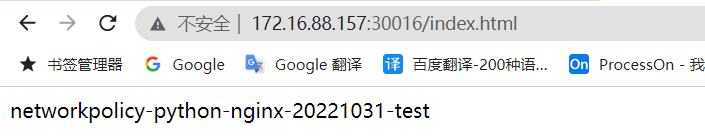
在python-ns2文件下准备部署文件
[root@easzlab-deploy python-ns2]# cat nginx.yaml kind: Deployment #apiVersion: extensions/v1beta1 apiVersion: apps/v1 metadata: labels: app: python-nginx-deployment-label name: python-nginx-deployment namespace: python spec: replicas: 1 selector: matchLabels: app: python-nginx-selector template: metadata: labels: app: python-nginx-selector project: python spec: containers: - name: python-nginx-container image: nginx:1.20.2-alpine #command: ["/apps/tomcat/bin/run_tomcat.sh"] #imagePullPolicy: IfNotPresent imagePullPolicy: Always ports: - containerPort: 80 protocol: TCP name: http - containerPort: 443 protocol: TCP name: https env: - name: "password" value: "123456" - name: "age" value: "18" # resources: # limits: # cpu: 2 # memory: 2Gi # requests: # cpu: 500m # memory: 1Gi --- kind: Service apiVersion: v1 metadata: labels: app: python-nginx-service-label name: python-nginx-service namespace: python spec: type: NodePort ports: - name: http port: 80 protocol: TCP targetPort: 80 nodePort: 30016 - name: https port: 443 protocol: TCP targetPort: 443 nodePort: 30456 selector: app: python-nginx-selector project: python #一个或多个selector,至少能匹配目标pod的一个标签 [root@easzlab-deploy python-ns2]# [root@easzlab-deploy python-ns2]# cat tomcat.yaml kind: Deployment #apiVersion: extensions/v1beta1 apiVersion: apps/v1 metadata: labels: app: python-tomcat-app1-deployment-label name: python-tomcat-app1-deployment namespace: python spec: replicas: 1 selector: matchLabels: app: python-tomcat-app1-selector template: metadata: labels: app: python-tomcat-app1-selector spec: nodeName: 172.16.88.160 containers: - name: python-tomcat-app1-container image: tomcat:7.0.109-jdk8-openjdk #command: ["/apps/tomcat/bin/run_tomcat.sh"] #imagePullPolicy: IfNotPresent imagePullPolicy: Always ports: - containerPort: 8080 protocol: TCP name: http env: - name: "password" value: "123456" - name: "age" value: "18" # resources: # limits: # cpu: 2 # memory: 2Gi # requests: # cpu: 500m # memory: 1Gi --- kind: Service apiVersion: v1 metadata: labels: app: python-tomcat-app1-service-label name: python-tomcat-app1-service namespace: python spec: type: NodePort ports: - name: http port: 80 protocol: TCP targetPort: 8080 nodePort: 30015 selector: app: python-tomcat-app1-selector [root@easzlab-deploy python-ns2]# [root@easzlab-deploy python-ns2]# kubectl apply -f nginx.yaml deployment.apps/python-nginx-deployment created service/python-nginx-service created [root@easzlab-deploy python-ns2]# [root@easzlab-deploy python-ns2]# kubectl apply -f tomcat.yaml deployment.apps/python-tomcat-app1-deployment created service/python-tomcat-app1-service created [root@easzlab-deploy python-ns2]# [root@easzlab-deploy python-ns2]# kubectl get pod -n python -owide NAME READY STATUS RESTARTS AGE IP NODE NOMINATED NODE READINESS GATES net-test-centos-pod1 1/1 Running 0 5h47m 10.200.40.227 172.16.88.160 <none> <none> python-nginx-deployment-5c658bf86b-l4q6h 1/1 Running 0 152m 10.200.40.230 172.16.88.160 <none> <none> python-tomcat-app1-deployment-5b9c8d6d9c-958lp 1/1 Running 0 58m 10.200.40.234 172.16.88.160 <none> <none> [root@easzlab-deploy python-ns2]# [root@easzlab-deploy python-ns2]# kubectl get svc -n python NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE python-nginx-service NodePort 10.100.151.110 <none> 80:30016/TCP,443:30456/TCP 152m python-tomcat-app1-service NodePort 10.100.179.187 <none> 80:30015/TCP 58m [root@easzlab-deploy python-ns2]#
创建nginx测试页面
[root@easzlab-deploy python-ns2]# kubectl exec -it -n linux linux-nginx-deployment-864bcf5f4c-vnssz sh kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead./ # cd /usr/share/nginx/html/ /usr/share/nginx/html # echo "networkpolicy-linux-nginx-20221031-test" > index.html /usr/share/nginx/html # [root@easzlab-deploy python-ns2]# kubectl exec -it -n python python-nginx-deployment-5c658bf86b-l4q6h sh kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. / # cd /usr/share/nginx/html//usr/share/nginx/html # echo "networkpolicy-python-nginx-20221031-test" > index.html /usr/share/nginx/html #
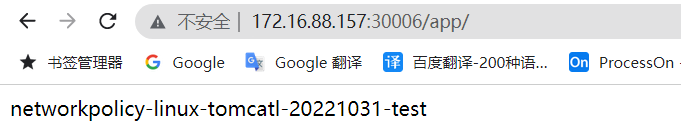
创建tomcat测试页面
[root@easzlab-deploy python-ns2]# kubectl exec -it -n linux linux-tomcat-app1-deployment-78c6ff7749-l6sf2 bash kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. root@linux-tomcat-app1-deployment-78c6ff7749-l6sf2:/usr/local/tomcat# cd webapps root@linux-tomcat-app1-deployment-78c6ff7749-l6sf2:/usr/local/tomcat/webapps# mkdir app root@linux-tomcat-app1-deployment-78c6ff7749-l6sf2:/usr/local/tomcat/webapps# echo "networkpolicy-linux-tomcatl-20221031-test" > app/index.jsp root@linux-tomcat-app1-deployment-78c6ff7749-l6sf2:/usr/local/tomcat/webapps# [root@easzlab-deploy python-ns2]# kubectl exec -it -n python python-tomcat-app1-deployment-5b9c8d6d9c-958lp bash kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. root@python-tomcat-app1-deployment-5b9c8d6d9c-d4f5b:/usr/local/tomcat# cd webapps root@python-tomcat-app1-deployment-5b9c8d6d9c-d4f5b:/usr/local/tomcat/webapps# mkdir app root@python-tomcat-app1-deployment-5b9c8d6d9c-d4f5b:/usr/local/tomcat/webapps# echo "networkpolicy-python-tomcatl-20221031-test" > app/index.jsp root@python-tomcat-app1-deployment-5b9c8d6d9c-d4f5b:/usr/local/tomcat/webapps#
三、NetworkPolicy应用场景
3.1、ingress-以pod为限制单位、 只允同namespace含有特定标签的源pod访问目标pod的所有端口
[root@easzlab-deploy python-ns2]# cat case1-ingress-podSelector.yaml
apiVersion: networking.k8s.io/v1
kind: NetworkPolicy
metadata:
name: tomcat-access--networkpolicy
namespace: python
spec:
policyTypes:
- Ingress
podSelector:
matchLabels:
app: python-tomcat-app1-selector #对匹配到的目的Pod应用以下规则
ingress: #入栈规则,如果指定目标端口就是匹配全部端口和协议,协议TCP, UDP, or SCTP
- from:
- podSelector:
matchLabels:
#app: python-nginx-selector #如果存在多个matchLabel条件,如果存在多个matchLabel条件,是and的关系,即要同时满足条件A、条件B、条件X
project: "python"
[root@easzlab-deploy python-ns2]#
结果:
1.不允许从其它namespace访问目标pod, 即默认禁止了跨ns访问目标pod。
- # kubectl exec -it net-test-centos-pod1 bash
- # curl python-tomcat-app1-service.python.svc.magedu.local/app/index.jsp #来自于default ns的请求会被禁止
2.非明确允许的pod, 同namespace 也无法访问
3.不允许从宿主机访问目标pod。
4.该策略只允许同namespace含有特定标签的源pod访问目标pod, 比如tomcat只允许了有特定标签的源pod nginx访问。
5.该策略不影响其它namespace的pod内部之间的相互访问, 即linux的pod与linux的pod访问正常。
6.该策略不影响各namespace的pod与非明确禁止的pod之间的访问, 即linux的pod访问python的其它pod也正常。
验证结果
[root@easzlab-deploy python-ns2]# kubectl get pod -n python -owide NAME READY STATUS RESTARTS AGE IP NODE NOMINATED NODE READINESS GATES net-test-centos-pod1 1/1 Running 0 9h 10.200.40.227 172.16.88.160 <none> <none> python-nginx-deployment-5c658bf86b-l4q6h 1/1 Running 0 6h1m 10.200.40.230 172.16.88.160 <none> <none> python-tomcat-app1-deployment-5b9c8d6d9c-958lp 1/1 Running 0 4h27m 10.200.40.234 172.16.88.160 <none> <none> [root@easzlab-deploy python-ns2]# kubectl get pod -n linux -owide NAME READY STATUS RESTARTS AGE IP NODE NOMINATED NODE READINESS GATES linux-nginx-deployment-864bcf5f4c-vnssz 1/1 Running 0 6h8m 10.200.40.228 172.16.88.160 <none> <none> linux-tomcat-app1-deployment-78c6ff7749-l6sf2 1/1 Running 0 6h8m 10.200.40.229 172.16.88.160 <none> <none> net-test-centos-pod1 1/1 Running 0 9h 10.200.40.226 172.16.88.160 <none> <none> [root@easzlab-deploy python-ns2]#
#启用networkpolicy策略 [root@easzlab-deploy python-ns2]# kubectl create -f case1-ingress-podSelector.yaml networkpolicy.networking.k8s.io/tomcat-access--networkpolicy created [root@easzlab-deploy python-ns2]# #测试普通pod访问linux、python 命名空间下资源 [root@easzlab-deploy python-ns2]# kubectl exec -it centos-net-test1 bash kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. [root@centos-net-test1 /]# curl http://10.200.40.230/index.html #正常访问python 命名空间下nginx pod 80端口 networkpolicy-python-nginx-20221031-test [root@centos-net-test1 /]# [root@centos-net-test1 /]# curl http://10.200.40.234:8080/app/index.jsp #访问python命名空间tomcat pod 8080失败 ^C [root@centos-net-test1 /]# [root@centos-net-test1 /]# curl http://10.200.40.228/index.html #访问linux命名空间nginx pod 80 端口正常 networkpolicy-linux-nginx-20221031-test [root@centos-net-test1 /]# [root@centos-net-test1 /]# curl http://10.200.40.229:8080/app/index.jsp #访问linux 命名空间下tomcat pod 8080 端口正常 networkpolicy-linux-tomcatl-20221031-test [root@centos-net-test1 /]#
#测试python 命名空间下测试pod访问 [root@easzlab-deploy python-ns2]# kubectl exec -it -n python net-test-centos-pod1 bash kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. [root@net-test-centos-pod1 /]# [root@net-test-centos-pod1 /]# curl http://10.200.40.230/index.html #访问python 命名空间下nginx pod 80端口正常 networkpolicy-python-nginx-20221031-test [root@net-test-centos-pod1 /]# curl http://10.200.40.234:8080/app/index.jsp #访问python 命名空间下tomcat pod 8080 端口失败 ^C [root@net-test-centos-pod1 /]# [root@net-test-centos-pod1 /]# curl http://10.200.40.228/index.html #访问linux 命名空间下nginx pod 80 端口正常 networkpolicy-linux-nginx-20221031-test [root@net-test-centos-pod1 /]# [root@net-test-centos-pod1 /]# curl http://10.200.40.229:8080/app/index.jsp #访问linux命名空间下tomcat pod 8080 端口正常 networkpolicy-linux-tomcatl-20221031-test [root@net-test-centos-pod1 /]#
#测试linux命名空间下测试pod访问 [root@easzlab-deploy python-ns2]# kubectl exec -it -n linux net-test-centos-pod1 bash kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. [root@net-test-centos-pod1 /]# [root@net-test-centos-pod1 /]# curl http://10.200.40.230/index.html #访问python 命名空间下nginx pod 80 端口正常 networkpolicy-python-nginx-20221031-test [root@net-test-centos-pod1 /]# curl http://10.200.40.234:8080/app/index.jsp #访问python 命名空间下tomcat pod 8080端口失败 ^C [root@net-test-centos-pod1 /]# [root@net-test-centos-pod1 /]# curl http://10.200.40.228/index.html #访问linux命名空间下nginx pod 80 端口正常 networkpolicy-linux-nginx-20221031-test [root@net-test-centos-pod1 /]# [root@net-test-centos-pod1 /]# curl http://10.200.40.229:8080/app/index.jsp #访问linux 命名空间下tomcat pod 8080端口正常 networkpolicy-linux-tomcatl-20221031-test [root@net-test-centos-pod1 /]#
3.2、ingress-以pod加端口为限制单位、 只允同namespace含有特定标签的源pod访问目标pod的指定端口
- 1.只允许指定的源pod访问同namespace目标pod的指定端口
- 2.非允许的端口将被禁止访问
[root@easzlab-deploy python-ns2]# vim case2-ingress-podSelector-ns-SinglePort.yaml [root@easzlab-deploy python-ns2]# cat case2-ingress-podSelector-ns-SinglePort.yaml apiVersion: networking.k8s.io/v1 kind: NetworkPolicy metadata: name: tomcat-access--networkpolicy namespace: python spec: policyTypes: - Ingress podSelector: matchLabels: app: python-tomcat-app1-selector ingress: - from: - podSelector: matchLabels: #app: python-nginx-selector #指定访问源的匹配条件,如果存在多个matchLabel条件,是and的关系,即要同时满足条件A、条件B、条件X project: "python" ports: #入栈规则,如果指定目标端口就是匹配全部端口和协议,协议TCP, UDP, or SCTP - protocol: TCP port: 8080 #允许通过TCP协议访问目标pod的8080端口,但是其它没有允许的端口将全部禁止访问 #port: 80 [root@easzlab-deploy python-ns2]#
验证结果
[root@easzlab-deploy python-ns2]# kubectl get pod -n python -owide NAME READY STATUS RESTARTS AGE IP NODE NOMINATED NODE READINESS GATES net-test-centos-pod1 1/1 Running 0 10h 10.200.40.227 172.16.88.160 <none> <none> python-nginx-deployment-5c658bf86b-q9xnf 1/1 Running 0 59s 10.200.40.235 172.16.88.160 <none> <none> python-tomcat-app1-deployment-7bf9bb6989-jbxhj 1/1 Running 0 59s 10.200.40.236 172.16.88.160 <none> <none> [root@easzlab-deploy python-ns2]#
#未启用networkpolicy策略,python命名空间下nginx可以正常访问tomcat 8080 [root@easzlab-deploy python-ns2]# kubectl exec -it -n python python-nginx-deployment-5c658bf86b-q9xnf sh kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. / # curl http://10.200.40.236:8080/app/index.jsp networkpolicy-python-tomcatl-20221031-test / #
#启用networkpolicy策略 [root@easzlab-deploy python-ns2]# grep port case2-ingress-podSelector-ns-SinglePort.yaml ports: #入栈规则,如果指定目标端口就是匹配全部端口和协议,协议TCP, UDP, or SCTP port: 8080 #允许通过TCP协议访问目标pod的8080端口,但是其它没有允许的端口将全部禁止访问 #port: 80 [root@easzlab-deploy python-ns2]# kubectl apply -f case2-ingress-podSelector-ns-SinglePort.yaml #启用networkpolicy策略 networkpolicy.networking.k8s.io/tomcat-access--networkpolicy created [root@easzlab-deploy python-ns2]# [root@easzlab-deploy python-ns2]# kubectl exec -it -n python python-nginx-deployment-5c658bf86b-q9xnf sh kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead./ # curl http://10.200.40.236:8080/app/index.jsp networkpolicy-python-tomcatl-20221031-test / # / # curl http://10.200.40.236:8080/app/index.jsp #此时python命名空间下nginx pod 还可以正常访问 networkpolicy-python-tomcatl-20221031-test / #
#修改networkpolicy策略之前的8080为80 [root@easzlab-deploy python-ns2]# vi case2-ingress-podSelector-ns-SinglePort.yaml [root@easzlab-deploy python-ns2]# grep port case2-ingress-podSelector-ns-SinglePort.yaml ports: #入栈规则,如果指定目标端口就是匹配全部端口和协议,协议TCP, UDP, or SCTP #port: 8080 #允许通过TCP协议访问目标pod的8080端口,但是其它没有允许的端口将全部禁止访问 port: 80 [root@easzlab-deploy python-ns2]# [root@easzlab-deploy python-ns2]# kubectl apply -f case2-ingress-podSelector-ns-SinglePort.yaml #重新加载networkpolicy策略 networkpolicy.networking.k8s.io/tomcat-access--networkpolicy configured [root@easzlab-deploy python-ns2]# root@easzlab-deploy python-ns2]# kubectl exec -it -n python python-nginx-deployment-5c658bf86b-q9xnf sh kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead./ # curl http://10.200.40.236:8080/app/index.jsp networkpolicy-python-tomcatl-20221031-test / # / # curl http://10.200.40.236:8080/app/index.jsp networkpolicy-python-tomcatl-20221031-test / # / # curl http://10.200.40.236:8080/app/index.jsp #此时python命名空间下nginx pod 访问失败 ^C / #
3.3、ingress-允许同namespace的所有pod访问当前namespace的目标pod多个指定端口
[root@easzlab-deploy python-ns2]# vim case3-ingress-podSelector-ns-MultiPort.yaml [root@easzlab-deploy python-ns2]# cat case3-ingress-podSelector-ns-MultiPort.yaml apiVersion: networking.k8s.io/v1 kind: NetworkPolicy metadata: name: tomcat-access-networkpolicy namespace: python spec: policyTypes: - Ingress podSelector: #目标pod matchLabels: app: python-tomcat-app1-selector ingress: - from: - podSelector: #匹配源pod,matchLabels: {}为不限制源pod即允许所有pod,写法等同于resources(不加就是不限制) matchLabels: {} ports: #入栈规则,如果指定目标端口就是匹配全部端口和协议,协议TCP, UDP, or SCTP - protocol: TCP port: 8080 #允许通过TCP协议访问目标pod的8080端口,但是其它没有允许的端口将全部禁止访问 #port: 80 - protocol: TCP port: 3306 - protocol: TCP port: 6379 [root@easzlab-deploy python-ns2]#
验证结果
[root@easzlab-deploy python-ns2]# kubectl apply -f case3-ingress-podSelector-ns-MultiPort.yaml #启用networkpolicy策略 networkpolicy.networking.k8s.io/tomcat-access-networkpolicy created [root@easzlab-deploy python-ns2]# #普通pod访问测试 [root@easzlab-deploy python-ns2]# kubectl exec -it centos-net-test1 bash kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. [root@centos-net-test1 /]# curl http://10.200.40.236:8080/app/index.jsp ^C [root@centos-net-test1 /]# #python 命名空间下pod访问 [root@easzlab-deploy python-ns2]# kubectl exec -it -n python python-nginx-deployment-5c658bf86b-q9xnf sh kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. / # / # curl http://10.200.40.236:8080/app/index.jsp networkpolicy-python-tomcatl-20221031-test / # [root@easzlab-deploy python-ns2]# kubectl exec -it -n python net-test-centos-pod1 bash kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. [root@net-test-centos-pod1 /]# curl http://10.200.40.236:8080/app/index.jsp networkpolicy-python-tomcatl-20221031-test [root@net-test-centos-pod1 /]# #linux命名空间下pod访问 [root@easzlab-deploy python-ns2]# kubectl exec -it -n linux net-test-centos-pod1 bash kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. [root@net-test-centos-pod1 /]# [root@net-test-centos-pod1 /]# curl 10.200.40.236:8080/app/index.jsp ^C [root@net-test-centos-pod1 /]#
拒绝访问的规则
[root@easzlab-k8s-node-01 ~]# iptables-save |grep 6379 (pod所在主机,其他主机无此规则) -A cali-pi-_0JuoNaejpHrnq9ok3ft -p tcp -m comment --comment "cali:qEZjDE_j-MWialKp" -m set --match-set cali40s:i_4-mErXOxx3I3EQOxm4JCQ src -m multiport --dports 3306,6379,8080 -j MARK --set-xmark 0x10000/0x10000 [root@easzlab-k8s-node-01 ~]#
3.4、ingress-允许同namespace的所有pod访问当前namespace的目标pod所有端口
[root@easzlab-deploy python-ns2]# cat case4-ingress-podSelector-ns.yaml apiVersion: networking.k8s.io/v1 kind: NetworkPolicy metadata: name: tomcat-access--networkpolicy namespace: python spec: policyTypes: - Ingress podSelector: #目标pod matchLabels: {} #匹配所有目标pod ingress: - from: - podSelector: #匹配源pod,matchLabels: {}为不限制源pod即允许所有pod,写法等同于resources(不加就是不限制) matchLabels: {} #ports: #入栈规则,如果指定目标端口就是匹配全部端口和协议,协议TCP, UDP, or SCTP #- protocol: TCP # port: {} #允许通过TCP协议访问目标pod的8080端口,但是其它没有允许的端口将全部禁止访问 #port: 80 #- protocol: TCP # port: 3306 #- protocol: TCP # port: 6379 [root@easzlab-deploy python-ns2]#
1.其它namespace无法访问目标ns的pod。
2.同namespace的pod可以访问当前namespace中的所有pod的任意端口。
验证结果
[root@easzlab-deploy python-ns2]# kubectl apply -f case4-ingress-podSelector-ns.yaml #启用networkpolicy策略 networkpolicy.networking.k8s.io/tomcat-access--networkpolicy created [root@easzlab-deploy python-ns2]#
#普通pod访问 [root@easzlab-deploy python-ns2]# kubectl exec -it centos-net-test1 bash kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. [root@centos-net-test1 /]# curl http://10.200.40.236:8080/app/index.jsp ^C [root@centos-net-test1 /]#
#python命名空间下pod访问 [root@easzlab-deploy python-ns2]# kubectl exec -it -n python net-test-centos-pod1 bash kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. [root@net-test-centos-pod1 /]# curl http://10.200.40.236:8080/app/index.jsp networkpolicy-python-tomcatl-20221031-test [root@net-test-centos-pod1 /]# [root@net-test-centos-pod1 /]# curl http://10.200.40.236:8080/app/index.jsp networkpolicy-python-tomcatl-20221031-test [root@net-test-centos-pod1 /]# [root@easzlab-deploy python-ns2]# kubectl exec -it -n python python-nginx-deployment-5c658bf86b-q9xnf sh kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. / # curl http://10.200.40.236:8080/app/index.jsp networkpolicy-python-tomcatl-20221031-test / #
#linux命名空间下pod访问 [root@easzlab-deploy python-ns2]# kubectl exec -it -n linux net-test-centos-pod1 bash kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. [root@net-test-centos-pod1 /]# curl 10.200.40.236:8080/app/index.jsp curl: (7) Failed connect to 10.200.40.236:8080; Connection timed out [root@net-test-centos-pod1 /]#
3.5、ingress-ipBlock白名单
[root@easzlab-deploy python-ns2]# cat case5-ingress-ipBlock.yaml.bak apiVersion: networking.k8s.io/v1 kind: NetworkPolicy metadata: name: tomcat-access--networkpolicy namespace: python spec: policyTypes: - Ingress podSelector: #目标pod matchLabels: app: python-tomcat-app1-selector ingress: - from: # - podSelector: #匹配源pod,matchLabels: {}为不限制源pod即允许所有pod,写法等同于resources(不加就是不限制) # matchLabels: {} - ipBlock: cidr: 10.200.0.0/16 #白名单,允许访问的地址范围,没有允许的将禁止访问目标pod except:
- 10.200.40.0/24 - 10.200.219.0/24 #在以上范围内禁止访问的源IP地址 - 10.200.229.0/24 #在以上范围内禁止访问的源IP地址 - 10.200.207.31/32 #在以上范围内禁止访问的源IP地址 ports: #入栈规则,如果指定目标端口就是匹配全部端口和协议,协议TCP, UDP, or SCTP - protocol: TCP port: 8080 #允许通过TCP协议访问目标pod的8080端口,但是其它没有允许的端口将全部禁止访问 #port: 80 - protocol: TCP port: 3306 - protocol: TCP port: 6379 [root@easzlab-deploy python-ns2]#
1.只要在白名单范围内没有被except指定禁止的源pod IP,都允许访问。
2.在只设置了ipBlock匹配的前提下,其它namespace 中没有在except范围的pod 也可以访问目标pod,及linux ns中的pod只要不在except地址范围内,也可以访问python ns中的pod了。
验证结果
[root@easzlab-deploy python-ns2]# kubectl apply -f case5-ingress-ipBlock.yaml #启用ip白名单 networkpolicy.networking.k8s.io/tomcat-access--networkpolicy configured [root@easzlab-deploy python-ns2]# [root@easzlab-deploy python-ns2]# kubectl exec -it -n python net-test-centos-pod1 bash kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. [root@net-test-centos-pod1 /]# [root@net-test-centos-pod1 /]# curl http://10.200.40.236:8080/app/index.jsp networkpolicy-python-tomcatl-20221031-test [root@net-test-centos-pod1 /]# curl http://10.200.40.236:8080/app/index.jsp ^C [root@net-test-centos-pod1 /]#
[root@easzlab-deploy python-ns2]# kubectl exec -it -n python python-nginx-deployment-5c658bf86b-q9xnf sh kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. / # / # curl http://10.200.40.236:8080/app/index.jsp networkpolicy-python-tomcatl-20221031-test / # curl http://10.200.40.236:8080/app/index.jsp ^C / #
3.6、ingress-namespace Selector-ns选择器
# kubectl label ns linux nsname=linux
# kubectl label ns python nsname=python
[root@easzlab-deploy python-ns2]# cat case6-ingress-namespaceSelector.yaml apiVersion: networking.k8s.io/v1 kind: NetworkPolicy metadata: name: tomcat-access--networkpolicy namespace: python spec: policyTypes: - Ingress podSelector: #目标pod matchLabels: {} #允许访问python namespace 中的所有pod # app: python-tomcat-app1-selector #可以只允许访问python namespace中指定的pod ingress: - from: # - podSelector: #匹配源pod,matchLabels: {}为不限制源pod即允许所有pod,写法等同于resources(不加就是不限制) # matchLabels: {} # - ipBlock: # cidr: 10.200.0.0/16 #指定禁止访问的源网段 # except: # - 10.200.218.0/24 #在以上范围内禁止访问的源IP地址 - namespaceSelector: # matchLabels: {} #允许所有namespace访问python namespace指定的目标端口或指定的pod加指定端口 matchLabels: nsname: linux #只允许指定的namespace访问 - namespaceSelector: matchLabels: nsname: python #只允许指定的namespace访问 ports: #入栈规则,如果指定目标端口就是匹配全部端口和协议,协议TCP, UDP, or SCTP - protocol: TCP port: 8080 #允许通过TCP协议访问目标pod的8080端口,但是其它没有允许的端口将全部禁止访问 #port: 80 - protocol: TCP port: 3306 - protocol: TCP port: 6379 [root@easzlab-deploy python-ns2]#
1.被明确允许的namespace中的pod可以访问目标pod
2.没有明确声明允许的namespace将禁止访问
3.没有明确声明允许的话, 即使同一个namespace也禁止访问
4.比如只允许了linux和python两个ns, 那么default中的pod将无法访问。
验证结果
[root@easzlab-deploy python-ns2]# kubectl apply -f case6-ingress-namespaceSelector.yaml networkpolicy.networking.k8s.io/tomcat-access--networkpolicy created [root@easzlab-deploy python-ns2]# [root@easzlab-deploy python-ns2]# kubectl exec -it centos-net-test1 bash #普通pod测试 kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. [root@centos-net-test1 /]# [root@centos-net-test1 /]# curl http://10.200.40.236:8080/app/index.jsp ^C [root@centos-net-test1 /]# [root@easzlab-deploy python-ns2]# kubectl exec -it -n linux net-test-centos-pod1 bash #指定linux命名空间测试 kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. [root@net-test-centos-pod1 /]# [root@net-test-centos-pod1 /]# curl 10.200.40.236:8080/app/index.jsp networkpolicy-python-tomcatl-20221031-test [root@net-test-centos-pod1 /]# [root@easzlab-deploy ~]# kubectl exec -it -n linux linux-nginx-deployment-864bcf5f4c-vnssz sh #linux命名空间下其他pod kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. / # / # curl 10.200.40.236:8080/app/index.jsp networkpolicy-python-tomcatl-20221031-test / # [root@easzlab-deploy python-ns2]# kubectl exec -it -n python net-test-centos-pod1 bash #python 命名空间下pod访问 kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. [root@net-test-centos-pod1 /]# [root@net-test-centos-pod1 /]# curl http://10.200.40.236:8080/app/index.jsp ^C [root@net-test-centos-pod1 /]# curl http://10.200.40.236:8080/app/index.jsp networkpolicy-python-tomcatl-20221031-test [root@net-test-centos-pod1 /]# [root@easzlab-deploy python-ns2]# kubectl exec -it -n python python-nginx-deployment-5c658bf86b-q9xnf sh kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. / #/ # curl http://10.200.40.236:8080/app/index.jsp ^C / # curl http://10.200.40.236:8080/app/index.jsp networkpolicy-python-tomcatl-20221031-test / #
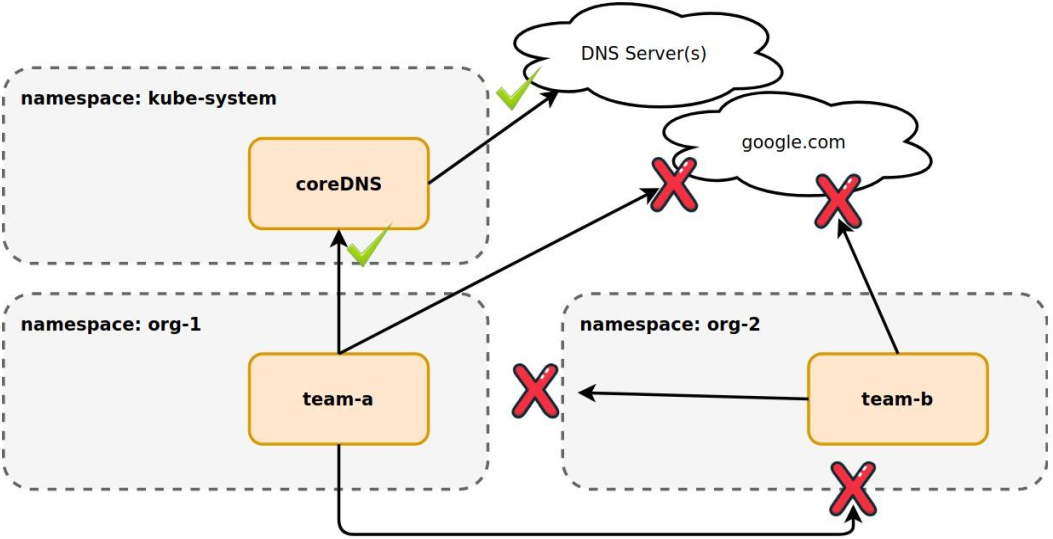
3.7、Egress-podSelector-Pod出口方向目的IP及目的端口限制-只允许访问指定的目的地址范围及端口
[root@easzlab-deploy python-ns2]# cat case7-Egress-ipBlock.yaml apiVersion: networking.k8s.io/v1 kind: NetworkPolicy metadata: name: egress-access-networkpolicy namespace: python spec: policyTypes: - Egress podSelector: #目标pod选择器 matchLabels: #基于label匹配目标pod app: python-tomcat-app1-selector #匹配python namespace中app的值为python-tomcat-app1-selector的pod,然后基于egress中的指定网络策略进行出口方向的网络限制 egress: - to: - ipBlock: cidr: 10.200.0.0/16 #允许匹配到的pod出口访问的目的CIDR地址范围 - ipBlock: cidr: 172.16.88.190/32 #允许匹配到的pod出口访问的目的主机 - ipBlock: cidr: 0.0.0.0/0 #允许匹配到的pod出口访问的目的主机 ports: - protocol: TCP port: 80 #允许匹配到的pod访问目的端口为80的访问 - protocol: TCP port: 53 #允许匹配到的pod访问目的端口为53 即DNS的解析 - protocol: UDP port: 53 #允许匹配到的pod访问目的端口为53 即DNS的解析 [root@easzlab-deploy python-ns2]#
验证结果
#未启用networkpolicy策略 [root@easzlab-deploy ~]# kubectl exec -it -n python python-tomcat-app1-deployment-7bf9bb6989-jbxhj bash kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. 16.^Cpython-tomcat-app1-deployment-7bf9bb6989-jbxhj:/usr/local/tomcat# root@python-tomcat-app1-deployment-7bf9bb6989-jbxhj:/usr/local/tomcat# ping www.baidu.com #ping 百度正常 PING www.a.shifen.com (182.61.200.6) 56(84) bytes of data. 64 bytes from 182.61.200.6 (182.61.200.6): icmp_seq=1 ttl=44 time=65.1 ms 64 bytes from 182.61.200.6 (182.61.200.6): icmp_seq=2 ttl=44 time=65.0 ms ^C --- www.a.shifen.com ping statistics --- 2 packets transmitted, 2 received, 0% packet loss, time 2ms rtt min/avg/max/mdev = 65.024/65.072/65.120/0.048 ms root@python-tomcat-app1-deployment-7bf9bb6989-jbxhj:/usr/local/tomcat# #启用networkpolicy策略
[root@easzlab-deploy python-ns2]# kubectl apply -f case7-Egress-ipBlock.yaml networkpolicy.networking.k8s.io/egress-access-networkpolicy created [root@easzlab-deploy python-ns2]# [root@easzlab-deploy ~]# kubectl exec -it -n python python-tomcat-app1-deployment-7bf9bb6989-jbxhj bash kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. root@python-tomcat-app1-deployment-7bf9bb6989-jbxhj:/usr/local/tomcat# ping www.baidu.com #ping 百度失败 PING www.a.shifen.com (182.61.200.7) 56(84) bytes of data. ^C --- www.a.shifen.com ping statistics --- 2 packets transmitted, 0 received, 100% packet loss, time 7ms root@python-tomcat-app1-deployment-7bf9bb6989-jbxhj:/usr/local/tomcat# curl http://172.16.88.190 #访问指定地址正常 <!doctype html> <html> <head> <meta charset="utf-8"> <title>Harbor</title> <base href="/"> <meta name="viewport" content="width=device-width, initial-scale=1"> <link rel="icon" type="image/x-icon" href="favicon.ico?v=2"> <link rel="preload" as="style" href="./light-theme.css?buildTimestamp=1657173838042"> <link rel="preload" as="style" href="./dark-theme.css?buildTimestamp=1657173838042"> <link rel="stylesheet" href="styles.f21a150d0d914470.css"></head> <body> <harbor-app> <div class="spinner spinner-lg app-loading app-loading-fixed"> Loading... </div> </harbor-app> <script src="runtime.b2a241ce383ba716.js" type="module"></script><script src="polyfills.40b0dd9c16ed9dc8.js" type="module"></script><script src="scripts.a459d5a2820e9a99.js" defer></script><script src="main.e999b3efec0fb336.js" type="module"></script></body> </html> root@python-tomcat-app1-deployment-7bf9bb6989-jbxhj:/usr/local/tomcat#
3.8、Egress-podSelector-Pod出口方向目的Pod限制-只允许访问指定的pod及端口
基于podSelector选择器, 限制源pod能够访问的目的pod
- 1.匹配成功的源pod只能访问指定的目的pod的指定端口
- 2.其它没有允许的出口请求将禁止访问
[root@easzlab-deploy python-ns2]# cat case8-Egress-PodSelector.yaml apiVersion: networking.k8s.io/v1 kind: NetworkPolicy metadata: name: egress-access-networkpolicy namespace: python spec: policyTypes: - Egress podSelector: #目标pod选择器 matchLabels: #基于label匹配目标pod app: python-nginx-selector #匹配python namespace中app的值为python-tomcat-app1-selector的pod,然后基于egress中的指定网络策略进行出口方向的网络限制 egress: - to: # - ipBlock: # cidr: 10.200.0.0/16 #允许访问的目的CIDR地址范围 # - ipBlock: # cidr: 172.31.7.106/32 #允许访问的目的主机地址 # - ipBlock: # cidr: 10.200.218.4/32 #白名单,允许访问的目的主机地址 - podSelector: #匹配pod,matchLabels: {}为不限制源pod即允许所有pod,写法等同于resources(不加就是不限制) matchLabels: app: python-tomcat-app1-selector ports: - protocol: TCP port: 8080 #允许80端口的访问 - protocol: TCP port: 53 #允许DNS的解析 - protocol: UDP port: 53 [root@easzlab-deploy python-ns2]#
验证结果
#未启用networkpolicy策略 [root@easzlab-deploy python-ns2]# kubectl exec -it -n python python-nginx-deployment-5c658bf86b-q9xnf sh kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. / # curl http://10.200.40.228/index.html networkpolicy-linux-nginx-20221031-test / # curl http://10.200.40.229:8080/app/index.jsp networkpolicy-linux-tomcatl-20221031-test / # / # curl http://10.200.40.235/index.html networkpolicy-python-nginx-20221031-test / # curl http://10.200.40.236:8080/app/index.jsp networkpolicy-python-tomcatl-20221031-test / # #启用networkpolicy策略 [root@easzlab-deploy python-ns2]# kubectl apply -f case8-Egress-PodSelector.yaml networkpolicy.networking.k8s.io/egress-access-networkpolicy created [root@easzlab-deploy python-ns2]# [root@easzlab-deploy python-ns2]# kubectl exec -it -n python python-nginx-deployment-5c658bf86b-q9xnf sh kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. / # curl http://10.200.40.228/index.html networkpolicy-linux-nginx-20221031-test / # curl http://10.200.40.229:8080/app/index.jsp networkpolicy-linux-tomcatl-20221031-test / # / # curl http://10.200.40.235/index.html networkpolicy-python-nginx-20221031-test / # curl http://10.200.40.236:8080/app/index.jsp networkpolicy-python-tomcatl-20221031-test / # / # / # curl http://10.200.40.228/index.html ^C / # curl http://10.200.40.229:8080/app/index.jsp ^C / # / # curl http://10.200.40.235/index.html networkpolicy-python-nginx-20221031-test / # curl http://10.200.40.236:8080/app/index.jsp networkpolicy-python-tomcatl-20221031-test / #
3.9、Egress-namespaceSelector
限制匹配成功的pod没有访问指定的namespace
- 1.匹配成功的源pod可以访问指定的目标namespace。
- 2.不能访问除指定的namespace以外的其它namespace及外网。
- 3.比如允许指定的源pod访问linux和python ns中的8080、 3306、 6379等端口, 但是其它ns无法访问
[root@easzlab-deploy python-ns2]# cat case9-Egress-namespaceSelector.yaml apiVersion: networking.k8s.io/v1 kind: NetworkPolicy metadata: name: egress-access-networkpolicy namespace: python spec: policyTypes: - Egress podSelector: #目标pod选择器 matchLabels: #基于label匹配目标pod app: python-nginx-selector #匹配python namespace中app的值为python-tomcat-app1-selector的pod,然后基于egress中的指定网络策略进行出口方向的网络限制 egress: - to: # - ipBlock: # cidr: 10.200.0.0/16 #允许访问的目的CIDR地址范围 # - ipBlock: # cidr: 172.31.7.106/32 #允许访问的目的主机地址 # - ipBlock: # cidr: 10.200.218.4/32 #允许访问的目的主机地址 # - podSelector: #匹配pod,matchLabels: {}为不限制源pod即允许所有pod,写法等同于resources(不加就是不限制) # matchLabels: # app: python-tomcat-app1-selector - namespaceSelector: matchLabels: nsname: python #指定允许访问的目的namespace - namespaceSelector: matchLabels: nsname: linux #指定允许访问的目的namespace ports: - protocol: TCP port: 8080 #允许80端口的访问 - protocol: TCP port: 53 #允许DNS的解析 - protocol: UDP port: 53 [root@easzlab-deploy python-ns2]#
验证结果
[root@easzlab-deploy python-ns2]# kubectl apply -f case9-Egress-namespaceSelector.yaml #启用networkpolicy策略 networkpolicy.networking.k8s.io/egress-access-networkpolicy created [root@easzlab-deploy python-ns2]# [root@easzlab-deploy python-ns2]# kubectl exec -it -n python python-nginx-deployment-5c658bf86b-q9xnf sh kubectl exec [POD] [COMMAND] is DEPRECATED and will be removed in a future version. Use kubectl exec [POD] -- [COMMAND] instead. / # curl http://10.200.40.228/index.html #访问linux命名空间下nginx pod 80失败 ^C / # curl http://10.200.40.229:8080/app/index.jsp #访问linux命名空间下tomcat pod 8080 正常 networkpolicy-linux-tomcatl-20221031-test / # / # curl http://10.200.40.235/index.html #访问自己正常 networkpolicy-python-nginx-20221031-test / # curl http://10.200.40.236:8080/app/index.jsp #访问python命名空间下tomcat pod 8080正常 networkpolicy-python-tomcatl-20221031-test / #






【推荐】国内首个AI IDE,深度理解中文开发场景,立即下载体验Trae
【推荐】编程新体验,更懂你的AI,立即体验豆包MarsCode编程助手
【推荐】抖音旗下AI助手豆包,你的智能百科全书,全免费不限次数
【推荐】轻量又高性能的 SSH 工具 IShell:AI 加持,快人一步
· TypeScript + Deepseek 打造卜卦网站:技术与玄学的结合
· 阿里巴巴 QwQ-32B真的超越了 DeepSeek R-1吗?
· 【译】Visual Studio 中新的强大生产力特性
· 10年+ .NET Coder 心语 ── 封装的思维:从隐藏、稳定开始理解其本质意义
· 【设计模式】告别冗长if-else语句:使用策略模式优化代码结构