12 flask之默认处理了xss攻击
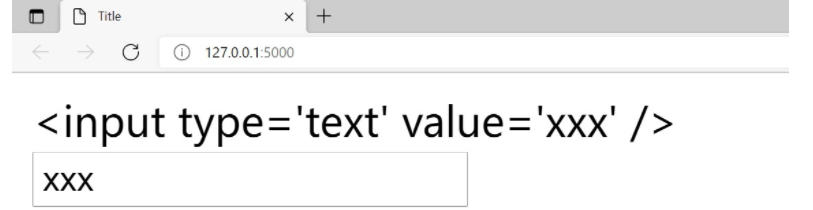
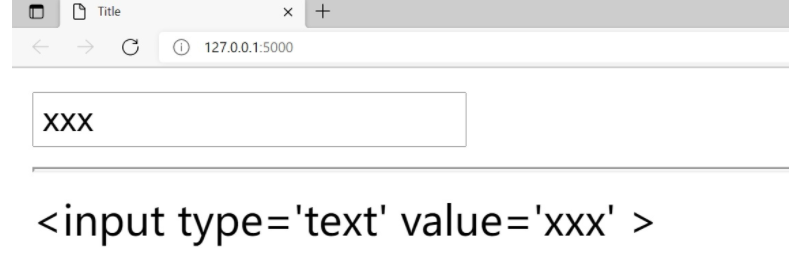
1 前端处理:safe
main.py
from flask import Flask, render_template
app = Flask(__name__)
@app.route('/')
def index():
ss = "<input type='text' value='xxx' />"
return render_template('index.html', ss=ss)
if __name__ == '__main__':
app.run()index.html
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<title>Title</title>
</head>
<body>
{{ss}}
<br>
{{ss|safe}}
</body>
</html> 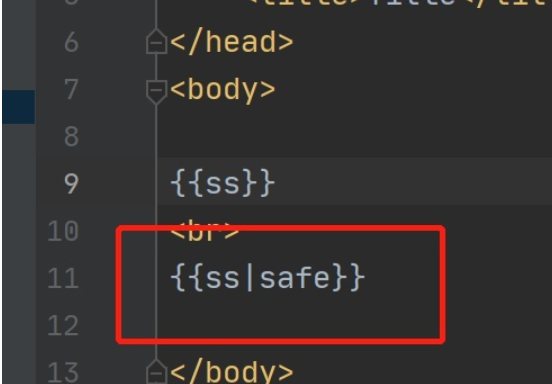
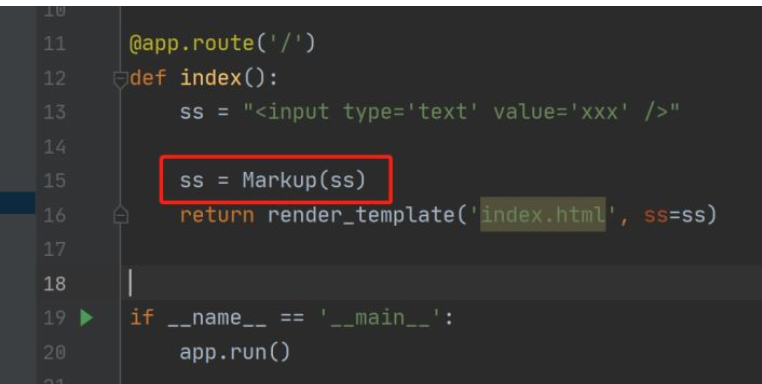
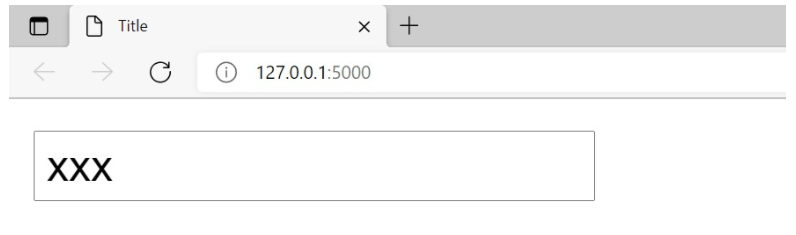
2 后端处理:Markup
main.py
from flask import Flask, render_template, Markup
app = Flask(__name__)
@app.route('/')
def index():
ss = "<input type='text' value='xxx' />"
ss = Markup(ss)
return render_template('index.html', ss=ss)
if __name__ == '__main__':
app.run()
index.html
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<title>Title</title>
</head>
<body>
{{ss}}
</body>
</html>
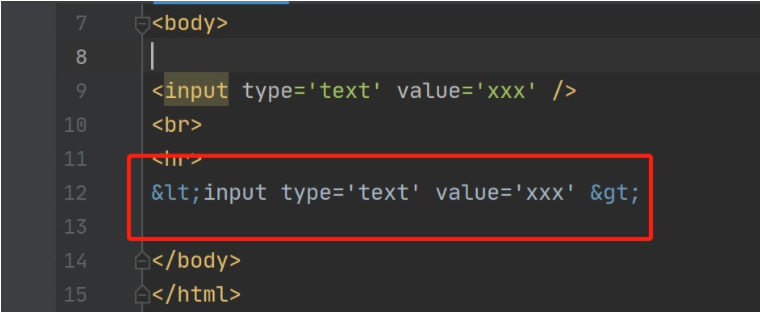
3 jinja2怎么处理xss攻击
html中的特殊符号
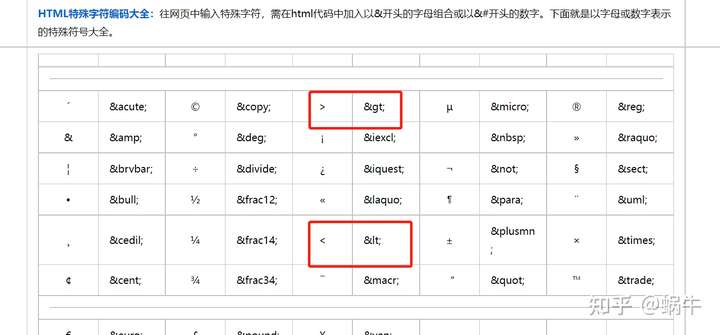
案例:html 中的 input 标签往前端返回是<会变成<,>会变成>
| <input type='text' value='xxx' /> | <input type='text' value='xxx' > |
|---|
main.py
# -*- coding: utf-8 -*-
# @Time : 2021/12/12 15:58
# @Author : dzg
from flask import Flask, render_template, Markup
app = Flask(__name__)
@app.route('/')
def index():
return render_template('index.html')
if __name__ == '__main__':
app.run()
index.html
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<title>Title</title>
</head>
<body>
<input type='text' value='xxx' />
<br>
<hr>
<input type='text' value='xxx' >
</body>
</html>
4 注意
1.Markup等价django的mark_safe ,
2.extends,include一模一样


 浙公网安备 33010602011771号
浙公网安备 33010602011771号