配置SVTI
路由器SVTI站点到站点VPN
在IOS 12.4之前建立安全的站点间隧道只能采用GRE over IPSec,从IOS 12.4之后设计了一种全新的隧道技术,即VIT(Virtual Tunnel Interface),这种技术是直接采用IPSec来创建的一个VTI隧道接口。相比GRE over IPSec,VTI技术减少了每个包GRE头部的那4B。
VTI分类:SVTI(静态VTI)和DVTI(Dynamic VTI)动态VTI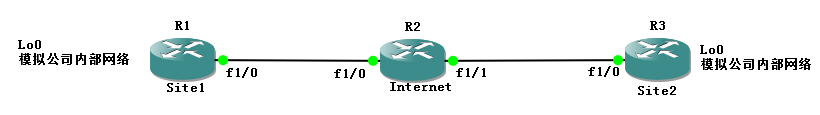
默认基本配置完成
R1的配置
crypto isakmp policy 10
authentication pre-share
crypto isakmp key cisco address 23.1.1.3
!
crypto ipsec transform-set trans esp-des esp-md5-hmac
!
crypto ipsec profile SVTI//名字是SVTI
set transform-set trans
!
interface Loopback0
ip address 1.1.1.1 255.255.255.0
!
interface Tunnel13
ip address 13.1.1.1 255.255.255.0
tunnel source 12.1.1.1
tunnel mode ipsec ipv4
tunnel destination 23.1.1.3
tunnel protection ipsec profile SVTI
!
interface FastEthernet1/0
ip address 12.1.1.1 255.255.255.0
duplex auto
speed auto
!
router ospf 1
router-id 1.1.1.1
log-adjacency-changes
network 1.1.1.0 0.0.0.255 area 0
network 13.1.1.0 0.0.0.255 area 0
!
ip route 0.0.0.0 0.0.0.0 12.1.1.2
R2的配置:
interface FastEthernet1/0
ip address 12.1.1.2 255.255.255.0
duplex auto
speed auto
!
!
interface FastEthernet1/1
ip address 23.1.1.2 255.255.255.0
duplex auto
speed auto
R3的配置:
crypto isakmp policy 10
authentication pre-share
crypto isakmp key cisco address 12.1.1.1
!
crypto ipsec transform-set trans esp-des esp-md5-hmac
!
crypto ipsec profile SVTI
set transform-set trans
!
interface Loopback0
ip address 3.3.3.3 255.255.255.0
!
interface Tunnel13
ip address 13.1.1.3 255.255.255.0
tunnel source 23.1.1.3
tunnel mode ipsec ipv4
tunnel destination 12.1.1.1
tunnel protection ipsec profile SVTI
!
interface FastEthernet1/0
ip address 23.1.1.3 255.255.255.0
duplex auto
speed auto
!
router ospf 1
router-id 3.3.3.3
log-adjacency-changes
network 3.3.3.0 0.0.0.255 area 0
network 13.1.1.0 0.0.0.255 area 0
!
ip route 0.0.0.0 0.0.0.0 23.1.1.2
R1#show crypto engine connections active
Crypto Engine Connections
ID Type Algorithm Encrypt Decrypt LastSeqN IP-Address
1 IPsec DES+MD5 0 196 224 12.1.1.1
2 IPsec DES+MD5 232 0 0 12.1.1.1
1001 IKE SHA+DES 0 0 0 12.1.1.1
R1#show crypto ipsec sa
interface: Tunnel13
Crypto map tag: Tunnel13-head-0, local addr 12.1.1.1
protected vrf: (none)
local ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)//可以看见这里的感兴趣流为任意源到任意目的,但是注意的是不是所有加入site1的都加密,而是进入SVTI的流量才会加密
remote ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
current_peer 23.1.1.3 port 500
PERMIT, flags={origin_is_acl,}
#pkts encaps: 240, #pkts encrypt: 240, #pkts digest: 240
#pkts decaps: 201, #pkts decrypt: 201, #pkts verify: 201
#pkts compressed: 0, #pkts decompressed: 0
#pkts not compressed: 0, #pkts compr. failed: 0
#pkts not decompressed: 0, #pkts decompress failed: 0
#send errors 0, #recv errors 30
local crypto endpt.: 12.1.1.1, remote crypto endpt.: 23.1.1.3
path mtu 1500, ip mtu 1500, ip mtu idb FastEthernet1/0
current outbound spi: 0x8965E6D8(2305156824)
PFS (Y/N): N, DH group: none
inbound esp sas:
spi: 0xE60BC2FF(3859530495)
transform: esp-des esp-md5-hmac ,
in use settings ={Tunnel, }
conn id: 1, flow_id: SW:1, sibling_flags 80000046, crypto map: Tunnel13-head-0
sa timing: remaining key lifetime (k/sec): (4595852/1924)
IV size: 8 bytes
replay detection support: Y
Status: ACTIVE
inbound ah sas:
inbound pcp sas:
outbound esp sas:
spi: 0x8965E6D8(2305156824)
transform: esp-des esp-md5-hmac ,
in use settings ={Tunnel, }
conn id: 2, flow_id: SW:2, sibling_flags 80000046, crypto map: Tunnel13-head-0
sa timing: remaining key lifetime (k/sec): (4595851/1924)
IV size: 8 bytes
replay detection support: Y
Status: ACTIVE
outbound ah sas:
outbound pcp sas:


