逆向中常见的加密算法
逆向中常见的加密算法
1.Base64
1) 原理与特征:
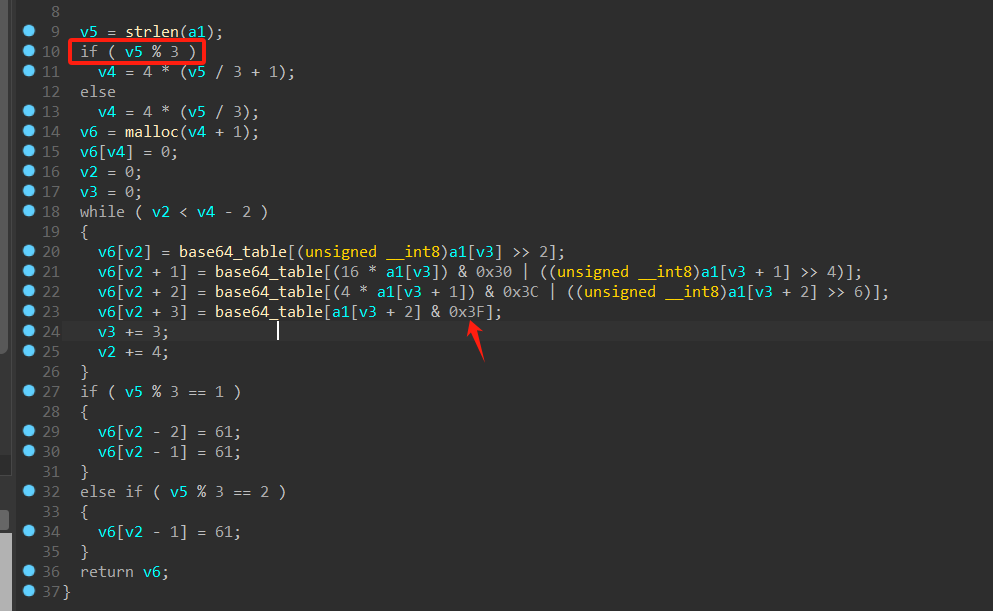
a.原理:将3个byte(即3×8=24bit)切割为4×6,然后根据6bit表示的数字在base64表(64byte的表)寻找对应的值;如果待加密字符串长度不为3的整数,则在末尾处补0对齐,其中0对应的字符为'='。
b.特征:在反汇编代码中会出现0x3F,‘=’ 的特殊标识。(某些题目可能会直接在base64加密函数修改而不仅仅是变表-安洵杯2019-crackme
2) 解密脚本
a.不换表
import base64
encode_str=''
decode_str=base64.b64decode(str0).decode('utf-8')
print(decode_str)
b.换表
import base64
encode_string = ""
string1 = ""#base64变表
string2 = "ABCDEFGIJKLMNOPQRSTUVWXYZabcdefgijklmnopqrstuvwxyz0123456789+/"
decode_str=base64.b64decode(encode_string.translate(str.maketrans(string1,string2)))
print(decode_str)
2.Tea-XTea
1) 原理与特征
a.原理:tea算法家族的原理比较简单(目前博主仅遇到的tea/xtea),魔改tea的类型也比较多,可能是在循环移位进行改动,也可能是修改了delta的值
b.特征:(出自 [HNCTF 2022 WEEK2]TTTTTTTTTea)
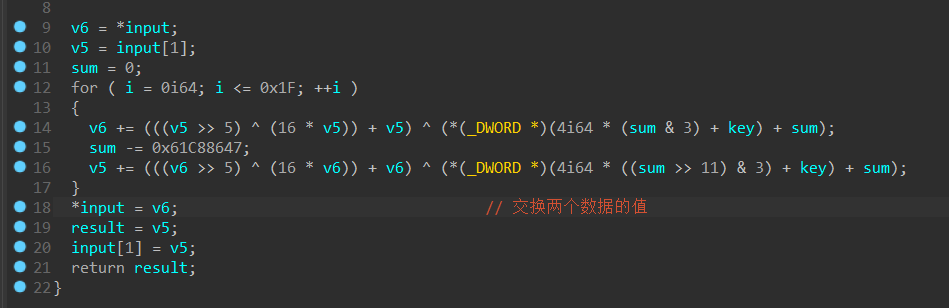
a) 存在delta,(上图delta=0x61C88647)
b) input[i]与input[i+n]进行移位/异或/加减操作
2) 解密脚本(题目出自 [HNCTF 2022 WEEK2]TTTTTTTTTea
#include <stdio.h>
int main() {
unsigned int enc[] = {0xC11EE75A, 0xA4AD0973, 0xF61C9018, 0x32E37BCD, 0x2DCC1F26, 0x344380CC};
unsigned int key[] = { 0x10203,0x4050607,0x8090A0B,0x0C0D0E0F };
unsigned int delta = 0x61C88647;
for(int j=0;j<6;j+=2)
{
unsigned int v4 = 0 - (32 * 0x61C88647);
for (int i = 0; i < 32; ++i)
{
enc[j + 1] -= (((enc[j] >> 5) ^ (16 * enc[j])) + enc[j]) ^ (key[((v4 >> 11) & 3)] + v4);
v4 += 0x61C88647;
enc[j] -= (((enc[j + 1] >> 5) ^ (16 * enc[j + 1])) + enc[j + 1]) ^ (key[(v4 & 3)] + v4);
}
printf("%lx,%lx,",enc[j],enc[j+1]);
}
printf("\n");
char* ptr = enc;
for (int p = 0; p < 24; p++) {
printf("%c", *(ptr++));
}
}
3.RC4
1) 原理与特征
a.原理:
a) 先初始化一个长度为256的s盒,同时根据密钥key初始化一个长度为256的T盒;
b) 根据T盒打乱S盒(重要的步骤是交换s盒元素的位置);
c) 将待加密的数据进行与s盒元素进行异或。
b.特征:a) 一般出现三个for循环,前两个循环进行256次,第三个循环32次;
b) 会出现两个长度为256的数组,其中一个数组的初始值一般为0-255。
2) 解密脚本
rc4是对称算法(异或),所以加密脚本也是解密脚本
(题目:vctf2024-vm)
#include <stdio.h>
#include <math.h>
#include <string.h>
#include<stdio.h>
/*
RC4初始化函数
*/
void rc4_init(unsigned char* s, unsigned char* key, unsigned long Len_k)
{
int i = 0, j = 0;
char k[256] = { 0 };
unsigned char tmp = 0;
for (i = 0; i < 256; i++) {
s[i] = i;
k[i] = key[i % Len_k];
}
for (i = 0; i < 256; i++) {
j = (j + s[i] + k[i]) % 256;
tmp = s[i];
s[i] = s[j];
s[j] = tmp;
}
}
/*
RC4加解密函数
unsigned char* Data 加解密的数据
unsigned long Len_D 加解密数据的长度
unsigned char* key 密钥
unsigned long Len_k 密钥长度
*/
void rc4_crypt(unsigned char* Data, unsigned long Len_D, unsigned char* key, unsigned long Len_k) //加解密
{
unsigned char s[256];
rc4_init(s, key, Len_k);
int i = 0, j = 0, t = 0;
unsigned long k = 0;
unsigned char tmp;
for (k = 0; k < Len_D; k++) {
i = (i + 1) % 256;
j = (j + s[i]) % 256;
Data[k] -= i; //这里有魔改
tmp = s[i];
s[i] = s[j];
s[j] = tmp;
t = (s[i] + s[j]) % 256;
Data[k] = Data[k] ^ s[t];
}
}
void main()
{
//字符串密钥
unsigned char key[] = "This_1s_f1lLllag";
unsigned long key_len = sizeof(key) - 1;
//数组密钥
//unsigned char key[] = {};
//unsigned long key_len = sizeof(key);
//加解密数据
unsigned char data[] = { 0x56, 0x54, 0xD9, 0xB5, 0xF3, 0xB1, 0xFD, 0x67, 0x15, 0xEE, 0xB0, 0x68, 0xB7, 0x2B, 0x4A, 0x64,
0x10, 0x27, 0x52, 0xDE, 0x43, 0x26, 0x0F, 0x2A, 0x41, 0x30, 0x75, 0x30, 0x98, 0x9E, 0x79, 0x5E };
//加解密
rc4_crypt(data, sizeof(data), key, key_len);
for (int i = 0; i < sizeof(data); i++)
{
printf("%c", data[i]);
}
printf("\n");
return;
}
//zstuctf{xXx_team_Is_GooD
//(c语言源码解释:https://www.cnblogs.com/Moomin/p/15023601.html)
//(解密脚本:https://blog.csdn.net/weixin_45582916/article/details/121429688
4.AES
1) 原理与特征
(AES的数学运算太复杂了,可以在b站或者其他博客研究原理,本博客侧重解密)
【5分钟搞定AES算法】https://www.bilibili.com/video/BV1yq4y1X7Kt?vd_source=69ffcd703762aa7a204e6cc6f57ba69d
a.加密过程简述:密钥扩展--字节替换--行移位--列混合--轮密钥加。
a) 先将密钥转化为4*4的矩阵进行扩展(这里的扩展会进行移位/异或的一系列操作)
b) 字节替换:AES有一个16×16=256长度的S盒用于替换字节,可以理解为二维数组。将原有字节,例如data=0xab,则替换为s盒中第a行第b列对应的值。(S盒的构造非常麻烦,所以一般是固定的,但也存在魔改AES的情况
c) 行移位:AES的操作基于4*4的矩阵进行,第i行循环左移i字节
d) 列混合:矩阵相乘
e) 轮密钥加:将数据与密钥进行异或
b.特征:
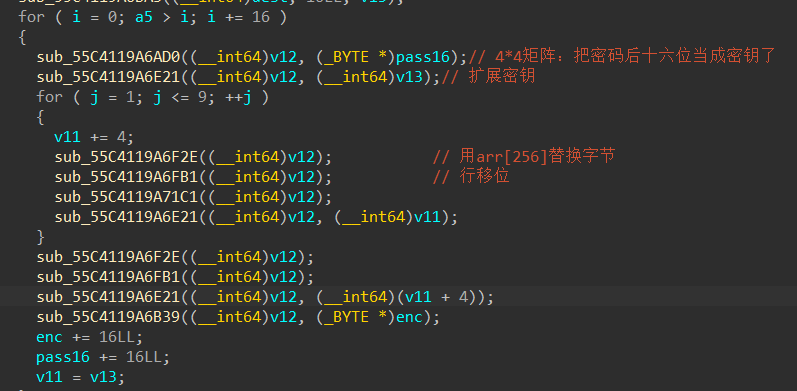
a) AES会进行9次循环(准确来说是10次?),且一般在反汇编代码中,每个操作以函数的形式存在
b) 密钥扩展存在轮常量:
1000000h, 2000000h, 4000000h, 8000000h, 10000000h, 20000000h, 40000000h, 80000000h, 1B000000h, 36000000h
c) 未魔改的s盒与逆s盒
uint8_t sbox[256] = {
0x63, 0x7c, 0x77, 0x7b, 0xf2, 0x6b, 0x6f, 0xc5, 0x30, 0x01, 0x67, 0x2b, 0xfe, 0xd7, 0xab, 0x76,
0xca, 0x82, 0xc9, 0x7d, 0xfa, 0x59, 0x47, 0xf0, 0xad, 0xd4, 0xa2, 0xaf, 0x9c, 0xa4, 0x72, 0xc0,
0xb7, 0xfd, 0x93, 0x26, 0x36, 0x3f, 0xf7, 0xcc, 0x34, 0xa5, 0xe5, 0xf1, 0x71, 0xd8, 0x31, 0x15,
0x04, 0xc7, 0x23, 0xc3, 0x18, 0x96, 0x05, 0x9a, 0x07, 0x12, 0x80, 0xe2, 0xeb, 0x27, 0xb2, 0x75,
0x09, 0x83, 0x2c, 0x1a, 0x1b, 0x6e, 0x5a, 0xa0, 0x52, 0x3b, 0xd6, 0xb3, 0x29, 0xe3, 0x2f, 0x84,
0x53, 0xd1, 0x00, 0xed, 0x20, 0xfc, 0xb1, 0x5b, 0x6a, 0xcb, 0xbe, 0x39, 0x4a, 0x4c, 0x58, 0xcf,
0xd0, 0xef, 0xaa, 0xfb, 0x43, 0x4d, 0x33, 0x85, 0x45, 0xf9, 0x02, 0x7f, 0x50, 0x3c, 0x9f, 0xa8,
0x51, 0xa3, 0x40, 0x8f, 0x92, 0x9d, 0x38, 0xf5, 0xbc, 0xb6, 0xda, 0x21, 0x10, 0xff, 0xf3, 0xd2,
0xcd, 0x0c, 0x13, 0xec, 0x5f, 0x97, 0x44, 0x17, 0xc4, 0xa7, 0x7e, 0x3d, 0x64, 0x5d, 0x19, 0x73,
0x60, 0x81, 0x4f, 0xdc, 0x22, 0x2a, 0x90, 0x88, 0x46, 0xee, 0xb8, 0x14, 0xde, 0x5e, 0x0b, 0xdb,
0xe0, 0x32, 0x3a, 0x0a, 0x49, 0x06, 0x24, 0x5c, 0xc2, 0xd3, 0xac, 0x62, 0x91, 0x95, 0xe4, 0x79,
0xe7, 0xc8, 0x37, 0x6d, 0x8d, 0xd5, 0x4e, 0xa9, 0x6c, 0x56, 0xf4, 0xea, 0x65, 0x7a, 0xae, 0x08,
0xba, 0x78, 0x25, 0x2e, 0x1c, 0xa6, 0xb4, 0xc6, 0xe8, 0xdd, 0x74, 0x1f, 0x4b, 0xbd, 0x8b, 0x8a,
0x70, 0x3e, 0xb5, 0x66, 0x48, 0x03, 0xf6, 0x0e, 0x61, 0x35, 0x57, 0xb9, 0x86, 0xc1, 0x1d, 0x9e,
0xe1, 0xf8, 0x98, 0x11, 0x69, 0xd9, 0x8e, 0x94, 0x9b, 0x1e, 0x87, 0xe9, 0xce, 0x55, 0x28, 0xdf,
0x8c, 0xa1, 0x89, 0x0d, 0xbf, 0xe6, 0x42, 0x68, 0x41, 0x99, 0x2d, 0x0f, 0xb0, 0x54, 0xbb, 0x16
};
uint8_t inVsbox[256] = {
0x52, 0x09, 0x6a, 0xd5, 0x30, 0x36, 0xa5, 0x38, 0xbf, 0x40, 0xa3, 0x9e, 0x81, 0xf3, 0xd7, 0xfb,
0x7c, 0xe3, 0x39, 0x82, 0x9b, 0x2f, 0xff, 0x87, 0x34, 0x8e, 0x43, 0x44, 0xc4, 0xde, 0xe9, 0xcb,
0x54, 0x7b, 0x94, 0x32, 0xa6, 0xc2, 0x23, 0x3d, 0xee, 0x4c, 0x95, 0x0b, 0x42, 0xfa, 0xc3, 0x4e,
0x08, 0x2e, 0xa1, 0x66, 0x28, 0xd9, 0x24, 0xb2, 0x76, 0x5b, 0xa2, 0x49, 0x6d, 0x8b, 0xd1, 0x25,
0x72, 0xf8, 0xf6, 0x64, 0x86, 0x68, 0x98, 0x16, 0xd4, 0xa4, 0x5c, 0xcc, 0x5d, 0x65, 0xb6, 0x92,
0x6c, 0x70, 0x48, 0x50, 0xfd, 0xed, 0xb9, 0xda, 0x5e, 0x15, 0x46, 0x57, 0xa7, 0x8d, 0x9d, 0x84,
0x90, 0xd8, 0xab, 0x00, 0x8c, 0xbc, 0xd3, 0x0a, 0xf7, 0xe4, 0x58, 0x05, 0xb8, 0xb3, 0x45, 0x06,
0xd0, 0x2c, 0x1e, 0x8f, 0xca, 0x3f, 0x0f, 0x02, 0xc1, 0xaf, 0xbd, 0x03, 0x01, 0x13, 0x8a, 0x6b,
0x3a, 0x91, 0x11, 0x41, 0x4f, 0x67, 0xdc, 0xea, 0x97, 0xf2, 0xcf, 0xce, 0xf0, 0xb4, 0xe6, 0x73,
0x96, 0xac, 0x74, 0x22, 0xe7, 0xad, 0x35, 0x85, 0xe2, 0xf9, 0x37, 0xe8, 0x1c, 0x75, 0xdf, 0x6e,
0x47, 0xf1, 0x1a, 0x71, 0x1d, 0x29, 0xc5, 0x89, 0x6f, 0xb7, 0x62, 0x0e, 0xaa, 0x18, 0xbe, 0x1b,
0xfc, 0x56, 0x3e, 0x4b, 0xc6, 0xd2, 0x79, 0x20, 0x9a, 0xdb, 0xc0, 0xfe, 0x78, 0xcd, 0x5a, 0xf4,
0x1f, 0xdd, 0xa8, 0x33, 0x88, 0x07, 0xc7, 0x31, 0xb1, 0x12, 0x10, 0x59, 0x27, 0x80, 0xec, 0x5f,
0x60, 0x51, 0x7f, 0xa9, 0x19, 0xb5, 0x4a, 0x0d, 0x2d, 0xe5, 0x7a, 0x9f, 0x93, 0xc9, 0x9c, 0xef,
0xa0, 0xe0, 0x3b, 0x4d, 0xae, 0x2a, 0xf5, 0xb0, 0xc8, 0xeb, 0xbb, 0x3c, 0x83, 0x53, 0x99, 0x61,
0x17, 0x2b, 0x04, 0x7e, 0xba, 0x77, 0xd6, 0x26, 0xe1, 0x69, 0x14, 0x63, 0x55, 0x21, 0x0c, 0x7d
};
b.解密脚本
a) 魔改S盒求逆S盒
//NKCTF2024-loginsystem
int main() {
int Sbox[16][16] = {
0x31, 0x52, 0x5A, 0xC8, 0x0B, 0xAC, 0xF3, 0x3A, 0x8B, 0x54, 0x27, 0x9B, 0xAB, 0x95, 0xDE, 0x83,
0x60, 0xCB, 0x53, 0x7F, 0xC4, 0xE3, 0x0A, 0x97, 0xE0, 0x29, 0xD5, 0x68, 0xC5, 0xDF, 0xF4, 0x7B,
0xAA, 0xD6, 0x42, 0x78, 0x6C, 0xE9, 0x70, 0x17, 0xD7, 0x37, 0x24, 0x49, 0x75, 0xA9, 0x89, 0x67,
0x03, 0xFA, 0xD9, 0x91, 0xB4, 0x5B, 0xC2, 0x4E, 0x92, 0xFC, 0x46, 0xB1, 0x73, 0x08, 0xC7, 0x74,
0x09, 0xAF, 0xEC, 0xF5, 0x4D, 0x2D, 0xEA, 0xA5, 0xDA, 0xEF, 0xA6, 0x2B, 0x7E, 0x0C, 0x8F, 0xB0,
0x04, 0x06, 0x62, 0x84, 0x15, 0x8E, 0x12, 0x1D, 0x44, 0xC0, 0xE2, 0x38, 0xD4, 0x47, 0x28, 0x45,
0x6E, 0x9D, 0x63, 0xCF, 0xE6, 0x8C, 0x18, 0x82, 0x1B, 0x2C, 0xEE, 0x87, 0x94, 0x10, 0xC1, 0x20,
0x07, 0x4A, 0xA4, 0xEB, 0x77, 0xBC, 0xD3, 0xE1, 0x66, 0x2A, 0x6B, 0xE7, 0x79, 0xCC, 0x86, 0x16,
0xD0, 0xD1, 0x19, 0x55, 0x3C, 0x9F, 0xFB, 0x30, 0x98, 0xBD, 0xB8, 0xF1, 0x9E, 0x61, 0xCD, 0x90,
0xCE, 0x7C, 0x8D, 0x57, 0xAE, 0x6A, 0xB3, 0x3D, 0x76, 0xA7, 0x71, 0x88, 0xA2, 0xBA, 0x4F, 0x3E,
0x40, 0x64, 0x0F, 0x48, 0x21, 0x35, 0x36, 0x2F, 0xE8, 0x14, 0x5D, 0x51, 0xD8, 0xB5, 0xFE, 0xD2,
0x96, 0x93, 0xA1, 0xB6, 0x43, 0x0D, 0x4C, 0x80, 0xC9, 0xFF, 0xA3, 0xDD, 0x72, 0x05, 0x59, 0xBF,
0x0E, 0x26, 0x34, 0x1F, 0x13, 0xE5, 0xDC, 0xF2, 0xC6, 0x50, 0x1E, 0xE4, 0x85, 0xB7, 0x39, 0x8A,
0xCA, 0xED, 0x9C, 0xBB, 0x56, 0x23, 0x1A, 0xF0, 0x32, 0x58, 0xB2, 0x65, 0x33, 0x6F, 0x41, 0xBE,
0x3F, 0x6D, 0x11, 0x00, 0xAD, 0x5F, 0xC3, 0x81, 0x25, 0xA8, 0xA0, 0x9A, 0xF6, 0xF7, 0x5E, 0x99,
0x22, 0x2E, 0x4B, 0xF9, 0x3B, 0x02, 0x7A, 0xB9, 0x5C, 0x69, 0xF8, 0x1C, 0xDB, 0x01, 0x7D, 0xFD
};
//博主用的是自己比较好理解的方式写的。。其实还有更简单的脚本
int InvSbox[16][16] = {0};
printf(" ");
for(int i =0;i<16;i++)
{
for(int j=0;j<16;j++)
{
InvSbox[(Sbox[i][j]) >> 4][(Sbox[i][j]) & 0xf] = (i << 4) + j;
}
}
for (int j = 0; j < 16;j++) {
printf("%.2x ", j);
for (int k = 0; k < 16; k++) {
printf("0x%.2x ", InvSbox[j][k]);
}
printf("\n");
}
}
接着将魔改的S盒导入以下博客里的脚本就可以解密
https://blog.csdn.net/weixin_45582916/article/details/121429445
b) 未魔改
from Crypto.Cipher import AES
from Crypto.Util.number import *
enc=0xBC0AADC0147C5ECCE0B140BC9C51D52B46B2B9434DE5324BAD7FB4B39CDB4B5B
key=0xcb8d493521b47a4cc1ae7e62229266ce
keyy=long_to_bytes(key)
encc=long_to_bytes(enc)
decrypt_str=AES.new(keyy,mode=AES.MODE_ECB)
flag=decrypt_str.decrypt(encc)
print(flag)
5.SM4
1) 原理与特征
a. 原理:
a) SM4的输入与密钥都是128bit,进行了32轮的迭代运算与1次反序变换,每一轮进行4bit的运算。
(详细原理请戳:https://www.bilibili.com/video/BV1LS4y167r3?vd_source=69ffcd703762aa7a204e6cc6f57ba69d)
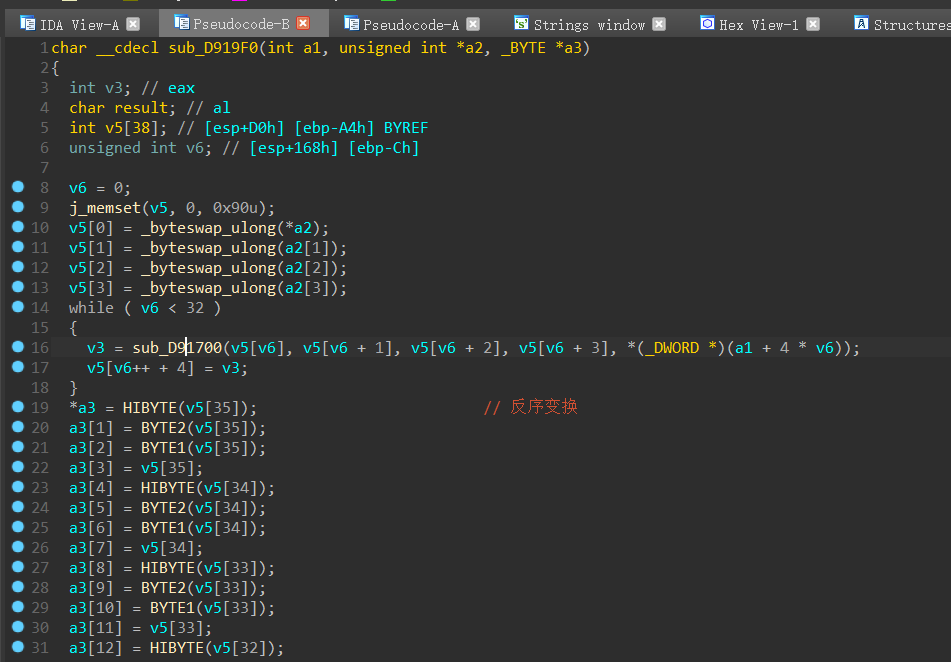
b) 以安洵杯2019-crackme为例
- 这里有很明显的轮密钥扩展特征(使用了findcrypt插件
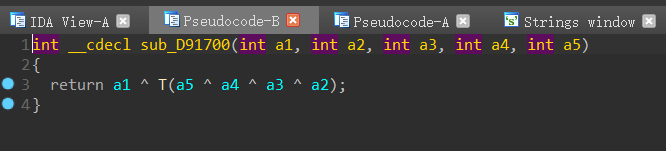
- 进入SM4加密,可以看到进行32次循环,跟进sub_D91700查看,发现是轮函数(即加密
b.特征:
a) 有S盒进行字节替换
s_box[256]={
0xD6, 0x90, 0xE9, 0xFE, 0xCC, 0xE1, 0x3D, 0xB7, 0x16, 0xB6, 0x14, 0xC2, 0x28, 0xFB, 0x2C, 0x05,
0x2B, 0x67, 0x9A, 0x76, 0x2A, 0xBE, 0x04, 0xC3, 0xAA, 0x44, 0x13, 0x26, 0x49, 0x86, 0x06, 0x99,
0x9C, 0x42, 0x50, 0xF4, 0x91, 0xEF, 0x98, 0x7A, 0x33, 0x54, 0x0B, 0x43, 0xED, 0xCF, 0xAC, 0x62,
0xE4, 0xB3, 0x1C, 0xA9, 0xC9, 0x08, 0xE8, 0x95, 0x80, 0xDF, 0x94, 0xFA, 0x75, 0x8F, 0x3F, 0xA6,
0x47, 0x07, 0xA7, 0xFC, 0xF3, 0x73, 0x17, 0xBA, 0x83, 0x59, 0x3C, 0x19, 0xE6, 0x85, 0x4F, 0xA8,
0x68, 0x6B, 0x81, 0xB2, 0x71, 0x64, 0xDA, 0x8B, 0xF8, 0xEB, 0x0F, 0x4B, 0x70, 0x56, 0x9D, 0x35,
0x1E, 0x24, 0x0E, 0x5E, 0x63, 0x58, 0xD1, 0xA2, 0x25, 0x22, 0x7C, 0x3B, 0x01, 0x21, 0x78, 0x87,
0xD4, 0x00, 0x46, 0x57, 0x9F, 0xD3, 0x27, 0x52, 0x4C, 0x36, 0x02, 0xE7, 0xA0, 0xC4, 0xC8, 0x9E,
0xEA, 0xBF, 0x8A, 0xD2, 0x40, 0xC7, 0x38, 0xB5, 0xA3, 0xF7, 0xF2, 0xCE, 0xF9, 0x61, 0x15, 0xA1,
0xE0, 0xAE, 0x5D, 0xA4, 0x9B, 0x34, 0x1A, 0x55, 0xAD, 0x93, 0x32, 0x30, 0xF5, 0x8C, 0xB1, 0xE3,
0x1D, 0xF6, 0xE2, 0x2E, 0x82, 0x66, 0xCA, 0x60, 0xC0, 0x29, 0x23, 0xAB, 0x0D, 0x53, 0x4E, 0x6F,
0xD5, 0xDB, 0x37, 0x45, 0xDE, 0xFD, 0x8E, 0x2F, 0x03, 0xFF, 0x6A, 0x72, 0x6D, 0x6C, 0x5B, 0x51,
0x8D, 0x1B, 0xAF, 0x92, 0xBB, 0xDD, 0xBC, 0x7F, 0x11, 0xD9, 0x5C, 0x41, 0x1F, 0x10, 0x5A, 0xD8,
0x0A, 0xC1, 0x31, 0x88, 0xA5, 0xCD, 0x7B, 0xBD, 0x2D, 0x74, 0xD0, 0x12, 0xB8, 0xE5, 0xB4, 0xB0,
0x89, 0x69, 0x97, 0x4A, 0x0C, 0x96, 0x77, 0x7E, 0x65, 0xB9, 0xF1, 0x09, 0xC5, 0x6E, 0xC6, 0x84,
0x18, 0xF0, 0x7D, 0xEC, 0x3A, 0xDC, 0x4D, 0x20, 0x79, 0xEE, 0x5F, 0x3E, 0xD7, 0xCB, 0x39, 0x48
}
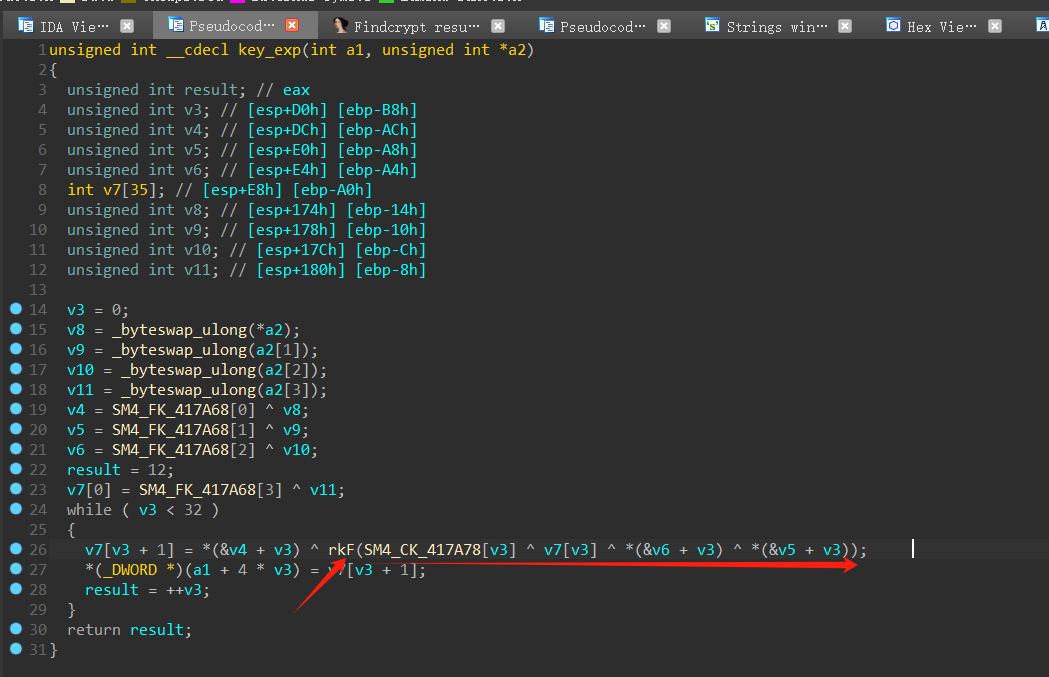
b) 轮密钥扩展时存在常数CK和FK
CK[32]={
0x00070e15, 0x1c232a31, 0x383f64d, 0x545b6269,
0x70777e85, 0x8c939aa1, 0xa8afb6bd, 0xc4cbd2d9,
0xe0e7eef5, 0xfc030a11, 0x181f262d, 0x343b4249,
0x50575e65, 0x6c737a81, 0x88f969d, 0xa4abb2b9,
0xc0c7ced5, 0xdce3eafl, 0xf8ff060d, 0x141b2229,
0x30373e45, 0x4c535a61, 0x686f767d, 0x848b9299,
0xa0a7aeb5, 0xbcc3cad1, 0xd8dfe6ed, 0xf4fb0209,
0x10171e25, 0x2c333a41, 0x484f565d, 0x646b7279
}
FK0=(A3B1BAC6),FK1=(56AA3350),FK2=(677D9197), FK3=(B27022DC)
b.解密脚本
在github上下载python库进行解密即可/在线解密/找脚本
https://github.com/yang3yen/pysm4
>>> from pysm4 import encrypt, decrypt
# 明文
>>> clear_num = 0x0123456789abcdeffedcba9876543210
# 密钥
>>> mk = 0x0123456789abcdeffedcba9876543210
# 加密
>>> cipher_num = encrypt(clear_num, mk)
>>> hex(cipher_num)[2:].replace('L', '')
'681edf34d206965e86b3e94f536e4246'
# 解密
>>> clear_num == decrypt(cipher_num, mk)
True


 浙公网安备 33010602011771号
浙公网安备 33010602011771号