IPSec的高可用性技术
IPSec VPN的高可用性技术:
①、DPD(Dead Peer Detection)对等体检测
——旨在检查有问题的IPSec VPN网络,并快速的切换到备用网关
②、RRI(Reverse Route Injection)反向路由注入
——解决高可用性的路由问题
****************DPD**************
DPD的工作模式:
周期性的工作模式——设置一个定时器,路由器会按照这个定时器所设置的时间周期性的发送DPD数据包; 好处在于快速的检测到对等体的问题;缺点是这样周期的发送DPD会消耗较多的设备资源和网络资源
按需工作模式——DPD默认的工作模式,这样的情况下,DPD信息会基于流量形式的不同而采取不同的发送方式。 好处是需要发送DPD的时候才发,节约资源和网络带宽;缺点是检测到IPSec VPN网关故障所需时间稍长。
实验拓扑: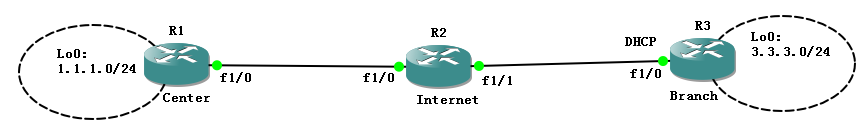
默认配置完成,此时是可以建立起IPSec VPN的:
Site2#sho cry en conn active
Crypto Engine Connections
ID Type Algorithm Encrypt Decrypt LastSeqN IP-Address
1 IPsec DES+MD5 0 10 13 23.1.1.3
2 IPsec DES+MD5 10 0 0 23.1.1.3
1001 IKE SHA+DES 0 0 0 23.1.1.3
那么我们来看一下在没有DPD功能的时候:
Site1#debug crypto isakmp
Crypto ISAKMP debugging is on
Internet(config)#int f1/0
Internet(config-if)#shu
Site1#ping 3.3.3.3 so 1.1.1.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 3.3.3.3, timeout is 2 seconds:
Packet sent with a source address of 1.1.1.1
.....
Success rate is 0 percent (0/5)
Site1#sho cry en conn active
Crypto Engine Connections
ID Type Algorithm Encrypt Decrypt LastSeqN IP-Address
1 IPsec DES+MD5 0 8 9 12.1.1.1
2 IPsec DES+MD5 19 0 0 12.1.1.1
1001 IKE SHA+DES 0 0 0 12.1.1.1
这说明没有启用DPD技术的时候,IPSec VPN无法探测有问题的网关,因此会继续使用又问题的IPSec SA加密数据包,接下来再看启用了DPD的情况:
Site1(config)#crypto isakmp keepalive ?
<10-3600> Number of seconds between keep alives
Site1(config)#crypto isakmp keepalive 10 periodic
Site2(config)#crypto isakmp keepalive 10 periodic
Site1/2#cle crypto isakmp
Site1/2#cle crypto sa
Internet(config)#int f1/0
Internet(config-if)#no shu
此时Site1和Site2之间又恢复了通信:
Site1#ping 3.3.3.3 so 1.1.1.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 3.3.3.3, timeout is 2 seconds:
Packet sent with a source address of 1.1.1.1
.!!!!
Success rate is 80 percent (4/5), round-trip min/avg/max = 184/208/240 ms
那么在来看一下DPD检测失效网关的效果:
Apr 22 23:56:20.535: ISAKMP:(1002):Sending NOTIFY DPD/R_U_THERE protocol 1
spi 1746747408, message ID = 1135002381
*Apr 22 23:56:20.535: ISAKMP:(1002): seq. no 0x1B47B85D
*Apr 22 23:56:20.535: ISAKMP:(1002): sending packet to 23.1.1.3 my_port 500 peer_port 500 (I) QM_IDLE
*Apr 22 23:56:20.535: ISAKMP:(1002):Sending an IKE IPv4 Packet.
*Apr 22 23:56:20.539: ISAKMP:(1002):purging node 1135002381
*Apr 22 23:56:20.539: ISAKMP:(1002):Input = IKE_MESG_FROM_TIMER, IKE_TIMER_IM_ALIVE
*Apr 22 23:56:20.543: ISAKMP:(1002):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE
Site1#
*Apr 22 23:56:20.767: ISAKMP:(1002):purging node 593664099
Site1#
*Apr 22 23:56:22.539: ISAKMP:(1002):DPD incrementing error counter (1/5)
*Apr 22 23:56:22.539: ISAKMP: set new node 511611758 to QM_IDLE
*Apr 22 23:56:22.539: ISAKMP:(1002):Sending NOTIFY DPD/R_U_THERE protocol 1
spi 1746747408, message ID = 511611758
*Apr 22 23:56:22.539: ISAKMP:(1002): seq. no 0x1B47B85E
*Apr 22 23:56:22.539: ISAKMP:(1002): sending packet to 23.1.1.3 my_port 500 peer_port 500 (I) QM_IDLE
*Apr 22 23:56:22.543: ISAKMP:(1002):Sending an IKE IPv4 Packet.
*Apr 22 23:56:22.543: ISAKMP:(1002):purging node 511611758
*Apr 22 23:56:22.547: ISAKMP:(1002):Input = IKE_MESG_FROM_TIMER, IKE_TIMER_PEERS_ALIVE
Site1#
*Apr 22 23:56:22.547: ISAKMP:(1002):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE
Site1#
*Apr 22 23:56:24.543: ISAKMP:(1002):DPD incrementing error counter (2/5)
*Apr 22 23:56:24.543: ISAKMP: set new node -2042738143 to QM_IDLE
*Apr 22 23:56:24.547: ISAKMP:(1002):Sending NOTIFY DPD/R_U_THERE protocol 1
spi 1746747408, message ID = -2042738143
*Apr 22 23:56:24.547: ISAKMP:(1002): seq. no 0x1B47B85F
*Apr 22 23:56:24.551: ISAKMP:(1002): sending packet to 23.1.1.3 my_port 500 peer_port 500 (I) QM_IDLE
*Apr 22 23:56:24.551: ISAKMP:(1002):Sending an IKE IPv4 Packet.
*Apr 22 23:56:24.551: ISAKMP:(1002):purging node -2042738143
*Apr 22 23:56:24.555: ISAKMP:(1002):Input = IKE_MESG_FROM_TIMER, IKE_TIMER_PEERS_ALIVE
Site1#
*Apr 22 23:56:24.555: ISAKMP:(1002):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE
Site1#
*Apr 22 23:56:26.555: ISAKMP:(1002):DPD incrementing error counter (3/5)
*Apr 22 23:56:26.555: ISAKMP: set new node 1264419706 to QM_IDLE
*Apr 22 23:56:26.559: ISAKMP:(1002):Sending NOTIFY DPD/R_U_THERE protocol 1
spi 1746747408, message ID = 1264419706
*Apr 22 23:56:26.559: ISAKMP:(1002): seq. no 0x1B47B860
*Apr 22 23:56:26.559: ISAKMP:(1002): sending packet to 23.1.1.3 my_port 500 peer_port 500 (I) QM_IDLE
*Apr 22 23:56:26.563: ISAKMP:(1002):Sending an IKE IPv4 Packet.
*Apr 22 23:56:26.563: ISAKMP:(1002):purging node 1264419706
*Apr 22 23:56:26.567: ISAKMP:(1002):Input = IKE_MESG_FROM_TIMER, IKE_TIMER_PEERS_ALIVE
Site1#
*Apr 22 23:56:26.567: ISAKMP:(1002):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE
Site1#
*Apr 22 23:56:28.007: ISAKMP:(1002):purging node 519630341
*Apr 22 23:56:28.567: ISAKMP:(1002):DPD incrementing error counter (4/5)
*Apr 22 23:56:28.567: ISAKMP: set new node 2041023417 to QM_IDLE
*Apr 22 23:56:28.571: ISAKMP:(1002):Sending NOTIFY DPD/R_U_THERE protocol 1
spi 1746747408, message ID = 2041023417
*Apr 22 23:56:28.571: ISAKMP:(1002): seq. no 0x1B47B861
*Apr 22 23:56:28.571: ISAKMP:(1002): sending packet to 23.1.1.3 my_port 500 peer_port 500 (I) QM_IDLE
*Apr 22 23:56:28.575: ISAKMP:(1002):Sending an IKE IPv4 Packet.
*Apr 22 23:56:28.575: ISAKMP:(1002):purging node 2041023417
Site1#
*Apr 22 23:56:28.579: ISAKMP:(1002):Input = IKE_MESG_FROM_TIMER, IKE_TIMER_PEERS_ALIVE
*Apr 22 23:56:28.579: ISAKMP:(1002):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE
Site1#
*Apr 22 23:56:30.579: ISAKMP:(1002):DPD incrementing error counter (5/5)
*Apr 22 23:56:30.579: ISAKMP:(1002):peer 23.1.1.3 not responding!
*Apr 22 23:56:30.583: ISAKMP:(1002):Input = IKE_MESG_FROM_TIMER, IKE_TIMER_PEERS_ALIVE
*Apr 22 23:56:30.583: ISAKMP:(1002):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE
*Apr 22 23:56:30.595: ISAKMP (1002): No more ipsec tunnels for this SA.
*Apr 22 23:56:30.599: ISAKMP: set new node 1589052764 to QM_IDLE
*Apr 22 23:56:30.603: ISAKMP:(1002): sending packet to 23.1.1.3 my_port 500 peer_port 500 (I) QM_IDLE
*Apr 22 23:56:30.603: ISAKMP:(1002):Sending an IKE IPv4 Packet.
*Apr 22 23:56:30.607: ISAKMP:(1002):purging node 1589052764
*Apr 22 23:56:30.607: ISAKMP:(1002):Input = IKE_MESG_FROM_IPSEC, IKE_PHASE2_DEL
*Apr 22 23:56:30.611: ISAKMP:(1002):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE
*Apr 22 23:56:30.619: ISAKMP: set new node 1168250615 to QM_IDLE
*Apr 22 23:56:30.619: ISAKMP:(1002): send
Site1#ing packet to 23.1.1.3 my_port 500 peer_port 500 (I) QM_IDLE
*Apr 22 23:56:30.623: ISAKMP:(1002):Sending an IKE IPv4 Packet.
*Apr 22 23:56:30.623: ISAKMP:(1002):purging node 1168250615
*Apr 22 23:56:30.627: ISAKMP:(1002):Input = IKE_MESG_INTERNAL, IKE_PHASE1_DEL
*Apr 22 23:56:30.627: ISAKMP:(1002):Old State = IKE_P1_COMPLETE New State = IKE_DEST_SA
*Apr 22 23:56:30.635: ISAKMP:(1002):deleting SA reason "No reason" state (I) QM_IDLE (peer 23.1.1.3)
*Apr 22 23:56:30.635: ISAKMP: Unlocking peer struct 0x68665020 for isadb_mark_sa_deleted(), count 0
*Apr 22 23:56:30.639: ISAKMP: Deleting peer node by peer_reap for 23.1.1.3: 68665020
*Apr 22 23:56:30.643: ISAKMP:(1002):Input = IKE_MESG_FROM_PEER, IKE_MM_EXCH
*Apr 22 23:56:30.643: ISAKMP:(1002):Old State = IKE_DEST_SA New State = IKE_DEST_SA
*Apr 22 23:56:30.887: ISAKMP:(1002):purging node -1414911362
可以看到的是:Site1上的DPD中,如果Site1周期性的发送的DPD信息没有得到远端的确认,那么会连续发送5次,若5次都没有远端的确认。site1马上就会清楚本地的IPSec和ISAKMP安全关联:
Site1#show crypto engine connections active
Crypto Engine Connections
ID Type Algorithm Encrypt Decrypt LastSeqN IP-Address
Site2#sho cry en conn active
Crypto Engine Connections
ID Type Algorithm Encrypt Decrypt LastSeqN IP-Address
以上的配置DPD会周期的发送。DPD按需工作模式会基于流量形式的不同而采取不同的发送方式,若IPSec VPN有持续的流量加密发送,并且还能持续解密对端发来的数据,那么此时,按需工作模式就会认为一切正常,不需要发送DPD:而在当一个数据加密发送出去,在一定的时间内没有收到任何的解密数据包额情况下,DPD才会怀疑IPSec VPN出现问题,发送DPD。若很快收到了DPD确认,那么表示远端正常,若一定的时间内没有收到DPD确认,那么也是5次之后,删除所有安全连接。
下面是按需发送的配置:
Site1(config)#no crypto isakmp keepalive 10 periodic
Site1(config)#crypto isakmp keepalive 10 //加密数据发出后10秒没有收到解密数据包,就发送DPD进行探测
Site2(config)#no crypto isakmp keepalive 10 periodic
Site2(config)#crypto isakmp keepalive 10
值得注意的是:在10秒后连续5次Site1删除本地的所有安全关联,但是在Site2上还是存在,除非Site2发出加密数据包,10秒内未得到解密数据包。
**************RRI********************
什么时候注入(动态产生)这一条路由呢?
在产生IPSec SA 的同时也产生这条路由,在IPSec SA消失的时候,也随之消失。由RRI产生的路由,其目的网络为远端通信网络,下一跳为远端加密点(也可以认为是隧道的终点)。
下面是测试RRI的工作特性,拓扑如下: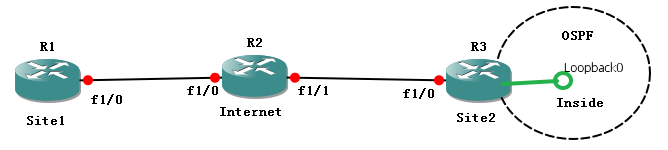
默认经典的IPSec VPN以及建立成功:
Site2#sho cry en connections active
Crypto Engine Connections
ID Type Algorithm Encrypt Decrypt LastSeqN IP-Address
1 IPsec DES+MD5 0 3 4 23.1.1.3
2 IPsec DES+MD5 3 0 0 23.1.1.3
1001 IKE SHA+DES 0 0 0 23.1.1.3
Site2(config)#crypto map cisco 10 ipsec-isakmp
Site2(config-crypto-map)#reverse-route
Site2(config-crypto-map)#set reverse-route tag 10
This will remove previously installed VPN routes and SAs
Site2(config-crypto-map)#exi
Site2(config)#route-map RRI permit 10
Site2(config-route-map)#match tag 10
Site2(config-route-map)#exi
Site2(config)#int f1/1
Site2(config-if)#ip add 35.1.1.3 255.255.255.0
Site2(config-if)#no shu
Site2(config-if)#int lo0
Site2(config-if)#no ip add
Site2(config-if)#end
Site2#conf t
Site2(config)#router os 1
Site2(config-router)#router-id 2.2.2.2
Site2(config-router)#net 35.1.1.0 0.0.0.255 a 0
Site2(config-router)#end
R5(config)#int f1/0
R5(config-if)#ip add 35.1.1.5 255.255.255.0
R5(config-if)#no sh
R5(config)#int lo0
R5(config-if)#ip add 3.3.3.3 255.255.255.0
R5(config-if)#router os 1
R5(config-router)#router-id 5.5.5.5
R5(config-router)#net 0.0.0.0 255.255.255.255 a 0
R5(config-router)#exi
现在的情况是在R5上没有R1的1.1.1.1的路由,因为反向注入还没有实施,所以即使匹配上了感兴趣流,但是还是不能通信
Site1#cle access-list counters
Site1#ping 3.3.3.3 so 1.1.1.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 3.3.3.3, timeout is 2 seconds:
Packet sent with a source address of 1.1.1.1
.....
Success rate is 0 percent (0/5)
Site2#sho access-lists
Extended IP access list vpn
10 permit ip 3.3.3.0 0.0.0.255 1.1.1.0 0.0.0.255 (4 matches)
下面是将RRI注入OSPF网络的配置:
Site2(config)#router os 1
Site2(config-router)#redistribute static route-map RRI subnets
Site2#sho ip ro static
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route, + - replicated route
Gateway of last resort is 23.1.1.2 to network 0.0.0.0
S* 0.0.0.0/0 [1/0] via 23.1.1.2
1.0.0.0/24 is subnetted, 1 subnets
S 1.1.1.0 [1/0] via 12.1.1.1
可以看到的是这里的RRI产生的静态是下一跳为12.1.1.1的,就是peer的加密点的地址
Site1#ping 3.3.3.3 so 1.1.1.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 3.3.3.3, timeout is 2 seconds:
Packet sent with a source address of 1.1.1.1
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 328/365/408 ms
Site1#show crypto engine connections active
Crypto Engine Connections
ID Type Algorithm Encrypt Decrypt LastSeqN IP-Address
7 IPsec DES+MD5 0 5 5 12.1.1.1
8 IPsec DES+MD5 5 0 0 12.1.1.1
1002 IKE SHA+DES 0 0 0 12.1.1.1
此时在R5的路由表中肯定有OE2的OSPF路由了:
R5#sho ip ro ospf
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route, + - replicated route
Gateway of last resort is not set
1.0.0.0/24 is subnetted, 1 subnets
O E2 1.1.1.0 [110/20] via 35.1.1.3, 00:00:03, FastEthernet1/0


