Xctf-easyapk
Xctf-easyapk Write UP
前期工作
-
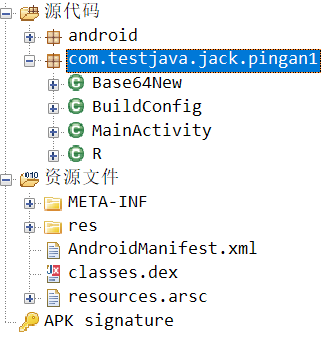
查壳
![image-20200727163745053]()
无壳
-
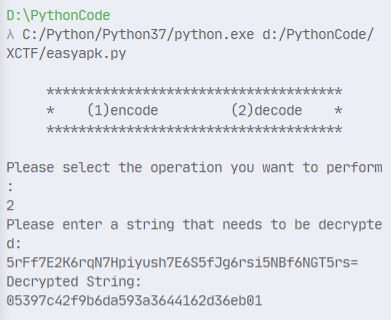
运行
![image-20200727163844688]()
没什么特别的
逆向分析
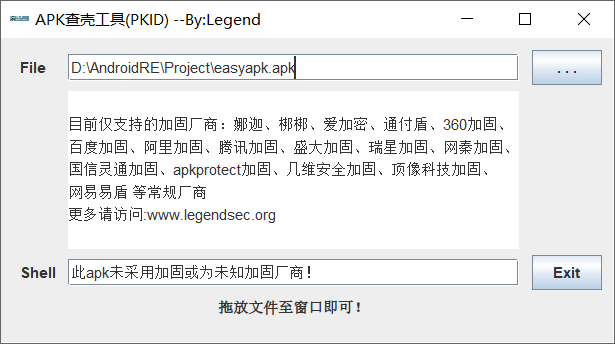
使用jadx反编译查看代码
先看看文件结构
MainActivity代码
public class MainActivity extends AppCompatActivity {
/* access modifiers changed from: protected */
public void onCreate(Bundle savedInstanceState) {
super.onCreate(savedInstanceState);
setContentView((int) R.layout.activity_main);
((Button) findViewById(R.id.button)).setOnClickListener(new View.OnClickListener() {
public void onClick(View view) {
if (new Base64New().Base64Encode(((EditText) MainActivity.this.findViewById(R.id.editText)).getText().toString().getBytes()).equals("5rFf7E2K6rqN7Hpiyush7E6S5fJg6rsi5NBf6NGT5rs=")) {
Toast.makeText(MainActivity.this, "验证通过!", 1).show();
} else {
Toast.makeText(MainActivity.this, "验证失败!", 1).show();
}
}
});
}
}
可以看到大概就是将通过Base64编码后比较。但是将代码中的Base64字符串拿去解码得不到正常字符串。注意到Base64New里的New,猜测是自己实现了一个新的Base64编码。
看看Base64New类的代码
public class Base64New {
private static final char[] Base64ByteToStr = {'v', 'w', 'x', 'r', 's', 't', 'u', 'o', 'p', 'q', '3', '4', '5', '6', '7', 'A', 'B', 'C', 'D', 'E', 'F', 'G', 'H', 'I', 'J', 'y', 'z', '0', '1', '2', 'P', 'Q', 'R', 'S', 'T', 'K', 'L', 'M', 'N', 'O', 'Z', 'a', 'b', 'c', 'd', 'U', 'V', 'W', 'X', 'Y', 'e', 'f', 'g', 'h', 'i', 'j', 'k', 'l', 'm', 'n', '8', '9', '+', '/'};
private static final int RANGE = 255;
private static byte[] StrToBase64Byte = new byte[128];
public String Base64Encode(byte[] bytes) {
StringBuilder res = new StringBuilder();
for (int i = 0; i <= bytes.length - 1; i += 3) {
byte[] enBytes = new byte[4];
byte tmp = 0;
for (int k = 0; k <= 2; k++) {
if (i + k <= bytes.length - 1) {
enBytes[k] = (byte) (((bytes[i + k] & 255) >>> ((k * 2) + 2)) | tmp);
tmp = (byte) ((((bytes[i + k] & 255) << (((2 - k) * 2) + 2)) & 255) >>> 2);
} else {
enBytes[k] = tmp;
tmp = 64;
}
}
enBytes[3] = tmp;
for (int k2 = 0; k2 <= 3; k2++) {
if (enBytes[k2] <= 63) {
res.append(Base64ByteToStr[enBytes[k2]]);
} else {
res.append('=');
}
}
}
return res.toString();
}
}
可以看到应该是替换了码表
编写脚本
# s = "ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+/"
a = [
'v', 'w', 'x', 'r', 's', 't', 'u', 'o', 'p', 'q', '3', '4', '5', '6', '7',
'A', 'B', 'C', 'D', 'E', 'F', 'G', 'H', 'I', 'J', 'y', 'z', '0', '1', '2',
'P', 'Q', 'R', 'S', 'T', 'K', 'L', 'M', 'N', 'O', 'Z', 'a', 'b', 'c', 'd',
'U', 'V', 'W', 'X', 'Y', 'e', 'f', 'g', 'h', 'i', 'j', 'k', 'l', 'm', 'n',
'8', '9', '+', '/'
]
s = ''.join(a)
def My_base64_encode(inputs):
# 将字符串转化为2进制
bin_str = []
for i in inputs:
x = str(bin(ord(i))).replace('0b', '')
bin_str.append('{:0>8}'.format(x))
#print(bin_str)
# 输出的字符串
outputs = ""
# 不够三倍数,需补齐的次数
nums = 0
while bin_str:
#每次取三个字符的二进制
temp_list = bin_str[:3]
if (len(temp_list) != 3):
nums = 3 - len(temp_list)
while len(temp_list) < 3:
temp_list += ['0' * 8]
temp_str = "".join(temp_list)
#print(temp_str)
# 将三个8字节的二进制转换为4个十进制
temp_str_list = []
for i in range(0, 4):
temp_str_list.append(int(temp_str[i * 6:(i + 1) * 6], 2))
#print(temp_str_list)
if nums:
temp_str_list = temp_str_list[0:4 - nums]
for i in temp_str_list:
outputs += s[i]
bin_str = bin_str[3:]
outputs += nums * '='
print("Encrypted String:\n%s " % outputs)
def My_base64_decode(inputs):
# 将字符串转化为2进制
bin_str = []
for i in inputs:
if i != '=':
x = str(bin(s.index(i))).replace('0b', '')
bin_str.append('{:0>6}'.format(x))
#print(bin_str)
# 输出的字符串
outputs = ""
nums = inputs.count('=')
while bin_str:
temp_list = bin_str[:4]
temp_str = "".join(temp_list)
#print(temp_str)
# 补足8位字节
if (len(temp_str) % 8 != 0):
temp_str = temp_str[0:-1 * nums * 2]
# 将四个6字节的二进制转换为三个字符
for i in range(0, int(len(temp_str) / 8)):
outputs += chr(int(temp_str[i * 8:(i + 1) * 8], 2))
bin_str = bin_str[4:]
print("Decrypted String:\n%s " % outputs)
print()
print(" *************************************")
print(" * (1)encode (2)decode *")
print(" *************************************")
print()
num = input("Please select the operation you want to perform:\n")
if (num == "1"):
input_str = input("Please enter a string that needs to be encrypted: \n")
My_base64_encode(input_str)
else:
input_str = input("Please enter a string that needs to be decrypted: \n")
My_base64_decode(input_str)
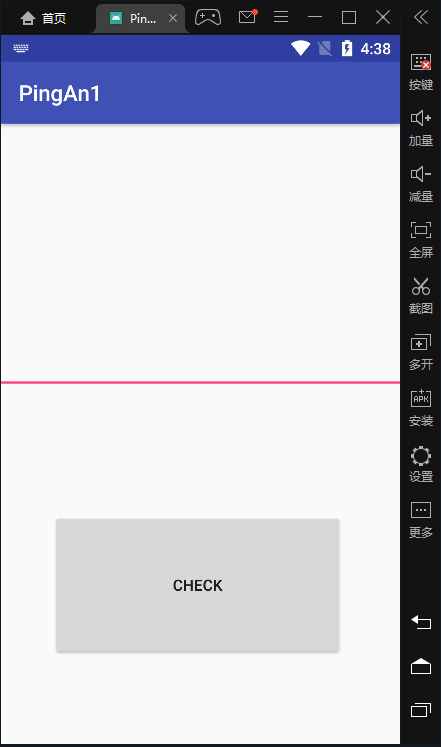
运行结果
-
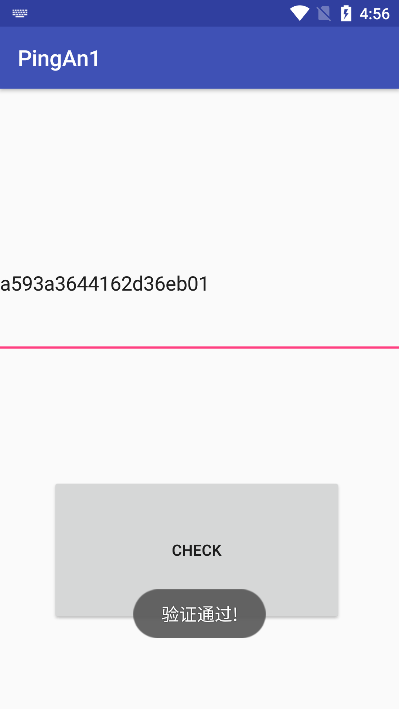
验证
![image-20200727165657019]()
flag
flag


 浙公网安备 33010602011771号
浙公网安备 33010602011771号