有人昨天以为rc4用的就是空秘钥,那么他是谁呢
通过在字符串里找到DASCTF的关键字,一直交叉引用可以找到主要逻辑
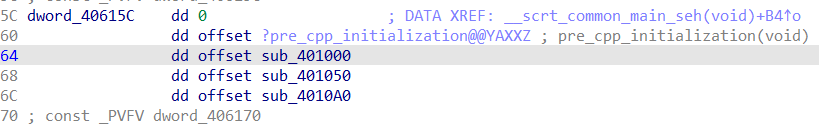
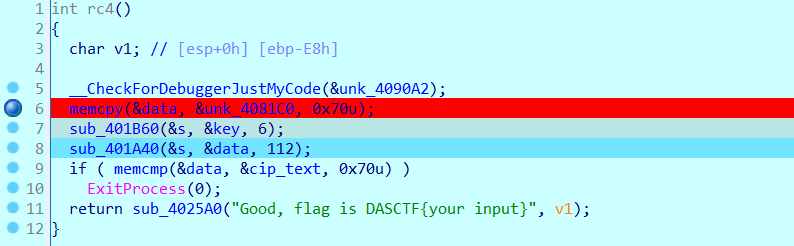
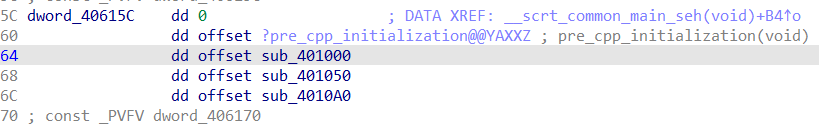
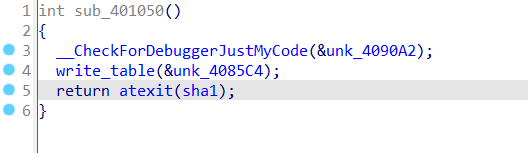
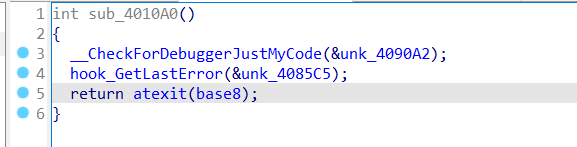
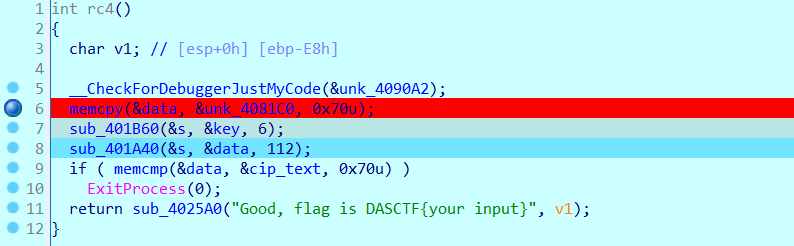
这里注册的三个函数就是整个题的流程了
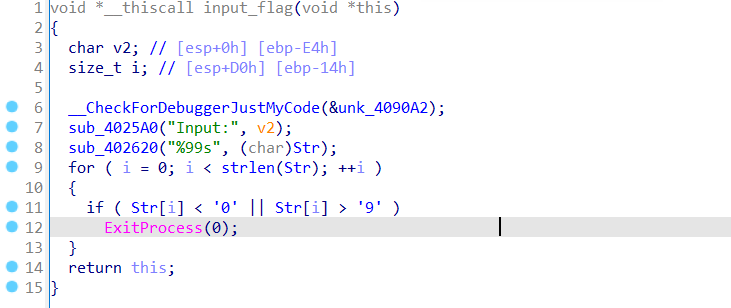
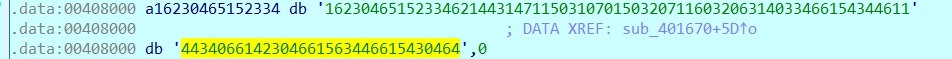
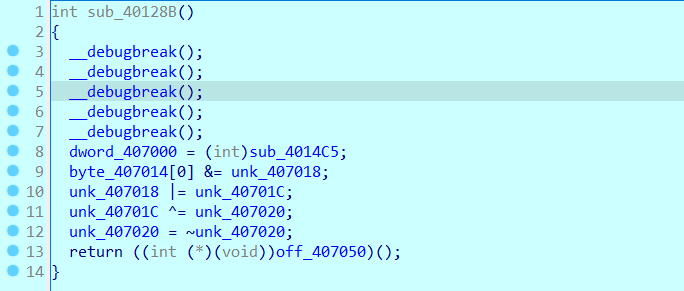
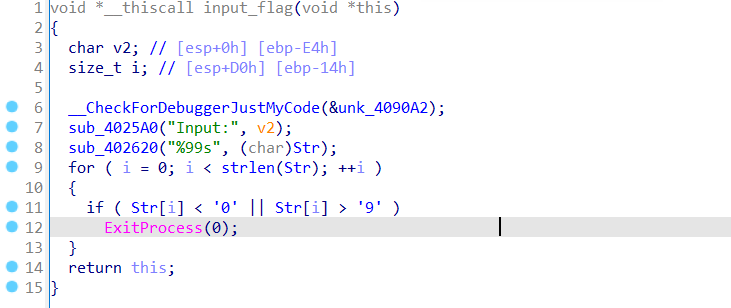
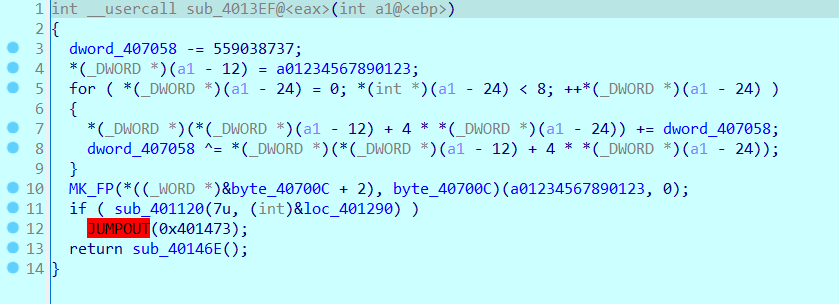
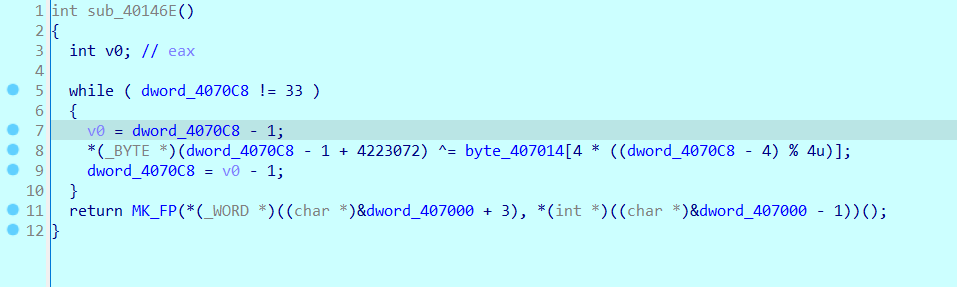
第一个函数里有输入,可以发现flag仅为0-9,然后还通过atexit注册了check函数,是一个很普通的rc4加密
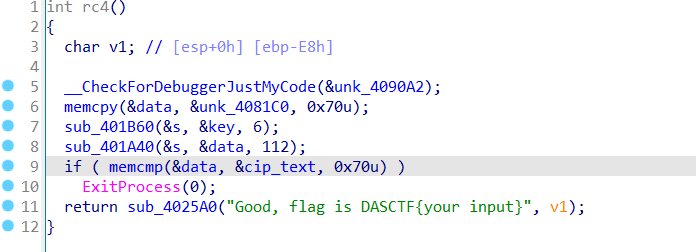
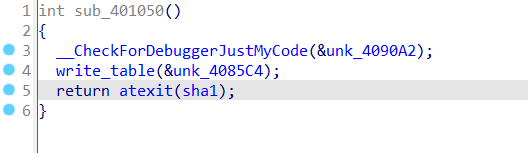
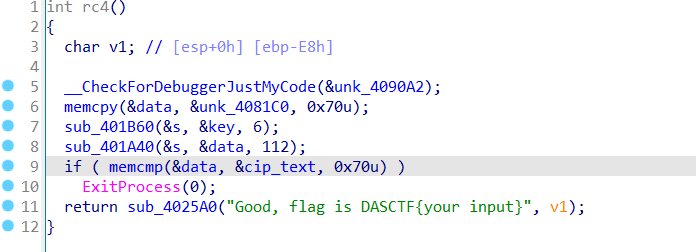
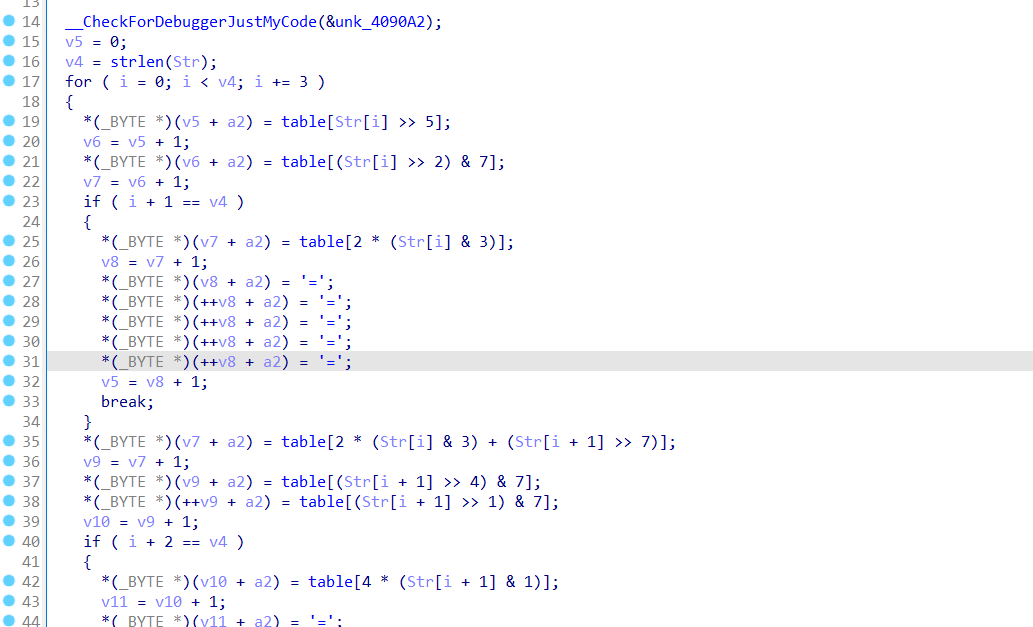
第二个函数先在write_table里通过取反拿到了一个01234567的表,然后通过atexit注册了一个sha-1,但是好像有一些改动,猜测这里仅仅是一个验证
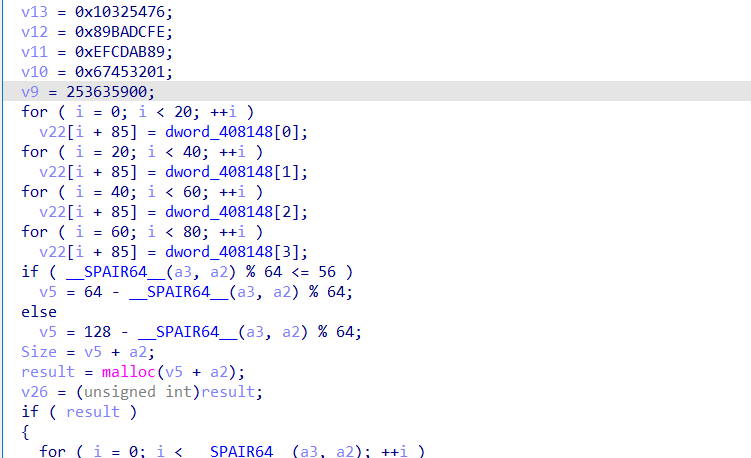
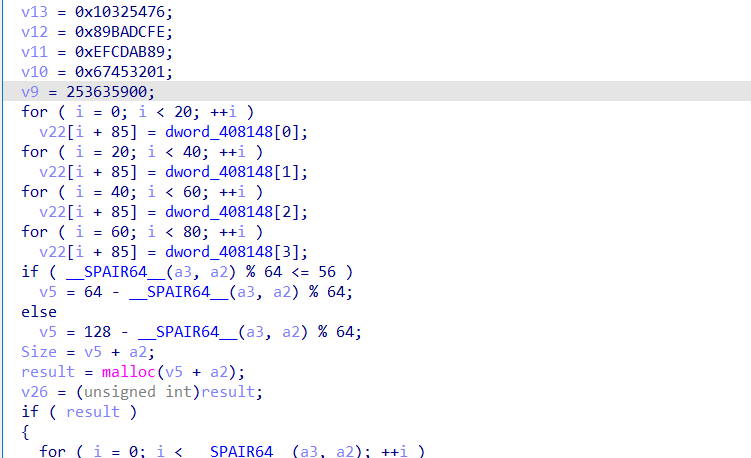
可以通过上面4个magic number初步确定其是sha-1加密
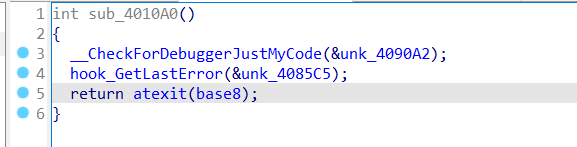
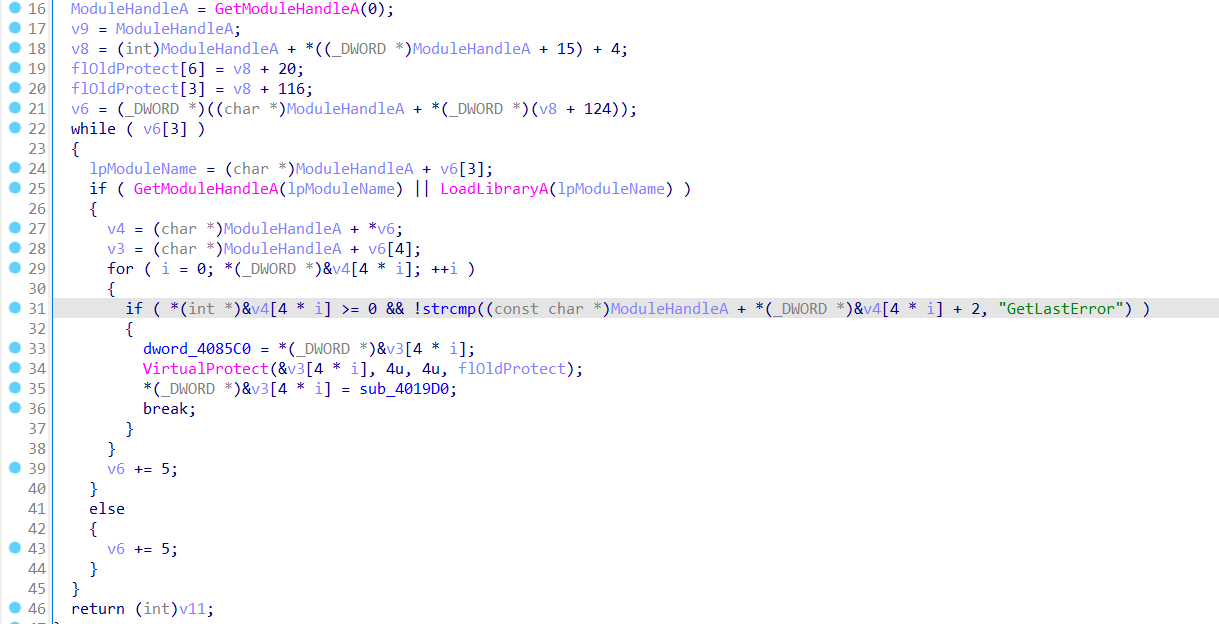
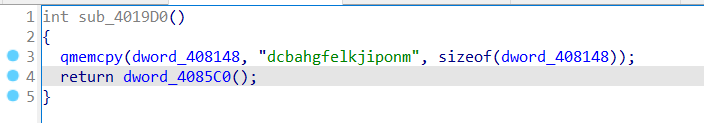
最后一部分先hook了GetLastError函数,然后注册了base8加密
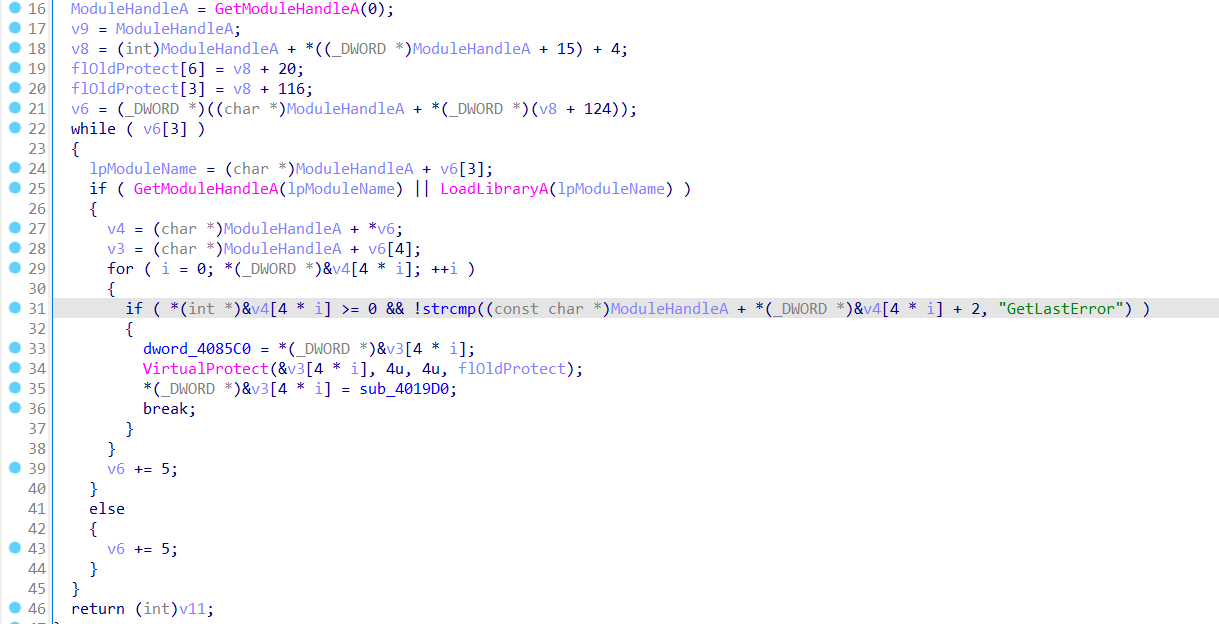
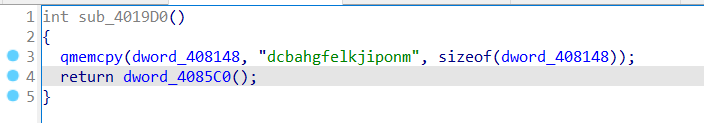
大概是通过填充密码常量来hook的,这部分不重要
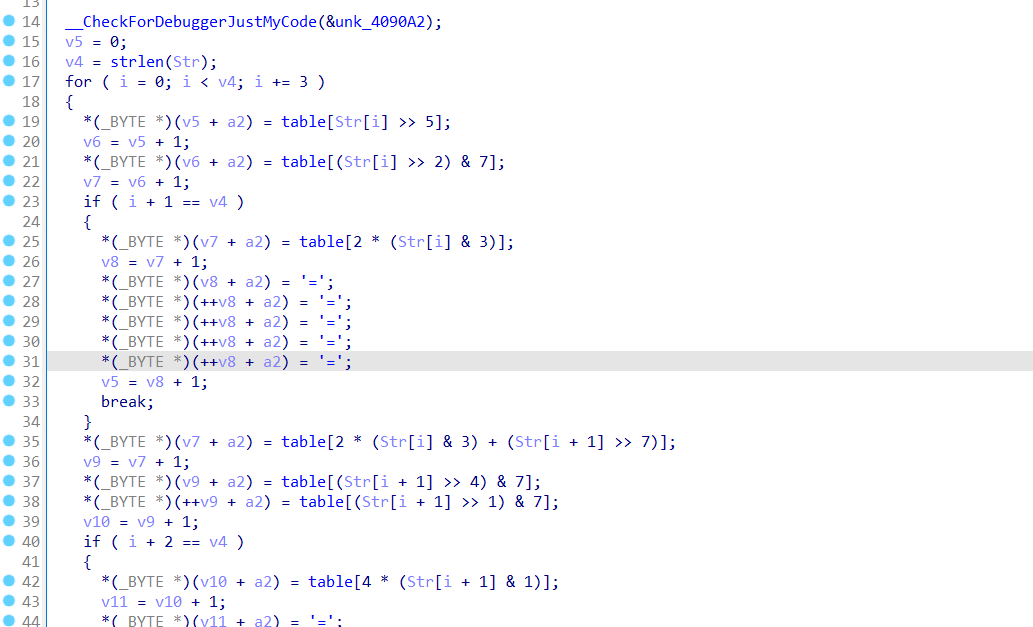
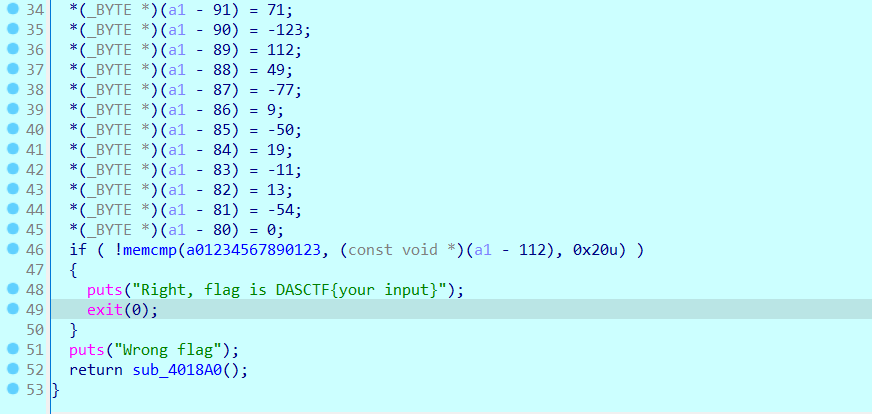
通过之前观察的table的值等可以发现是base8加密,并且只有这个函数访问过最开始输入的flag明文
综合一下上面得到的信息,现在就该动调了。
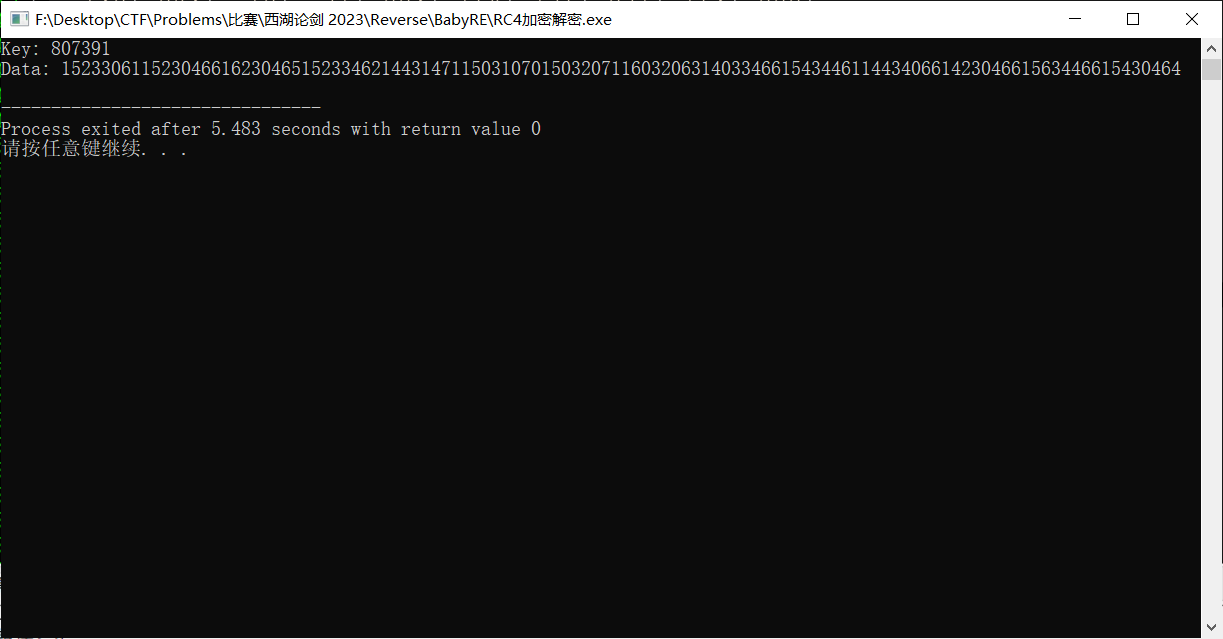
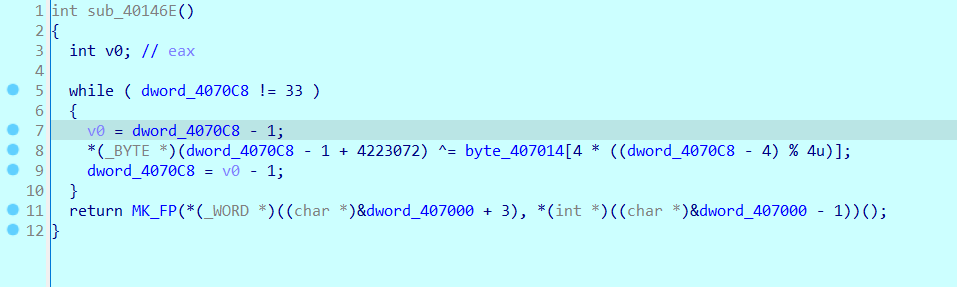
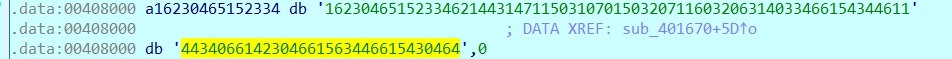
这里可以解出一段flag是915572239428449843076691286116796614
随后类似sha-1的加密部分并没法看出什么东西
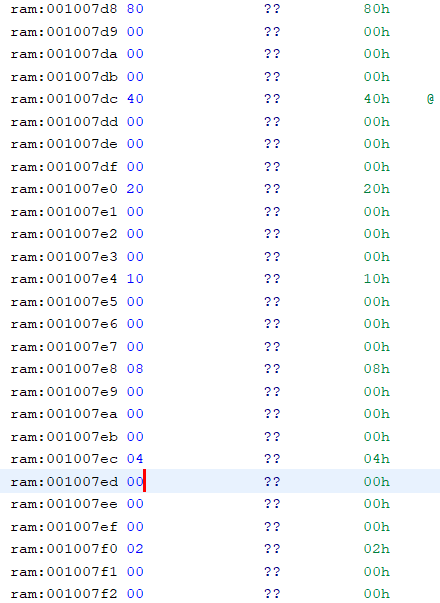
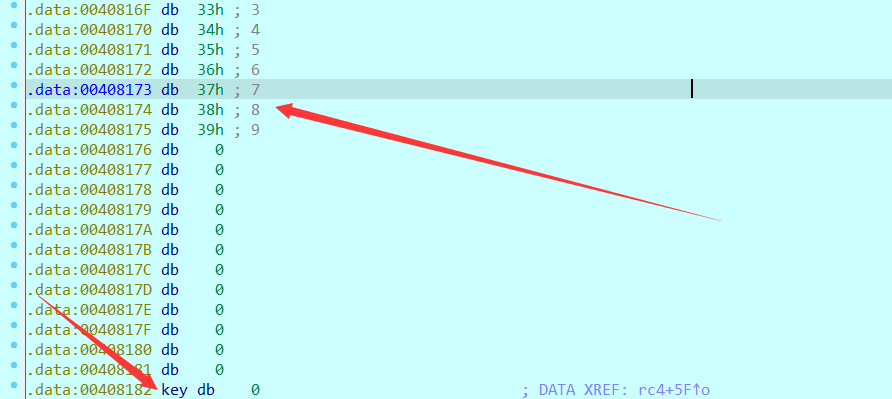
rc4的部分,可以看到key的长度为6,密文长度为112,但点进key后什么是一串0,昨天赛中做的有点急,以为真的是空秘钥,复现的时候发现:
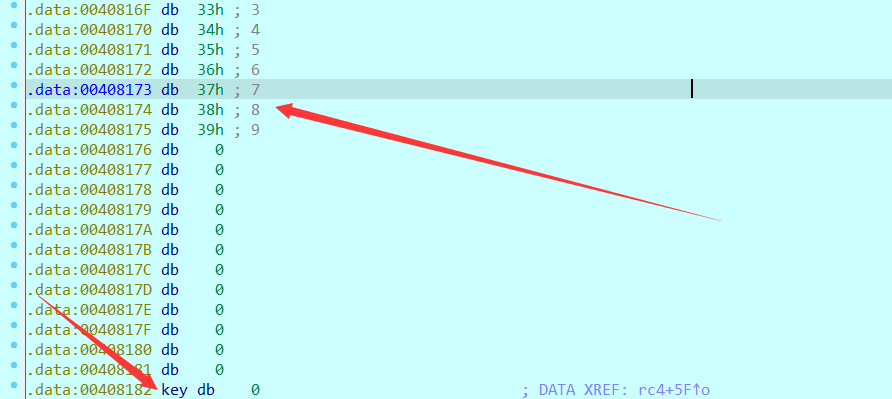
上面那串是我们输入的flag,数了一下发现是42位,下面空的0是因为我的输入只有30位。
联系一下上面rc4部分,很容易想到:flag一共48位,并且使用flag后6位作为rc4的密钥。
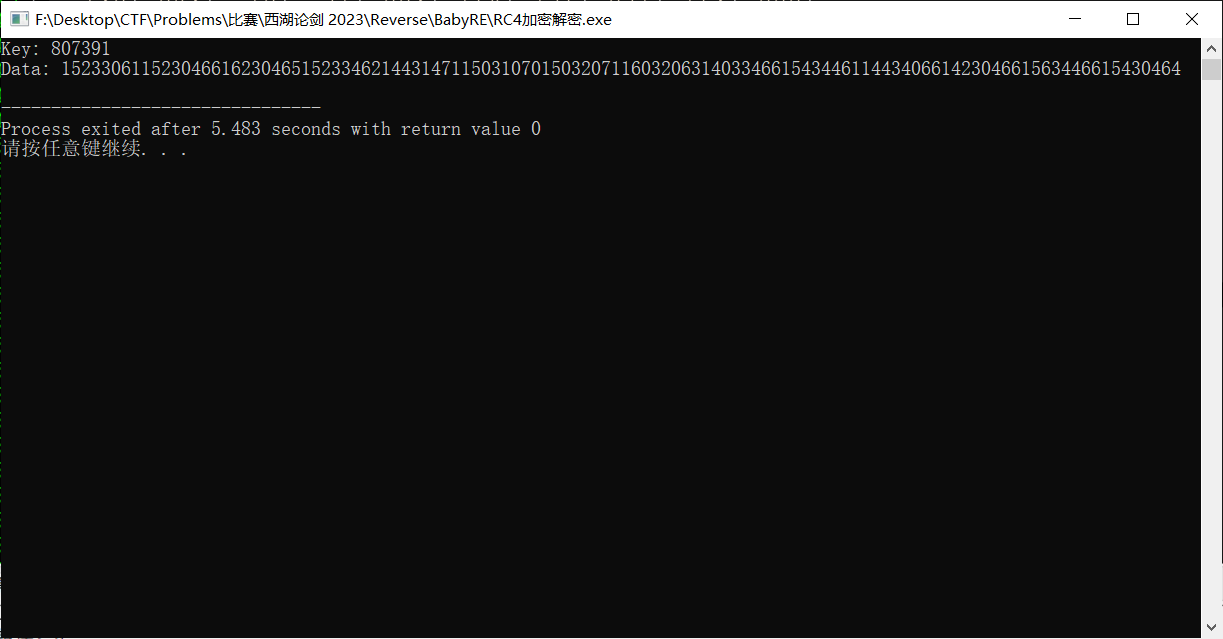
现在的形式很明显了:由于密钥仅6位,我们爆破rc4密钥并反解密文后再解一次base8,如果解出来是明文那就符合要求
#include <bits/stdc++.h>
using namespace std;
void init(int *s, char *key, int len)
{
int t[256] = {0};
char tmp = 0;
for (int i = 0; i < 256; ++i)
{
s[i] = i;
t[i] = key[i % len];
}
int j = 0;
for (int i = 0; i < 256; ++i)
{
j = (j + s[i] + t[i]) % 256;
swap(s[i], s[j]);
}
}
void crypt(int *s, char *data, int len)
{
int i = 0, j = 0, t = 0;
char tmp;
for (int k = 0; k < len; ++k)
{
i = (i + 1) % 256;
j = (j + s[i]) % 256;
swap(s[i], s[j]);
t = (s[i] + s[j]) % 256;
data[k] ^= s[t];
}
}
int cip[2333] =
{
63, 149, 187, 242, 87, 241, 122, 90, 34, 97,
81, 67, 162, 250, 155, 111, 68, 99, 192, 8,
18, 101, 92, 138, 140, 76, 237, 94, 202, 118,
185, 133, 175, 5, 56, 237, 66, 62, 66, 223,
93, 190, 5, 139, 53, 109, 243, 28, 207, 248,
106, 115, 37, 228, 183, 185, 54, 251, 2, 17,
160, 240, 87, 171, 33, 198, 199, 70, 153, 189,
30, 97, 94, 238, 85, 24, 238, 3, 41, 132,
127, 148, 95, 180, 106, 41, 216, 108, 228, 192,
157, 107, 204, 213, 148, 92, 221, 204, 213, 61,
192, 239, 12, 41, 229, 176, 147, 241, 179, 222,
176, 112
};
char data[2333];
char key[2333];
int s[260];
void check()
{
for (int i = 0; i < 112; ++i)
{
if (data[i] < 32 || data[i] > 127) return;
}
printf("Key: %s\nData: %s\n", key, data);
}
void dfs(char now, int dep)
{
key[dep] = now;
if (dep == 5)
{
init(s, key, 6);
int len = 112;
for (int i = 0; i < len; ++i) data[i] = cip[i];
crypt(s, data, len);
check();
return;
}
for (int i = '0'; i <= '9'; ++i) dfs(i, dep + 1);
}
int main()
{
for (int i = '0'; i <= '9'; ++i) dfs(i, 0);
return 0;
}
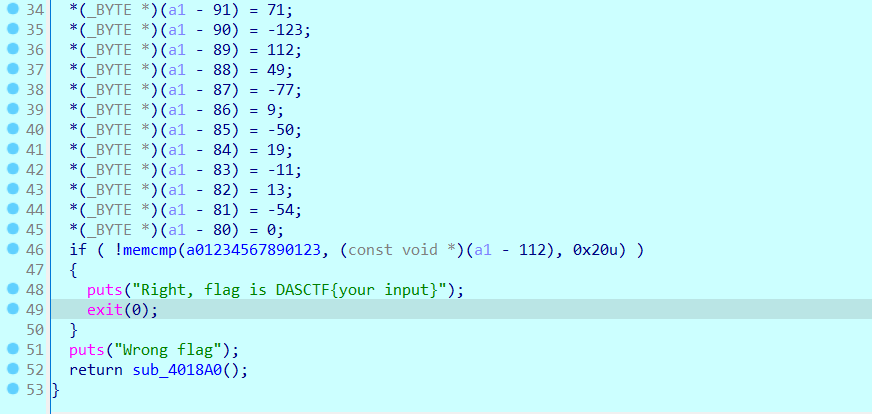
把data用base8解码,再把key拼在后面,得到flag:DASCTF{561516915572239428449843076691286116796614807391}
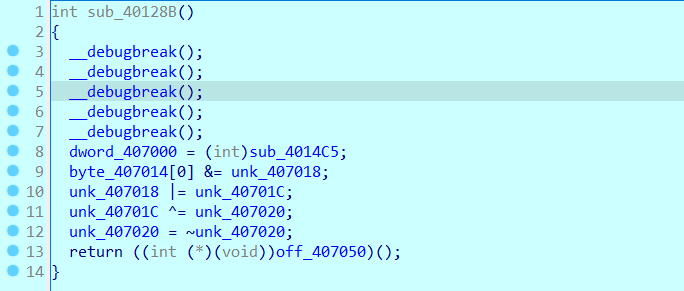
前面以为是加了一大堆反调试,后面发现只有32位切64位这一个反调试
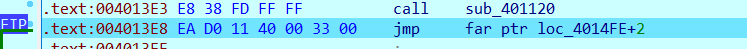
在sub_401120之后会出现类似smc的变化
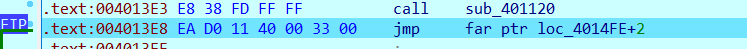
这里会变成jmp far ptr,这句话会远跳转到33:4011D0这个地址。远跳转有一个隐形的操作,他会将代码段寄存器CS设置为跳转到的这个段对应的段选择子,这里执行完了远跳转之后CS的值会变为0x33,熟悉天堂之门等玩意的话应该马上能联想到这里会切成64位程序。
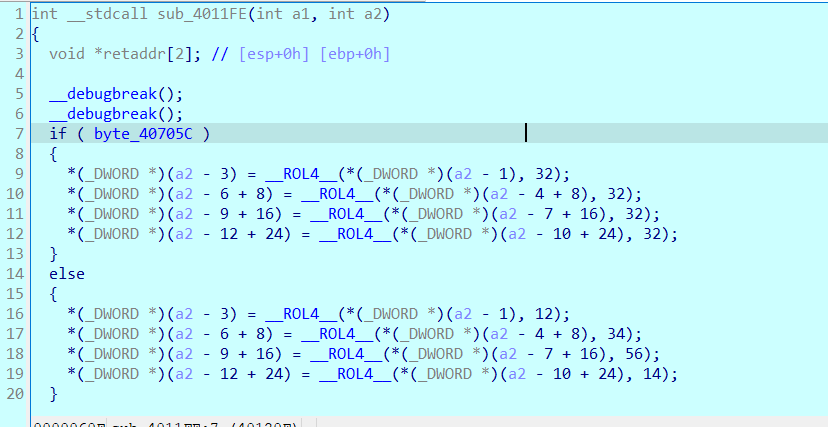
随后我们从4011D0开始,把0全部nop掉,创建函数后就能勉强看见加密流程了
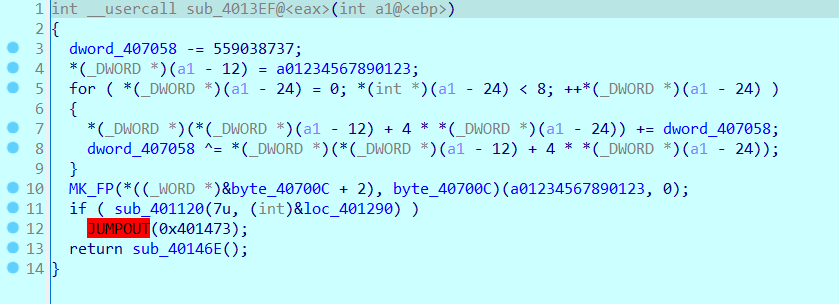
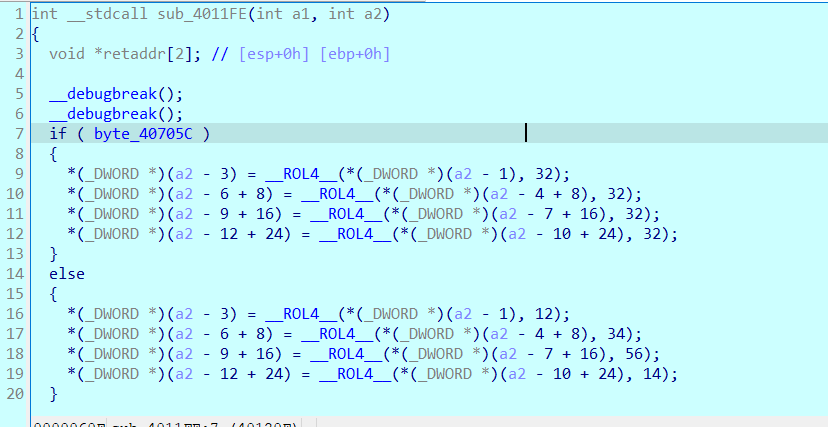
然后就跟着破碎的流程勉强走一次吧
#include <bits/stdc++.h>
using namespace std;
typedef unsigned int uint32;
typedef unsigned int uint;
typedef unsigned long long uint64;
#define _DWORD uint32
#define _QWORD uint64
template<class T> T __ROL__(T value, uint count)
{
const uint nbits = sizeof(T) * 8;
count %= nbits;
T high = value >> (nbits - count);
value <<= count;
value |= high;
return value;
}
template<class T> T __ROR__(T value, uint count)
{
const uint nbits = sizeof(T) * 8;
count %= nbits;
T low = value << (nbits - count);
value >>= count;
value |= low;
return value;
}
_DWORD flag[9];
_DWORD dword_407058 = 0x5DF966AE;
_DWORD key[] = {0x9D, 0x44, 0x37, 0xB5};
int main()
{
char enflag[] = {0xAA, 0x4F, 0x0F, 0xE2, 0xE4, 0x41, 0x99, 0x54, 0x2C, 0x2B, 0x84, 0x7E, 0xBC, 0x8F, 0x8B, 0x78, 0xD3, 0x73, 0x88, 0x5E, 0xAE, 0x47, 0x85, 0x70, 0x31, 0xB3, 0x09, 0xCE, 0x13, 0xF5, 0x0D, 0xCA};
for (int i = 0; i < 8; ++i) flag[i] = *(_DWORD *)(enflag + (4 * i));
key[0] &= key[1];
key[1] |= key[2];
key[2] ^= key[3];
key[3] = ~key[3];
for (int i = 0; i < 32; ++i) *((char *)flag + i) ^= key[i % 4];
*(_QWORD *)((char *)flag + 24) = __ROR__(*(_QWORD *)((char *)flag + 24), 14);
*(_QWORD *)((char *)flag + 16) = __ROR__(*(_QWORD *)((char *)flag + 16), 56);
*(_QWORD *)((char *)flag + 8) = __ROR__(*(_QWORD *)((char *)flag + 8), 34);
*(_QWORD *)((char *)flag) = __ROR__(*(_QWORD *)((char *)flag), 12);
dword_407058 -= 0x21524111;
for (int i = 0; i < 8; ++i)
{
_DWORD tmp = flag[i];
flag[i] -= dword_407058;
dword_407058 ^= tmp;
}
cout << (char*) flag << endl;
}
逆算法的时候发现好像前面看加密的时候的顺序有点不对劲,不知道为什么,但至少做出来了(
DASCTF{6cc1e44811647d38a15017e389b3f704}
赛中费了很大的功夫去配bpf程序的编写环境,以为能动调,然后发现屁用没有,笑嘻了
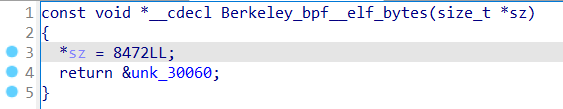
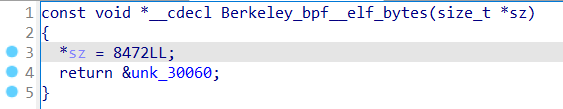
这里加载了一段长8472的代码,ELF文件,按函数的名字来说应该是一个bpf文件,直接用IDA Python给他摸下来
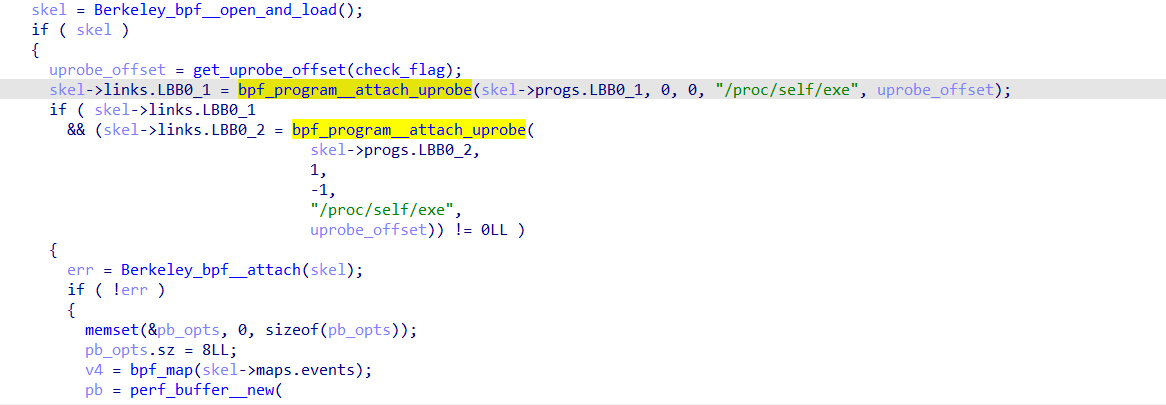
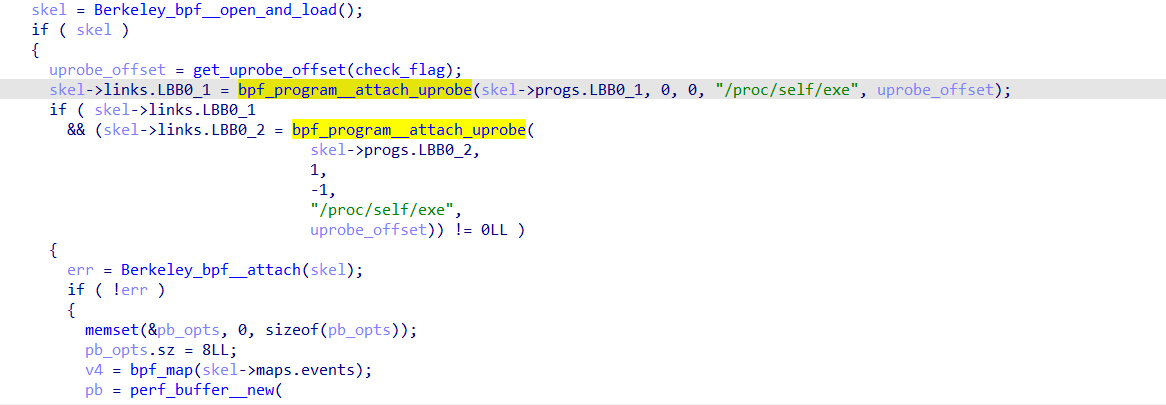
刚刚的elf文件是在open_and_load里面找到的,接下来的program_attach_uprobe函数,查了一下
bpf_program__attach_uprobe() 用于绑定 uprobe 和 uretprobe 追踪目标的信息。
是个注册ebpf的函数
接下来看不懂了,转到刚才提取的elf文件。ghidra有分析bpf文件的插件
https://github.com/Nalen98/eBPF-for-Ghidra/releases/tag/v0.2
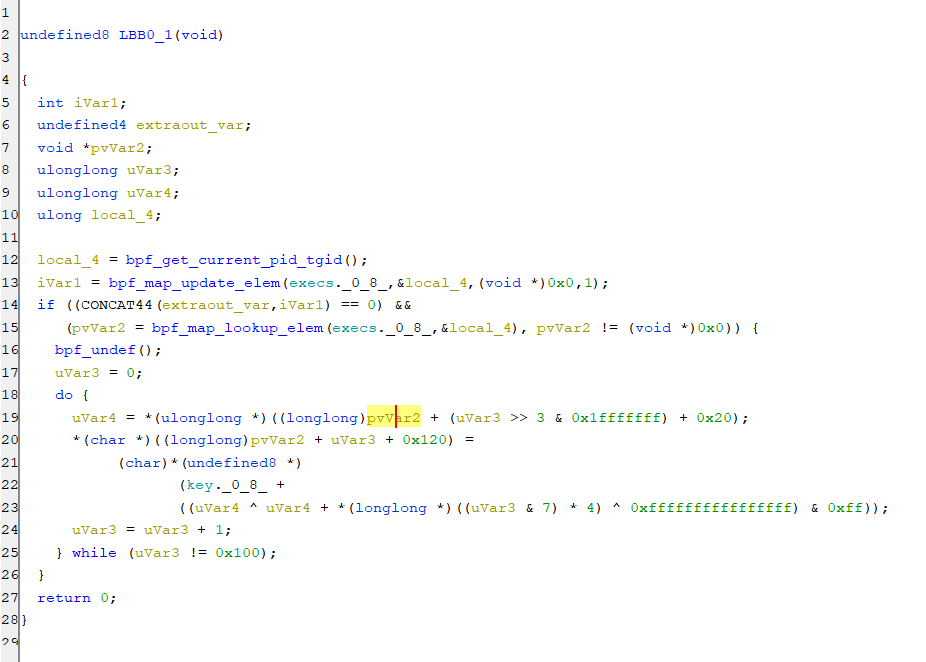
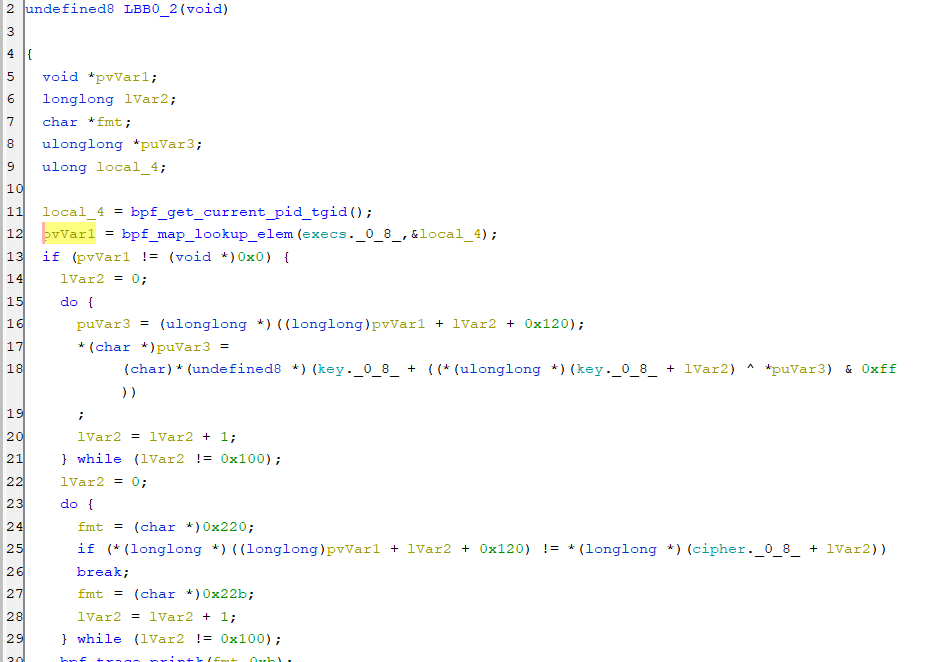
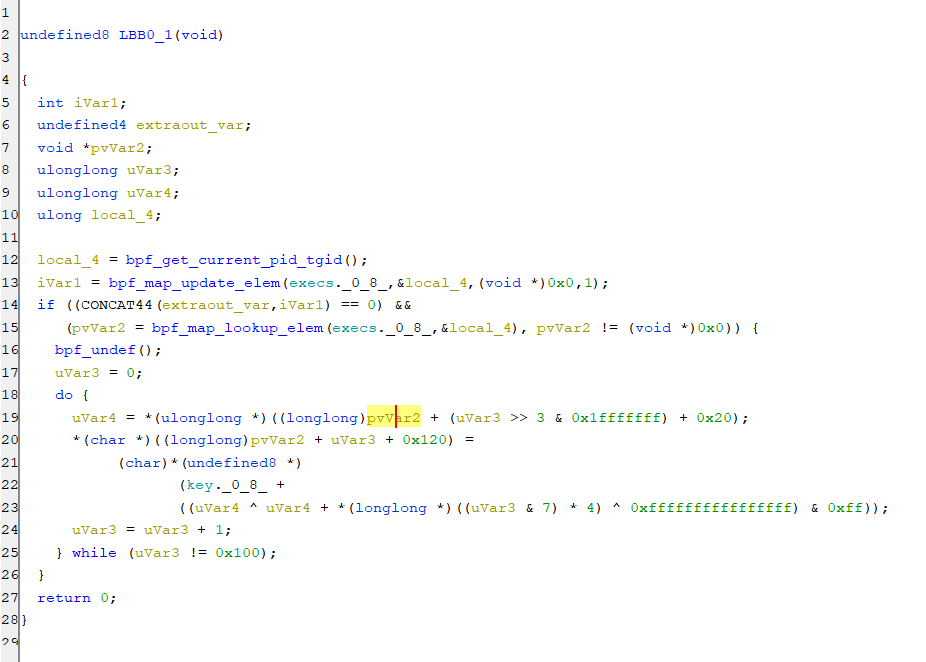
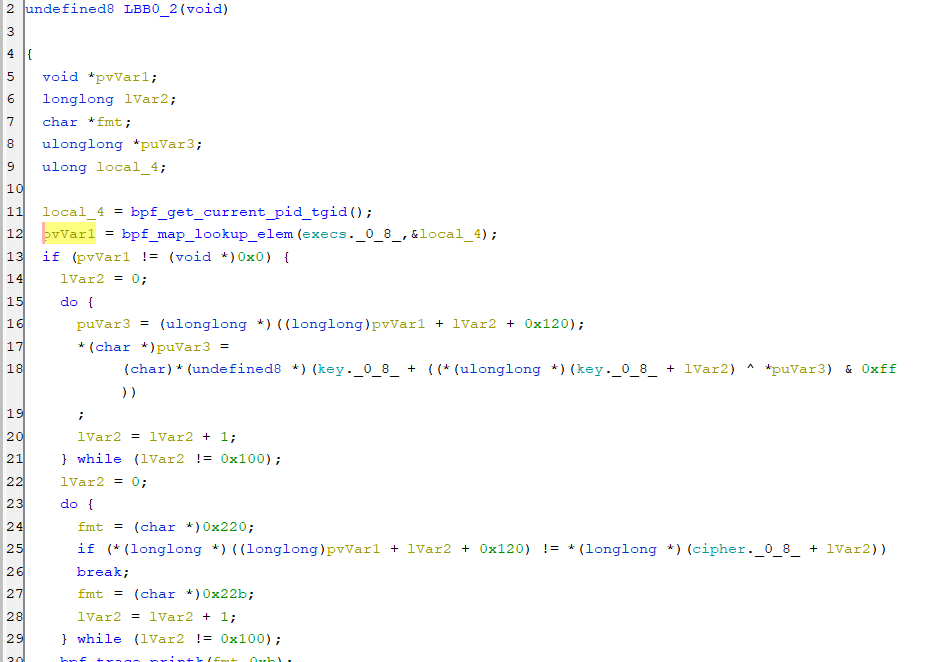
这个elf里面主要有两个函数,比较明显的能看出来是个加密的东西,联想到之前bpf_program__attach_uprobe的作用,推测是用这俩函数把check_flag给替换掉了,这才是真的check函数
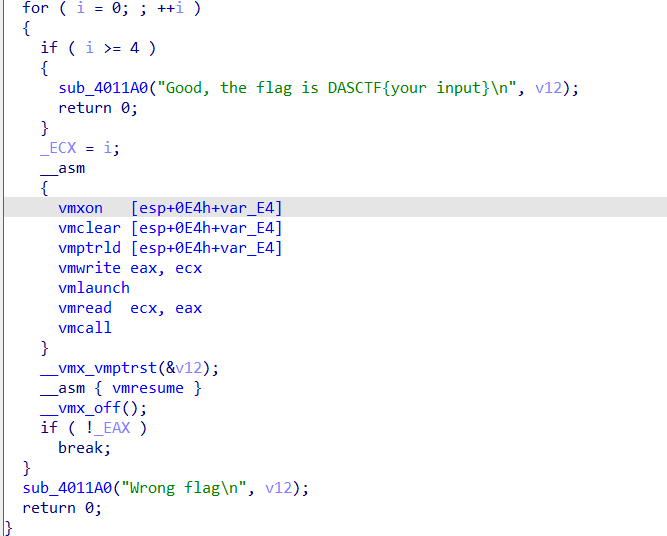
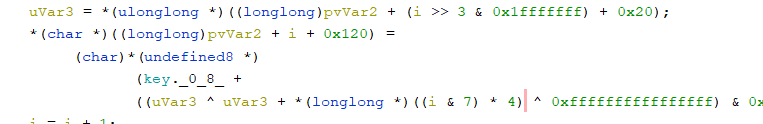
在这个地方可以发现少了个8位数组,显然是xxx[i & 7],这里没找到
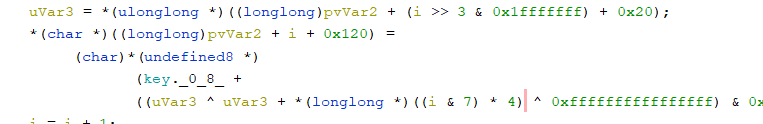
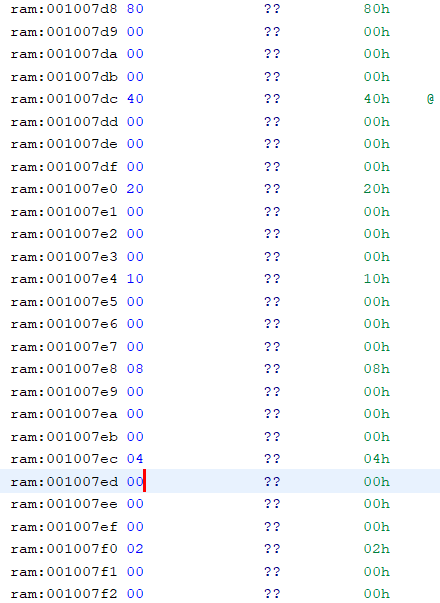
在ram段里面翻了一年后发现这个,那应该就是这些数据
整个新check函数翻译成更好看的伪代码如下
显然,可以先爆破第二个循环之前的enflag值,再爆破flag
key = [ 0xc1, 0xd1, 0x02, 0x61, 0xd6, 0xf7, 0x13, 0xa2, 0x9b, 0x20, 0xd0, 0x4a, 0x8f, 0x7f, 0xee, 0xb9, 0x00, 0x63, 0x34, 0xb0, 0x33, 0xb7, 0x8a, 0x8b, 0x94, 0x60, 0x2e, 0x8e, 0x21, 0xff, 0x90, 0x82, 0xd5, 0x87, 0x96, 0x78, 0x22, 0xb6, 0x48, 0x6c, 0x45, 0xc7, 0x5a, 0x16, 0x80, 0xfd, 0xe4, 0x8c, 0xbf, 0x01, 0x1f, 0x4b, 0x79, 0x24, 0xa0, 0xb4, 0x23, 0x4d, 0x3b, 0xc5, 0x5d, 0x6f, 0x0d, 0xc9, 0xd4, 0xca, 0x55, 0xe0, 0x39, 0xad, 0x2b, 0xcd, 0x2c, 0xec, 0xc2, 0x6b, 0x30, 0xe6, 0x0c, 0xa8, 0x9a, 0x2f, 0xf6, 0xe8, 0xbb, 0x32, 0x57, 0xfb, 0x0b, 0x9d, 0xf2, 0x3f, 0xb5, 0xf9, 0x59, 0xe5, 0x10, 0xcf, 0x51, 0x41, 0xe9, 0x50, 0xdf, 0x26, 0x74, 0x58, 0xcb, 0x64, 0x54, 0x73, 0xab, 0xf4, 0xb2, 0x9f, 0x18, 0xf8, 0x4e, 0xfe, 0x08, 0x1d, 0x4f, 0x49, 0xd3, 0xac, 0x38, 0x12, 0x77, 0x11, 0x69, 0x07, 0x1c, 0x99, 0xb3, 0xe7, 0x3d, 0x05, 0xd8, 0xfc, 0x70, 0x46, 0x93, 0x09, 0x65, 0x89, 0xb1, 0xc6, 0x52, 0xfa, 0xd2, 0x0e, 0xa9, 0x17, 0xe3, 0x91, 0xa1, 0x68, 0x5b, 0x2a, 0xf0, 0xc3, 0x42, 0xcc, 0x29, 0xde, 0xdc, 0x85, 0x98, 0x31, 0x5c, 0xbc, 0x2d, 0xef, 0x5e, 0x7e, 0xaf, 0x67, 0x62, 0xa7, 0x56, 0x88, 0xa4, 0x43, 0x40, 0xe1, 0x37, 0x9e, 0x36, 0x76, 0x71, 0x84, 0xbd, 0x06, 0x8d, 0x47, 0x7d, 0x53, 0xd7, 0xc8, 0xce, 0x15, 0x92, 0x95, 0x4c, 0x28, 0x6d, 0x75, 0xeb, 0x7c, 0xf3, 0xbe, 0xaa, 0xb8, 0xed, 0x03, 0x3c, 0x27, 0x3e, 0x19, 0xdd, 0xa6, 0x66, 0x25, 0x1e, 0xc4, 0x6e, 0xc0, 0xe2, 0xdb, 0x3a, 0xd9, 0x81, 0xa5, 0x1b, 0xf5, 0x04, 0xae, 0xba, 0xea, 0x97, 0x83, 0x35, 0x44, 0xa3, 0x7a, 0x1a, 0xf1, 0x86, 0xda, 0x7b, 0x14, 0x72, 0x9c, 0x6a, 0x0f, 0x5f, 0x0a, 0x00 ]
cipher = [ 0xf3, 0x27, 0x47, 0x1b, 0x8f, 0x09, 0xfb, 0x17, 0x70, 0x48, 0xb0, 0x53, 0x32, 0xdb, 0xc0, 0xb8, 0x63, 0x2d, 0x40, 0x4b, 0xf5, 0x16, 0xf0, 0x35, 0xe7, 0xdf, 0xea, 0xa2, 0x9c, 0x41, 0xb3, 0x25, 0xd7, 0x0c, 0x33, 0x9c, 0x7b, 0x5a, 0xcd, 0x13, 0xbb, 0xee, 0x3e, 0x0e, 0xf2, 0xcf, 0x35, 0xda, 0xaf, 0xa2, 0x66, 0x7d, 0x38, 0x37, 0x67, 0x1e, 0x1f, 0x6b, 0x7b, 0x30, 0x0b, 0x7a, 0x02, 0xa9, 0xc8, 0x61, 0x27, 0x41, 0xdb, 0x01, 0x22, 0x31, 0x6f, 0xb6, 0xd4, 0x1b, 0x04, 0xd3, 0x94, 0xb8, 0x46, 0xc7, 0x24, 0xcf, 0xbd, 0xaf, 0x0b, 0xdc, 0x2e, 0xbb, 0xb2, 0x71, 0xf4, 0x99, 0x57, 0x36, 0xd1, 0x95, 0x52, 0x92, 0xba, 0x6d, 0xf3, 0x30, 0x50, 0x59, 0x9b, 0xea, 0x2f, 0x83, 0xdc, 0xf0, 0xde, 0x57, 0xa1, 0xac, 0xd2, 0x51, 0xa2, 0x1d, 0x59, 0xa8, 0x00, 0xb6, 0xe2, 0x65, 0x41, 0x0c, 0x4f, 0xeb, 0xf0, 0x2e, 0x58, 0x2a, 0x1f, 0xf4, 0x95, 0x72, 0x88, 0x7c, 0xa9, 0x0e, 0xcb, 0x3c, 0x42, 0xb9, 0xf3, 0x49, 0x9b, 0x52, 0x98, 0x12, 0xa3, 0x17, 0x51, 0xc0, 0x59, 0x40, 0x0a, 0xbc, 0xe8, 0x4c, 0x04, 0xfb, 0x13, 0x0a, 0x17, 0x3f, 0xe6, 0x36, 0x97, 0xdf, 0xb3, 0xe2, 0x42, 0x7f, 0xf8, 0xcc, 0x0e, 0xd1, 0x77, 0xc4, 0xa8, 0x46, 0x48, 0xe3, 0xf1, 0x0a, 0xef, 0x94, 0x56, 0x54, 0x5b, 0xca, 0xbd, 0xdd, 0x7f, 0x56, 0x47, 0xc2, 0x99, 0xfa, 0x89, 0xcc, 0xe1, 0xb9, 0x3a, 0x78, 0xe2, 0x37, 0x58, 0x01, 0x1b, 0xc3, 0x4b, 0xe6, 0x8c, 0xf3, 0xe5, 0xb6, 0x71, 0x9e, 0x63, 0xaf, 0x11, 0xce, 0x87, 0xf6, 0x6e, 0xde, 0xc8, 0xb1, 0xd0, 0x7a, 0x15, 0x6c, 0x10, 0x08, 0x99, 0x7b, 0x22, 0x55, 0x10, 0x7a, 0x82, 0x73, 0xfc, 0x62, 0xcb, 0x34, 0xa7, 0xb7, 0x62, 0xfa, 0x6b, 0x9f ]
enflag = []
for i in range(256):
for j in range(256):
if (key[key[i] ^ j] & 0xFF) == cipher[i]:
enflag.append(j)
break
data = [0x80, 0x40, 0x20, 0x10, 0x08, 0x04, 0x02, 0x01]
tmp = [0 for i in range(8)]
for i in range(32):
for c in range(32, 128):
for j in range(8):
k = (c ^ (c + data[j]) ^ 0xFFFFFFFFFFFFFFFF) & 0xFF
tmp[j] = key[k]
if tmp == enflag[8 * i: 8 * (i + 1)]:
print(chr(c), end="")
break
得到flag: DASCTF{71c2ac98ac8d99a2e8a95111449a7393}
https://bbs.kanxue.com/thread-271967.htm
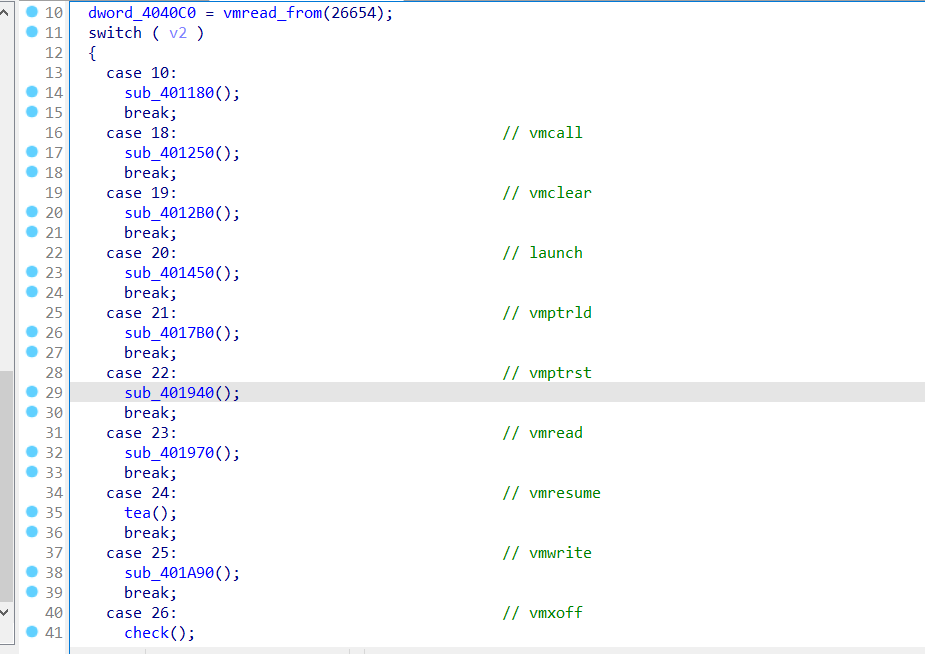
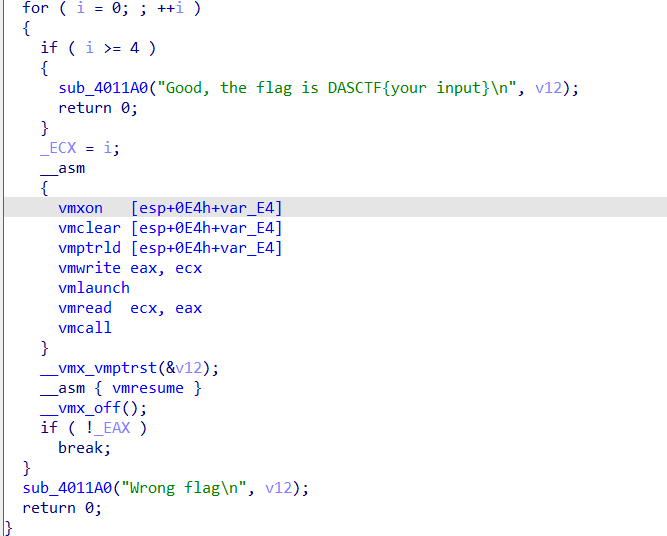
参考这个blog,vmexit事件处理函数的框架,可以在驱动程序里面看见重点流程
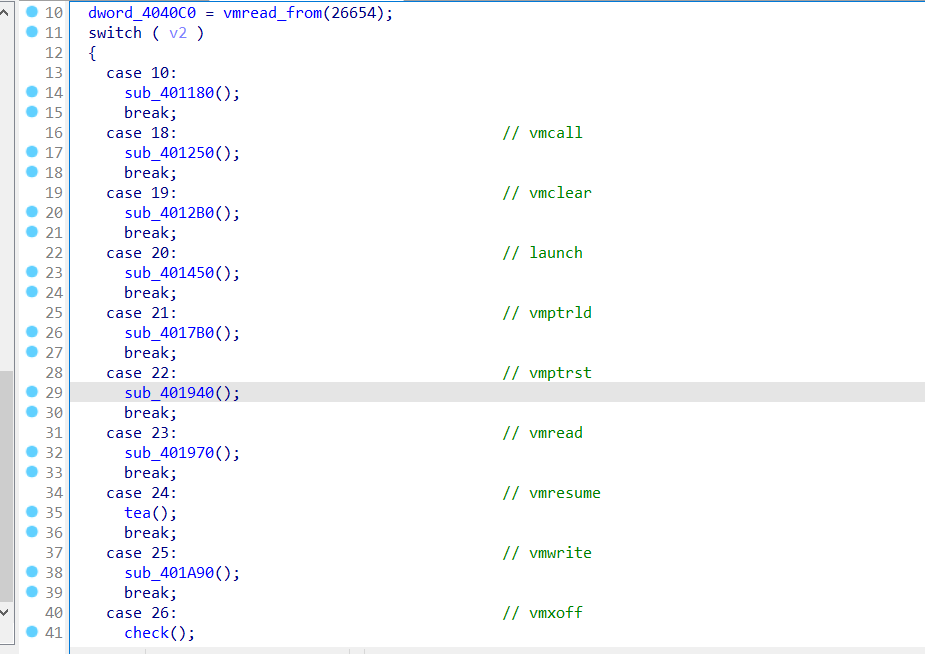
在主程序中
意思就是下面的东西得跑4轮,全过的话flag正确。这个内联汇编部分给出了后续程序的执行顺序,一共10个vm函数
那么这就是驱动里面switch-case的执行顺序了。在驱动程序里可以发现,vmxon-vmread在初始化数据,vmcall-vmresume在加密,vmxoff是最终check。
一个tea一个rc4,然后数据有一些变化,解一下就行
得到flag: DASCTF{81920c3758be43705ba154bb8f5998460}(跑不动VT程序,但解出了明文flag应该就是对的吧大概)
__EOF__
作 者:iPlayForSG
出 处:https://www.cnblogs.com/Here-is-SG/p/17090521.html
关于博主:编程路上的小学生,热爱技术,喜欢专研。评论和私信会在第一时间回复。或者直接私信我。
版权声明:署名 - 非商业性使用 - 禁止演绎,协议普通文本 | 协议法律文本。
声援博主:如果您觉得文章对您有帮助,可以点击文章右下角【推荐】一下。您的鼓励是博主的最大动力!



【推荐】国内首个AI IDE,深度理解中文开发场景,立即下载体验Trae
【推荐】编程新体验,更懂你的AI,立即体验豆包MarsCode编程助手
【推荐】抖音旗下AI助手豆包,你的智能百科全书,全免费不限次数
【推荐】轻量又高性能的 SSH 工具 IShell:AI 加持,快人一步
· 无需6万激活码!GitHub神秘组织3小时极速复刻Manus,手把手教你使用OpenManus搭建本
· C#/.NET/.NET Core优秀项目和框架2025年2月简报
· Manus爆火,是硬核还是营销?
· 终于写完轮子一部分:tcp代理 了,记录一下
· 【杭电多校比赛记录】2025“钉耙编程”中国大学生算法设计春季联赛(1)