Windows驱动开发学习记录-Windbg打印Shadow SSDT 脚本
一、脚本
-
X86环境
1 aS ufLinkS "<u><col fg=\\\"emphfg\\\"><link name=\\\"%p\\\" cmd=\\\"uf 0x%p\\\">";
2 aS ufLinkE "</link></col></u>";
3
4 r $t1 = nt!KeServiceDescriptorTableShadow;
5 r $t2 = @$t1 + 0x04*4;
6 r $t3 = poi(@$t2 + 0x8);
7 r $t2 = poi(@$t2);
8
9 .printf "\n\nKeServiceDescriptorTableShadow->W32pServiceTable: %p\nKeServiceDescriptorTableShadow->Count: %d\n", @$t2, @$t3;
10 .printf "\nOrd Address fnAddr Symbols\n";
11 .printf "--------------------------------\n\n";
12
13 .for (r $t0 = 0; @$t0 != @$t3; r $t0 = @$t0 + 1)
14 {
15 r @$t4 = (poi(@$t2 + @$t0 * 4))
16
17
18 .printf /D "[%3d] ${ufLinkS}%p${ufLinkE} (%y)\n", @$t0, @$t4, @$t4, @$t4, @$t4;
19 }
20
21 .printf "\n- end -\n";
-
x64环境
1 aS ufLinkS "<u><col fg=\\\"emphfg\\\"><link name=\\\"%p\\\" cmd=\\\"uf 0x%p\\\">";
2 aS ufLinkE "</link></col></u>";
3
4 r $t1 = nt!KeServiceDescriptorTableShadow;
5 r $t2 = @$t1 + 0x08*4;
6 r $t3 = poi(@$t2 + 0x10);
7 r $t2 = poi(@$t2);
8
9 .printf "\n\nKeServiceDescriptorTableShadow->W32pServiceTable: %p\nKeServiceDescriptorTableShadow->Count: %d\n", @$t2, @$t3;
10 .printf "\nOrd Address Symbols\n";
11 .printf "--------------------------------\n\n";
12
13 .for (r $t0 = 0; @$t0 != @$t3; r $t0 = @$t0 + 1)
14 {
15 r @$t4 = (poi(@$t2 + @$t0 * 4)) & 0x00000000`FFFFFFFF;
16 $$.printf "2. %p\n", @$t4;
17
18 .if ( @$t4 & 0x80000000 )
19 {
20 r @$t4 = (@$t4 >> 4) | 0xFFFFFFFF`F0000000;
21 r @$t4 = 0 - @$t4;
22 r @$t4 = @$t2 - @$t4;
23 }
24 .else
25 {
26 r @$t4 = (@$t4 >> 4);
27 r @$t4 = (@$t2 + @$t4);
28 }
29
30 .printf /D /os "[%3d] ${ufLinkS}%p${ufLinkE} (%y)\n", @$t0, @$t4, @$t4, @$t4, @$t4;
31 }
32
33 .printf "\n- end -\n";
二、使用方法
因为Shadow SSDT 的W32pServiceTable表数据在系统进程是不可访问的,所以要先附加到可以访问该数据的进程,我这里选的是桌面进程explorer.exe。
先执行 !process 0 0 explorer.exe,查找桌面进程的EPROCESS地址。
4: kd> !process 0 0 explorer.exe
PROCESS 893e5bc0 SessionId: 1 Cid: 03b0 Peb: 7ffd6000 ParentCid: 0080
DirBase: be4bb6c0 ObjectTable: 9b2dbac8 HandleCount: 572.
Image: explorer.exe
然后附加到该进程,.process 893e5bc0
4: kd> .process 893e5bc0 ReadVirtual: 893e5bd8 not properly sign extended Implicit process is now 893e5bc0 WARNING: .cache forcedecodeuser is not enabled
重新加载win32k.sys的符号
4: kd> .reload win32k.sys Press ctrl-c (cdb, kd, ntsd) or ctrl-break (windbg) to abort symbol loads that take too long. Run !sym noisy before .reload to track down problems loading symbols.
之后再执行脚本, "$><"后边加上脚本路径
4: kd> $><E:\驱动代码\x86SSDTShadow.txt
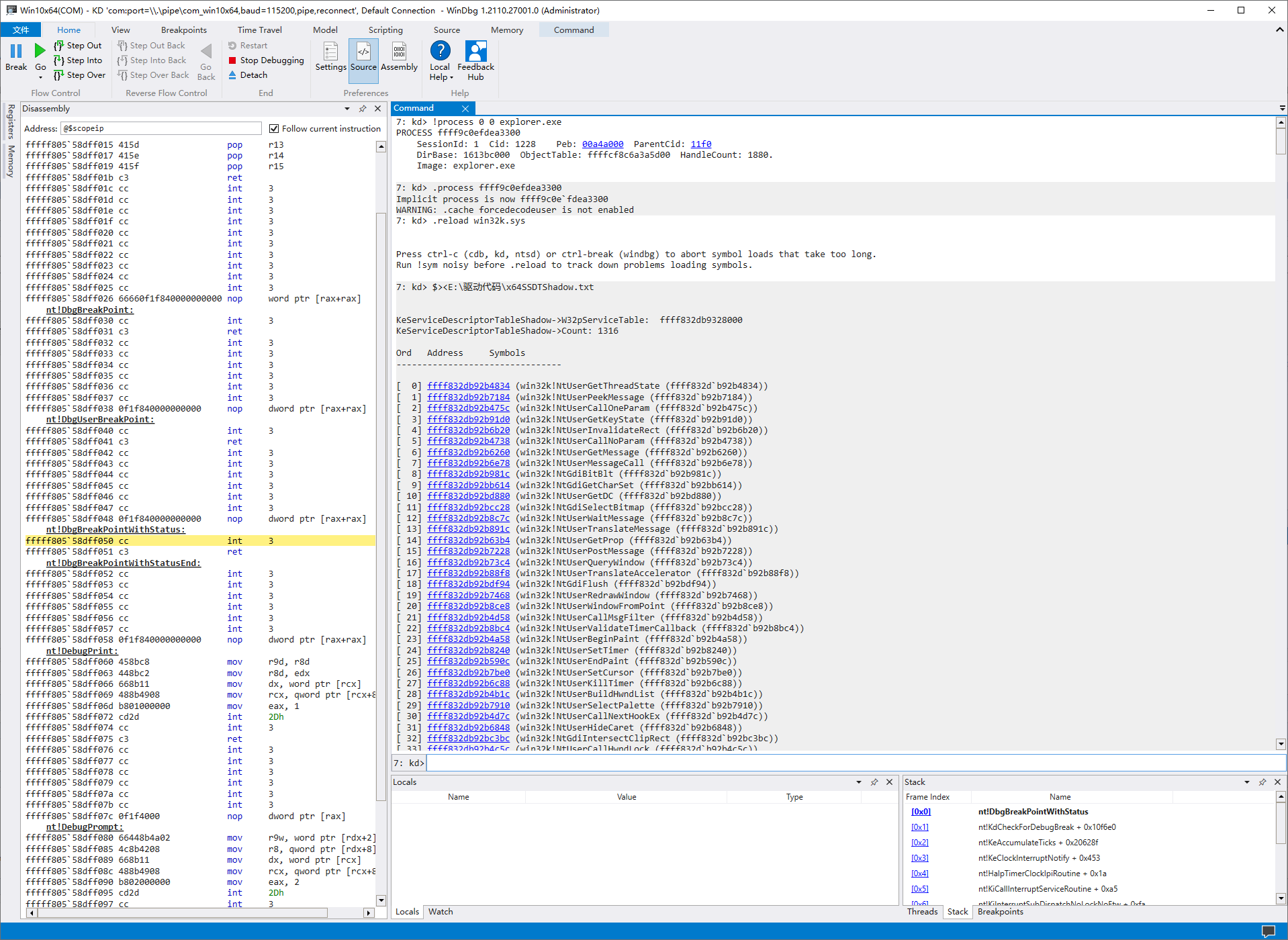
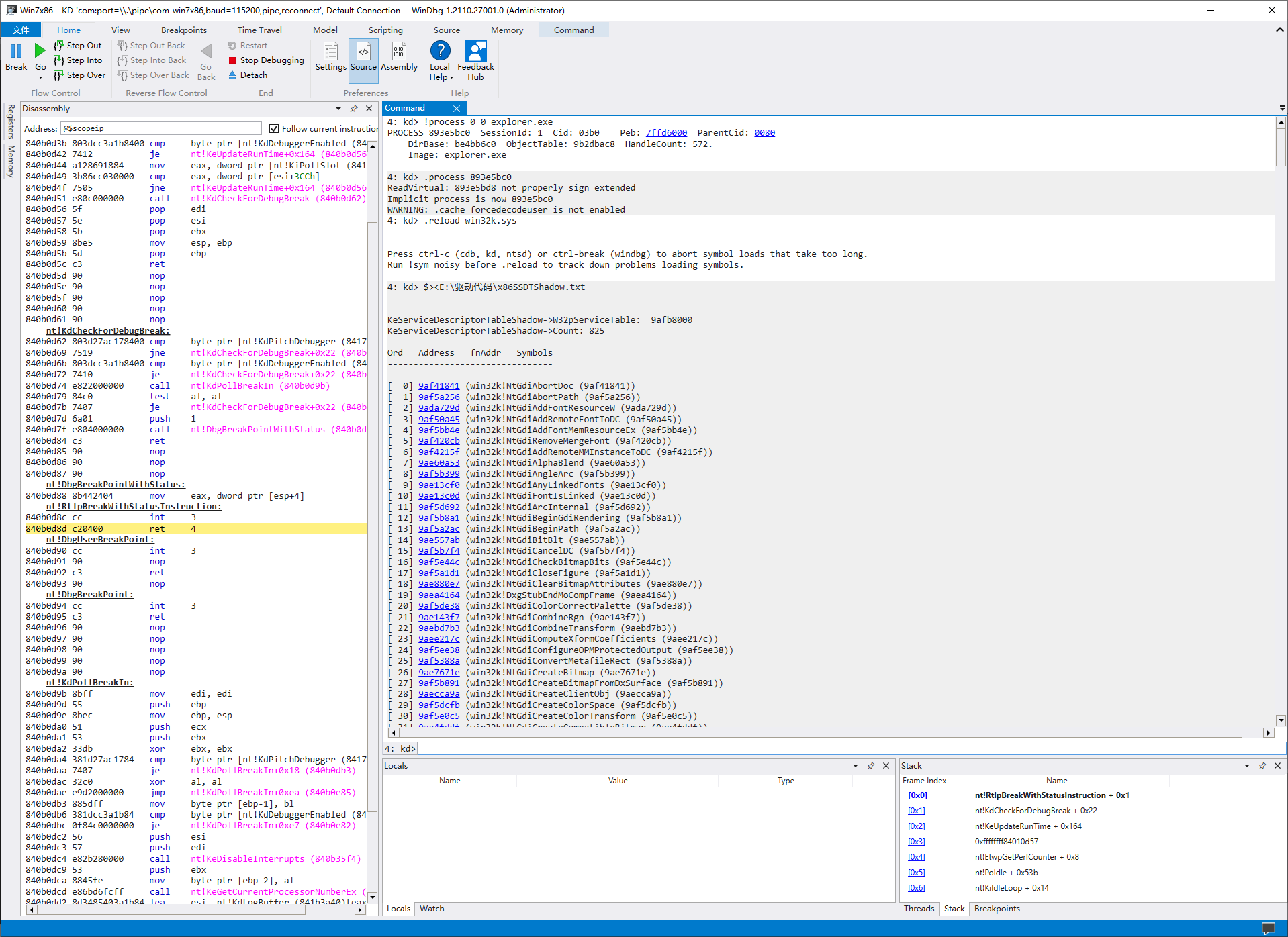
三、测试效果
-
x86(Win7 x86)
-
x64(Win10 x64)